CARBANAK Week Part Two: Continuing the CARBANAK Source Code Analysis
Mandiant
Written by: Michael Bailey, James T. Bennett
Update (April 30): Following the release of our four-part CARBANAK Week blog series, many readers have found places to make the data shared in these posts actionable. We have updated this post to include some of this information.
In the previous installment, we wrote about how string hashing was used in CARBANAK to manage Windows API resolution throughout the entire codebase. But the authors used this same string hashing algorithm for another task as well. In this installment, we’ll pick up where we left off and write about CARBANAK’s antivirus (AV) detection, AV evasion, authorship artifacts, exploits, secrets, and network-based indicators (Part Three and Part Four are now available).
Antivirus Evasions
Source code unquestionably accelerates analysis of string hashes. For example, the function AVDetect in AV.cpp iterates processes to detect AV by process name hash as shown in Figure 1.
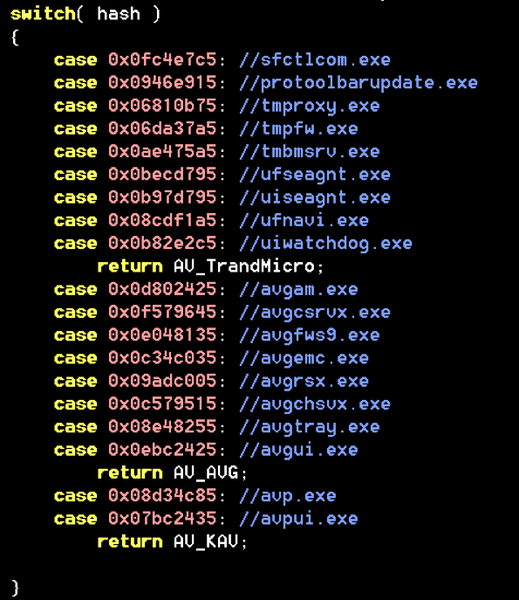
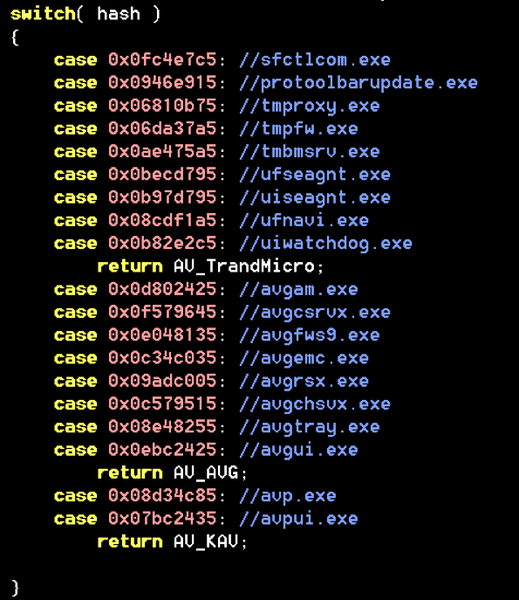
Figure 1: Antivirus detection by process name hash
What does CARBANAK do with this information? It evades AV according to what is installed. Figure 2 shows the code for an AVG evasion that the authors disabled by commenting it out. Based on this, it appears as if the AVG evasion was retired, but FLARE team member Ryan Warns confirmed in November 2017 that it still worked with one minor tweak. FLARE disclosed this to AVG immediately upon confirming it. Avast indicates that after our disclosure, they updated the affected DLL to ignore DLL_PROCESS_DETACH and leave its hooks in place.
