Private networking patterns to Vertex AI workloads
Ammett Williams
Developer Relations Engineer
Deepak Michael
Networking Specialist Customer Engineer
As enterprise strategic use cases for AI adoption increases, secure and reliable connectivity is more crucial than ever. Get ready to explore several private connections options for your Vertex AI workloads! In this blog, we'll dive into the existing options and reveal the services to get you connected on your AI journey.
Connectivity matrix
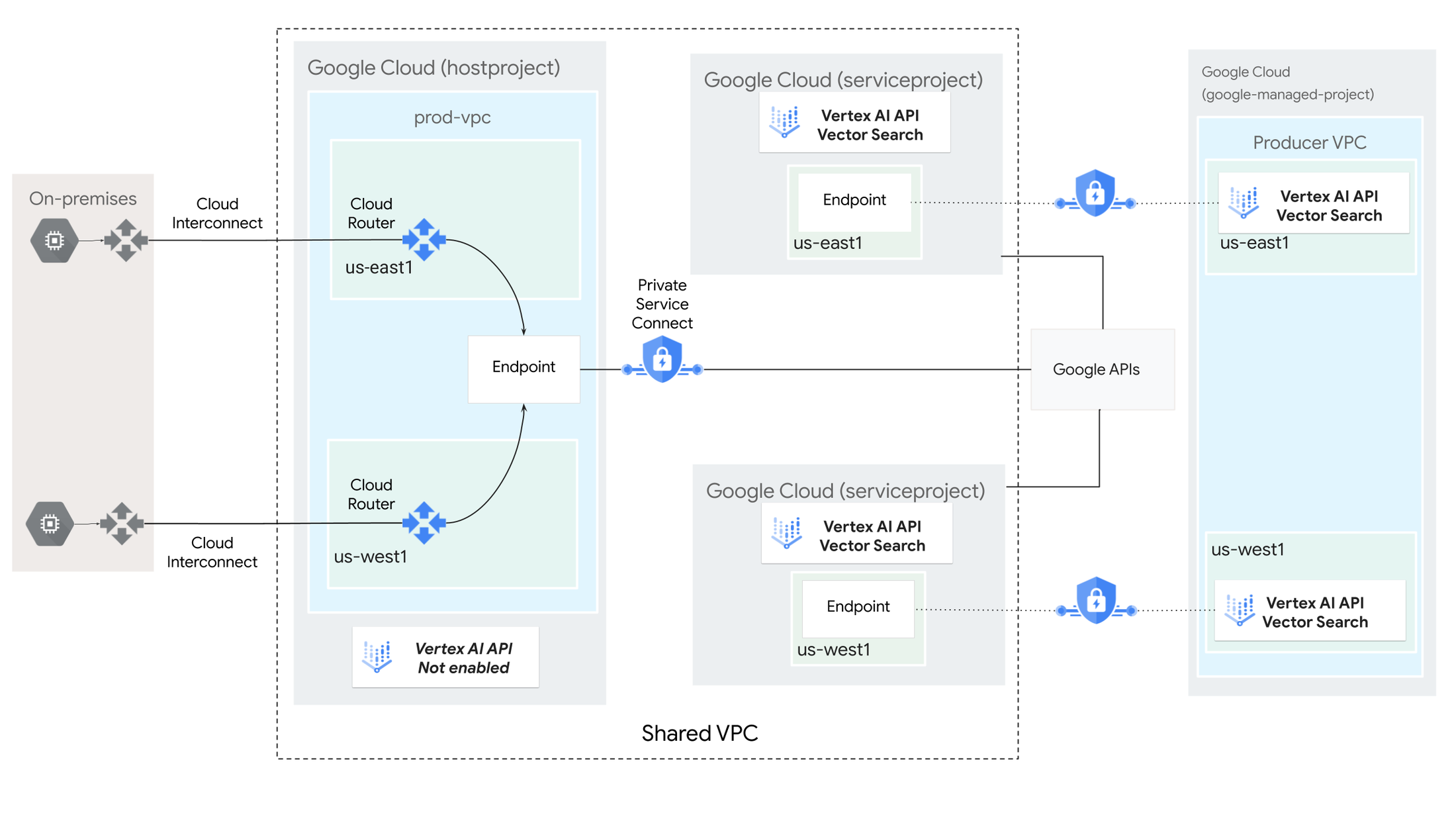
Vertex AI is a suite of products which provide different AI workloads that provide varying functionalities. The default method to access Vertex AI API’s are public which is the case with Google APIs in general. Depending on your architecture you may have the requirement to access your API’s privately, because of security and enterprise governance, which means traffic does not travel over the internet to the public address of the API. In these cases there are several options which we will explore later in the blog but it will vary depending on the Vertex AI product you are connecting to. The image below shows the connectivity matrix for accessing Vertex AI from on-premises and multicloud.


Options
As you can see from the previous matrix image there are several methods in addition to the public internet. These include:
-
Private Service Connect (PSC) for Google APIs - Provides private access to Google APIs over hybrid networking or within a Virtual Private Cloud (VPC) using a customer-specified IP address(s) and DNS endpoint name that can be leveraged for one or more use cases.
-
Private Google Access - Provides private access to Google APIs over hybrid networking or within a Virtual Private Cloud (VPC) using a Google defined subnet.
-
Private Service Access (PSA) - Google and other providers, collectively known as "service providers," can offer services hosted within a Google-managed VPC network. PSA enables you to define IP addresses for the managed services in addition to establishing VPC peering to access the internal IP addresses of these Google and third-party services over hybrid networking or within the VPC.
