Cloud CISO Perspectives: February 2023

Phil Venables
VP/CISO, Google Cloud
Try Google Cloud
Start building on Google Cloud with $300 in free credits and 20+ always free products.
Free trialWelcome to February’s Cloud CISO Perspectives. This month, we’re going to take a look at one of the most important issues our industry faces right now: securing the software supply chain. At Google Cloud, we’ve been heavily invested in creating a layered approach to software supply chain security, which I talk about in my column below.
But first, I want to acknowledge that it has been one year since Russia invaded Ukraine. In addition to the immeasurable impact on the lives across the region, this also marks the first time that cyber operations have played such a prominent role in a world conflict. There were more cyberattacks against Ukraine from January to April than there had been in the entire eight years preceding the invasion.
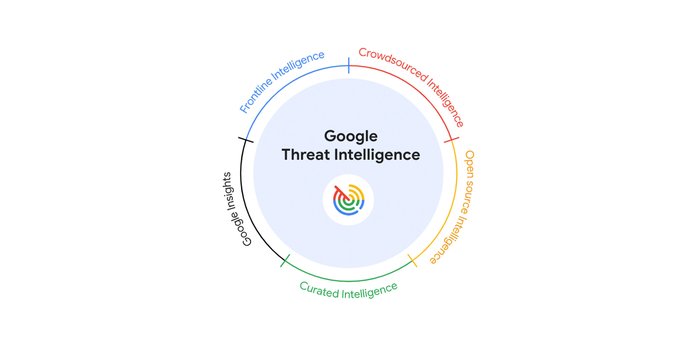
We’ve reflected on this further in “The Fog of War,” a new report by Google’s Threat Analysis Group (TAG) and Mandiant. It was also a primary topic of discussion at the Munich Cyber Security Conference, where policymakers, business leaders, and technology experts discussed how the role of transformational technologies can help build more resilient cyber defenses. We’re continuing to provide support for the Ukrainian government and aid organizations before, during, and after security events.
As with all Cloud CISO Perspectives, the contents of this newsletter are posted to the Google Cloud blog. If you’re reading this on the website and you’d like to receive the email version, you can subscribe here.
SBOM+SLSA = Safer software
As the complexity of today’s software has increased, and the role it plays in businesses become even more vital than before, so too has securing the software supply chain grown more important. Google has pledged $10 billion to advancing cybersecurity, and we are committed to protect key open source components that are vital to our public infrastructure and organizations around the world. While high-profile security incidents such as SolarWinds and Log4j have helped convince government and business leaders of the importance of securing the software supply chain, there is still much work to be done.
Securing the software we depend on is a key priority for defenders and something Google is committed to helping organizations do. At Google Cloud, we strongly believe that using a software bill of materials (SBOM) in conjunction with our open-source Supply chain Levels for Software Artifacts (SLSA) framework can create a more secure and more resilient software supply chain ecosystem.
An SBOM will tell you what’s in the software, and if there are any publicly-disclosed vulnerabilities that you need to update. Those are important, but that still leaves the supply chain at risk of exploitation: An SBOM won’t tell you if the software was produced with security and integrity in mind.
In the case of SolarWinds, having an SBOM wouldn’t have helped stop the attack or detect the breach earlier because the attack vector relied on rogue software implanted through a software build system compromise. To know that you can trust the software, you also need to understand how the organization that produced the software is controlled.
Nearly a decade in development, the SLSA framework can help you analyze end-to-end software supply chain risk. It creates a set of incremental, enforceable security guidelines that automatically create auditable metadata. It’s a verifiable way to assure consumers that the software they use hasn’t been tampered with.
Organizations need to know what is in the software and have the ability to assess the integrity of how the software is built. Combining SBOM and SLSA creates the framework needed to answer this. As public cloud providers apply SBOM and SLSA to their own software supply chains, their customers will automatically benefit from the improved security.
We have also been working on products so organizations can utilize these frameworks in their software development processes. Our Software Delivery Shield solution, announced at Google Cloud Next in October 2022, is a fully-managed software supply chain security solution with a modular set of capabilities to help developers, DevOps, and security teams build secure applications. It supports organizations at different stages of software development maturity, so they can tailor the solution to their specific needs and security priorities.
We also have our Assured Open Source Software (OSS) service that can help development teams incorporate the same OSS packages that Google uses into their developer workflows. The software curated by the Assured OSS service is regularly scanned for vulnerabilities, updated, and tested by Google, is verifiably signed by Google, and is SLSA compliant.
I’ve spoken at length about how at Google Cloud we believe in a shared fate approach to security. While that’s true for identifying security responsibilities with our customers, it’s also true for how we approach industry-wide problems such as securing the software supply chain. Software developers and security leaders can come together to make software more resilient against cyberattacks to continue to build global trust in technology.
In case you missed it
Here are the latest updates, products, services, and resources from our security teams this month:
Join our quarterly Security Talks on March 22: Our quarterly digital event Google Cloud Security Talks explores the latest security products, trends, and innovations coming from our cybersecurity leaders and practitioners. In our first session of the year, we combine several short discussions on topics including modernizing your security operations and building security into your cloud transformation journey with a deep dive on the latest threat intel trends from our Mandiant research teams. Register now.
Security takeaways from our report on Russian cyber operations against Ukraine: As a new Google report demonstrates, organizations are at risk from the types of attacker activities that Russia has been using against Ukraine. Executive leaders who understand these threats are better positioned to help their organization reduce risk. Here's why.
Security Leaders Survival Guide: How to tell if your team is on the right path: Digital transformations can be a difficult exercise, with concerns or requirements for data compatibility, sovereignty, resiliency, and security all playing a role. For the third blog in this series, we offer cloud security advice for financial services security leaders. Read more.
