Analiza paquetes de Go automáticamente
Obtén información para habilitar el análisis automático, enviar una imagen de contenedor a Artifact Registry y ver una lista de las vulnerabilidades que se encontraron en la imagen.
Artifact Analysis analiza las vulnerabilidades cada vez que se envía una imagen a Artifact Registry. Los administradores de la plataforma y los desarrolladores de aplicaciones pueden usar esta función de análisis automático para identificar riesgos en su canalización de entrega de software.
En esta guía de inicio rápido, se usa un paquete simple disponible de forma pública para demostrar un tipo de análisis de paquetes. De forma predeterminada, Artifact Analysis analiza las vulnerabilidades en varios tipos de paquetes una vez que habilitas la API de análisis. Los tipos de paquetes compatibles incluyen: OS, Go, Java (Maven), Python y Node.js (npm).
Antes de comenzar
- Sign in to your Google Cloud account. If you're new to Google Cloud, create an account to evaluate how our products perform in real-world scenarios. New customers also get $300 in free credits to run, test, and deploy workloads.
-
Install the Google Cloud CLI.
-
Si usas un proveedor de identidad externo (IdP), primero debes acceder a gcloud CLI con tu identidad federada.
-
Para inicializar gcloud CLI, ejecuta el siguiente comando:
gcloud init -
Create or select a Google Cloud project.
Roles required to select or create a project
- Select a project: Selecting a project doesn't require a specific IAM role—you can select any project that you've been granted a role on.
-
Create a project: To create a project, you need the Project Creator
(
roles/resourcemanager.projectCreator), which contains theresourcemanager.projects.createpermission. Learn how to grant roles.
-
Create a Google Cloud project:
gcloud projects create PROJECT_ID
Replace
PROJECT_IDwith a name for the Google Cloud project you are creating. -
Select the Google Cloud project that you created:
gcloud config set project PROJECT_ID
Replace
PROJECT_IDwith your Google Cloud project name.
-
Verify that billing is enabled for your Google Cloud project.
-
Enable the Artifact Registry and Container Scanning APIs:
Roles required to enable APIs
To enable APIs, you need the Service Usage Admin IAM role (
roles/serviceusage.serviceUsageAdmin), which contains theserviceusage.services.enablepermission. Learn how to grant roles.gcloud services enable containerscanning.googleapis.com
artifactregistry.googleapis.com -
Install the Google Cloud CLI.
-
Si usas un proveedor de identidad externo (IdP), primero debes acceder a gcloud CLI con tu identidad federada.
-
Para inicializar gcloud CLI, ejecuta el siguiente comando:
gcloud init -
Create or select a Google Cloud project.
Roles required to select or create a project
- Select a project: Selecting a project doesn't require a specific IAM role—you can select any project that you've been granted a role on.
-
Create a project: To create a project, you need the Project Creator
(
roles/resourcemanager.projectCreator), which contains theresourcemanager.projects.createpermission. Learn how to grant roles.
-
Create a Google Cloud project:
gcloud projects create PROJECT_ID
Replace
PROJECT_IDwith a name for the Google Cloud project you are creating. -
Select the Google Cloud project that you created:
gcloud config set project PROJECT_ID
Replace
PROJECT_IDwith your Google Cloud project name.
-
Verify that billing is enabled for your Google Cloud project.
-
Enable the Artifact Registry and Container Scanning APIs:
Roles required to enable APIs
To enable APIs, you need the Service Usage Admin IAM role (
roles/serviceusage.serviceUsageAdmin), which contains theserviceusage.services.enablepermission. Learn how to grant roles.gcloud services enable containerscanning.googleapis.com
artifactregistry.googleapis.com Abre la página Repositorios en la consola de Google Cloud .
Haz clic en Crear repositorio.
En la página Crear repositorio, ingresa la siguiente configuración:
- Nombre:
quickstart-docker-repo - Formato: Docker
- Modo: Estándar
- Tipo de ubicación: Región
- Región:
us-central1
- Nombre:
Haz clic en Crear.
Cambia a un directorio en el que quieras guardar la imagen de contenedor.
Copia una imagen en tu directorio local. Por ejemplo, puedes usar Docker para extraer la imagen de Go más reciente de Docker Hub.
docker pull golang:1.17.6-alpine- PROJECT es tu Google Cloud
ID del proyecto.
