Why your risk assessments need the added insight of threat intelligence

Jamie Collier
Lead Threat Intelligence Advisor (Europe), Google Threat Intelligence Group
Enhance your cyber risk posture with robust threat metrics
If your company is planning to build a large software development team from scratch, you should want to understand any associated risks. In today’s software development world, the prominent use of open-source tools and software dependencies can make supply chain security one of the most important risks to manage. A cyber risk assessment can help business leaders understand those risks, yet cyber risk assessments are too often lopsided.
These assessments routinely detail mission-critical risks related to assets, vulnerabilities, and business priorities, but that’s only a partial view of the overall risk that organizations face. Many organizations still lack solid metrics on cyber threats and threat intelligence, a missed opportunity for business leaders to step in and make risk assessments more effective.
Honing the relevance of cyber risk assessment through threat intelligence is particularly important for organizations during a digital transformation. As nascent technologies are adopted, it’s vital for business leaders to understand how their risk posture is impacted.
Supply chain security is hardly a hypothetical. Inadequate protections of the software supply chain have led to some of the most damaging cyberattacks in recent years, including the Log4j vulnerability, which was exploited by a variety of threat actors and targeted many different technologies. In fact, as we noted in the whitepaper, 2021 was the first year Mandiant identified more supply chain compromises involving developer tools or software dependencies than compromises affecting final software products.
Cyber threat intelligence (CTI) can help risk assessment determine strategies to better manage the risk. In this case, some of those would include:
Utilizing a software bill of materials (SBOM) in conjunction with Google’s Supply chain Levels for Software Artifacts (SLSA) framework to document, understand, and track build components associated with application development.
Establishing a change control process and board for all enterprise hardware and software changes. This could include a centralized IT or IT security-managed process for downloading, testing, and pushing updates out to users.
Deploying an advanced endpoint security solution, such as an endpoint detection and response, to detect malicious behavior if a tainted software package is downloaded and executed.
Security assessments and audits should be an integral part of the software development lifecycle or continuous integration and deployment (CI/CD) pipeline for any internally developed software that is customer facing or integral to internal functions of the organization.
Practical steps on how CTI and risk professionals can work together are outlined in a new Mandiant whitepaper, Better Together: The Benefits of Integrating Cyber Threat Intelligence and Risk Management. CTI can inform more than just risk assessments, and can even play a role for executives in their broader strategic decision making. It can help with many situations, such as the risks associated with entering a new market, proceeding with a cloud adoption project, or collaboration with third parties.
Cyber risk and cyber threat intelligence confer clear benefits to organizations independently. However, their value multiplies exponentially when brought together. Mandiant has brought to Google Cloud an unparalleled insight into the threat landscape, which can inform an organization’s strategy throughout their digital transformation.
A strong understanding of the cyber threat landscape is essential within cyber risk management for three key reasons:
The dynamic nature of the threat landscape can quickly render static cyber risk assessments outdated. Whether the scourge of ransomware during the pandemic or the significant uptick of destructive cyber operations throughout the Russia-Ukraine conflict, global events directly shape cyber operations. By keeping abreast of these developments, organizations are better prepared against emerging threats.
Threat metrics help organizations focus on what really matters in an area prone to both over and under-correction. Many security functions spend too much time worrying about the cyber threats hitting the headlines. However, the media will often focus on novel and interesting threats, rather than those most likely to affect organizations. By contrast, accurate metrics on the threats impacting a particular region and sector help organizations to identify relevant threats through a more precise and evidence-led strategy.
An accurate threat picture helps security functions to maximize efficiency. All security functions operate in resource-constrained environments, and often struggle to keep on top of patching vulnerabilities or triaging the constant supply of security alerts. Threat metrics provide focus – for instance, helping organizations to prioritize patching vulnerabilities that are already being exploited or escalate alerts linked to active threats.
Unlock the benefits of a cyber threat profile
Organizations can kickstart more direct engagement with the threat landscape by developing a threat profile, which leverages CTI to produce a holistic view of external cyber threats relevant to a specific organization.
