For the strongest encryption between Looker and your database, you can create a SSH tunnel to either a tunnel server or the database server itself.
Step 1: Choose a host on which to terminate the tunnel
The first step to set up SSH tunnel access for your database is to choose the host that will be used to terminate the tunnel. The tunnel can be terminated on either the database host itself, or on a separate host (the tunnel server).
Using the database server
When you don't use a tunnel server, Looker connects directly to your database server through an SSH tunnel over the public internet. Terminating on the database has the advantage of simplicity. One fewer host is involved, so there are no additional machines and their associated costs. This option may not be feasible if your database server is on a protected network that does not have direct access from the Internet.
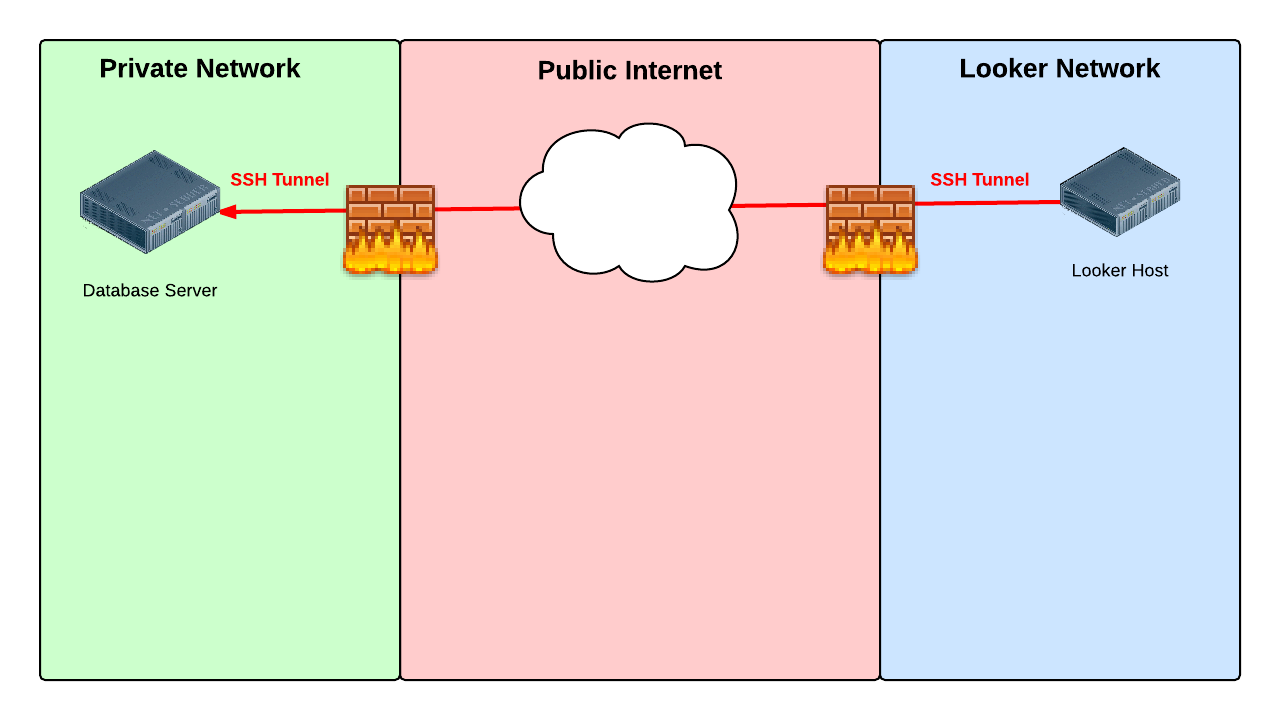
Using a tunnel server
When you use a tunnel server, Looker connects to your database server through a separate tunnel server on a restricted network. Terminating the tunnel on a separate server has the advantage of keeping your database server inaccessible from the Internet. If the tunnel server is compromised it is one step removed from the database server. We recommend that you remove all non-essential software and users from the tunnel server and closely monitor it with tools such as an IDS.

The tunnel server can be any Unix or Linux host that:
- Can be accessed from the Internet using SSH
- Can access the database
Step 2: Create IP allowlist
The second step is to allow network traffic to reach the tunnel server or database host through SSH, which is generally on TCP port 22.
Allow network traffic from each of the IP addresses listed here for the region where your Looker instance is hosted. By default, this will be the United States.