Si el ID de tu proyecto contiene dos puntos (
:), consulta Proyectos con alcance de dominio. us-central1es la región del repositorio de Artifact Registry.docker.pkg.deves el nombre de host de los repositorios de Docker.quickstart-imagees el nombre de imagen que deseas usar en el repositorio. El nombre de la imagen puede ser diferente al nombre de la imagen local.tag1es una etiqueta que agregas a la imagen de Docker. Si no especificaste una etiqueta, Docker aplicará la etiqueta predeterminadalatest.Obtén la lista de repositorios.
En la lista de repositorios, haz clic en uno.
En la lista de imágenes, haz clic en el nombre de una imagen.
Los totales de vulnerabilidades para cada resumen de imagen se muestran en la columna Vulnerabilidades.

Para ver la lista de vulnerabilidades de una imagen, haz clic en el vínculo de la columna Vulnerabilidades.
En la sección Resultados del análisis, se muestra un resumen de los tipos de paquetes analizados, la cantidad total de vulnerabilidades, las vulnerabilidades con correcciones disponibles, las vulnerabilidades sin correcciones y la gravedad efectiva.

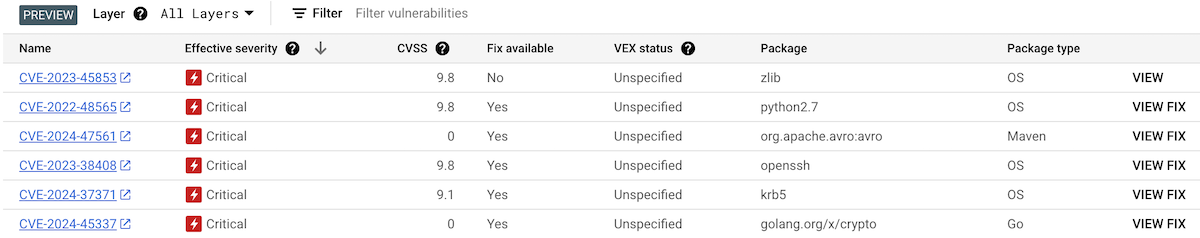
En la tabla de vulnerabilidades, se indica el nombre de las vulnerabilidades y exposiciones comunes (CVE) para cada vulnerabilidad encontrada, la gravedad efectiva, la puntuación del Common Vulnerability Scoring System (CVSS), las correcciones (cuando están disponibles), el nombre del paquete que contiene la vulnerabilidad y el tipo de paquete.
La consola deGoogle Cloud muestra hasta 1,200 vulnerabilidades por página en esta tabla. Puedes filtrar y ordenar estos archivos para verificar un archivo, un directorio, una capa o un tipo de archivo específicos por extensión.
Para obtener detalles sobre una CVE específica, haz clic en su nombre.
Para ver los detalles de la ocurrencia de la vulnerabilidad, como el número de versión y la ubicación afectada, haz clic en Ver o Ver corregida en la fila con el nombre de la vulnerabilidad. El texto del vínculo es Ver para las vulnerabilidades sin corrección y Ver corregido para las vulnerabilidades en las que se aplicó una corrección.
En Artifact Registry, abre tu lista de repositorios.
En la página Repositorios, haz clic en un repositorio.
En la página Detalles del repositorio, haz clic en una imagen.
En la lista de versiones de la imagen, haz clic en un resumen de la imagen.
En la página de detalles del resumen de la imagen, haz clic en la pestaña Vulnerabilidades.
Cuando hay metadatos basados en capas disponibles, Artifact Analysis muestra una lista de capas seleccionables en la barra Capa:
Para ver la lista de capas, haz clic en el menú desplegable de capas.
Se abrirá una lista desplegable que muestra una lista numerada de capas. La capa 0 representa la capa inferior, y cada capa siguiente se basa en la anterior. Solo se muestran las capas en las que se encontraron vulnerabilidades.