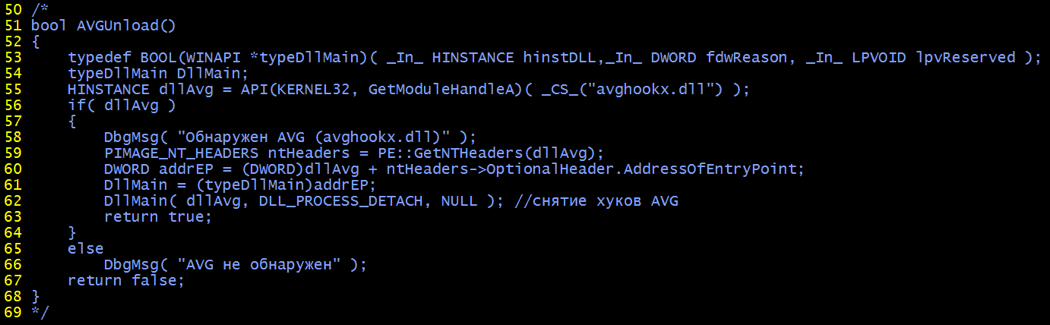
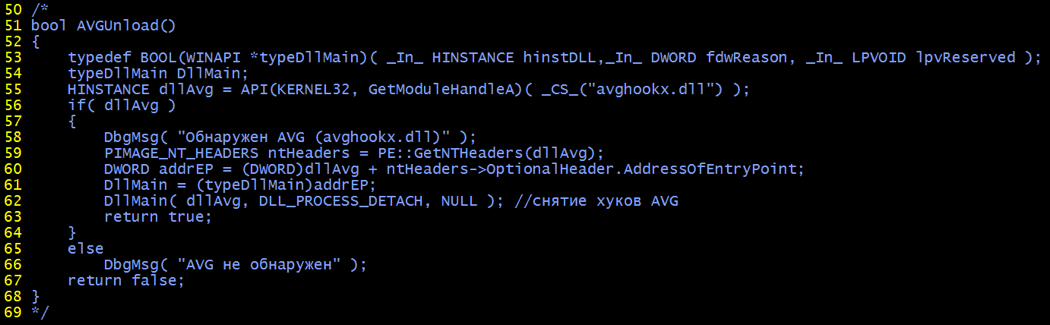
Figure 2: Commented out source code to unload AVG user-space hooks
In November of 2017, FLARE also disclosed an evasion for Trend Micro’s detection of process injection that remained active in the CARBANAK source code. The evasion mirrors a technique used in Carberp that replaces remote heap allocation and a call to CreateRemoteThread with memory mapping and queueing of an asynchronous procedure call via QueueUserAPC. Following our disclosure, Trend Micro indicated that they had updated their behavior monitoring rules and released OfficeScan XG SP1 in December 2017 with a new “Aggressive Event” detection feature that covers this behavior.
Author Characterization
Having source code could pose unique opportunities to learn about the individuals behind the keyboard. To that end, I searched for artifacts in the source code dump that might point to individuals. I found the most information in Visual Studio solution files. Most of these referenced drive O: as the source root, but I did find the following host paths:
- C:\Users\hakurei reimu\AppData\Local\Temp
- C:\Users\Igor\AppData\Local\Temp
- E:\Projects\progs\Petrosjan\WndRec\...
- E:\Projects\progs\sbu\WndRec\...
Unfortunately, these data points don’t yield many answers. If they are observed in later artifacts, connections might be inferred, but as of this writing, not much else is known about the authors.
Source Code Survey
The CARBANAK source code contained numerous exploits, previous C2 hosts, passwords, and key material. I decided to comprehensively search these out and determine if they led to any new conclusions or corroborated any previous observations.
Exploits
I wanted to know if the CARBANAK authors wielded any exploits that were not publicly disclosed. To the contrary, I found all the exploits to be well-documented. Table 1 breaks out the escalation code I reviewed from the CARBANAK source code dump.
Table 1: Exploits for elevation found in CARBANAK source code
The CARBANAK source code also contains code copied wholesale from Mimikatz including the sekurlsa module for dumping passwords from lsass.exe and Terminal Services patching code to allow multiple remote desktop protocol connections.