Instances hosted on Google Cloud
Looker-hosted instances are hosted on Google Cloud by default. For instances that are hosted on Google Cloud, add to the allowlist the IP addresses that match your region.
Click here for a full list of IP addresses for instances that are hosted on Google Cloud
Moncks Corner, South Carolina, USA (us-east1)
34.23.50.13735.211.210.6435.211.95.5535.185.59.10034.111.239.10235.237.174.1734.73.200.23535.237.168.21634.75.58.12335.196.30.11035.243.254.166
Ashburn, Northern Virginia, USA (us-east4)
34.150.212.934.150.174.5434.85.200.21735.221.30.17735.245.82.7334.86.214.22635.245.177.11235.245.211.10934.86.118.23934.86.136.19035.194.74.18534.86.52.18835.221.3.16335.221.62.21834.86.34.13535.236.240.16835.199.50.23734.145.252.25535.245.141.4235.245.20.1634.145.147.14634.145.139.2234.150.217.2035.199.35.17635.245.72.3534.85.187.17535.236.220.22534.150.180.944.85.195.16834.86.126.12434.145.200.834.85.142.9534.150.217.9635.245.140.3634.86.124.23435.194.69.23935.230.163.2635.186.187.4834.86.154.13434.85.128.25035.245.212.21235.245.74.7534.86.246.18734.86.241.21634.85.222.934.86.171.12734.145.204.10634.150.252.16935.245.9.213
Council Bluffs, Iowa, USA (us-central1)
104.154.21.23135.192.130.12635.184.100.5134.70.128.7434.69.207.17635.239.118.19734.172.2.22734.71.191.21034.173.109.5035.225.65.334.170.192.19034.27.97.6735.184.118.15534.27.58.16034.136.4.15335.184.8.25535.222.218.14034.123.109.4934.67.240.23104.197.72.4034.72.128.3335.226.158.6634.134.4.9135.226.210.85
The Dalles, Oregon, USA (us-west1)
34.127.41.19934.82.57.22535.197.66.24435.197.64.5734.82.193.21535.247.117.035.233.222.22634.82.120.2535.247.5.9935.247.61.15135.233.249.16035.233.172.2335.247.55.3334.83.138.10535.203.184.4834.83.94.15134.145.90.8334.127.116.8535.197.35.18834.105.127.12235.233.191.8434.145.93.13035.233.178.16634.105.18.120104.199.118.1435.185.228.21634.145.16.15134.82.91.7534.82.142.24534.105.35.1934.83.231.9634.168.230.4735.247.46.21434.105.44.2535.185.196.7534.145.39.11334.168.121.44
Los Angeles, California, USA (us-west2)
35.236.22.7735.235.83.17735.236.51.71
Montréal, Québec, Canada (northamerica-northeast1)
35.234.253.10335.203.46.25534.152.60.21035.203.0.635.234.252.15035.203.96.23534.152.34.22934.118.131.3635.203.113.51
London, England, UK (europe-west2)
34.105.198.15135.246.117.5834.142.123.9634.89.124.13934.89.127.5134.105.209.4435.242.138.13335.197.222.22035.189.111.17334.105.219.15434.105.181.13334.89.25.535.246.10.20634.105.131.13334.142.77.1834.89.54.8435.189.94.10535.246.36.6735.234.140.7735.242.174.15835.197.199.2034.89.3.12034.105.156.10735.246.79.7234.105.139.3834.105.147.15734.105.195.12934.105.194.21034.142.79.12334.142.55.5834.142.85.24934.105.148.3835.246.100.6635.246.3.16534.105.176.20935.189.95.16734.89.55.2
Frankfurt, Germany (europe-west3)
35.242.243.25534.159.247.21135.198.128.12634.159.10.5934.159.72.7734.159.224.18734.89.159.13834.159.253.10334.159.244.4335.246.162.18734.89.141.19034.159.65.10634.159.197.3134.89.194.13434.159.252.15534.141.65.21634.159.124.6235.246.130.21334.89.206.2134.89.185.20134.159.171.4635.246.217.22835.242.236.11534.159.148.253
Mumbai, India (asia-south1)
35.200.234.3434.100.205.3734.93.225.1234.93.221.13735.244.24.19835.244.52.179
Eemshaven, Netherlands (europe-west4)
35.204.118.2835.204.216.734.90.52.19135.204.176.2934.90.199.9534.90.145.22634.141.162.735.204.56.18935.204.11.22934.34.66.13134.32.195.8934.32.173.138
Changhua County, Taiwan (asia-east1)
