Configuring secure remote access for Compute Engine VMs
Collin Frierson
Product Manager, Google Cloud
System administrators are frequently asked to assess risk when moving their applications to the cloud. One common concern is the platform’s inherent presence on the internet, and how to properly secure cloud-based virtual machines and services that are now exposed. In Google Cloud, you can configure VMs and APIs so they’re not connected to the public internet but still accessible to system administrators. Here’s how.
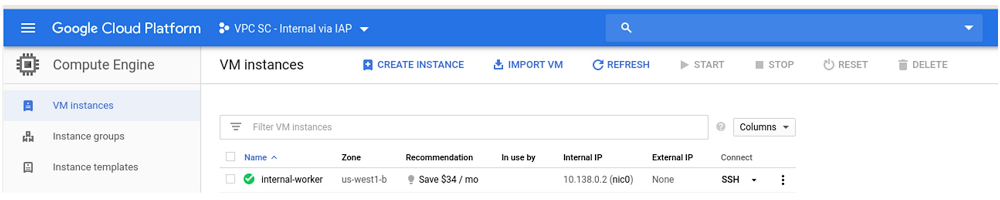
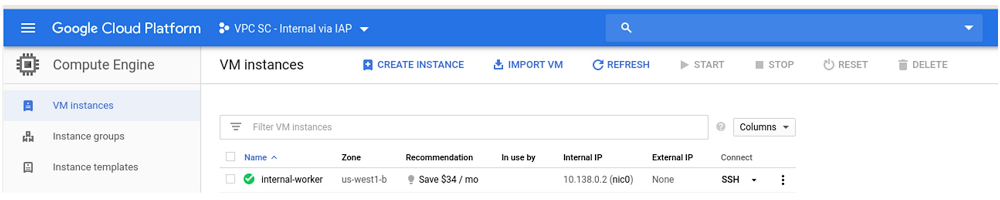
Use Compute Engine’s No External IP Org policy
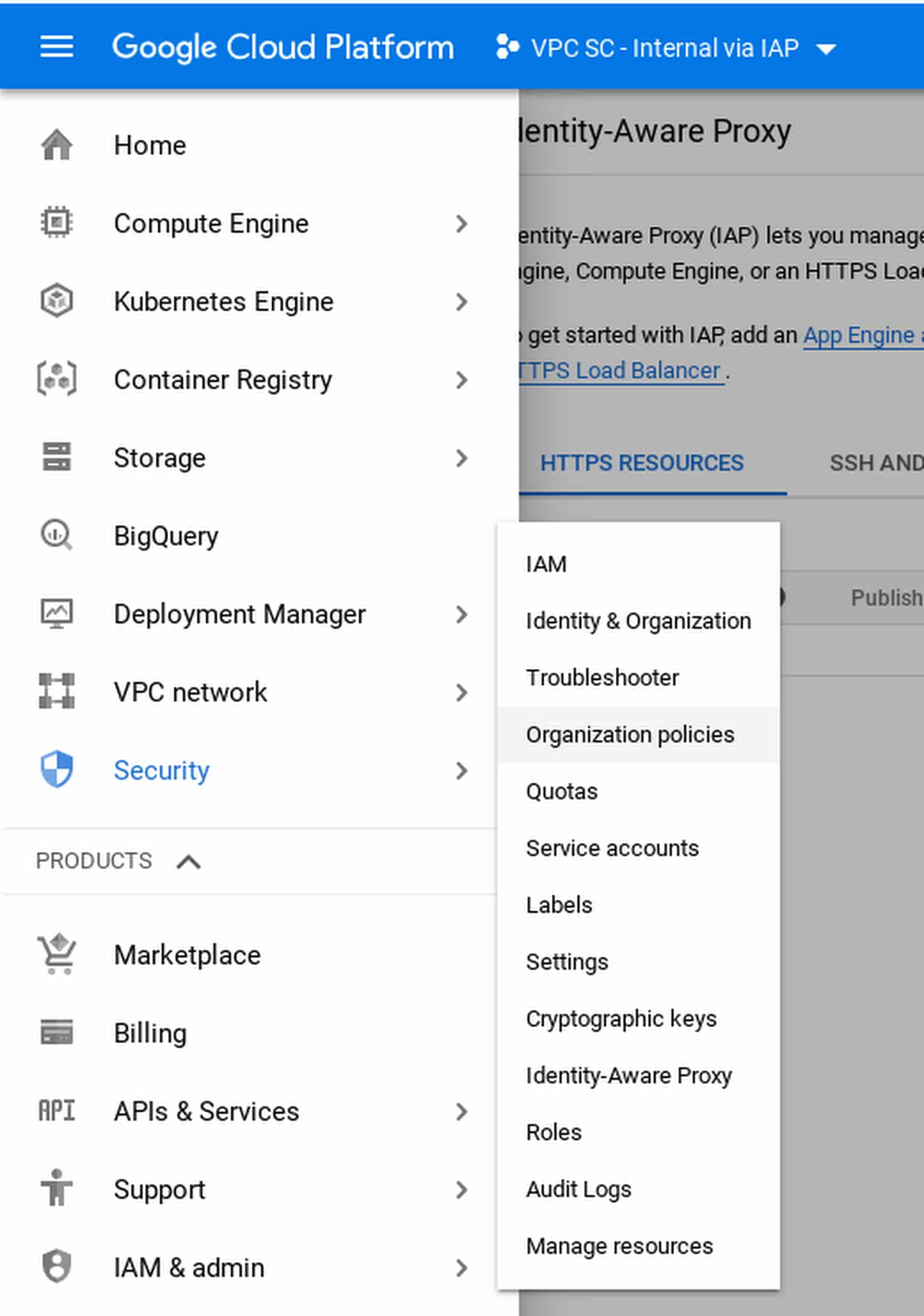
The first thing you can do to protect VMs it to configure a policy that disallows VMs from obtaining an external IP. From the admin console, click Security and select Organization Policies.