Secrets
My analysis included an audit of passwords and key material found in the source code and accompanying binaries. Although many of these were used for debug versions, I curated them for reference in case a need might arise to guess future passwords based on passwords used in the source code. Table 2 shows recovered passwords used for RC2-encrypted communications and other purposes along with the corresponding name in the source code and their status as they were encountered (active in source code, commented out, or compiled into a binary).
Table 2: Passwords found in CARBANAK source code and binaries
I found an encrypted server certificate in a debug directory. This seemed like it could provide a new network-based indicator to definitively tie operations together or catch new activity. It was trivial to brute force this container by adapting a publicly available code sample of X509 handling in C# to cycle through passwords in a popular password list. The password was found in less than 1 second because it was the single-character password “1”. The certificate turns out to be for testing, hence the weak password. The certificate is shown in Figure 3, with details in Table 3.
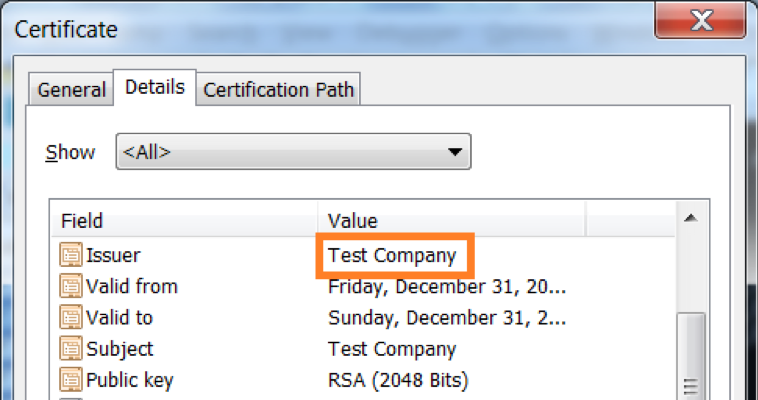
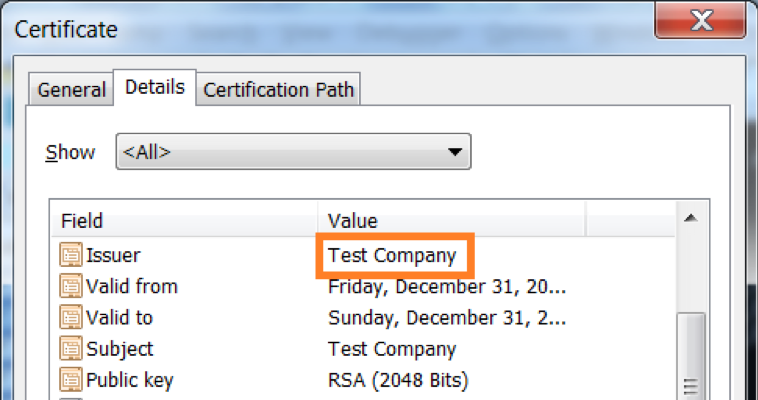
Figure 3: Test Company certificate
Table 3: Test Company certificate details
Here is a pivot shared by @mrdavi51 demonstrating how this self-signed certificate is still hosted on several IPs.
FireEye has observed the certificate most recently being served on the following IPs (Table 4):
Table 4: Recent Test Company certificate use
While these IPs have not been observed in any CARBANAK activity, this may be an indication of a common developer or a shared toolkit used for testing various malware. Several of these IPs have been observed hosting Cobalt Strike BEACON payloads and METERPRETER listeners. Virtual Private Server (VPS) IPs may change hands frequently and additional malicious activity hosted on these IPs, even in close time proximity, may not be associated with the same users.
I also parsed an unprotected private key from the source code dump. Figure 4 and Table 5 show the private key parameters at a glance and in detail, respectively.
