With software supply chain security, developers have a big role to play
Pali Bhat
Vice President of Product & Design
Try Google Cloud
Start building on Google Cloud with $300 in free credits and 20+ always free products.
Free trialWhen it comes to security headlines, 2021 has unfortunately been one for the record books. Colonial Pipeline, which supplies nearly half the United States East Coast’s gasoline, was the victim of a ransomware attack that forced it to take down its systems. Several high-profile breaches, on Kaseya, SolarWinds, Codecov, and others, gained global attention. To strengthen the U.S.’s cybersecurity profile, President Biden signed an executive order mandating changes for companies that do business with the federal government about how to secure their software.
While traditional security efforts have centered around securing the perimeter, the responsibility for security is increasingly falling to developers. Specifically, a key element of the executive order is focused on enhancing the security of the enterprise software supply chain. Securing the software supply chain entails knowing exactly what components are being used in your software products—everything that impacts your code as it goes from development to production. This includes having visibility into even the code you didn't write, like open-source or third-party dependencies, or any other artifacts, and being able to prove their provenance.
In a number of the above-mentioned events, attackers were able to exploit vulnerabilities in the software supply chain, for example, leveraging a downstream vulnerability that had gone unnoticed; injecting bad code; or using leaked credentials to access a CI/CD pipeline. These are all things that can be prevented by implementing strong software supply chain best practices.
At Google, securing the software supply chain is something to which we’ve given a lot of thought, for example, working with organizations like the National Institute of Standards and Technology (NIST) and the National Security Council (NSC) to develop guidelines. In the next couple of months, after consultation with the federal government, various private sector companies and academia, we plan to publish these guidelines together with NIST.
In the meantime, we’re hosting Building trust in your software supply chain on July 29, an event designed to explore this topic in depth. To get us started, I’ll be talking with a panel of industry experts:
Phil Venables, Chief Information Security Officer, Google Cloud, will talk about the White House executive order, what it means to enterprises, and how Google can help you follow it.
Eric Brewer, VP, Google Fellow, Google Cloud, will talk about some recent attacks, how they could have been avoided, and the role of open-source software and standards bodies in the future of cybersecurity.
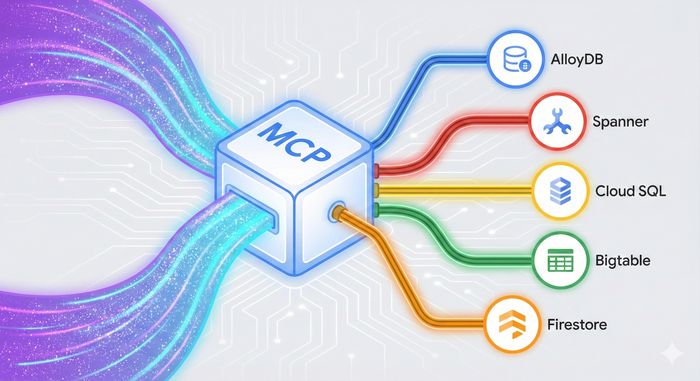
Aparna Sinha, Director, Product Management, Google Cloud will tell you about Google Cloud tools that leverage software supply chain best practices, and that you can use to make your builds more secure and compliant, simplify how you manage your open-source dependencies, and make policy management more scalable across your deployment.
Shane Lawrence, Staff Infrastructure Security Engineer, Shopify, will share how his company approaches security, and how that focus actually helps them increase their development velocity.
In a series of breakout sessions, you’ll also learn about software supply chain best practices, and how to implement them in your own organization. I’m looking forward to seeing you all. If you haven’t already done so, register here.