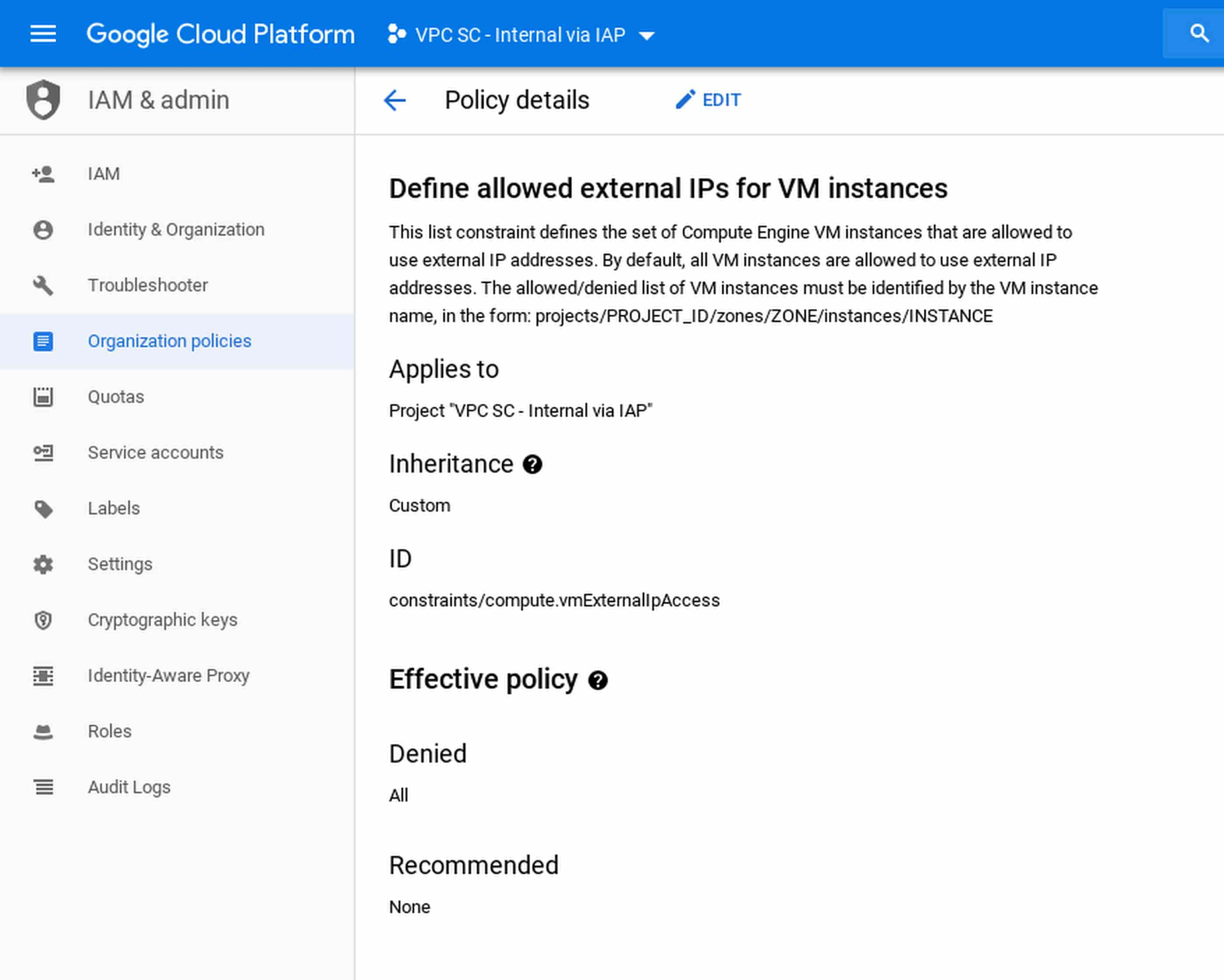
Note that this policy is not retroactive, so if you already have machines with external IP addresses, this policy does not remove them. Also be aware that while the default VPC has firewall rules to allow SSH / RDP, without an external IP, these are only accessible from the internal network.
Use Cloud Identity-Aware Proxy
Next, you need to allow developers to access these machines. Traditionally, you configure a VPN client to connect to the VPC. In Google Cloud, there’s a better way: you can use Cloud Identity-Aware Proxy (IAP) to connect to the machines. To show you how, we’ll follow this guide.