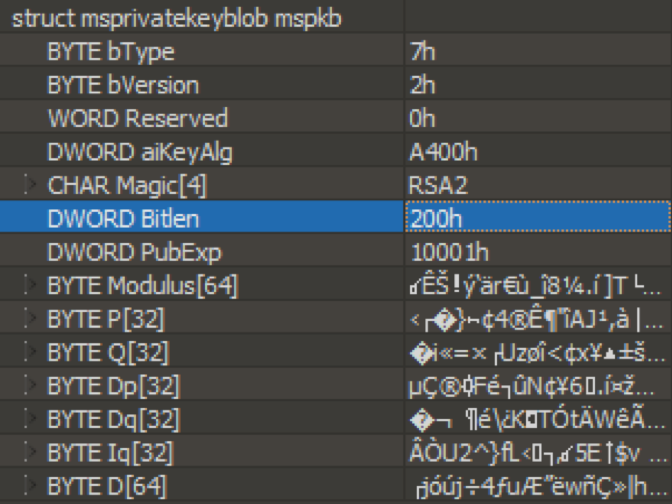
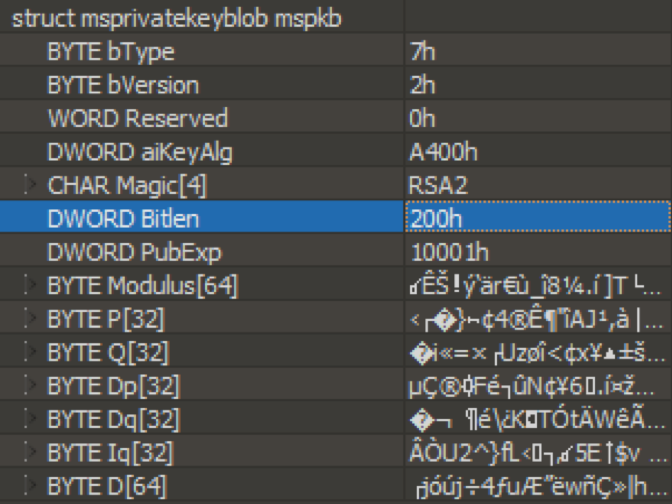
Figure 4: Parsed 512-bit private key
Table 5: Private key parameters
I found a value named PUBLIC_KEY defined in a configuration header, with comments indicating it was for debugging purposes. The parsed values are shown in Table 6.
Table 6: Key parameters for PUBLIC_KEY defined in configuration header
Network Based Indicators
The source code and binaries contained multiple Network-Based Indicators (NBIs) having significant overlap with CARBANAK backdoor activity and FIN7 operations previously observed and documented by FireEye. Table 7 shows these indicators along with the associated FireEye public documentation. This includes the status of each NBI as it was encountered (active in source code, commented out, or compiled into a binary). Domain names are de-fanged to prevent accidental resolution or interaction by browsers, chat clients, etc.
Table 7: NBIs and prevously observed activity
Four of these TCP endpoints (80.84.49[.]50:443, 52.11.125[.]44:443, 85.25.84[.]223, and 37.1.212[.]100:700) were new to me, although some have been documented elsewhere.
Conclusion
Our analysis of this source code dump confirmed it was CARBANAK and turned up a few new and interesting data points. We were able to notify vendors about disclosures that specifically targeted their security suites. The previously documented NBIs, Windows API function resolution, backdoor command hash values, usage of Windows cabinet file APIs, and other artifacts associated with CARBANAK all match, and as they say, if the shoe fits, wear it. Interestingly though, the project itself isn’t called CARBANAK or even Anunak as the information security community has come to call it based on the string artifacts found within the malware. The authors mainly refer to the malware as “bot” in the Visual Studio project, filenames, source code comments, output binaries, user interfaces, and manuals.
The breadth and depth of this analysis was a departure from the usual requests we receive on the FLARE team. The journey included learning some Russian, searching through a hundred thousand of lines of code for new information, and analyzing a few dozen binaries. In the end, I’m thankful I had the opportunity to take this request.
In the next post, Tom Bennett takes the reins to provide a retrospective on his and Barry Vengerik’s previous analysis in light of the source code. Part Four of CARBANAK Week is available as well.
