Integrating Google Cloud Build with JFrog Artifactory
Ankush Chadha
Senior Solution Developer, JFrog
[Editor’s note: Today we hear from software artifact management provider JFrog about how and why to use Google Cloud Build in conjunction with its Artifactory binary repository. Their tools aim to make the application development pipeline more secure and deterministic and in turn ensure reliable apps.]
By the time an end user first interacts with an application, developers have already made countless decisions about how best to bring it to life: which language to use, which package types, whether to use a service such as Google Cloud Build to build and containerize applications, what repository to use to store assets that are written in Java, npm, Go, etc., and finally, where to run these containerized services, e.g., on Google Kubernetes Engine.
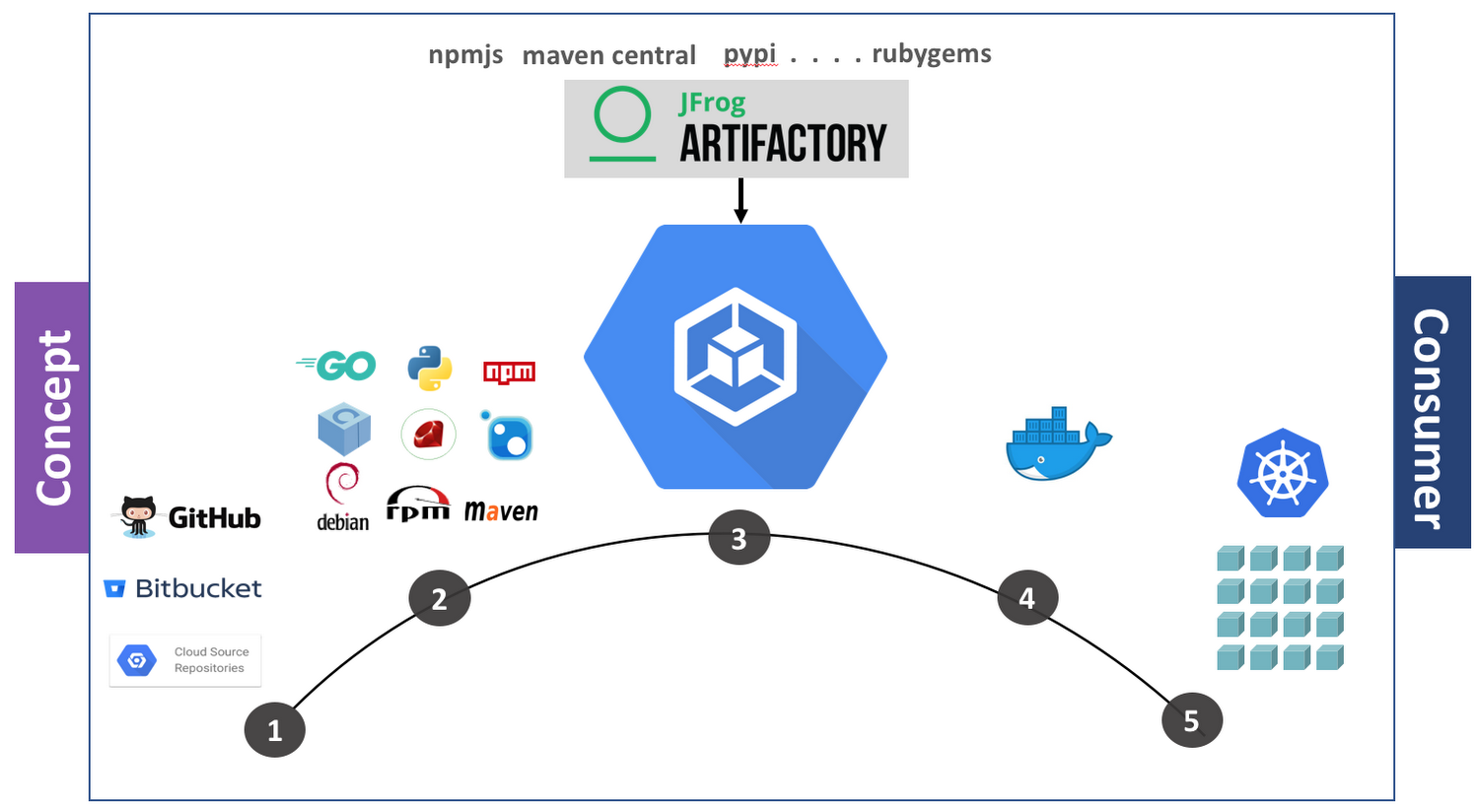
These typical steps of building an application, from concept to final consumer product, are shown here:
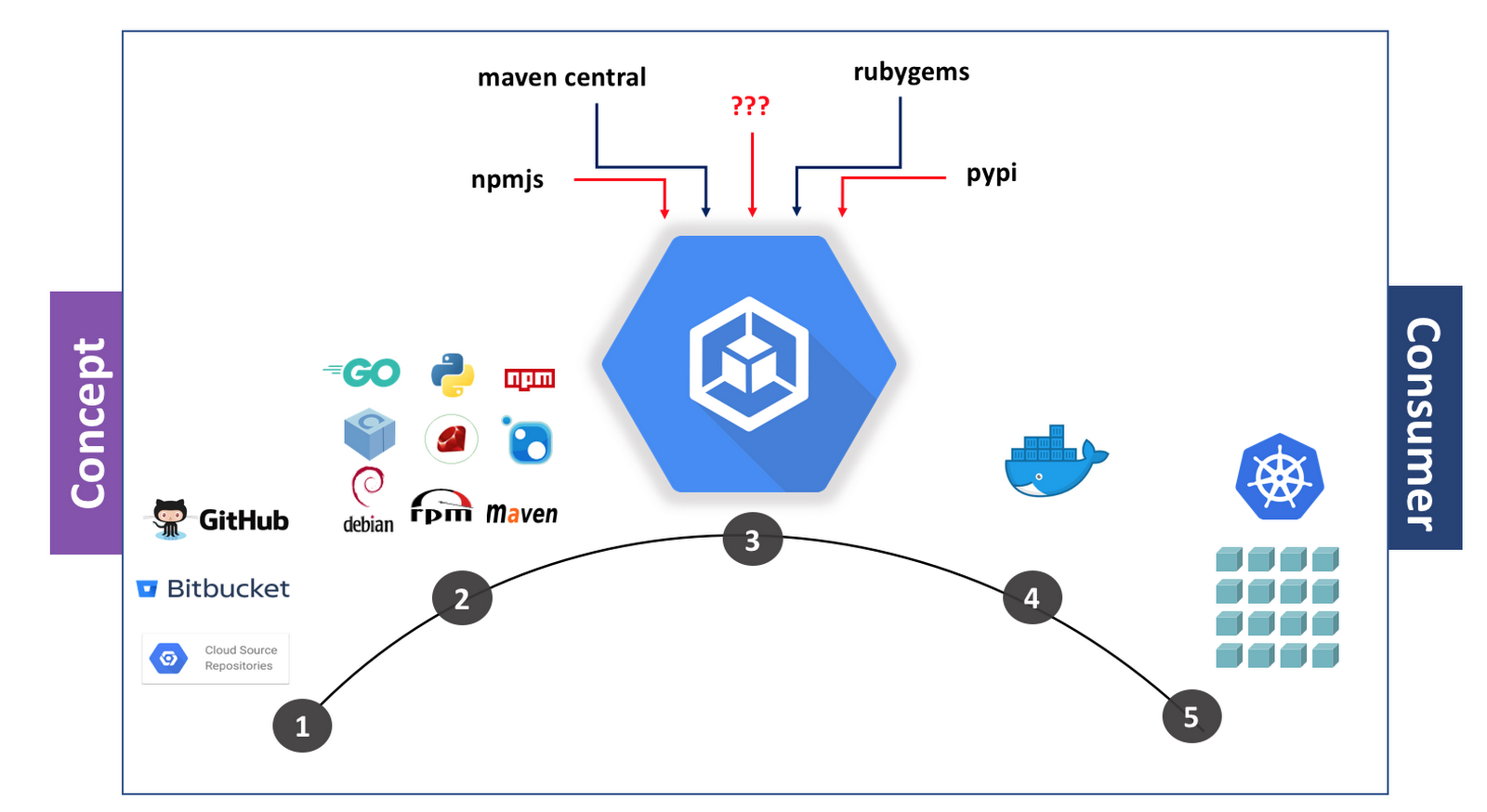
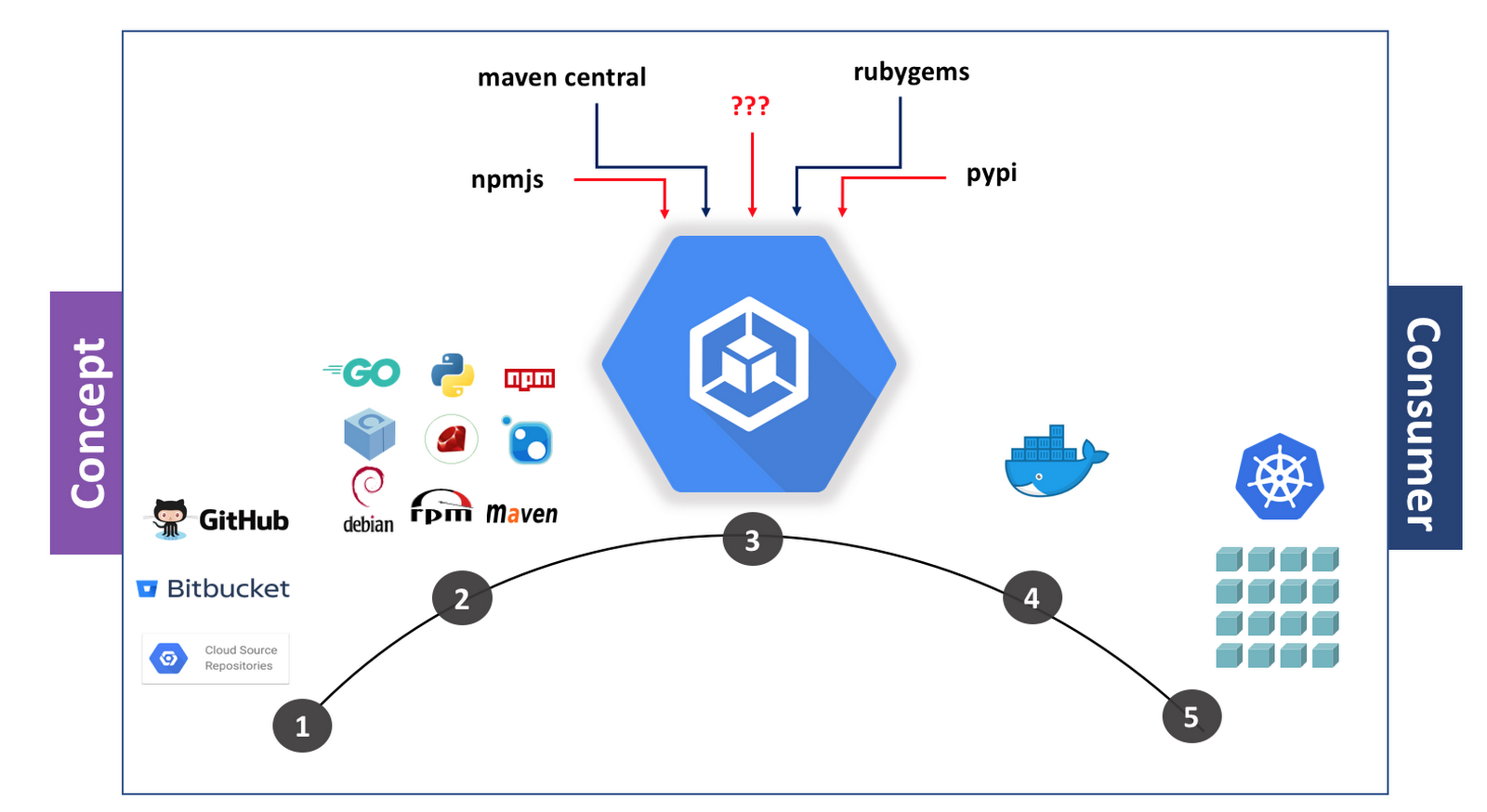
In the first step, you commit to a version control system. Next, you’ll choose a package such as Maven, Vgo or npm to speed the development process. Then, you can use a service like Cloud Build to containerize an app. Finally, the app is deployed on platforms such as Kubernetes. In this image above, the third-party dependencies in step three can be downloaded from multiple places, including random or unapproved places, which may be a concern.