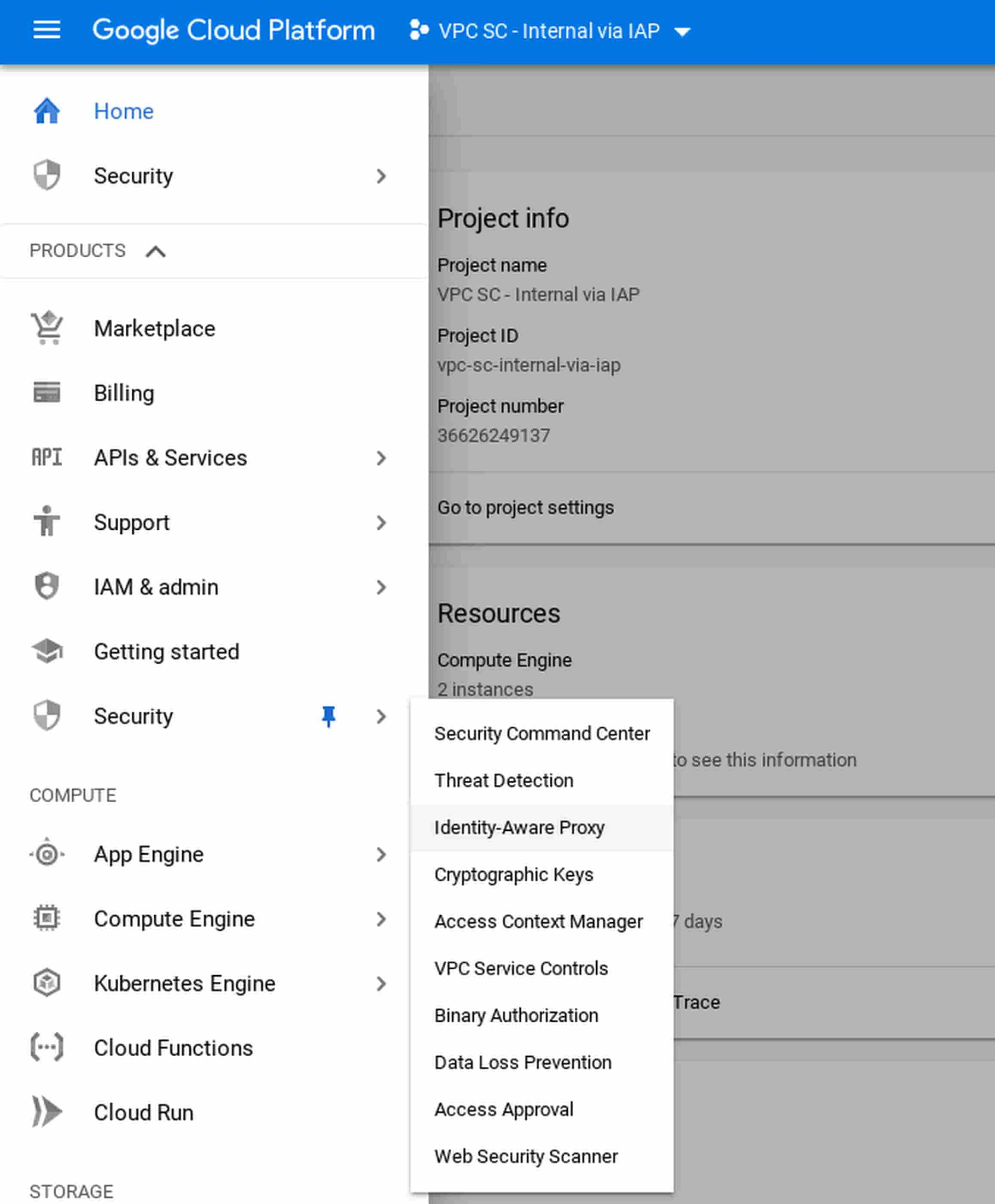
From the admin console, click Security then select Identity-Aware Proxy.
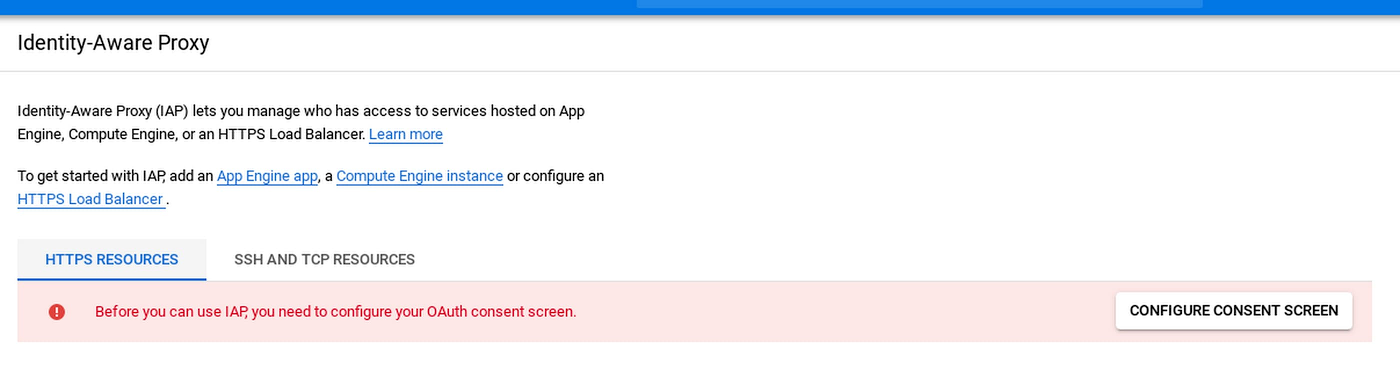
If you haven’t used Cloud IAP before, you’ll need