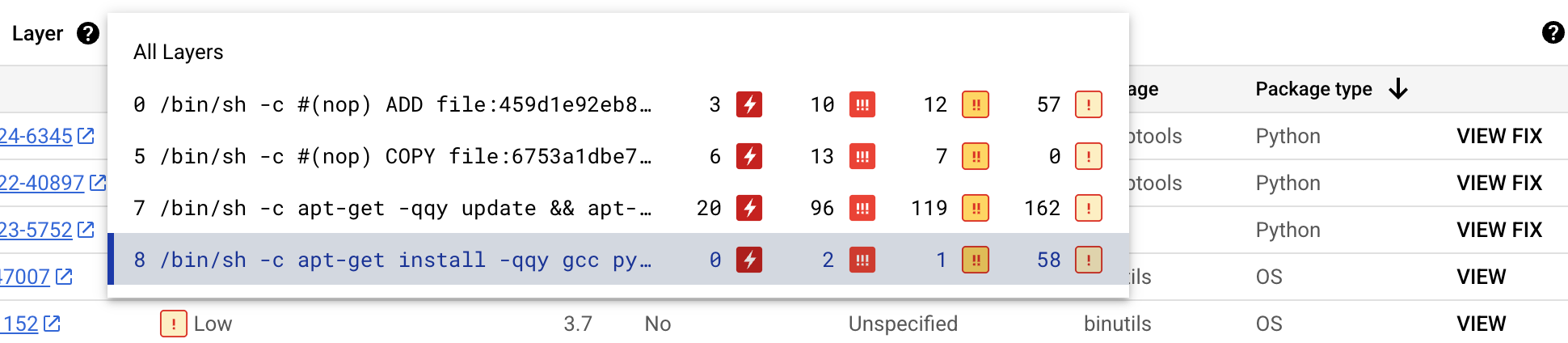
Para cada capa, Artifact Analysis muestra el comando de Docker que se usó para compilarla y la cantidad de vulnerabilidades que se encontraron en ella.
Para obtener más información sobre las vulnerabilidades en una capa específica, selecciona una capa de la lista de capas.
La tabla de vulnerabilidades se actualiza para mostrar solo las vulnerabilidades encontradas en la capa seleccionada. Puedes aplicar más filtros o investigar vulnerabilidades específicas.
Haz clic en VER o VER LA CORRECCIÓN junto a una vulnerabilidad para ver información más detallada sobre ella.
En el panel lateral Detalles de la vulnerabilidad, se muestran las ubicaciones de los archivos en los que los paquetes tienen vulnerabilidades.
En la tabla Ubicaciones de archivos, coloca el cursor sobre el signo de interrogación para abrir metadatos de capas adicionales.
En un diálogo, se muestran el índice de la capa, el comando de compilación de la capa, el resumen de la capa y la imagen base en la que puedes corregir la vulnerabilidad.
Crea un repositorio de Docker en Artifact Registry
Crea un repositorio de Docker para almacenar la imagen de muestra de esta guía de inicio rápido.
Verás la página Repositorios. Tu repositorio quickstart-docker-repo se agrega a la lista de repositorios.
Configura la autenticación
Antes de poder enviar o extraer imágenes con Artifact Registry, debes configurar Docker para que use Google Cloud CLI con el objetivo de autenticar las solicitudes enviadas a Artifact Registry.
En Cloud Shell o en tu shell local, configura la autenticación para los repositorios de Docker en la región us-central1:
gcloud auth configure-docker us-central1-docker.pkg.dev
Cómo obtener un paquete
Etiqueta tu paquete con el nombre de un repositorio
Cuando desees enviar un paquete a Artifact Registry, deberás configurar el comando docker push para enviar la imagen a una ubicación específica.
Ejecuta el siguiente comando para etiquetar la imagen como quickstart-image:tag1:
docker tag golang:1.17.6-alpine \ us-central1-docker.pkg.dev/PROJECT/quickstart-docker-repo/quickstart-image:tag1
Aquí:
Envía la imagen a Artifact Registry
Artifact Analysis analiza automáticamente los paquetes de Go nuevos cuando se suben a Artifact Registry.
Para enviar tu imagen a tu repositorio de Docker en Artifact Registry, ejecuta el siguiente comando:
docker push us-central1-docker.pkg.dev/PROJECT/quickstart-docker-repo/quickstart-image:tag1
Reemplaza PROJECT por tu Google Cloud
ID del proyecto.
Si el ID de tu proyecto contiene dos puntos (:), consulta Proyectos con alcance de dominio.
Consulta los resultados del análisis de vulnerabilidades
Para ver las vulnerabilidades de una imagen, sigue estos pasos:
Cómo ver las vulnerabilidades en una capa específica
Artifact Analysis proporciona metadatos específicos de la capa para ayudarte a identificar qué paquete contiene vulnerabilidades y qué comando de compilación de Docker introdujo esa capa.
Para ver los metadatos de vulnerabilidades basados en capas en la consola de Google Cloud , haz lo siguiente:
Limpia
Para evitar que se apliquen cargos a tu cuenta de Google Cloud por los recursos que se usaron en esta página, borra el proyecto de Google Cloud que tiene los recursos.
Si creaste un proyecto nuevo para esta guía, ahora puedes borrarlo.Delete a Google Cloud project:
gcloud projects delete PROJECT_ID