104.199.206.20934.80.173.21235.185.137.114
Tokyo, Japan (asia-northeast1)
34.85.3.19834.146.68.20334.84.4.218
Jurong West, Singapore (asia-southeast1)
34.143.210.11634.143.132.20634.87.134.20234.101.158.8834.101.157.23834.101.184.52
Jakarta, Indonesia (asia-southeast2)
34.101.158.8834.101.157.23834.101.184.52
Sydney, Australia (australia-southeast1)
34.87.195.3634.116.85.14034.151.78.4835.189.13.2935.189.9.8135.244.68.217
Osasco (São Paulo), Brazil (southamerica-east1)
34.151.199.20135.199.122.1934.95.180.12234.95.168.3834.151.235.24134.95.181.1935.199.91.12035.247.197.10935.199.86.4835.199.106.16635.198.1.19135.247.235.12835.247.211.235.247.200.24934.95.177.253
Instances hosted on Amazon Elastic Kubernetes Service (Amazon EKS)
For instances that are hosted on Amazon EKS, add to the allowlist the IP addresses that match your region.Click here for a full list of IP addresses for instances that are hosted on Amazon EKS
US East (N. Virginia) (us-east-1)
18.210.137.13054.204.171.25350.17.192.8754.92.246.22375.101.147.9718.235.225.16352.55.239.16652.86.109.6854.159.176.1993.230.52.22054.211.95.15052.55.10.236184.73.10.8552.203.92.11452.3.47.18952.7.255.5454.196.92.552.204.125.24434.200.64.24318.206.32.25454.157.231.7654.162.175.24454.80.5.1735.168.173.23852.44.187.2218.213.96.4023.22.133.20634.239.90.16934.236.92.873.220.81.24154.197.142.23834.200.121.563.83.72.4154.159.42.1443.229.81.10134.225.255.22054.162.193.16534.235.77.1173.233.169.6354.87.86.11318.208.86.2952.44.90.201
US East (Ohio) (us-east-2)
3.135.171.2918.188.208.2313.143.85.223
US West (Oregon) (us-west-2)
44.237.129.3254.184.191.25035.81.99.30
Canada (Central) (ca-central-1)
52.60.157.6135.182.169.2552.60.59.12835.182.207.12815.222.172.643.97.27.5135.183.191.13315.222.86.12352.60.52.14
Europe (Ireland) (eu-west-1)
54.74.243.24654.195.216.9554.170.208.6752.49.220.10352.31.69.11734.243.112.7652.210.85.11052.30.198.16334.249.159.11252.19.248.17654.220.245.17154.247.22.227176.34.116.19754.155.205.15952.16.81.13954.75.200.18834.248.52.454.228.110.3234.248.104.9854.216.117.22552.50.172.40
Europe (Frankfurt) (eu-central-1)
18.157.231.10818.157.207.3318.157.64.19818.198.116.1333.121.148.1783.126.54.154
Asia Pacific (Tokyo) (ap-northeast-1)
54.250.91.5713.112.30.11054.92.76.24152.68.245.253.114.138.054.249.39.36
Asia Pacific (Sydney) (ap-southeast-2)
13.238.132.1743.105.238.713.105.113.36
South America (São Paulo) (sa-east-1)
54.232.58.18154.232.58.98177.71.134.208
Instances hosted on Microsoft Azure
For instances that are hosted on Azure, add to the allowlist the IP addresses that match your region.Click here for a full list of IP addresses for instances that are hosted on Microsoft Azure
Virginia, USA (us-east2)
52.147.190.201
Legacy hosting
Use these IP addresses for all instances that are hosted on AWS and that were created before 07/07/2020.Click here for a full list of IP addresses for legacy hosting
United States (AWS default)
54.208.10.16754.209.116.19152.1.5.22852.1.157.15654.83.113.5
Canada
99.79.117.12735.182.216.56
Asia
52.68.85.4052.68.108.109
Ireland
52.16.163.15152.16.174.170
Germany
18.196.243.9418.184.246.171
Australia
52.65.128.17052.65.124.87
South America
52.67.8.10354.233.74.59
Step 3: SSH tunneling
If the SSH Servers tab is enabled, follow the instructions on this page to add your SSH server configuration information into Looker.
In the Connections page in the Admin section of Looker, select the SSH Server tab.
