Cloud Armor: enhancing security at the edge with Adaptive Protection, expanded coverage scope, and new rules
Emil Kiner
Senior Product Manager, Cloud Armor
Try Google Cloud
Start building on Google Cloud with $300 in free credits and 20+ always free products.
Free trialCloud Armor, Google Cloud’s DDoS defense service and web-application firewall (WAF) helps customers protect their websites and services from denial of service and web attacks every day using the same infrastructure, network, and technology that has protected Google’s own internet-facing properties from the largest DDoS attacks reported. To stay ahead of the evolving threat landscape, we’re continuing to enhance protections delivered at the edge of Google’s network through innovations in Cloud Armor.
First, we’re releasing the preview of Cloud Armor Adaptive Protection, a machine learning-powered capability to protect your applications and services from Layer 7 DDoS attacks. We have been building and maturing this technology with internal and external design partners and testers over the last few years. All Cloud Armor customers can try it at no extra charge during the preview period.
To further help customers keep their networks safe with Cloud Armor, we are announcing general availability of four new preconfigured WAF rules and a reference architecture to help Google Cloud customers protect themselves from the OWASP Top 10 web-app vulnerability risks. Finally, we are introducing preview releases of Cloud Armor protection for content served from Cloud CDN or Google Cloud Storage backend buckets, as well as per-client rate limiting.
Adaptive Protection: Detect suspicious traffic early for rapid attack mitigation
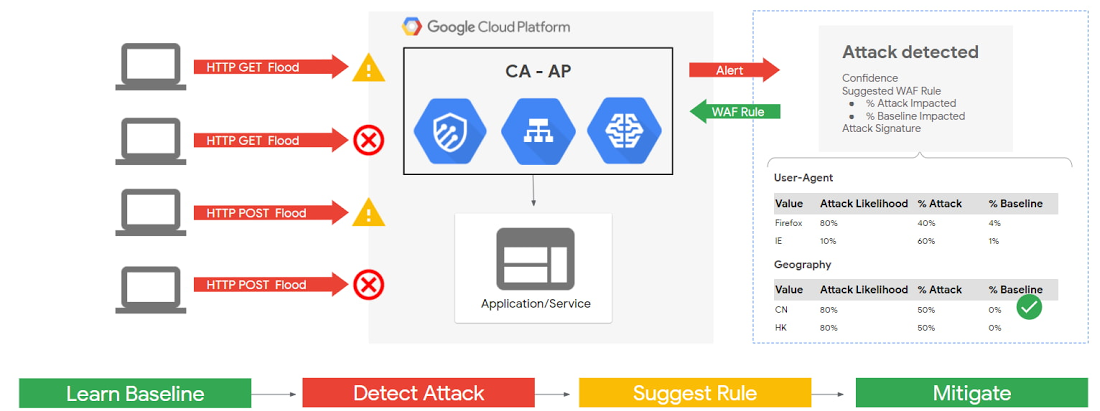
First, let’s take a deeper dive into what Adaptive Protection has to offer. Adaptive Protection monitors traffic out-of-band and learns what normal traffic patterns look like, developing and constantly updating a baseline on a per-application/service basis. Adaptive Protection quickly identifies and analyzes suspicious traffic patterns and provides customized, narrowly tailored rules that mitigate ongoing attacks in near-real time.
Applications and workloads exposed to the internet are at constant risk of DDoS attacks. While L3/L4 volumetric- and protocol-based attacks are effectively mitigated at Google’s edge, targeted application layer (Layer 7) attacks are still a constant risk. In L7 attacks, well-formed, legitimate web requests are generated by automated processes from compromised devices (e.g., botnets) at volumes high enough to saturate the web site or service. This problem has grown increasingly acute as the size and frequency of DDoS attacks increases with the proliferation of widely-available DDoS attack tools and for-hire botnets. Since attacks can come from millions of individual IPs, manual triage and analysis to generate and enforce blocking rules becomes time and resource intensive, ultimately allowing high-volume attacks to impact applications.