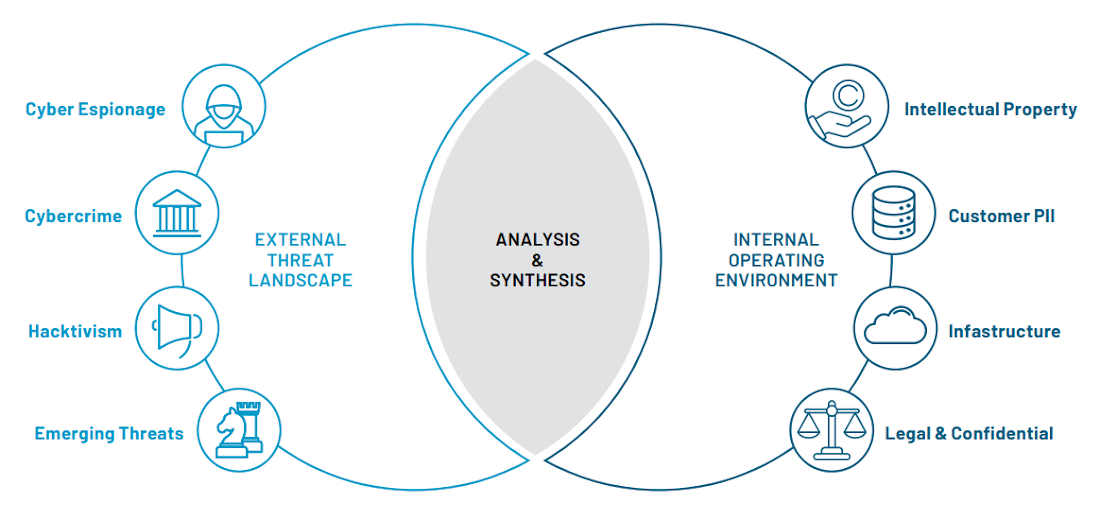
A cyber threat profile combines the externally facing threat landscape with a more introspective review of an organization's internal operating environment (including their people, processes, and technology). Once the pool of relevant cyber threats has been narrowed, a high-level dossier is created on recent operations and the tactics used by relevant threat actors. This forms an essential anchor document, guiding development on an intelligence-led approach to cyber risk by providing the key data needed to properly scope, prioritize, and describe cyber threats.
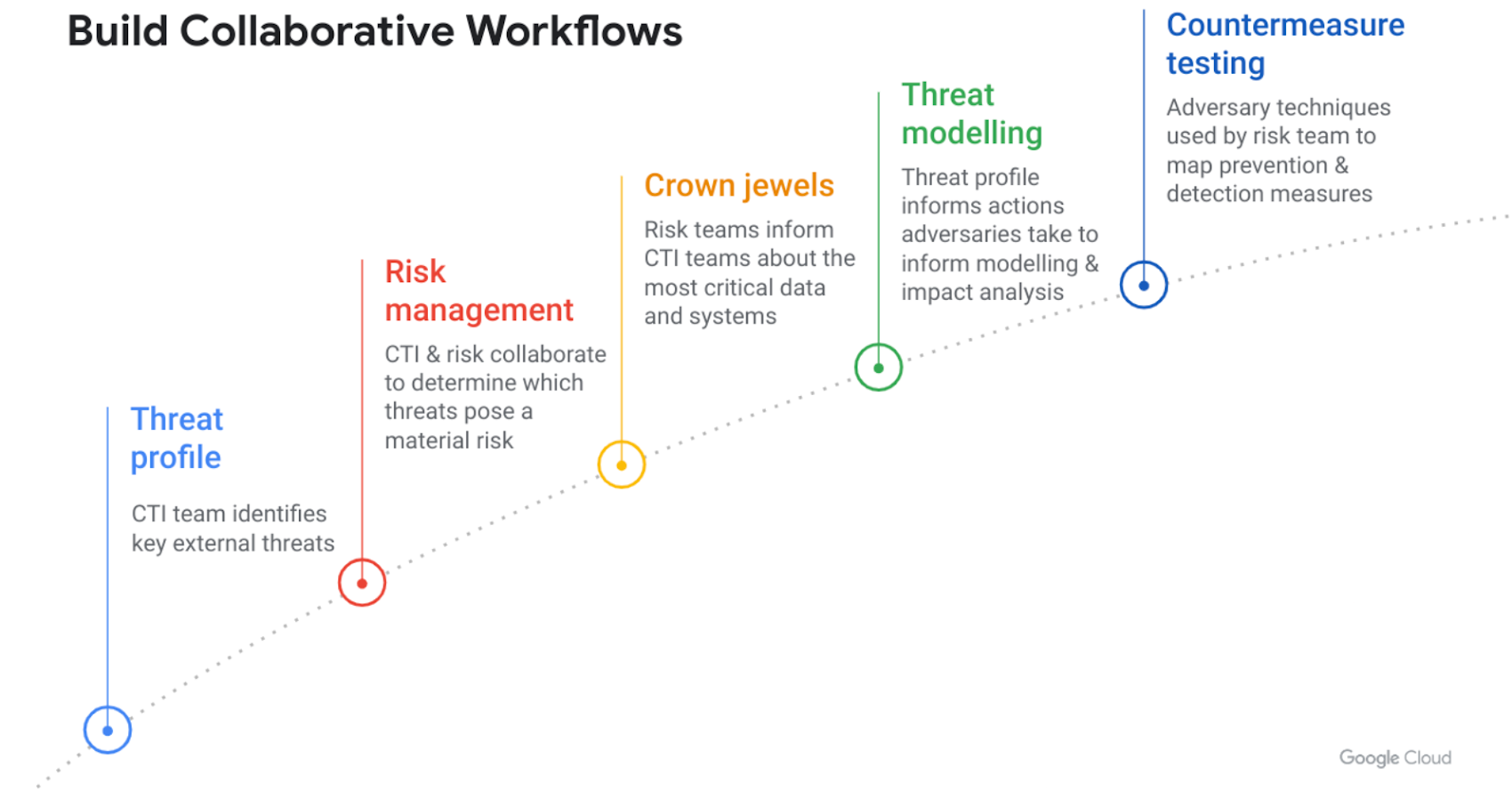
A threat profile not only documents relevant threats facing an organization, but can also serve as a catalyst for additional collaboration between CTI and cyber risk teams.
Developing collaborative workflows between CTI and cyber risk
There are many opportunities to embed cyber threat intelligence into risk management workflows. Threat modeling represents one of the most obvious and fruitful collaborative opportunities. This involves evaluating organizational security controls to reveal unknown risks and vulnerabilities within systems. Threat modeling provides insight into the types of cyber threat actors an organization faces and their potential impacts. It is also a key part of several frameworks, including Factor Analysis of Information Risk (FAIR) or Vocabulary for Event Recording and Incident Sharing (VERIS).
However, threat modeling is just one component of what can be a much broader collaborative workflow.