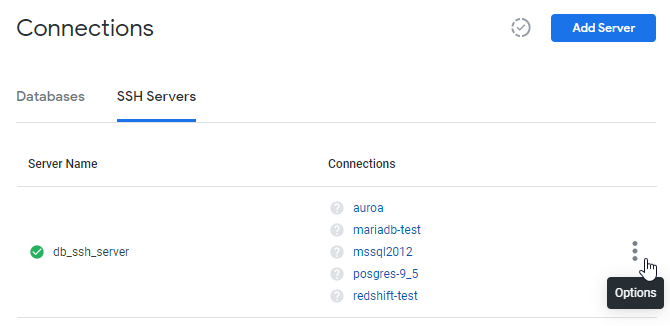
Then select Add Server. Looker displays the Add SSH Server page:
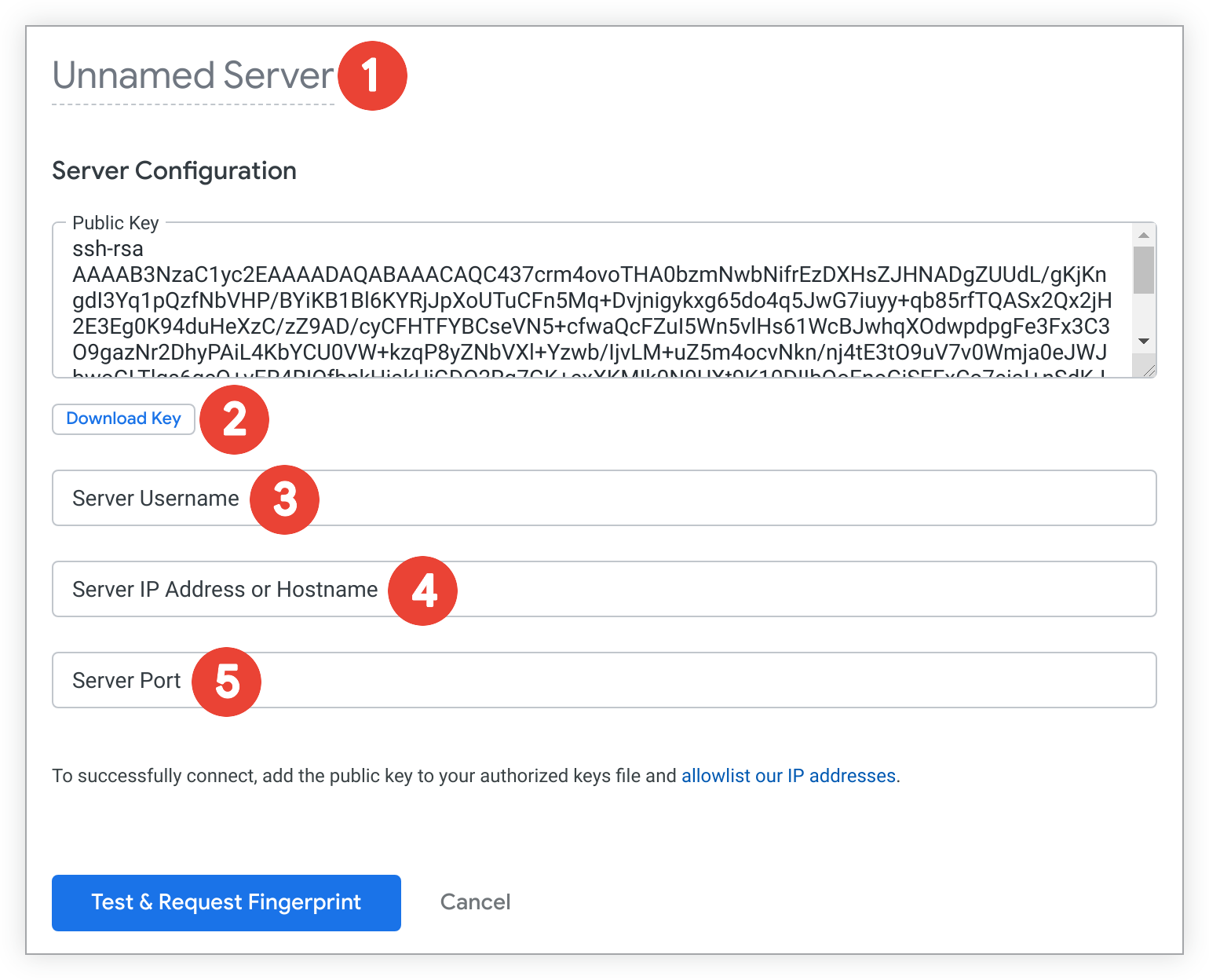
- Enter a name for the SSH server configuration.
