Packet Mirroring: Visualize and protect your cloud network
Mahesh Narayanan
Product Manager, GKE
Yang Liang
Product Marketing Manager
Editor’s note: As of March 4, 2020, Packet Mirroring is generally available.
As networks grow in complexity, network and security administrators need to be able to analyze and monitor network traffic to respond to security breaches and attacks. However, in public cloud environments, getting access to network traffic can be challenging.
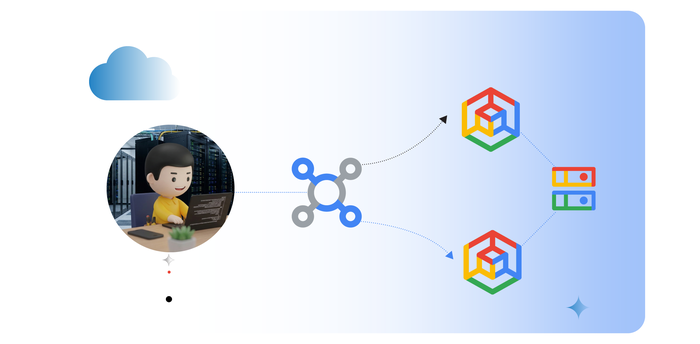
Many customers use advanced security and traffic inspection tools on-prem, and need the same tools to be available in the cloud for certain applications. Our new Packet Mirroring service is now in beta, and allows you to troubleshoot your existing Virtual Private Clouds (VPCs). With this service, you can use third-party tools to collect and inspect network traffic at scale, provide intrusion detection, application performance monitoring, and better security controls, helping you ensure the security and compliance of workloads running in Compute Engine and Google Kubernetes Engine (GKE). For more, watch this video.
For instance, Packet Mirroring lets you identify network anomalies within and across VPCs, internal traffic from VMs to VMs, traffic between end locations on the Internet and VMs, and also traffic between VMs to Google services in production.
Packet Mirroring is available in all Google Cloud Platform (GCP) regions, for all machine types, for both Compute Engine instances and GKE clusters.
In short, Packet Mirroring allows you to:
Help ensure advanced network security by proactively detecting threats. Respond to intrusions with signature-based detection on predetermined attack patterns, and also identify previously unknown attacks with anomaly-based detection.
Improve application availability and performance with the capability to diagnose and analyze what's going on over the wire instead of relying only on application logs.
Support regulatory and compliance requirements by logging and monitoring of transactions for auditing purposes.


“Google Cloud's new Packet Mirroring service accelerates our cloud adoption by giving us the visibility we need to secure our applications and protect our most precious asset, our customers.” - Diane Brown, Senior Director IT Risk Management, Ulta Beauty
Packet Mirroring is important for enterprise users from both a security and networking perspective. You can use Packet Mirroring in a variety of deployment setups for different network topologies, such as VPC Network Peering and Shared VPC. In Shared VPC environments, for instance, an organization may have packet mirroring policies and collector backends that were set up by the networking or security team in the host project; the packet mirroring policy, meanwhile, is enabled in the service projects where the developer team runs its applications. This centralized deployment mode improves the ease of use of Packet Mirroring for security and networking teams, at the same time making it transparent to the development teams.
Packet Mirroring is natively integrated with Google’s Andromeda SDN fabric. This approach keeps Packet Mirroring performance and management overhead low, as the receiving software appliances running on the collector backends don’t need to perform any decapsulation operation to parse the receive packet mirrored data.
Partnering for network security
We’ve been working with several partners to help us test and develop Packet Mirroring, and have received valuable feedback along the way. Here are our Packet Mirroring partners, and how they work with the tool:
- Awake Security - Awake Delivers Security with Network Traffic Analysis in Google Cloud
- Check Point - CloudGuard IaaS Now Integrates with Google Cloud Packet Mirroring
- Cisco - Cisco Stealthwatch Cloud and Google Cloud continue partnership to secure customers
- Corelight - Finding Truth in the Cloud: Google Cloud Packet Mirroring & Corelight Network Traffic Analysis
- cPacket Networks - Googling Packets Inside Google Cloud
- ExtraHop Networks - ExtraHop Reveal(x) + Google Cloud Packet Mirroring
- Flowmon - Enhancing Network Visibility & Security in Google Cloud
- Ixia, a Keysight Business - Improving cloud visibility with CloudLens and Packet Mirroring
- Netscout - NETSCOUT Extends Its Visibility Without Borders into Google Cloud with Packet Mirroring
- Palo Alto Networks - Announcing the new VM-Series Integration with Google Cloud Packet Mirroring Service
Help ensure security and compliance in the cloud
Our goal is to give you the right advanced security solutions for connecting your business to Google Cloud. With Packet Mirroring, you can reduce risk, diagnose to ensure the availability of your mission-critical applications and services and meet compliance requirements. Click here to learn more about GCP’s cloud networking portfolio and reach out to us with feedback at gcp-networking@google.com.