Introducing table-level access controls in BigQuery
Uladzimir Makaranka
Software Engineer, Google Cloud
Uri Gilad
Product Manager, Google Cloud Data Governance
We’re announcing a key capability to help organizations govern their data in Google Cloud. Our new BigQuery table-level access controls (table ACLs) are an important step that enables you to control your data and share it at an even finer granularity. Table ACLs also bring closer compatibility with other data warehouse systems where the base security primitives include tables—allowing migration of security policies more easily.
Table ACLs are built on top of Cloud Identity and Access Management (Cloud IAM), Google Cloud’s enterprise-grade access control platform that integrates across our cloud products. BigQuery already lets organizations provide controls over access to data sets, projects, and folders. With BigQuery table-level ACLs, you can use these same controls at the table scope, satisfying the principle of “least privilege.” This capability, combined with BigQuery column-level security, is key in helping organizations effectively govern data in Google Cloud and maintain regulatory compliance, such as GDPR, CCPA, etc.
Table ACLs enable you to share a single table, for reading and/or writing, without the surrounding dataset. This capability opens up use cases like sharing a single table externally with an outside contributor and segregating access control at the individual table level.
Many BigQuery customers use authorized views to control read-only access to tables. Authorized views allow data owners to join multiple tables and reshape the data before sharing it. However, if you want to simply share a single table as is, authorized views become cumbersome. Table ACLs streamline and simplify this use case.
Getting started with table ACLs
Table ACLs are available in the BigQuery Web UI as a “share table” button that exposes the Cloud IAM permission panel (same as for sharing a dataset):
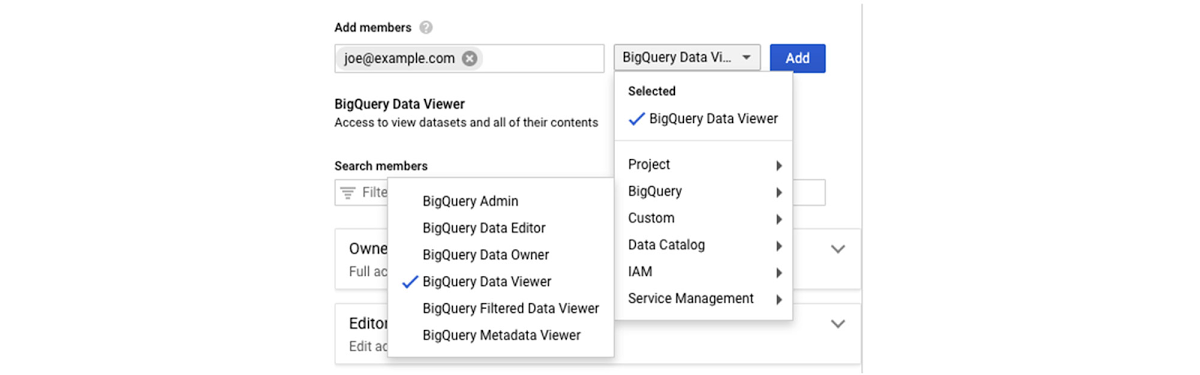
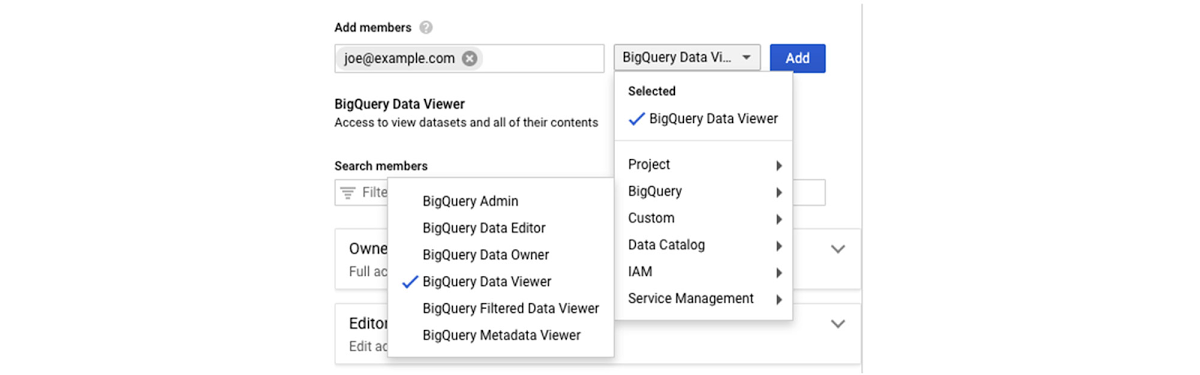
The Table ACL functionality is also available via the BigQuery command line and REST APIs. Both of them use Cloud IAM Policy JSON. A policy defines and enforces which roles are granted to which members, and this policy is attached to a resource. The following example shows a policy where alice@example.com has been granted the BigQuery data owner role, and bob@example.com has been granted the BigQuery data viewer role:
To obtain or set table policy, you can use bq get-iam-policy and bq set-iam-policy commands, respectively. Similarly, you can use tables.getIamPolicy and table.setIamPolicy REST APIs. For more info about IAM policies, see Understanding policies.
To get started, check out the BigQuery table ACL documentation to learn more about specific permission types and use cases.