Health-ISAC and Google Cloud partner to build more resilient healthcare: Working with the Health-ISAC Threat Operations Center, Google Cloud security engineers have connected the Health-ISAC Indicator Threat Sharing (HITS) feed directly to our Chronicle Security Operations information and event management. HITS allows Health-ISAC members to easily connect and quickly share threat intelligence through machine-to-machine automation. Read more.
Black History Month: Celebrating the success of Black founders with Google Cloud: F8th: Vivene Salmon Gagné, co-founder and chief legal officer for cybersecurity startup F8th, talks about how Google Cloud helped F8th grow and develop its behavioral biometric algorithms. Read more.
Vroom! Google Cloud joins Catena-X to help car makers build a sovereign data ecosystem: Google Cloud brings to the Catena-X Automotive Network Association secure and sovereign data management, data analytics, cloud-first integration of advanced AI technologies, and open source efforts to help create a shared service ecosystem. Read more.
How Google Cloud Armor helps Broadcom block DDoS Attacks: As Broadcom migrated its enterprise security solution infrastructure from Amazon Web Services to Google Cloud, defending the environment’s network security infrastructure remained a top priority. Here’s how we helped Broadcom protect against DDoS attacks. Read more.
Three steps to protect your software supply chain today: A new paper from Google Cloud analyzes recent high-profile software supply chain attacks and recommends three actions your organization can take to better protect your software supply chain. Read more.
The top five global data and AI trends in 2023: Global organizations have increased customer trust and productivity by improving how they discover, classify, and manage their structured and unstructured data. Our 2023 Data and AI Trends report can help security leaders and teams learn more about why knowing your data is vital to your organization. Read more.
Google Cloud security tips, tricks, and updates
Mandiant now supports Attack Surface Management for Google Cloud: How do adversaries see your network? You can see what they see with Mandiant Attack Surface Management for Google Cloud, which can enable customers to centralize visibility into cloud-hosted external assets. Read more.
Confidential GKE Nodes now available on Compute Optimized C2D VMs: Organizations which rely on Google Kubernetes Engine can enhance the security of GKE clusters or node pools, which includes keeping data encrypted in memory with dedicated keys generated and managed by the processor. Read more.
Harden Kubernetes clusters, monitor workload compliance at scale: Evaluate your new and existing applications for PCI DSS compliance with Google Cloud’s Policy Controller, which enables the enforcement of fully programmable policies for your clusters. Read more.
New Google Cloud Firewall capabilities now available: Our unique, fully-distributed architectural approach to firewalls is a scalable, built-in service with advanced protection capabilities that can help strengthen and simplify your security posture, and implement Zero Trust networking, for cloud workloads. Here's how to get started.
How to integrate Cloud SQL for PostgreSQL or MySQL in your authentication flow: Hardening a complex application is a challenge, especially for applications that include multiple layers with different authentication schemes. With our new Integrated IAM authentication capability, customers can leverage end-to-end authentication for their applications and while applying our robust auditing capabilities. Read more.
How to secure Cloud Run deployments with least privilege access: With Cloud Run, developers can quickly deploy production web apps and APIs on a serverless environment running on top of Google Cloud. Here’s how to improve Cloud Run security by applying the principle of least privilege to inbound and outbound scenarios. Read more.
How to use Anthos to improve governance and security for platforms and apps: Anthos is our secure container application platform that runs on premises and in the cloud, with integrated and easy-to-operationalize security features connected to a centralized control plane in the Google Cloud. It can be used to implement security policies across distributed platforms and applications. Learn how.
Document AI Workbench can train document extraction models for production use cases: AI for security is not just about anomaly and malware detection: It can have huge benefits for workflow and productivity enhancements. Read more.
Compliance and Controls
How Google Cloud is preparing for NIS2 and supporting a stronger European cyber ecosystem: To help combat the threat of online data theft, the EU passed the Network and Information Security Directive 2.0 (NIS2), which outlines new security requirements for companies operating in critical sectors. Google Cloud is committed to ensuring that our cloud platform and security tools support the highest standard of compliance. Read more.
Introducing Google Workspace security guidance to address Canadian data security requirements: New security guidance can help Canadian government agencies introduce Google Workspace tools while adhering to Canadian government compliance standards. Read more.
Google Cloud Security Podcasts
We launched a weekly podcast focusing on Cloud Security in February 2021. Hosts Anton Chuvakin and Timothy Peacock chat with cybersecurity experts about the most important and challenging topics facing the industry today. This month, they discussed:
How Google does vulnerability management: Vulnerability prioritization, impact assessment, vulnerability management processes unique to Google, and the vital metrics it all gets measured by are the hot topics discussed with Ana Oprea, the European lead for our Vulnerability Coordination Center. Listen here.
Hunting in the clouds: Threat hunting lessons, learned the hard way: From defining what it means to hunt threats online to what threat detection specialists can learn from threat hunters, we dive deep into this often-misunderstood world with John Stoner, principal security strategist, Google Cloud. Listen here.
How Google Cloud secures its usage at massive scale: Security team, secure thyself. How does Google Cloud secure its own massive, diverse use of its own resources? Karan Dwivedi, security engineering manager for enterprise infrastructure protection explains how we do what we do for you, for ourselves. Listen here.
High-velocity detection, high-complexity response: Tim and Anton argue a lot about what kind of detection is best: fully bespoke and homemade or scalable off-the-shelf. David Seidman, head of detection and response at Robinhood, helps them settle that debate and others including: What matters more, detection skills or cloud skills? What’s most effective to focus on when building a team? And what are your favorite telemetry data sources for detection in the cloud? Listen here.
To have our Cloud CISO Perspectives post delivered every month to your inbox, sign up for our newsletter. We’ll be back next month with more security-related updates.