Security, simplified: Making Shielded VM the default for Compute Engine
Jasika Bawa
Product Manager, Google Cloud
Last April we announced the general availability of Shielded VM—virtual machine instances that are hardened with a set of easily configurable security features to ensure that when your VM boots, it’s running a verified bootloader and kernel. To make it accessible to everyone, we offered Shielded VM at no additional charge.
To continue improving the safety and security of our ecosystem, today we’re making Unified Extensible Firmware Interface (UEFI) and Shielded VM the default for everyone using Google Compute Engine—at no additional charge. This provides defense-in-depth hardening features to all supported VM instances, including protection from:
Malicious guest system firmware, UEFI extensions, and drivers
Persistent boot and kernel compromise in the guest OS
VM-based secret exfiltration and replay
“Using Shielded VM to run our secure services on Google Cloud Platform has improved our security posture, while being quick and simple to implement,” said Michael Capicotto, Cloud Security Architect at Two Sigma. “Making this the default for Compute Engine is a great next step toward improving security for all.”
What's new
Since Shielded VM became generally available, we’ve continued to add support for common use cases based on your feedback and feature suggestions.
Adoption across Google Cloud: In addition to making Shielded VM the default across Google Compute Engine, several VM-based Google Cloud services, including Cloud SQL, Google Kubernetes Engine, Kaggle, and Managed Service for Microsoft Active Directory, are now using Shielded VM as their underlying infrastructure.
Migration support: Starting with version 4.5, Migrate for Compute Engine (formerly Velostrata) includes support for migration of UEFI-based VMs from on-prem to Shielded VM in Google Compute Engine.
The power to choose
In addition to the new features we’ve added, Shielded VMs now offer more flexibility around the operating system images you can use and how you get them.
Support across multiple operating systems: For an extensive list of operating systems that support Shielded VM features, as well as which projects these can be found in, please see Google Compute Engine images.
Marketplace for an open ecosystem: Shielded VM images are also available in the GCP Marketplace. These are brought to you in collaboration with Deep Learning VM, as well as our third-party partners at Center for Internet Security (CIS) and Server General.
"Our goal is to help our customers to secure their data and achieve regulatory compliance with ease,” said Raj Sharma, CEO at Server General. “Moving our MySQL and PostgreSQL images to Shielded VM has allowed us to provide verifiable security by extending the trust model from the platform to the application server layer, and ultimately to data that is stored in a database or a file server."
Custom Shielded-ready images: You can also use your own keys to sign binaries and create custom images for your application or workload. These can be imported to Compute Engine at no additional charge.
Get started with a simplified UI
It’s now even easier to get started with Shielded VM via the Cloud Console, gcloud, or API. Let’s look at how to create a Shielded VM from the console.
First, visit the "VM instances" option from the left navigation bar in the Compute Engine console. Then select “New VM instance” from the menu.
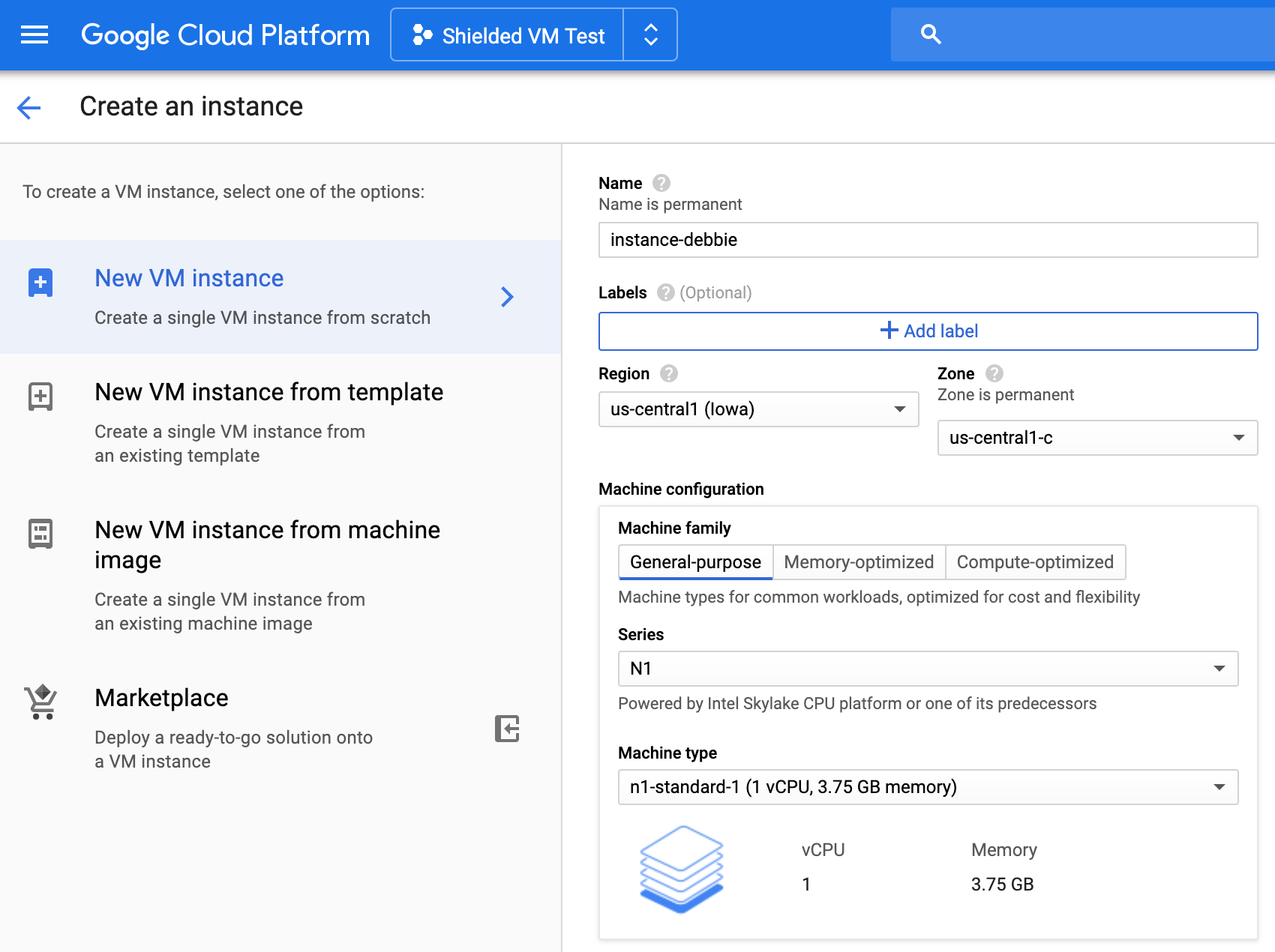
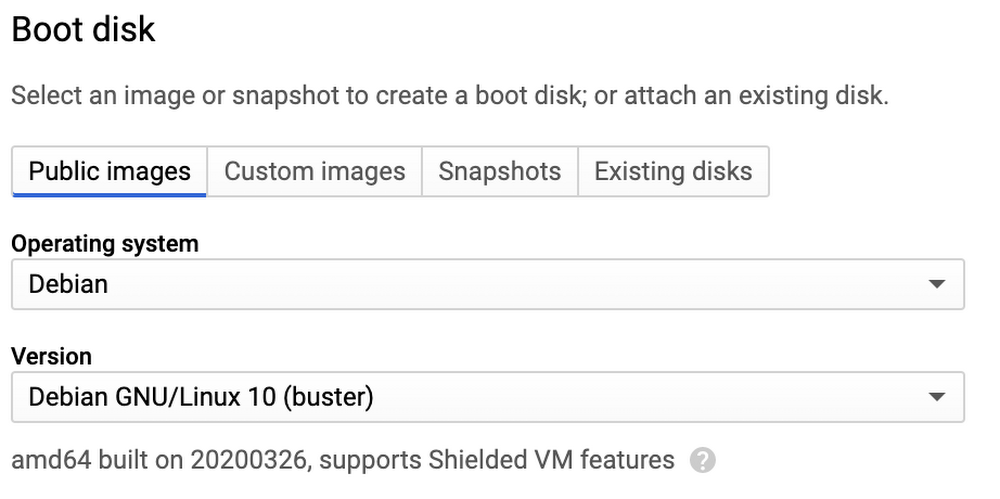
- Then, simply pick a boot disk that supports Shielded VM features. In this example, we’re creating a VM instance using the Debian operating system.
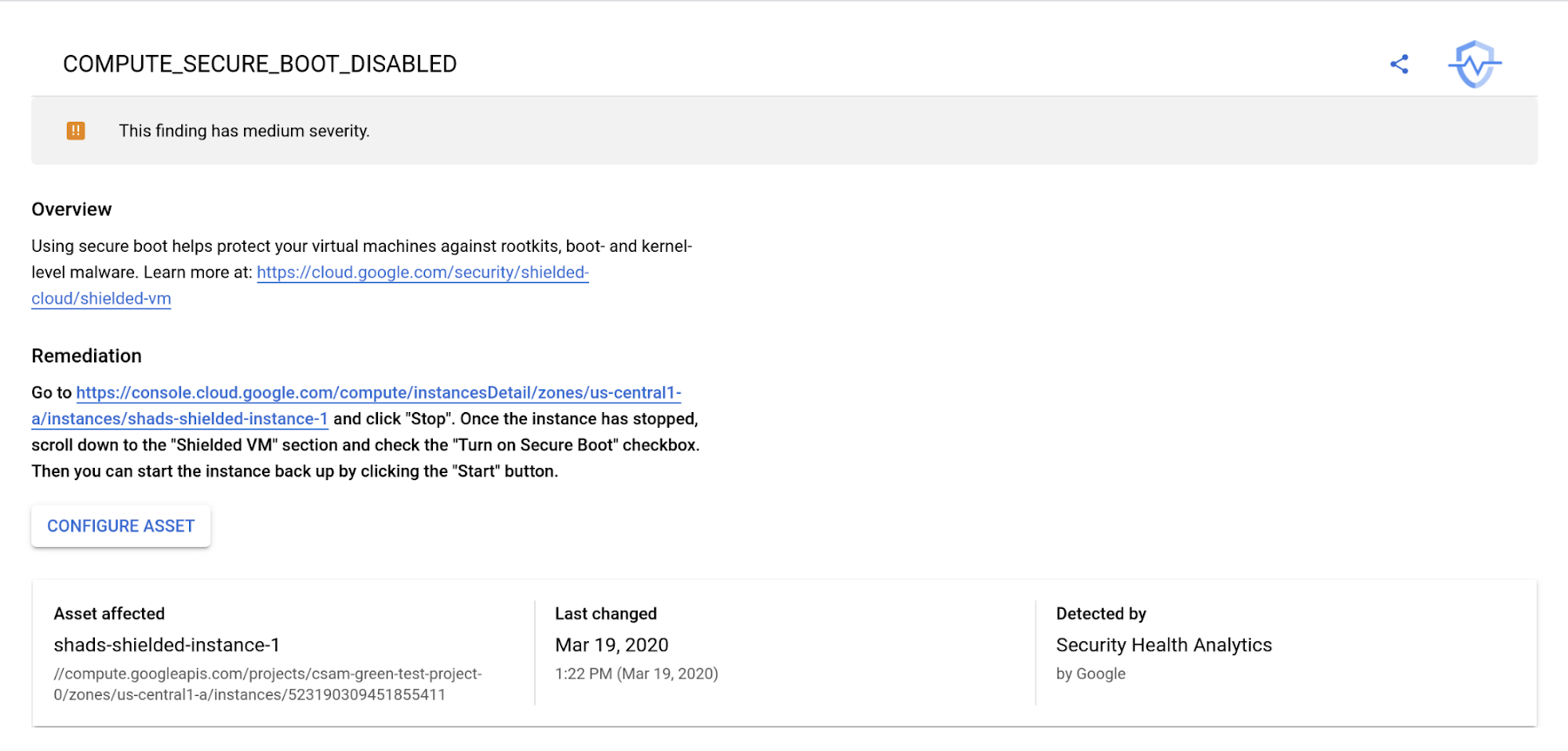
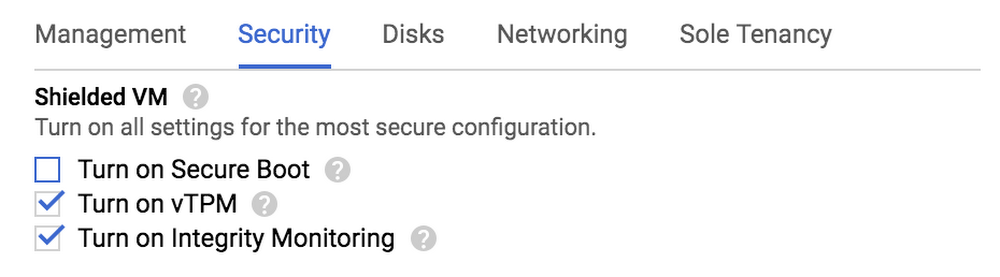
- Once you've selected a boot disk, you can adjust Shielded VM’s configuration options—Secure Boot, vTPM, and integrity monitoring—under the “Security” tab. On a Shielded VM instance, the vTPM and integrity monitoring options are enabled by default, but Secure Boot is not. This is because some customers use unsigned drivers or other similar features that are incompatible with Secure Boot. If you don't need these features, we strongly encourage you to enable Secure Boot.
At this time we want to be especially mindful of the many challenges organizations are facing. By making Shielded VM the default for Google Compute Engine, we hope to help simplify your workflows and provide the peace of mind that your VMs and VM-based services are protected from persistent rootkits and bootkits. To learn more, please check out the Shielded VM documentation.