At JFrog, the goal of our Artifactory product is to ensure the third-party libraries you’re using come from trusted sources, and that you avoid errors like ERR! 418 I'm a Teapot. You might choose to use Cloud Build with a private repository manager like JFrog Artifactory if you need to:
Containerize an existing application that’s stored in a private repository
Containerize an application that relies on both private and public dependencies
Speed up build and deployment time by caching dependencies
When Google Cloud Platform (GCP) recently launched Cloud Build, we were immediately excited by the potential of Cloud Build and Artifactory together. Cloud Build makes high-velocity software development safe and easy, and unleashes your team’s productivity. It enables you to build software quickly across different languages and gives you complete control over the definition of your workflows for building, testing, and deploying across multiple environments.
So we added support for Cloud Build to Artifactory. Using the two together lets you build containerized applications more quickly and flexibly by streamlining dependencies. In this graphic below, you can see what the application development process looks like when you’re using JFrog Artifactory along with Cloud Build. You can see in step three that various packages are pulled from Artifactory as they’re brought into Cloud Build.
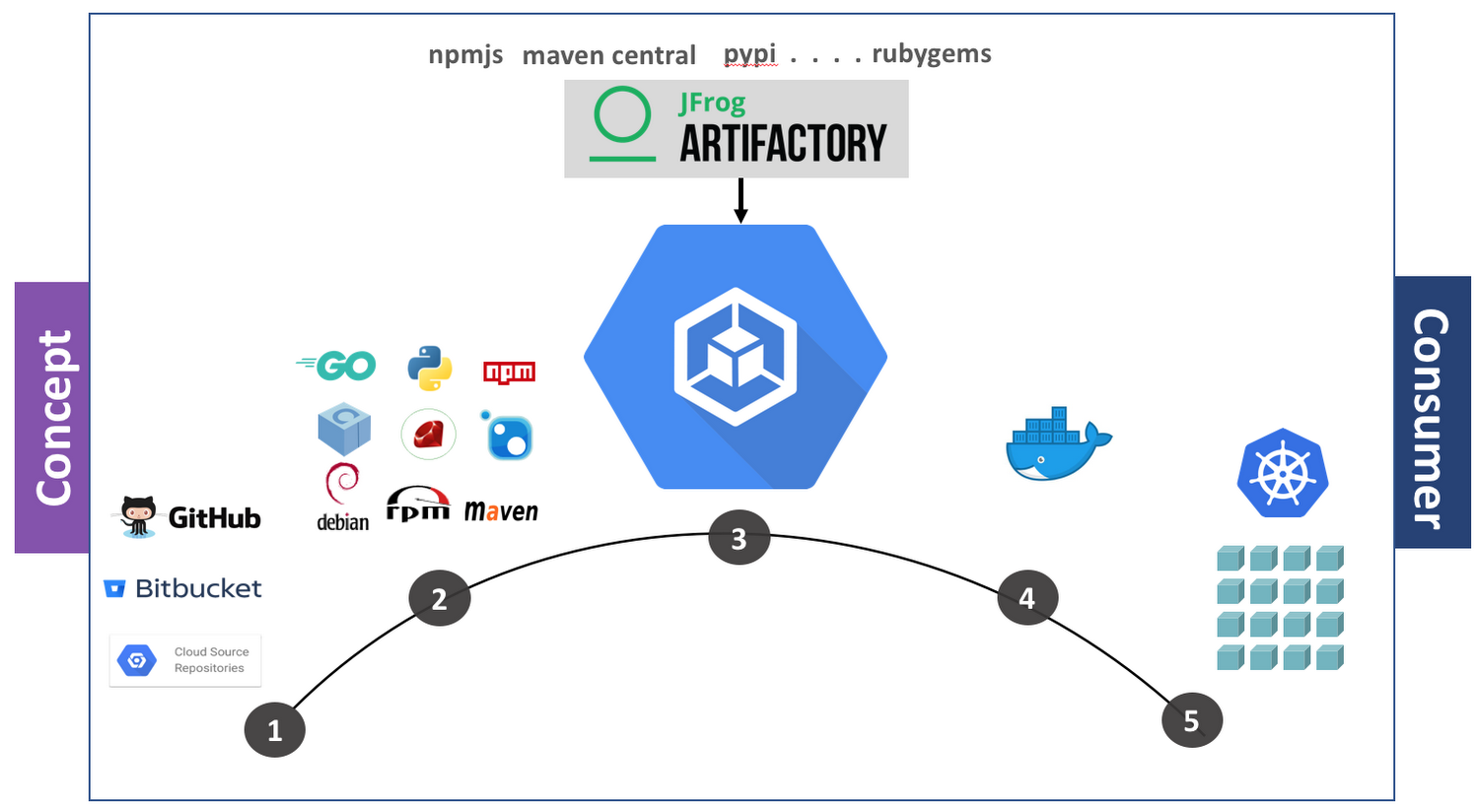
We’ll walk you through how to build containerized applications that pull dependencies from Artifactory, with Maven and Java as our sample package and language. Let’s get started.
Ensure sufficient security from the start
JFrog Artifactory uses your credentials to authenticate and allow you to pull or push packages, and it is extremely important that this sensitive information not be compromised. Here’s how to encrypt an API key:
a. Create a Google Cloud Key Management Service (KMS) KeyRing and CryptoKey
i. Create KeyRing
gcloud kms keyrings create [KEYRING-NAME] --location=global
ii. Create CryptoKey
gcloud kms keys create [KEY-NAME] --location=global --keyring=[KEYRING-NAME] --purpose=encryption
b. Encrypt the API key
echo $RT_API_KEY | gcloud kms encrypt --plaintext-file=- --ciphertext-file=- --location=global --keyring=[KEYRING-NAME] --key=[KEY-NAME] | base64
This command outputs an encrypted version of APIKEY that we will refer to as [ENCRYPTED_API_KEY].
Create a Cloud Build image that includes the JFrog CLI
We’ll use the example provided in the build step contributed by JFrog Artifactory.
This example points to a pre-built Cloud Build image that includes Maven and the JFrog CLI. If the requirement is to use another package type such as npm, Go, Conan, NuGet or Docker, or to use a different flavor of Maven, then we recommend creating a custom Cloud Build image. You can find sample instructions here to build the Maven builder image, though you can modify it based on your needs. Before you continue, configure your GCP service account permissions to allow it to build images.
Configure Cloud Build to pull Maven packages from Artifactory
First, configure JFrog CLI to authenticate with JFrog Artifactory.
Note: There is an added step to use the encrypted version of APIKEY.
Configure the JFrog CLI to specify Maven repositories to use for pull/push. You can find more information on how to do this here, and you can check out a sample version of a configuration file here.
Next, build the sample Maven project.
Containerize the Java application
Now, you’re ready to containerize your Java application.
Next, update cloudbuild.yaml with actual values of [ARTIFACTORY-USER], [ARTIFACTORY-URL], [ENCRYPTED_API_KEY], [KEYRING-NAME] & [KEY-NAME] and trigger a build.