How Adaptive Protection works to detect potential attacks
Adaptive Protection is the result of a multi-year research and development effort conducted by teams across Google, with feedback and testing from external technology partners and customers. Security operations teams receive three primary benefits from Adaptive Protection: 1) early alerts on anomalous requests on a per-backend-service basis, 2) dynamically generated signatures describing the potential attack, and 3) a suggested custom WAF rule to block the offending traffic. Alerts from Adaptive Protection are sent to the Cloud Armor dashboard, Security Command Center, and Cloud Logging with notification of an impending attack. The attack-specific signatures and WAF rule are the result of a second set of ML models, comprised of dozens of traffic features and attributes. Adaptive Protection’s models are built using TensorFlow in order to efficiently and accurately detect application level attacks and identify the best way to mitigate them. The WAF rule is presented to the user as part of the alert issued for the detection. Users are then able to choose to deploy the proposed WAF rule in near-real time to block the attack at the edge of Google’s network. This early detection helps the teams rapidly mitigate attacks far upstream from cloud infrastructure and services.
How Project Shield uses Adaptive Protection: a case study


Adaptive Protection is used by Project Shield, a service from Google that helps protect news, human rights, and election monitoring sites from DDoS attacks. Adaptive Protection has allowed the team to greatly increase efficiency while offering insight, analysis, and more effective mitigations of attacks.
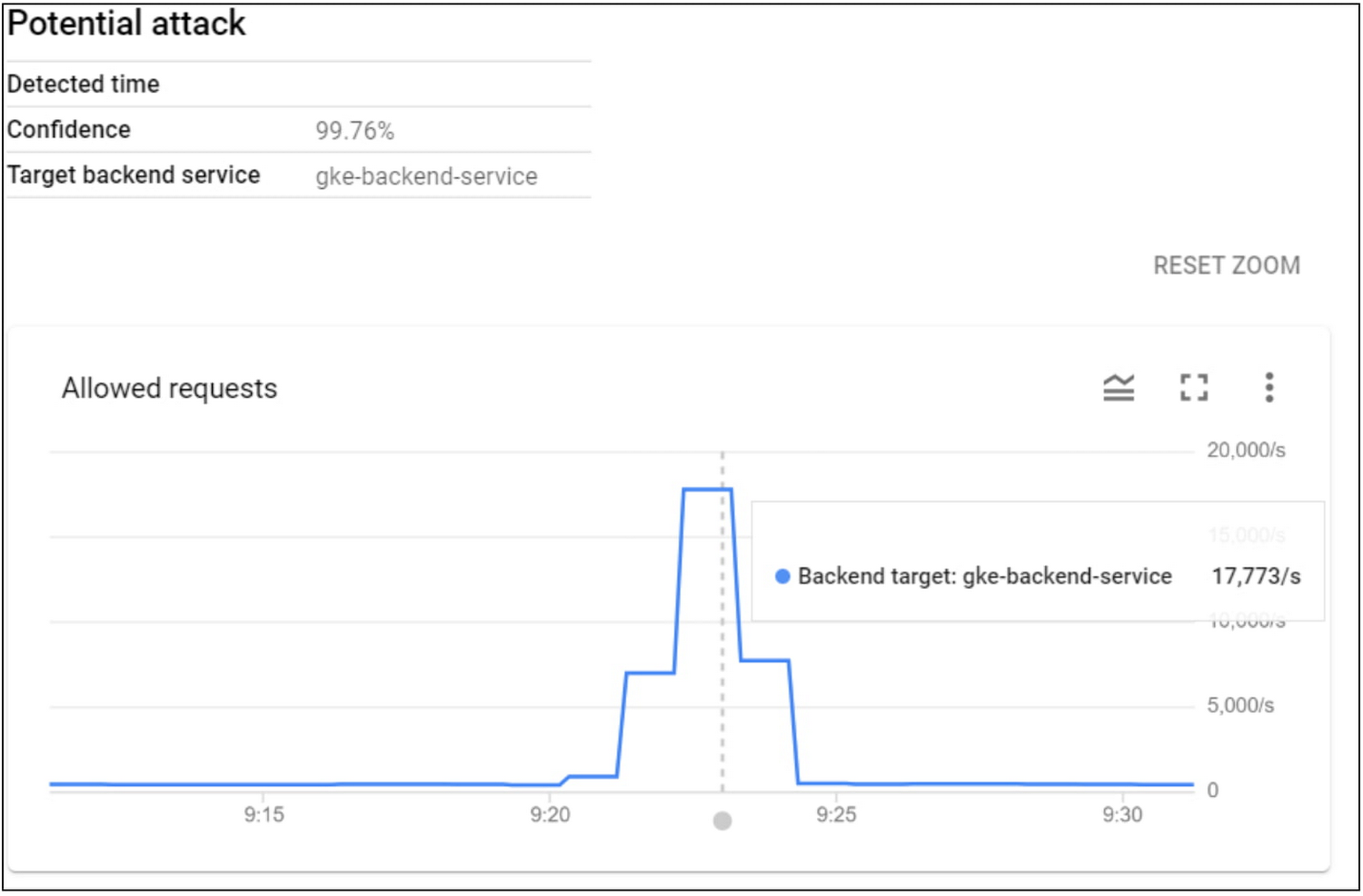
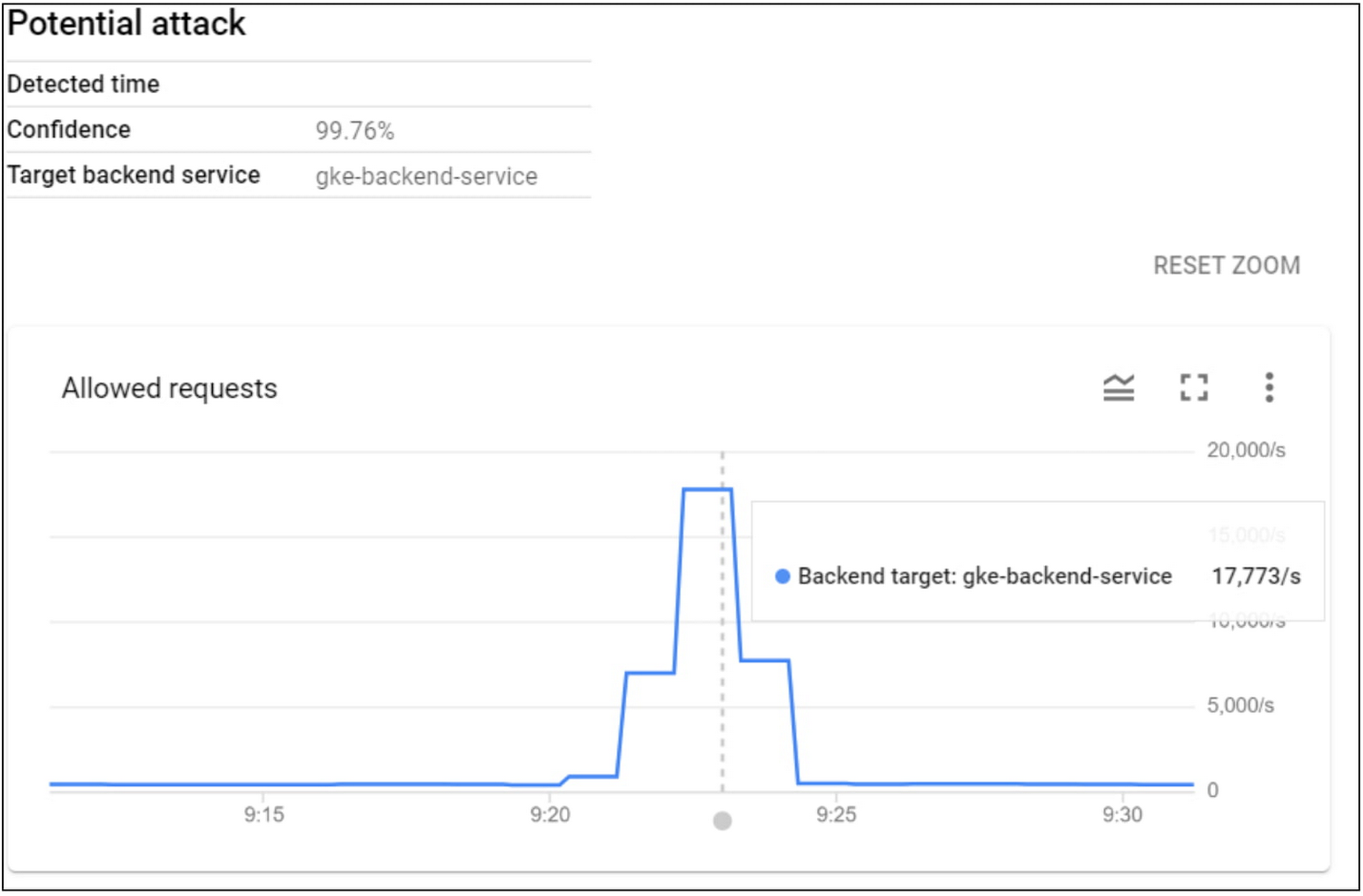
For example, the Project Shield team recently received the alert in the image above. This attack, an HTTP Flood, peaked above 17,700 requests per second (RPS) which represented an anomalous increase from normal traffic volumes for this endpoint.
