Google Cloud networking in depth: What’s new with Cloud DNS
Marshall Vale
Product Manager
Yang Liang
Product Marketing Manager
Editor’s note: At Google Cloud Next ‘19 we announced several additions to our networking portfolio, including new features for Cloud DNS. This blog post will get you into deep dive on those additions. Now, read on to learn more.
Google Cloud DNS is a scalable, reliable and managed authoritative Domain Name System (DNS) service that translates requests for domain names like www.google.com into IP addresses like 74.125.29.101. Running on the same high performing, low-latency and high availability infrastructure as Google, Cloud DNS is a cost-effective and easy way to make your applications and services available to your enterprise users.
In the past couple of months, we’ve launched many Cloud DNS networking features to make it easier for you to deploy and connect services on your private GCP networks. Today, let’s dive deeper into what we announced and how these new features can help you easily publish and manage millions of DNS zones and records from a simple user interface.
Private zones perform internal DNS resolution for your private GCP networks
Cloud DNS private zones (GA) provide an easy-to-manage internal DNS solution for your private GCP networks, eliminating the need to provision and manage additional software and resources. Since it restricts DNS queries for private zones to a private network, no one else can access your internal network information.
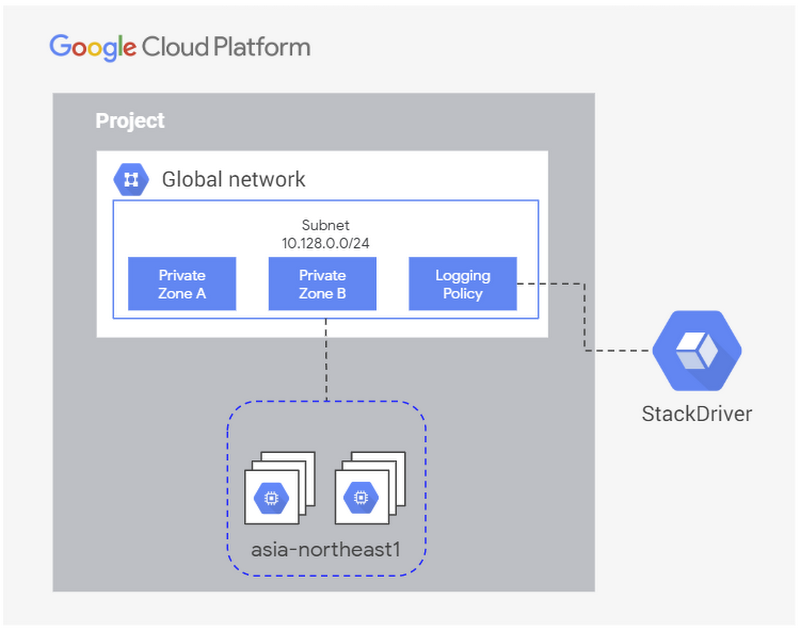
Cloud DNS private zones offers flexibility in your configurations by allowing multiple zones to be attached to a single VPC network. Additionally, support for split horizons allows you to have a private zone share the same name as a public zone while resolving to different IP addresses in each zone.
DNS peering allows one network to forward DNS requests to another network
When GCP networks are peered, they do not automatically share private DNS zones, DNS policies, or even internal DNS records. Cloud DNS peering, currently in beta, provides a second method for sharing DNS data. You can configure all or a portion of the DNS namespace to be sent from one VPC to another and, once there, it will respect the DNS policies or matching zones defined in the peered network.
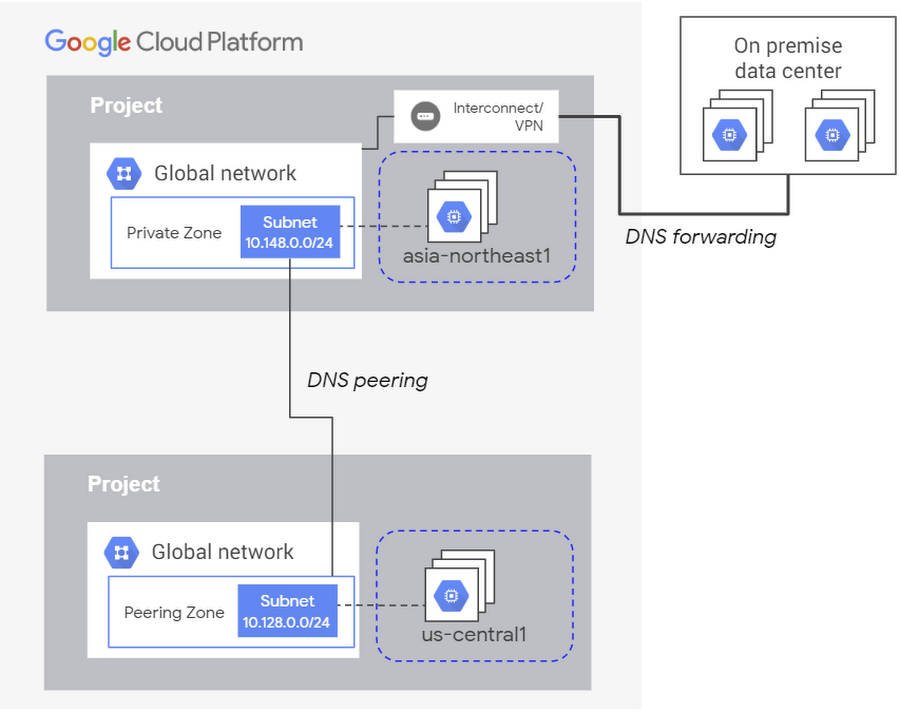
You can use DNS peering to connect multiple VPCs to your on-prem DNS service by setting up a hub and spoke model for your VPCs. Here, the hub VPC utilizes DNS forwarding to perform the hybrid connection, and the spoke VPCs uses DNS peering to connect to the hub VPC.
Cloud DNS can now export query logs and monitoring metrics from private zones to Stackdriver
With DNS logging and monitoring (beta), you can now view DNS logs for private zones in Stackdriver, and export them to any destination that Stackdriver Logging export supports. Logged queries can come from Compute Engine virtual machines, Google Kubernetes Engine containers in the same VPC network or peering zones, or they can come from on-premises clients via inbound DNS forwarding.
Monitoring metrics report on the DNS response types and the number of each response seen. Together these logs and metrics can help debug your DNS configuration or support DNS security analysis tools, so you can identify threats within your private networks.
Keeping up with Cloud DNS
Together, Cloud DNS private zones, peering, and logging improve the flexibility of your private cloud architecture, while providing you visibility into your private DNS traffic. Let us know how you plan to use these new networking services, and what capabilities you’d like to have in the future. You can learn more about GCP’s cloud networking portfolio online and reach us at gcp-networking@google.com.