- Select Download Key to download the public key to a text file. Be sure to save this file, as you will need to add the public key to your SSH server's authorized key file later.
- Enter the username Looker will use to connect to the SSH server.
- Enter the SSH server IP address or hostname.
- Enter the port number used to connect to the SSH server.
Step 4: Prepare the tunnel host
Add the public key to your authorized_keys file
To authenticate the SSH tunnel session, Looker requires a unique public key (Looker does not support logging in with a password). If the SSH Servers tab is enabled on your instance, you can download the public key to a text file by selecting the Download Key button when you enter your SSH configuration information. If you are configuring your SSH tunnel with the assistance of a Looker analyst, your Looker analyst will provide you with a unique public key.
You will need to prepare your host (either the database server or the tunnel server) by creating a looker user and adding the Looker public key to the Looker .ssh/authorized_keys file. Here's how:
In your command line, create a group called
looker:sudo groupadd lookerCreate user
lookerand its home directory:sudo useradd -m -g looker lookerSwitch to the
lookeruser:sudo su - lookerCreate the
.sshdirectory:mkdir ~/.sshSet permissions:
chmod 700 ~/.sshChange to the
.sshdirectory:cd ~/.sshCreate the
authorized_keysfile:touch authorized_keysSet permissions:
chmod 600 authorized_keys
Using your favorite text editor, add the SSH key provided by your Looker analyst to the authorized_keys file. The key must be all on one line. In some cases, when you retrieve the key from your email, line breaks will be inserted by your email client. If you don't remove them it will be impossible to establish the SSH tunnel.
Add ssh-rsa to your sshd_config file
OpenSSH has disabled ssh-rsa by default, which can cause errors when setting up an SSH tunnel. To resolve this, add the ssh-rsa to your server's list of accepted algorithms. Here's how:
- Edit your
sshd_configfile. This can usually be found at~/etc/ssh/sshd_config. Add the following to your
sshd_configfile:HostKeyAlgorithms +ssh-rsa PubKeyAcceptedAlgorithms +ssh-rsa
Redshift MTU setting
Amazon Redshift users must set their Redshift client and SSH server to an MTU of 1500.
Tunnel security notes
When an SSH tunnel is terminated on the database server, the connection from Looker appears to be a local connection on the database server. Therefore, it defeats the connection-based security mechanisms built into database platforms such as MySQL. For example, it is very common for local access to be granted to the root user with no password!
By default, opening SSH access also allows forwarding of any ports, circumventing any firewalls between Looker and the database host that is terminating the SSH tunnel. This security risk may well be deemed unacceptable. This port forwarding, and the ability to log in to your tunnel server, can be controlled by properly configuring the .ssh/authorized_keys entry for the Looker public key.
For example, the following text could be prepended to the Looker SSH key in your authorized_keys file. Note that this text MUST be customized for your environment.
no-pty,no-X11-forwarding,permitopen="localhost:3306",permitopen="localhost:3307",
command="/bin/echo Login Not Permitted"
See the man ssh and man authorized_keys Linux documentation for examples and full details.
Next steps
If the SSH Servers tab is enabled on your instance, return to the Add SSH Server page, and select Test & Request Fingerprint to verify your connection to the SSH server. Looker will show a screen with the new SSH configuration and options to download or view the public key, and to view the unique fingerprint of the SSH server configuration.
Then, on your database Connection Settings page:
- Enable the SSH Server toggle and select your SSH server configuration from the drop-down list.
- In the Remote Host and Port fields, enter the IP address or hostname and port number of your database.
If you are configuring your SSH tunnel with the assistance of a Looker analyst, notify your Looker analyst that you are ready to test the SSH tunnel. Once they confirm that the tunnel is established, they will provide you with the port number for the Looker side of the SSH tunnel.
Then, on your database Connection Settings page:
- Enter
localhostin the Remote Host field. - In the Port field, enter the port number for the Looker side of the SSH tunnel that was provided by your Looker analyst.
Toggle off Verify SSL Cert on your database Connections page.
SSL Certificates are not supported when setting up an SSH tunnel to your database from Looker. Instead, the SSH key that you added in step 4 provides the handshake security between Looker and your database.