to configure the oAuth screen:
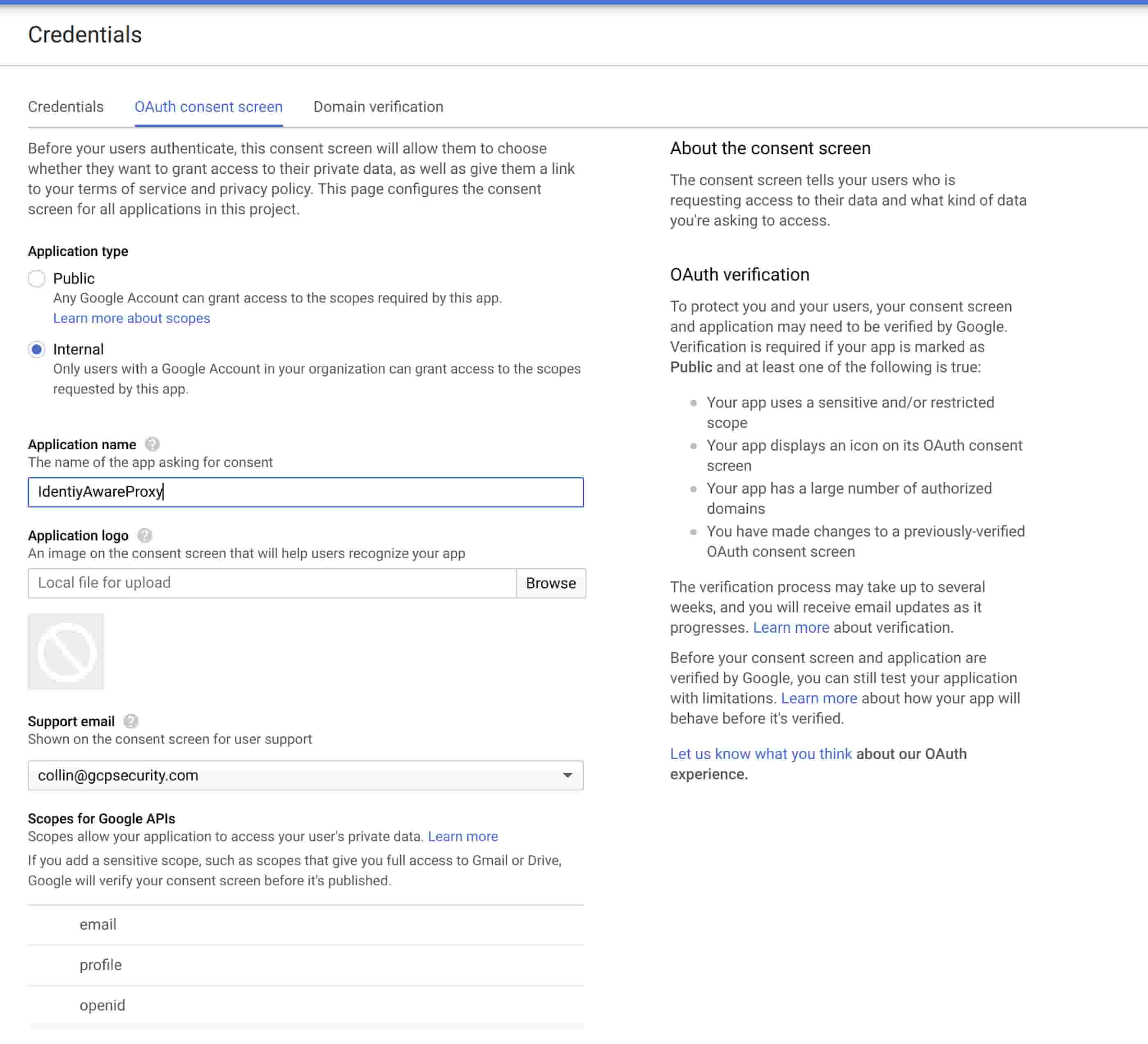
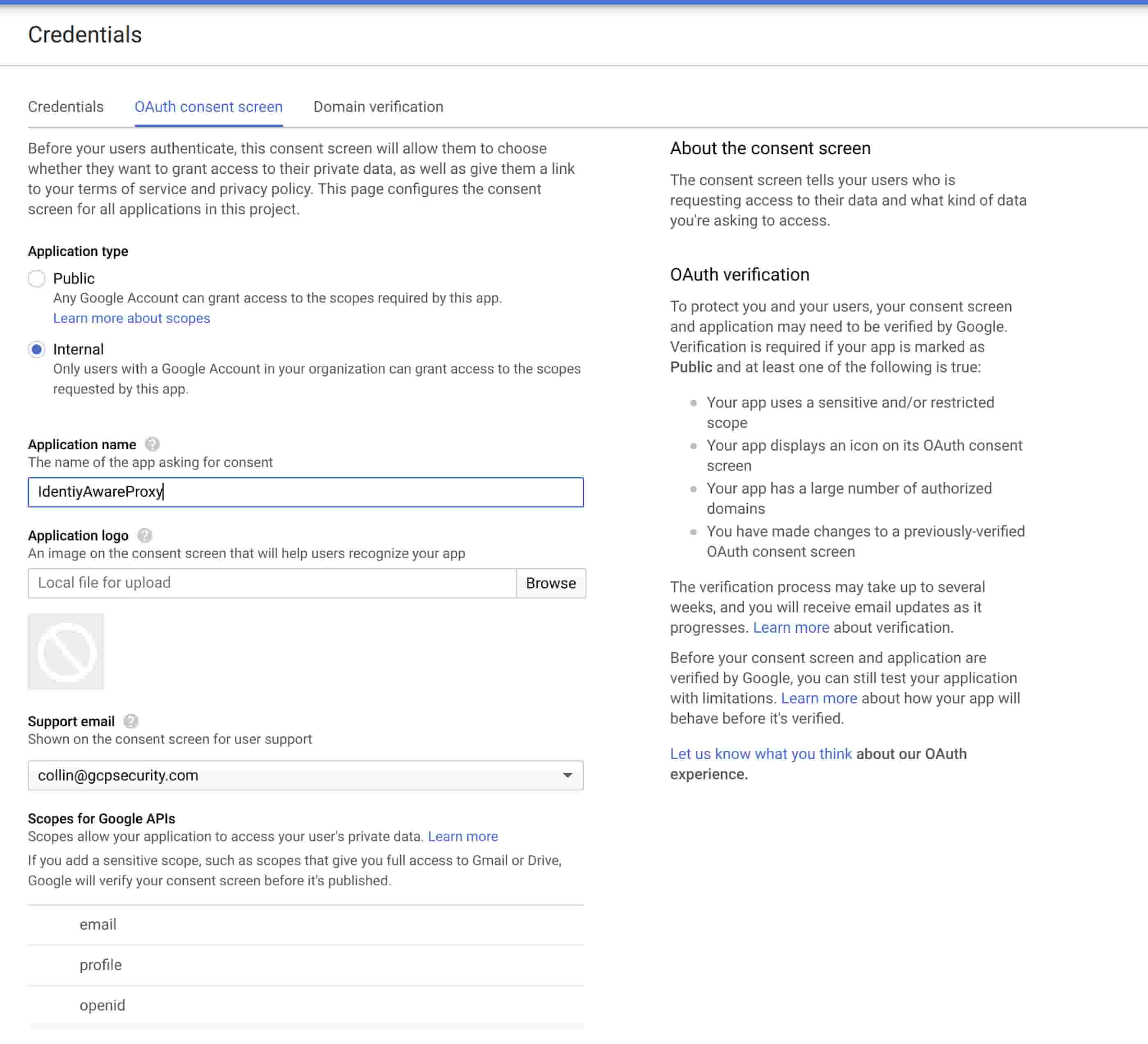
Configure the consent screen to only allow internal users in your domain, and click Save.