Adaptive Protection detected and alerted on the attack a few seconds after it started. Critically, the alert arrived almost 2 minutes before the attack ramped up to its eventual peak, and it came with a proposed mitigation.
The alert that arrived was enriched by our signature detection models with a thorough analysis on the nature and origins of the attacks, and suggested a Cloud Armor WAF rule to block the attack. An example of the signature of the attack provided is captured in the below two images.
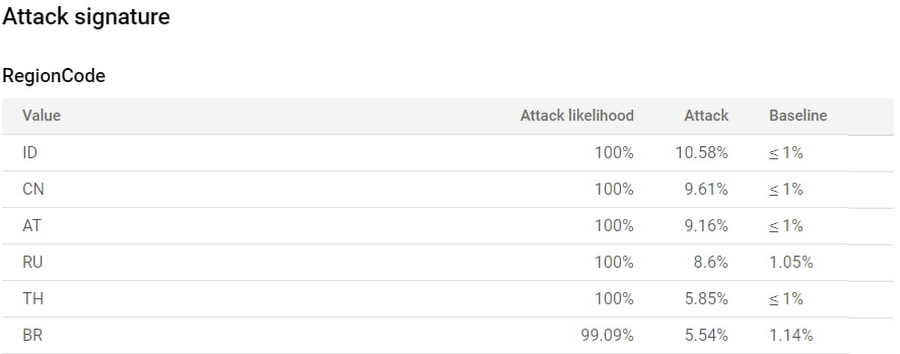
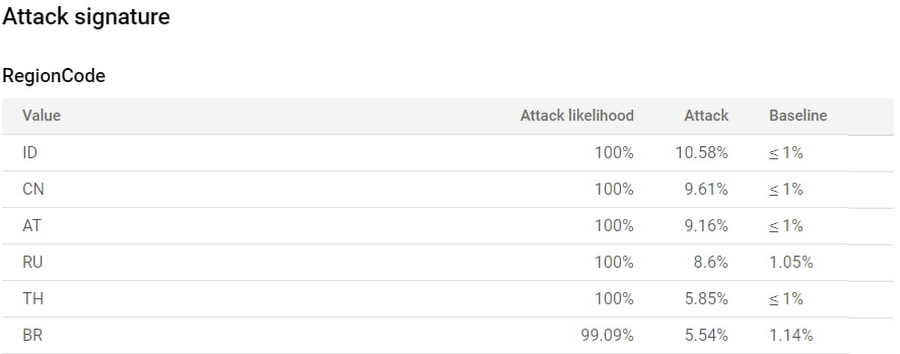
The team was able to immediately see the regions from which the attack traffic was originating, as well as a side-by-side comparison of the prevalence of the implicated source regions during the event to their prevalence in the established baseline. The six implicated regions collectively contributed ~50% of the attack traffic during the event, while normally they contribute less than 1% of all traffic, according to the baseline model.