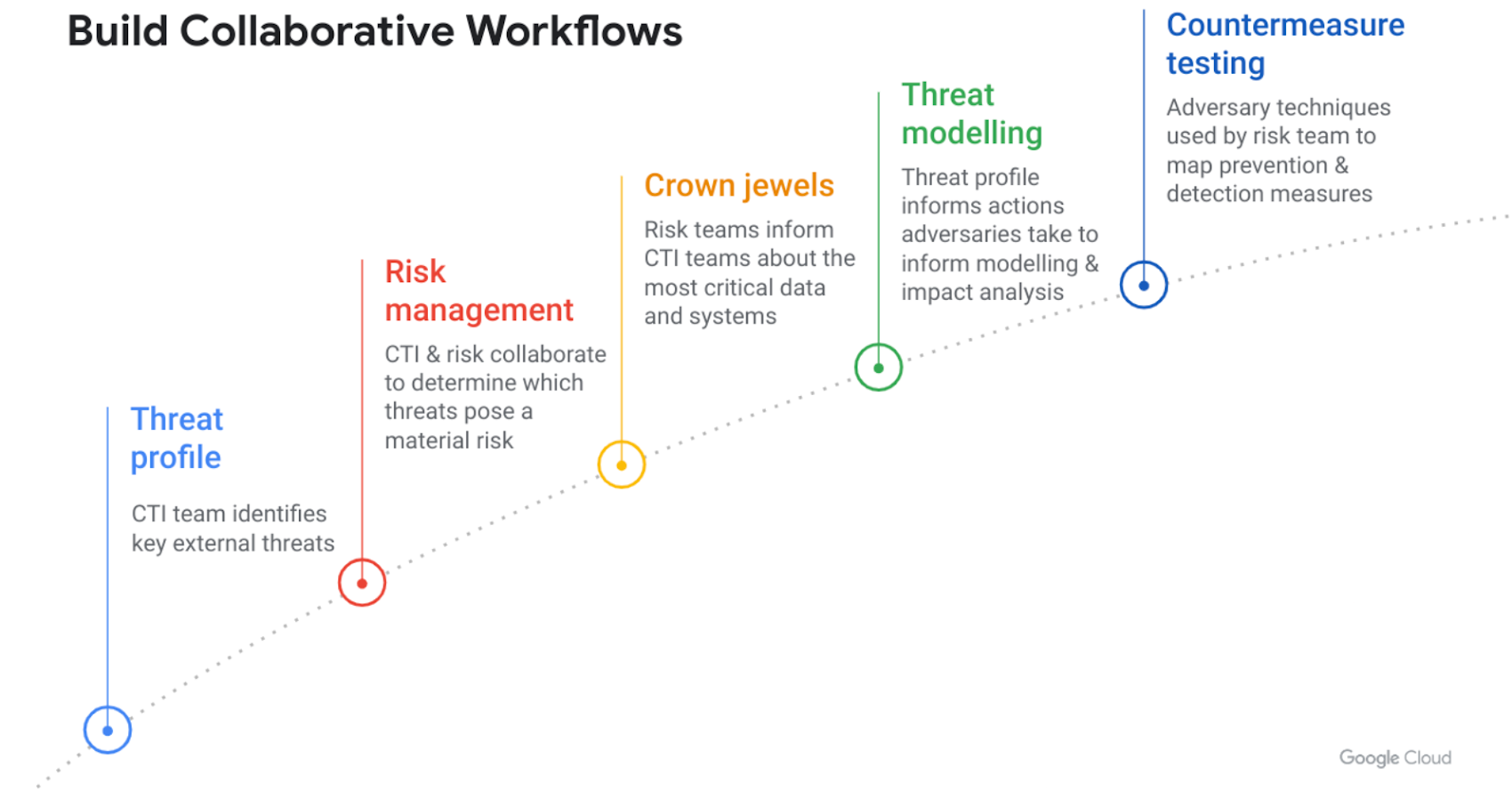
Further details on building intelligence-risk workflows are outlined in the whitepaper.
Cyber risk and CTI are both growing fields – and ones that increasingly require specialist skills. This means cyber risk and CTI professionals can understandably feel detached from each other's process. Yet, it is not necessary for each discipline to master the other's skills and knowledge base in order to engage. Instead, there are plenty and fruitful opportunities for an intelligence function to become a meaningful contributor to cyber risk.
Much like a good peanut butter and jelly sandwich, while cyber risk and CTI each offer benefits to organizations that utilize them, their value multiplies when brought together. An approach to cyber risk that is deeply connected to developments in the threat landscape can enable decision makers to adopt a genuinely evidence-led approach to confronting their most pressing and complex challenges.
The language and logic of risk assessments can help security staff to better communicate the potential danger associated with a threat development or a business decision in terms that boards, business leaders, and executives understand. These holistic risk assessments can further enable stakeholders across an organization to suggest better strategies for mitigating, avoiding, accepting, and transferring risk. Ultimately, they can help leaders make better-informed plans for their organization's future success.
To learn more, you can review Mandiant’s guides on cyber risk management and threat intelligence.