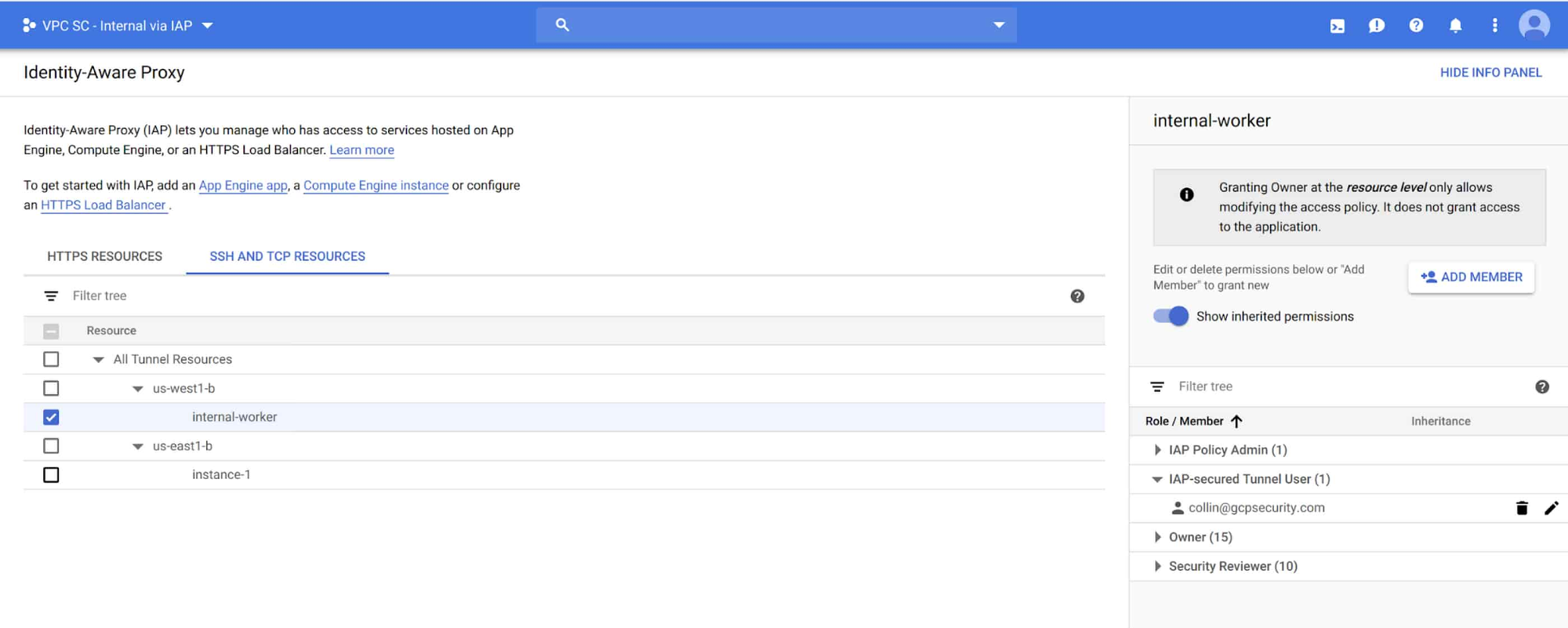
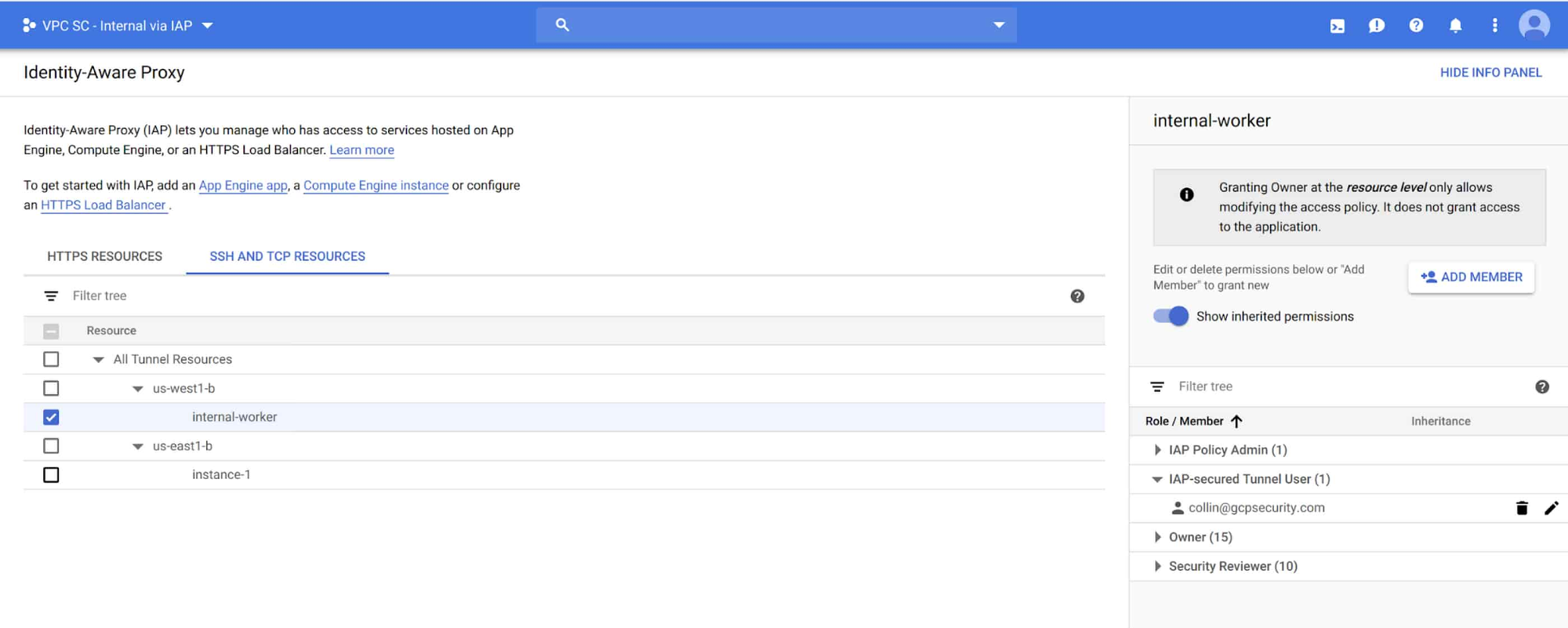
Next, you need to define users who are allowed to use Cloud IAP to connect remotely. Add a user to the “IAP-secured Tunnel User” role on the resource you’d like to connect to.