This step triggers a build on GCP for this project, and pulls the Maven dependencies from Artifactory while building the application. Once the application is built, it is containerized and the final image is pushed to Google Container Registry, GCP’s managed container registry service. From there, you can choose your deployment target, including Google Kubernetes Engine.
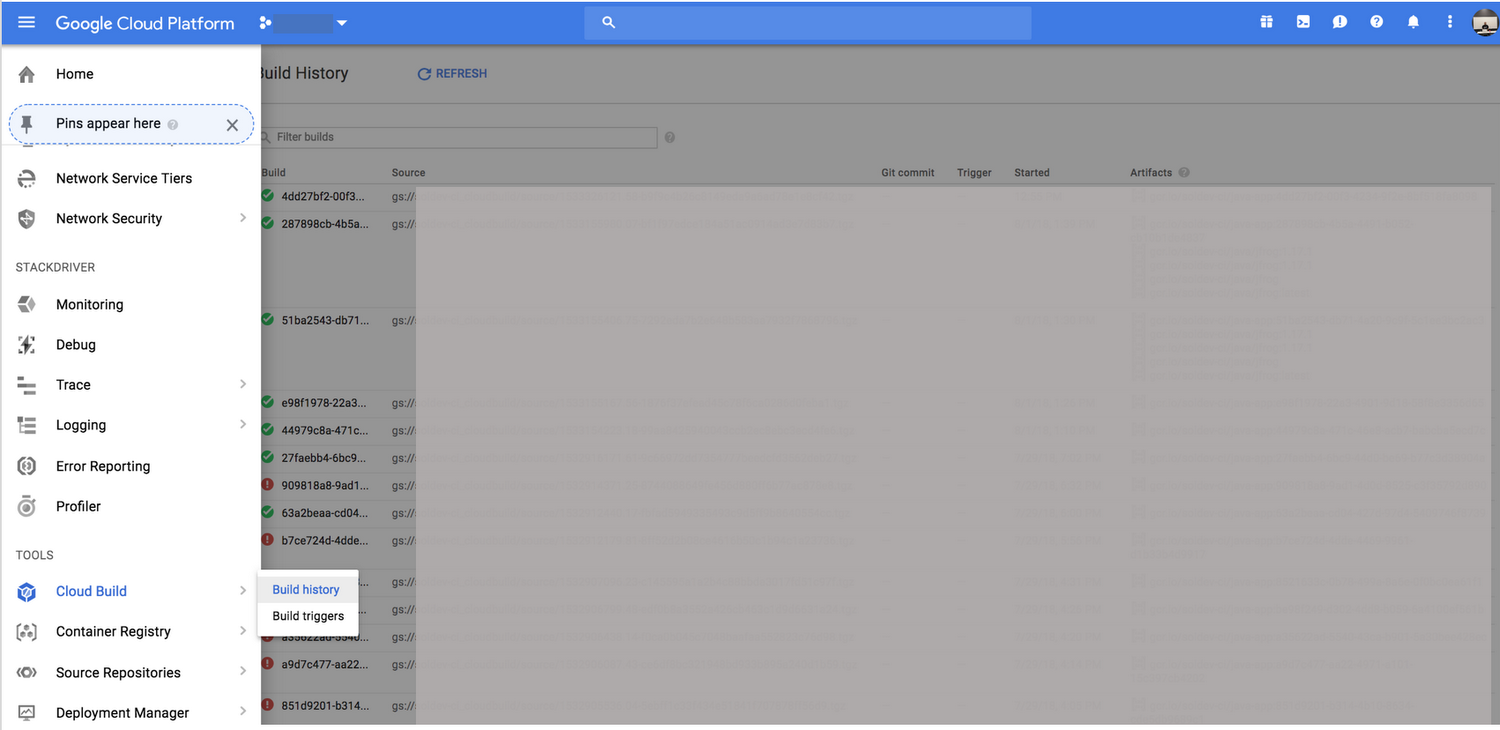
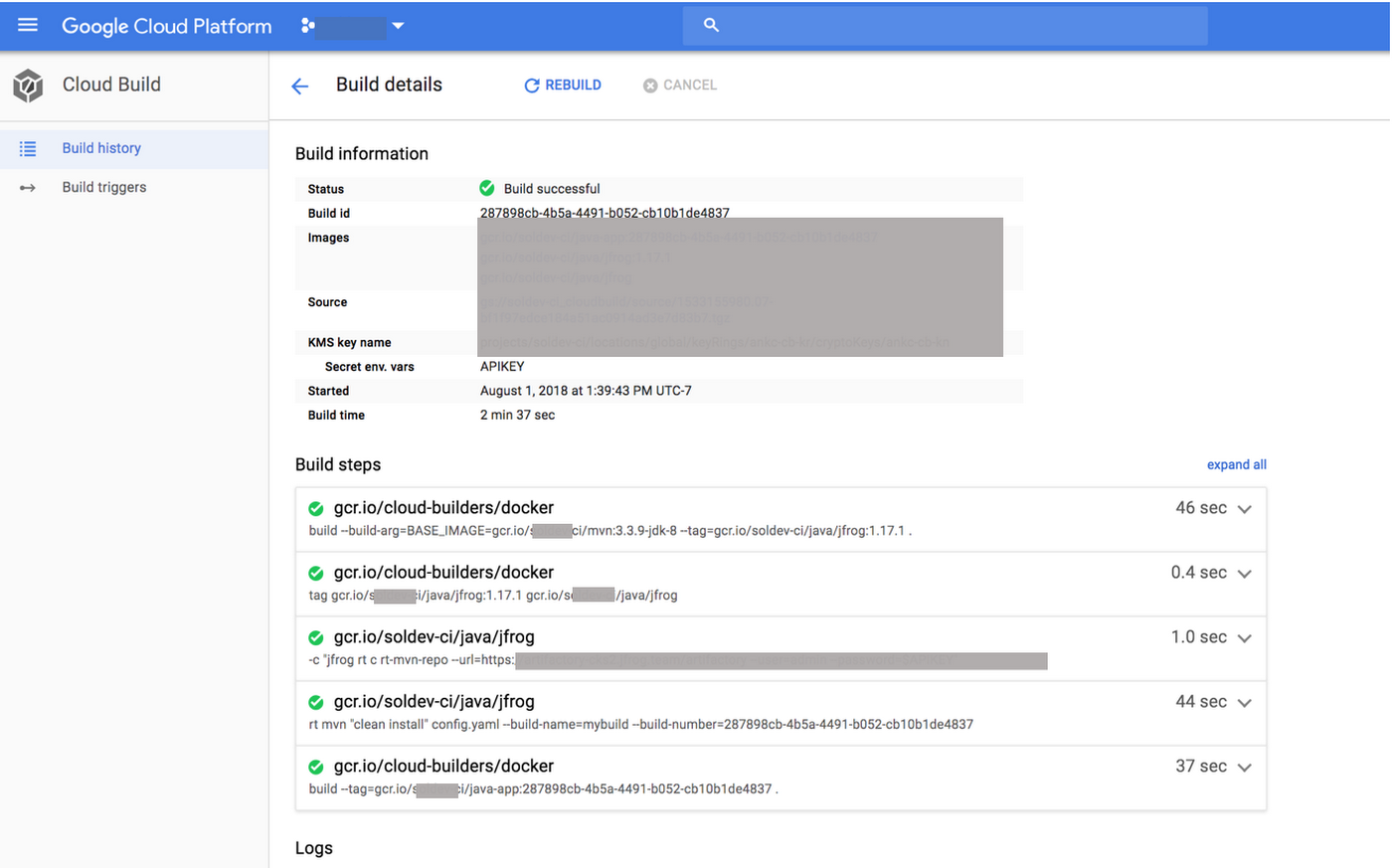
To check build results, navigate to Tools > Cloud Build > Build History:
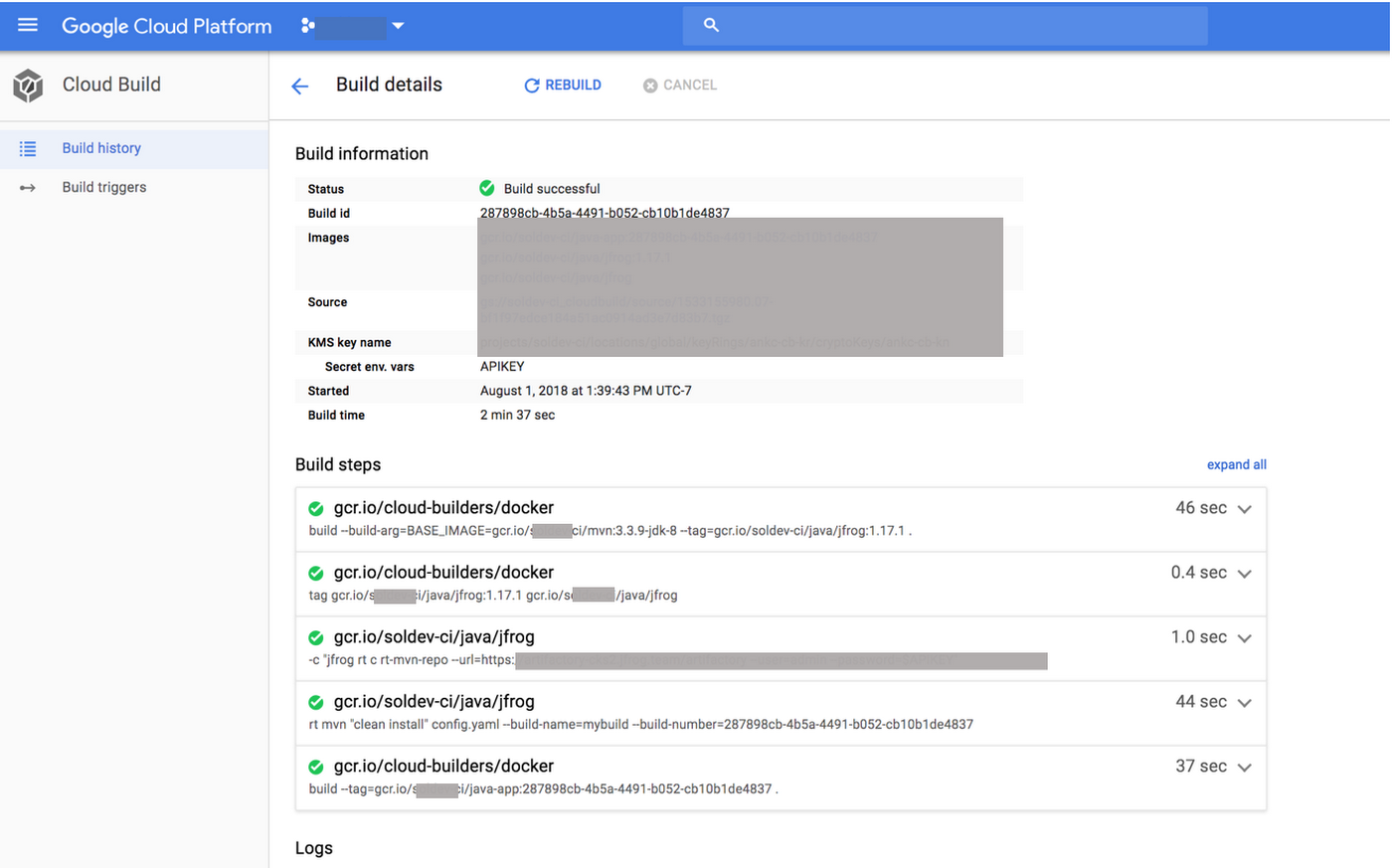
The status of a successful build will look like this:
Congratulations! You’ve successfully configured Google Cloud Build to work with JFrog Artifactory using Maven packages. To learn more about Cloud Build, read the documentation. To learn how to configure Artifactory for other package formats, check out our documentation, and happy building.