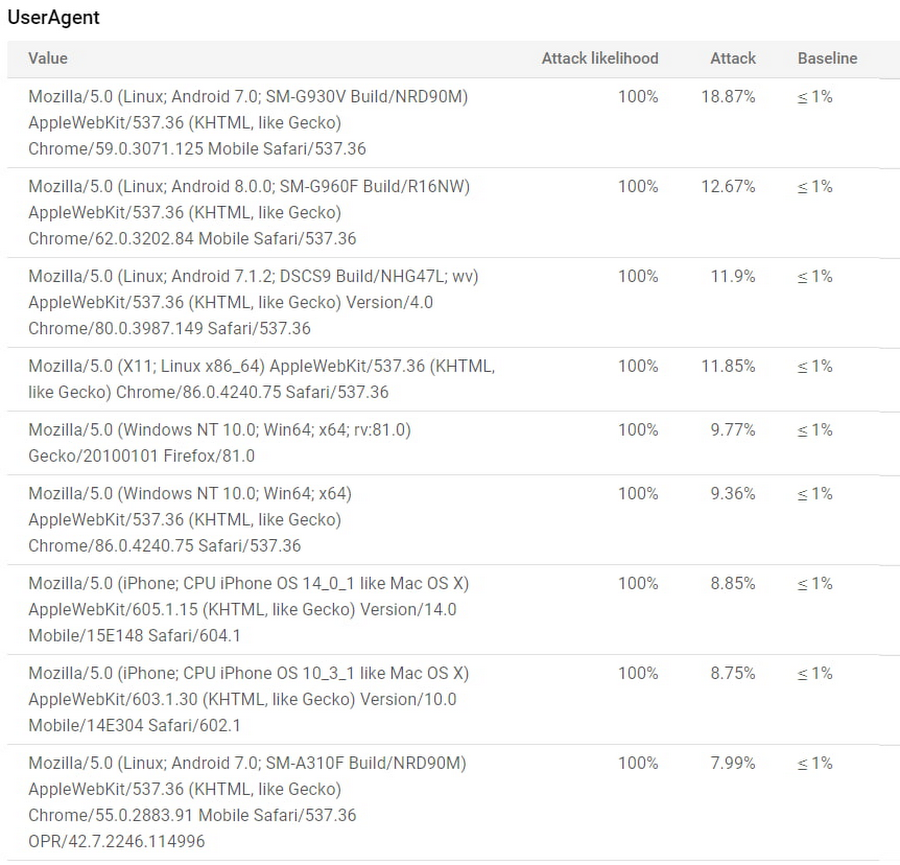
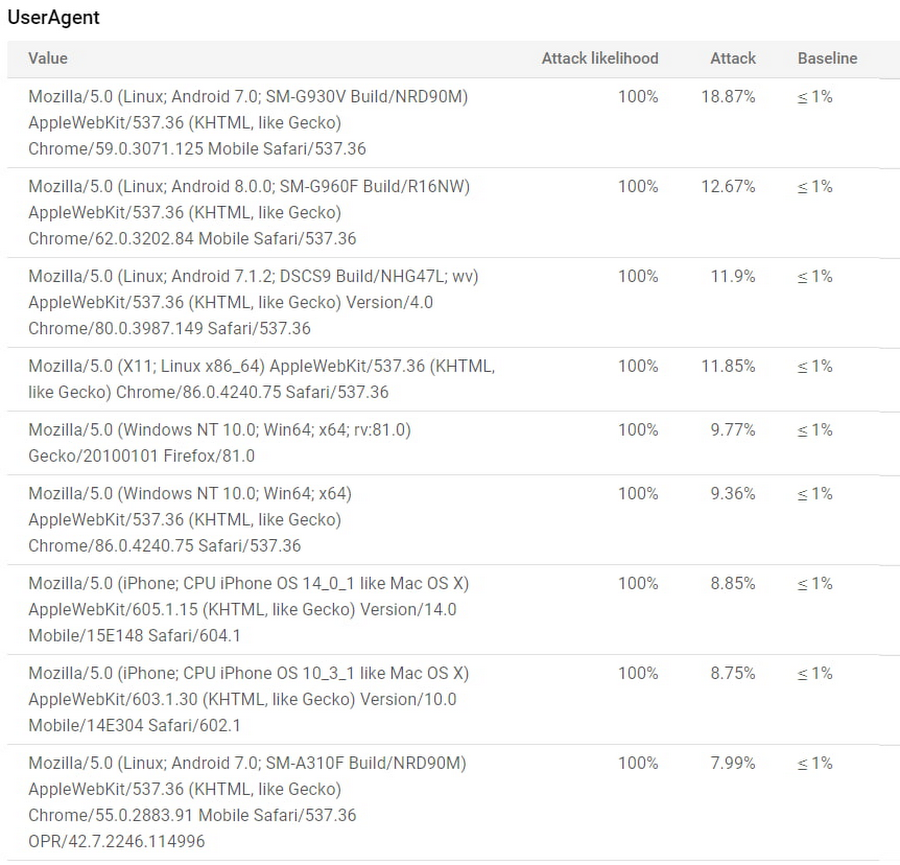
A similar analysis of client types surfaced nine distinct user-agents that contributed ~100% of the attack traffic, whereas in the baseline model those same nine appeared in less than 1% of requests. This is not surprising, as the implicated user-agent strings corresponded to older mobile and desktop browser versions that could be utilized by common attack tools while legitimate clients typically use up-to-date browser versions.