-
Private Service Connect endpoint - Enables consumers to securely access managed services hosted by Google or other providers from within their own Virtual Private Cloud (VPC) network or via hybrid networking, eliminating the need to define the producer's VPC network. Communication with managed services is established through PSC endpoints or backends defined by the consumer's IP space, facilitating multi-tenancy to producer services across VPCs.
Example
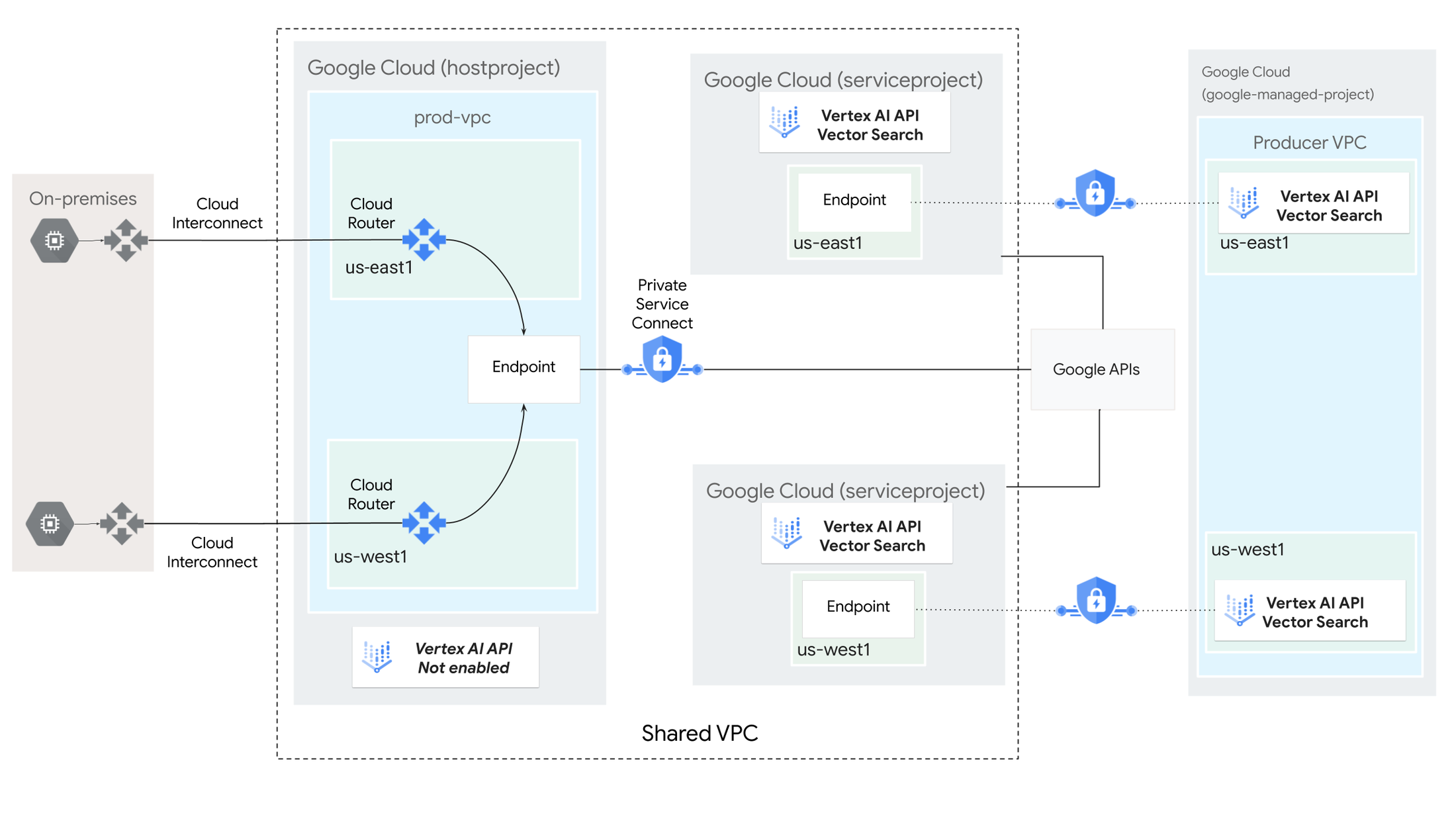
The following diagram shows a Vector Search architecture in which the Vector Search API is enabled and managed in a service project (appropriately named "serviceproject") as part of a Shared VPC deployment. The Vector Search Compute Engine resources are deployed as a Google-managed Infrastructure-as-a-Service (IaaS) in the service producer's VPC network.
Private Service Connect endpoints are deployed in the consumer's VPC network (serviceproject) for index query, in addition to Private Service Connect endpoints for Google APIs for private index creation deployed in the host project, the VPC where the cloud router resides. Both index creation and index query are accessible privately through hybrid networking or within the VPC.
If the organization requires public access to index query, you can leverage the same producer service as a Private Service Connect Network Endpoint Groups (PSC NEG) backend to a External Load Balancer, thereby enabling public access to the endpoint while also providing WAF and DDoS capabilities when associated with Cloud Armor.
Get hands-on and learn more
This topic is hot right now, and there are many approaches you can use. There are a few resources available that you can use to get some hands-on experience. Please check out the following tutorials.
-
Tutorial - Use Private Service Connect to access a Vector Search index from on-premises.
-
Tutorial - Use Private Service Connect to access Generative AI on Vertex AI from on-premises.
-
Tutorial - Use Private Service Connect to access Vertex AI online predictions from on-premises
-
Tutorial - Use Private Service Connect to access Vertex AI batch predictions from on-premises
To learn out more or share a thought find me on Linkedin.