Then, connect to the machine via the ssh button in the web UI or gcloud.
When using the web UI, notice the URL parameter useAdminProxy=true.


Tip: If you don’t have gcloud installed locally, you can also use Cloud Shell:
You should now be connected! You can verify that you don’t have internet connectivity by attempting to ping out. 8.8.8.8 (Google’s Honest DNS) is a good address to try this with.
Controlling access with VPC Service Controls
Most GCP developers will still want access to Google Cloud APIs. You can give them access to Google Cloud APIs while restricting them to resources that are present in the project by using VPC Service Controls.
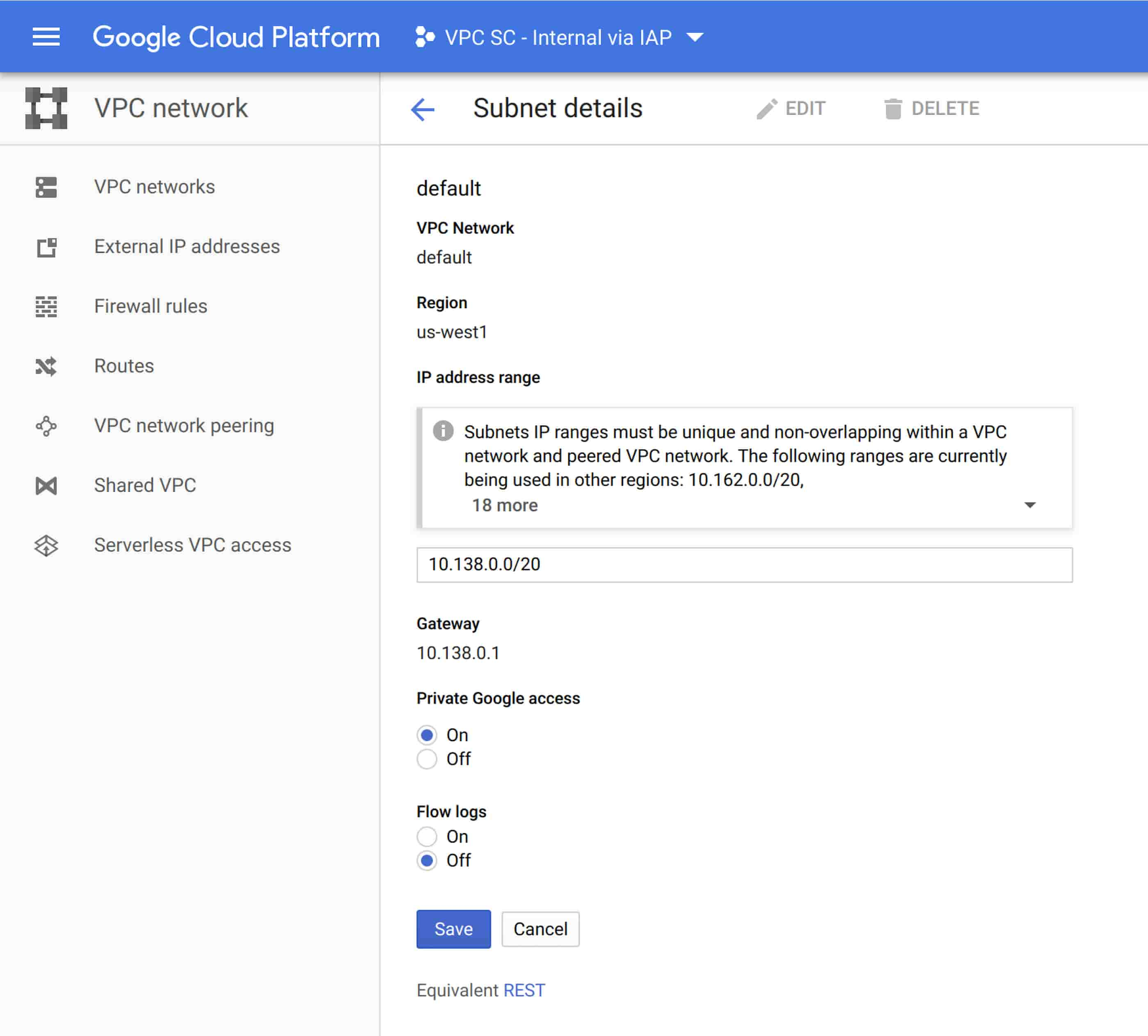
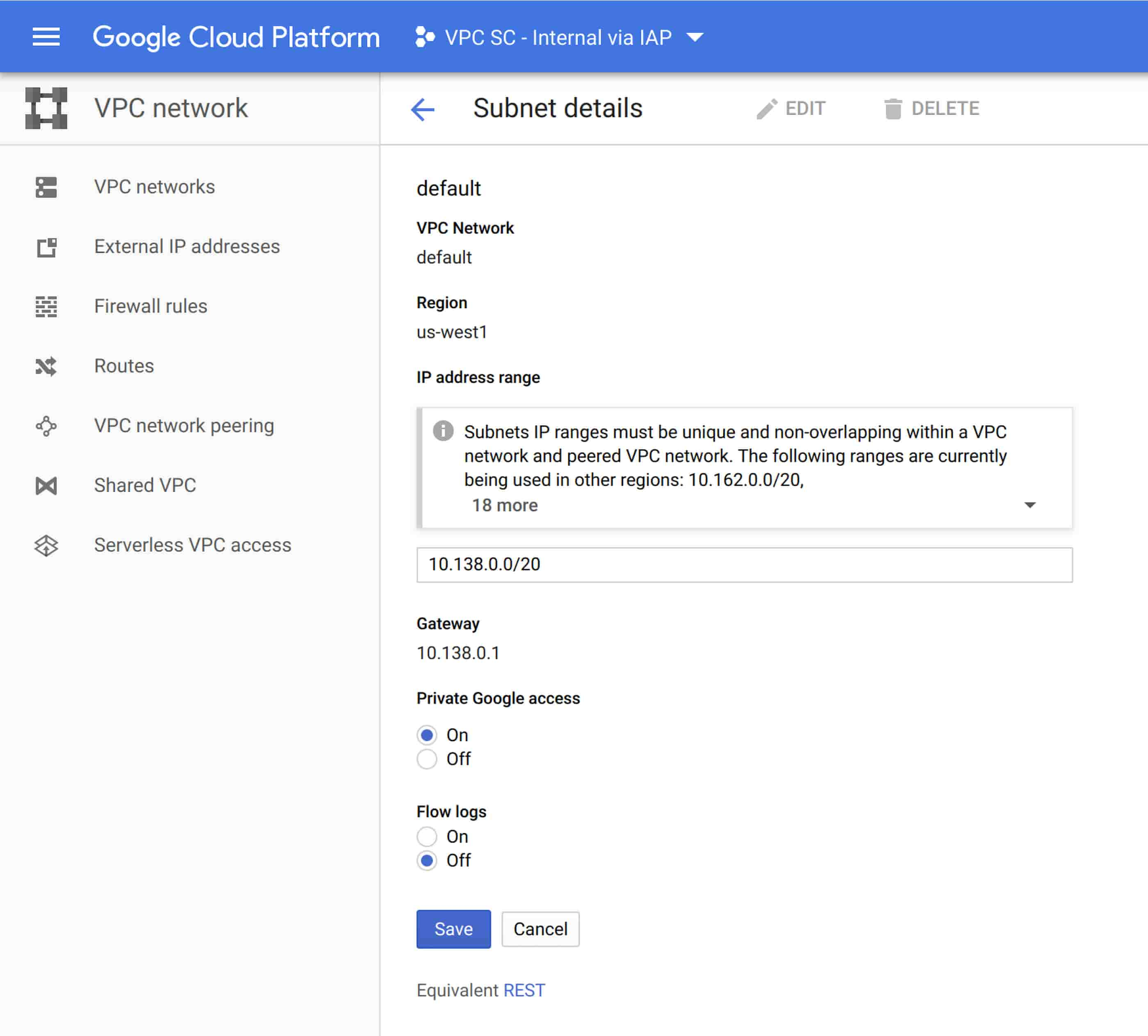
First, enable private Google API access on the VPC network where your VM is located (in this example, US-West1.) Select the VPC network in the region where your virtual machines are located. Select the subnet, and click Edit. Enable Private Google access by selecting “Private Google Access” and click Save.
Once you’ve enabled private access, gcloud commands from the VM will work.
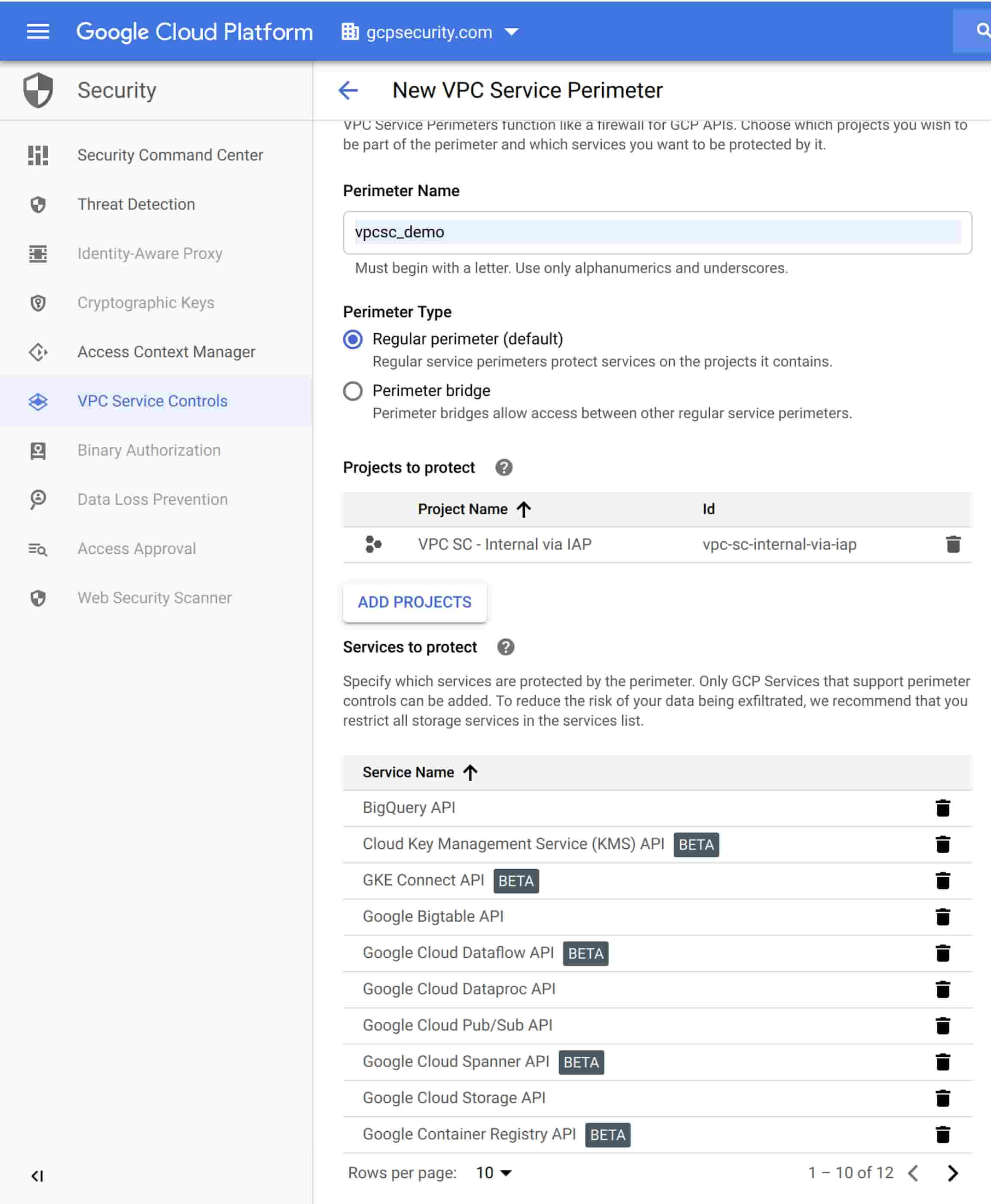
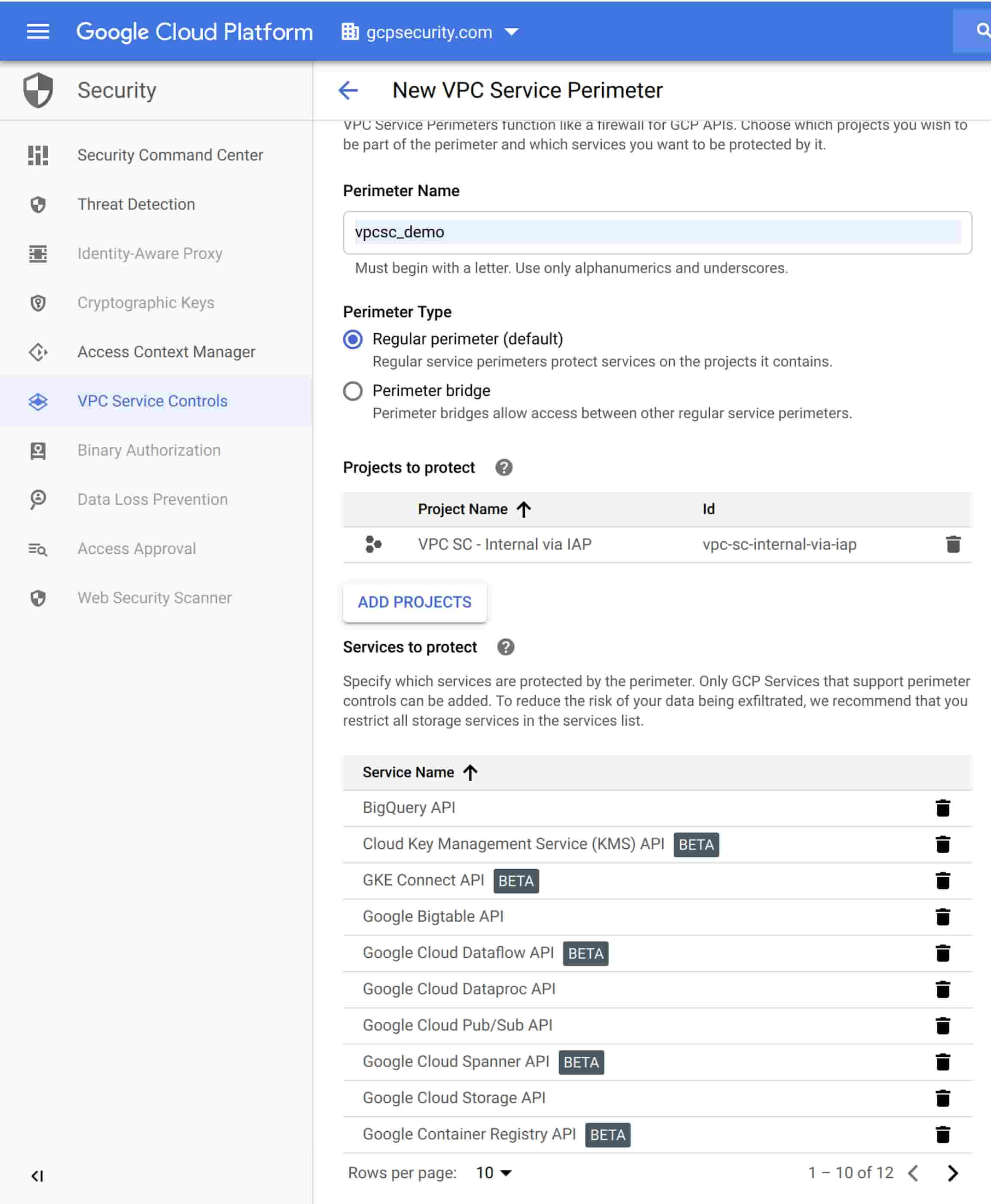
Now use VPC Service Controls to define where you’d like those API requests to be allowed. Navigate to the ORG node for your domain and select VPC Service Controls from the Security tab. Select New Perimeter. Add your project and the APIs you’d like to protect to the “New VPC Service Perimeter” and click Save.
Now that you’ve gone through all these steps, your VMs should be configured so they are only accessible via Identity-Aware Proxy, and only have access to the local network and Google APIs that are part of the project to which they belong.
As you can see, using Google Cloud tools like Cloud IAP and VPC Service Controls can help you insulate projects from the public internet, reducing risk and fears about moving apps and infrastructure to the cloud. To learn about more security capabilities and features, visit cloud.google.com/security.