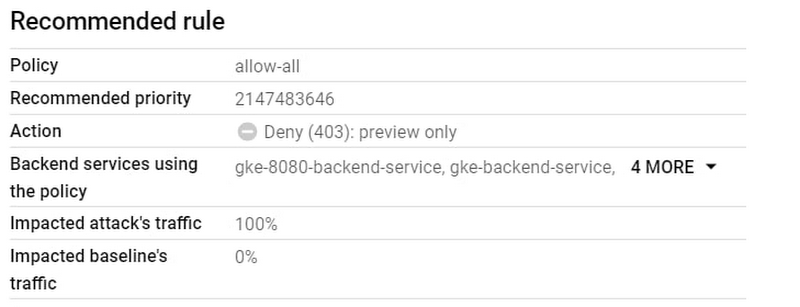
Finally, the alert that was generated in the first few seconds of the attack included not only the full signature details described above but also a recommended Cloud Armor WAF rule narrowly tailored to block only the attack traffic and allow genuine requests through. With the alert, the analysis, and the proposed WAF rule, the defenders were enabled to respond to the attack in near real time without having to spend precious minutes or hours analyzing logs to synthesize a mitigation.
Get started with Adaptive Protection
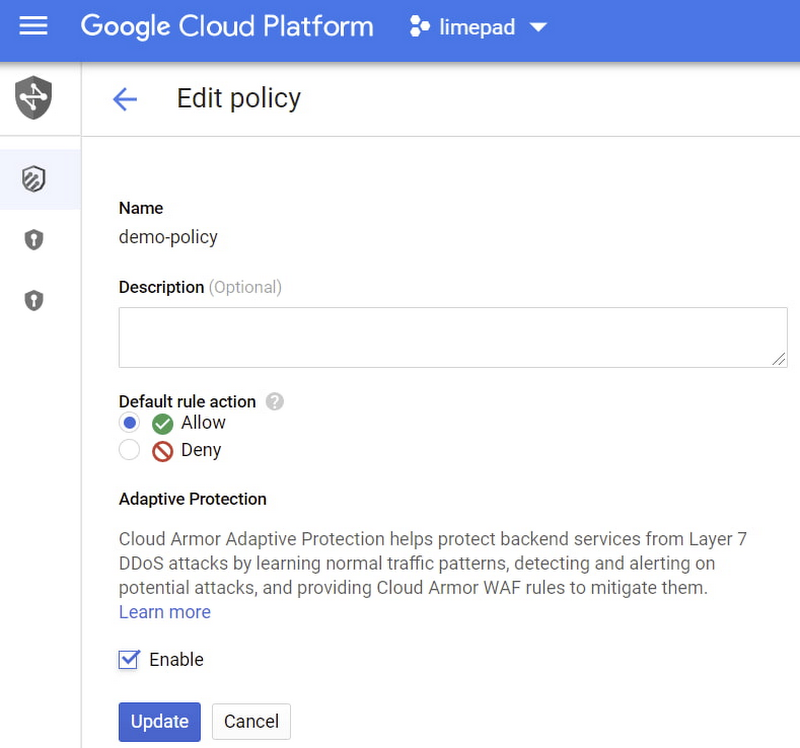
Get started today by enabling Adaptive Protection in existing security policies by checking the “enable” check box when editing the policy from your Cloud Armor section in the Console. All Cloud Armor customers can try out Adaptive Protection while it is in preview at no extra charge. When it reaches general availability, Adaptive Protection’s attack detection and notification will continue to be included in Cloud Armor Standard, while attack signature identification and mitigating rules suggestions will only be available as part of our recently announced Cloud Armor Managed Protection Plus subscription.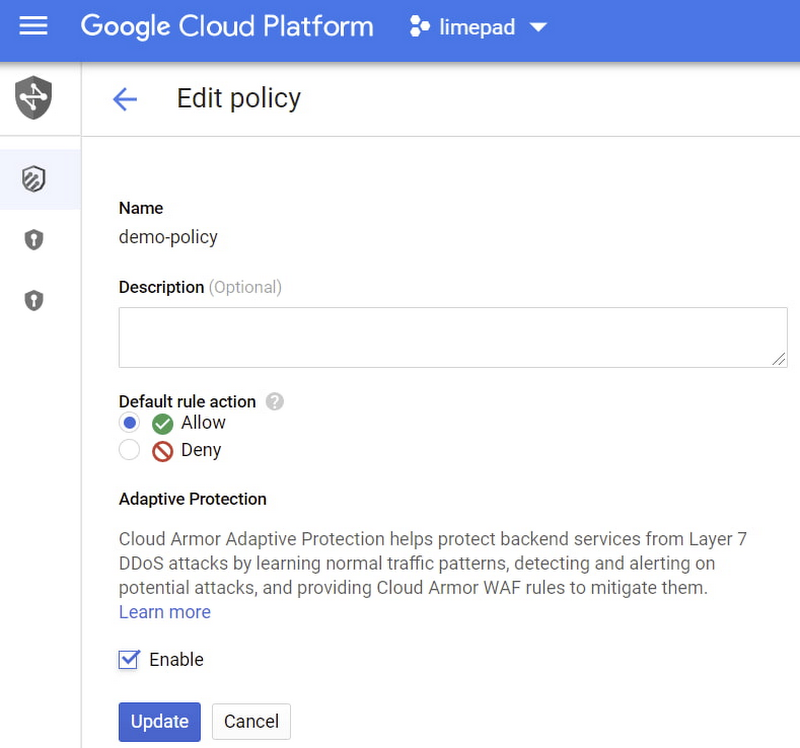
New rules, reference architecture, and protections
Enterprises must satisfy requirements for external compliance frameworks, like PCI DSS, as well as internal security goals. Cloud Armor enhancements make this easier. Four additional preconfigured WAF rules are now generally available to help mitigate OWASP Top 10 web-app vulnerability risks. Together, they help protect your websites and services from attacks such as HTTP request smuggling and unwanted scanners and crawlers:
Scanner Detection
PHP Injection
Session Fixation
Protocol Enforcement
Additionally, we have published a whitepaper and reference architectures to help you understand how to leverage and configure a variety of products and controls on Google Cloud to help protect yourself from the OWASP Top 10 and meet compliance requirements.
We are also expanding the scope of protection on Google Cloud by introducing the preview of Cloud Armor protection for workloads serving content from Cloud CDN as well as Google Cloud Storage (GCS) backend buckets. Now you can enforce geography-based access policies and block unwanted users in order to comply with licensing or regulatory requirements by deploying Cloud Armor edge security policies in front of your CDN or GCS enabled services to filter requests before they are served from cache.
Finally, we are announcing the preview release of per-client rate limiting in Cloud Armor by introducing two new rule actions: throttle and rate-based-ban. Now users can help ensure the availability of their applications, prevent abuse, and mitigate malicious activity like credential stuffing by configuring Cloud Armor to throttle clients to a specified request rate or block all traffic from abusive clients. Rate limiting rules will be available to all Cloud Armor customers (both Standard and Managed Protection Plus) in the upcoming weeks.
With all of these advancements Cloud Armor continues to provide customers around the world with cloud-native protections that help keep their networks safe from evolving threats. To learn more, explore the following resources:



