How GCP helps you take command of your threat detection
Max Saltonstall
Developer Relations Engineer, Google
Timothy Peacock
Senior Product Manager, Google Cloud
Why do we keep talking about security all the time? Why hasn’t anyone just gone and fixed it?
You’ve probably heard these questions, whether from your leadership, or a board member, or just from friends. Then you labor at explaining why security in the cloud is so complex and challenging, the constant arms race, and eventually their eyes glaze over. But you’re right: It is complex, and it can be hard.
As a security leader today, you likely spend a lot of your time focused on getting information: what’s going on, what new vulnerability just surfaced, what threats are present in your environment, and how to remediate them. And you probably already have a few dozen tools in place to measure, analyze, collect, and search through your data.
Right now, with your set of existing tools, you hopefully have a good sense of your on-prem systems and your overall attack surface. But across all those datasets, you’re juggling incongruous access patterns, stale data, and cluttered information coming from disparate tools—it’s not organized by topic, risk, or project. So unifying and rectifying the data sources, to really give you a full picture, just doesn’t happen.
Then you add cloud systems to the mix, and it’s a whole ‘nother ball of wax. To wrap up National Cybersecurity Awareness Month, we wanted to detail a few security features we’ve developed—most recently Event Threat Detection, available today in beta—and highlight some information that can help you reduce the complexity of your organization’s security, and improve your security posture.
Gain visibility and control, and prevent threats
With Cloud Security Command Center (Cloud SCC), Google brings a flexible platform to give you wide visibility and rapid response capabilities. Beyond just risk and vulnerability management, Cloud SCC focuses on active defense, showing you threats that have been detected and the path to greater holistic security in your cloud resources. It integrates with existing partner security solutions you already use and Google Cloud security tools. And its API is accessible to you and your vendors, so any additional data is easy to integrate.
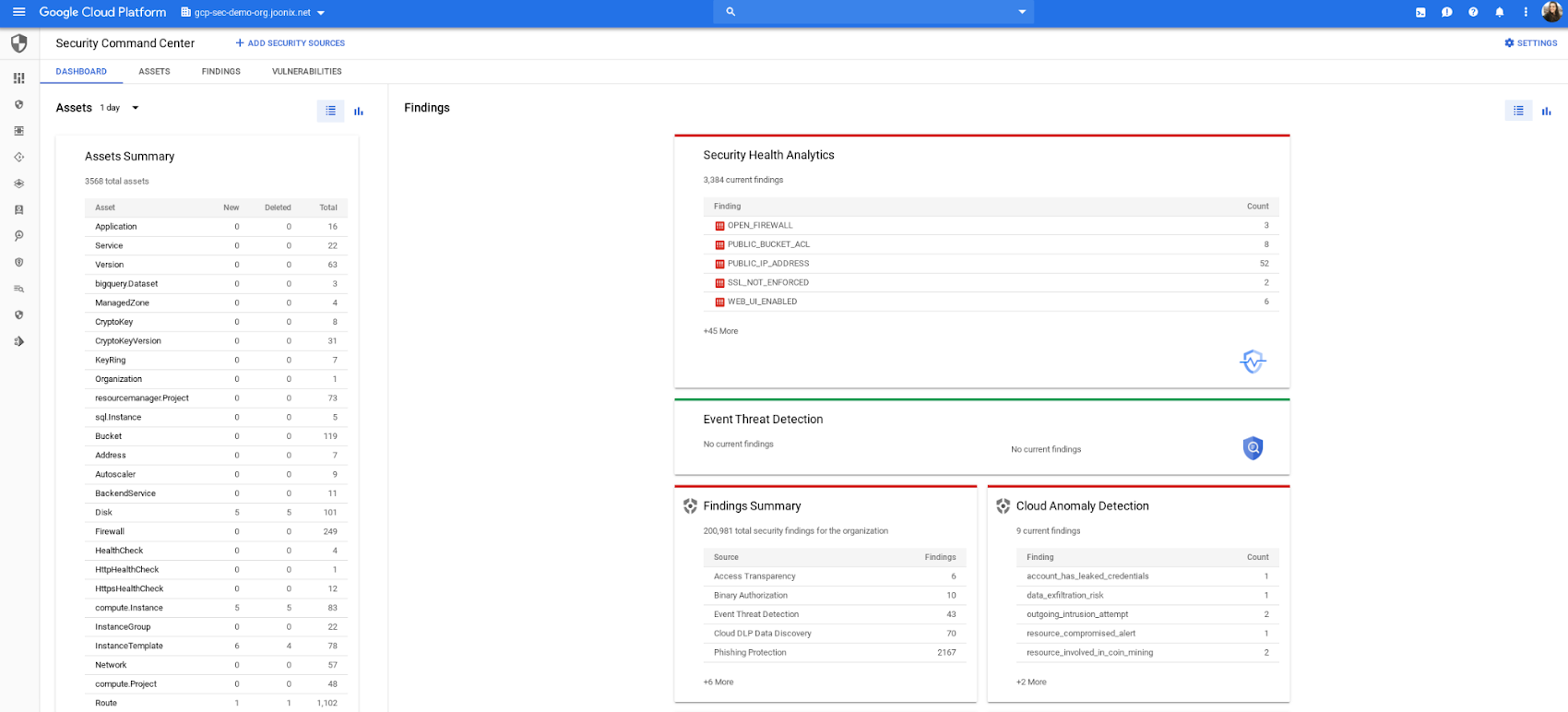
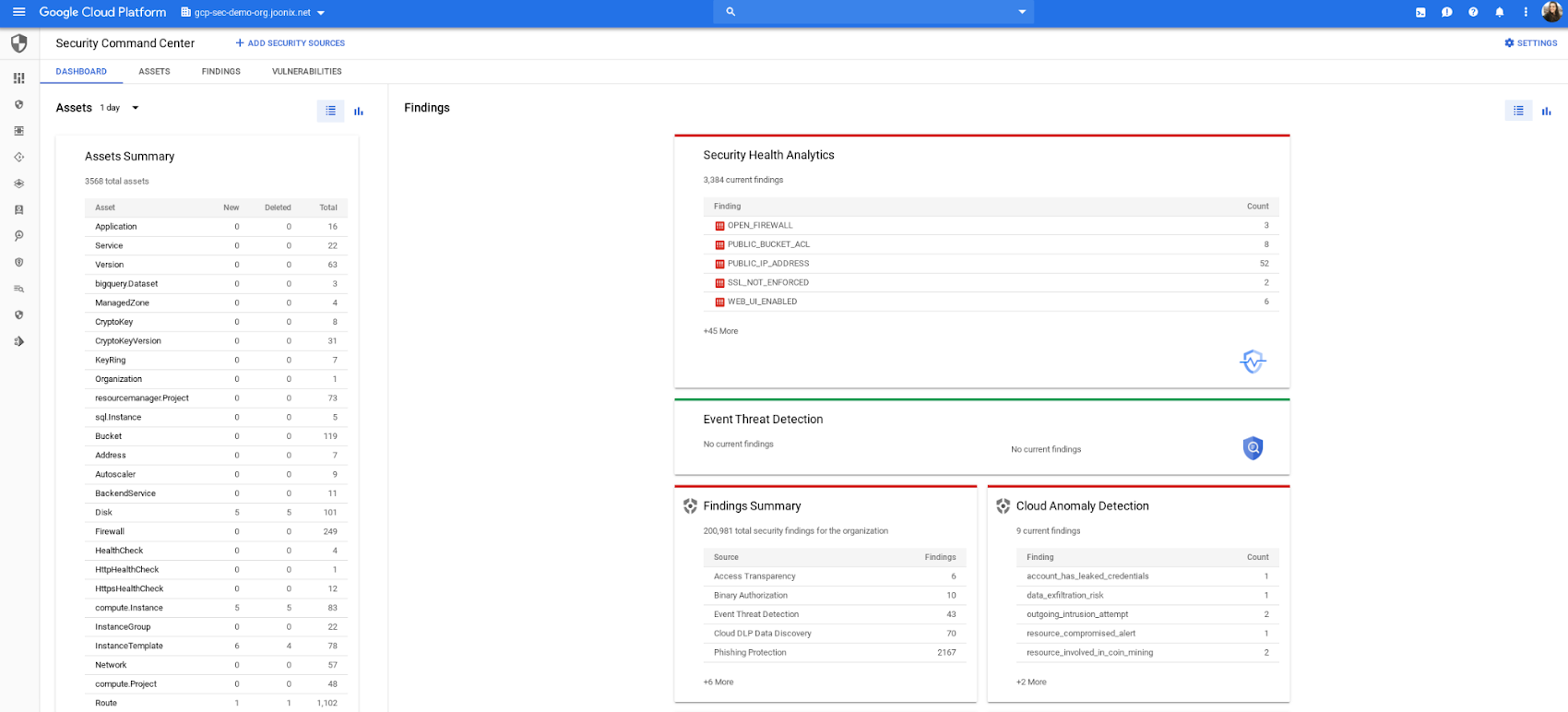
The model above is a centralized dashboard for threat prevention, detection, and response, with views of your current state that you can change based on your needs. For example, you can focus on assets to get a comprehensive list of every firewall, network, disk, bucket, and so on in your organization.
You can also orient your view based on findings (results) of what’s wrong in your Google Cloud Platform (GCP) environment. We recently launched the Vulnerabilities dashboard to show findings from Security Health Analytics. It’s an integrated security product that helps you identify misconfigurations and compliance violations in your GCP resources and take action.
Reduce threat exposure with Event Threat Detection
Reducing your exposure to threats goes hand-in-hand with being able to respond quickly to those threats that are present in your environment. Today, we’re excited to announce the beta of Event Threat Detection, a security product that integrates into Cloud SCC, and was inspired by how Google protects itself. We wanted to extend our scale and threat intelligence to help you protect your environment and improve your security posture.
Event Threat Detection helps you detect threats in your logs and send high-risk threats to your SIEM (Security Information and Event Management system) for further investigation. It also can help you save time and money by focusing your attention on the most worrisome cloud-based threats.
Due to the growth in cloud computing, we’ve seen an increase in the number of customers running VPC Flow logs, Cloud DNS logs, Cloud Audit logs, and syslog delivered via the fluentd agent on GCP. Event Threat Detection uses Google’s threat intelligence to surface threats present in these logs, including anomalous IAM grants, malware, cryptomining, outgoing DDoS, and brute-force SSH.
When Event Threat Detection finds a threat in your logs, it shows up as a finding on the Cloud SCC dashboard. If you need to further analyze any of these threats, you can send them to your SIEM, saving time and money because Event Threat Detection has already determined the high-risk logs you need to investigate further.
Event Threat Detection integrates with Cloud Functions to make it easier for you to export findings to your SIEM of choice. You can also use Cloud Functions to automate responses and changes to Event Threat Detection findings. See the video below for more information.

Respond to threats
Once threats have been detected, the final step is, obviously, responding to them. To help speed up your response game, you can set up automated actions for when threats are detected. When Cloud SCC detects an anomaly, or an active threat, you can have it change a VM configuration, perhaps cutting the VM off from other parts of your network. You can also change firewall rules automatically. Using these events to trigger Cloud Functions, you can set up any response you like, fully automated. At the same time, you can send incident metrics and data to Stackdriver or your own SIEM to make sure your incident response team has everything they need.
Together, these features give you the power to structure and organize the data you gather, which is key to making cloud security work for large, mature organizations. Cloud SCC lets you create tags for items to assist with incident response or project-based inquiry, and to aid in custom dashboard creation. The constant goal: give you the information you need quickly, so you can take the necessary action.
Cloud SCC details
Now that you have a high-level view of how Cloud SCC and Event Threat Detection can help your organization become more secure, here are some other resources highlighting Google security features that integrate into Cloud Security Command Center, how they work, and how they can help you improve your security posture:
Find and fix misconfigurations in your Google Cloud resources with Security Health Analytics
Stop data exfiltration with Cloud Data Loss Prevention
Detect and remediate security anomalies with Cloud Anomaly Detection
Catch web app vulnerabilities before they hit production with Cloud Web Security Scanner
These blogs feature step-by-step instructions with screenshots, and each has a companion video. Check them out, and let us know if there are any other issues and solutions you’d like us to detail.
Get started
To get started with Cloud Security Command Center, watch our video below.

If you’re new to GCP and want to give these products a try, simply start your free GCP trial, enable Cloud SCC, and turn on our integrated security products, like Event Threat Detection. If you’re an existing Cloud SCC customer, just enable Event Threat Detection and our other security products from Security Sources in Cloud SCC. For more information on Event Threat Detection, read our documentation.

