Private Service Connect: Now hybrid and global
Mark Church
Product Manager, GCP Foundation Services
Shaowen Ma
Product Manager, Google Cloud
Over the past couple years, private connectivity has become the de-facto method of accessing managed services in Google Cloud. Private Service Connect is a popular option because it provides an alternative to peering that eliminates shared scaling dependencies, improves security, and reduces IP coordination between the producer and consumer of a managed service. Thanks to these improvements, PSC is supported across a number of Google and third-party services. Now, we’re taking the next step with new options to enable hybrid access and global access across PSC endpoints. Read on to learn more.
Private Service Connect overview
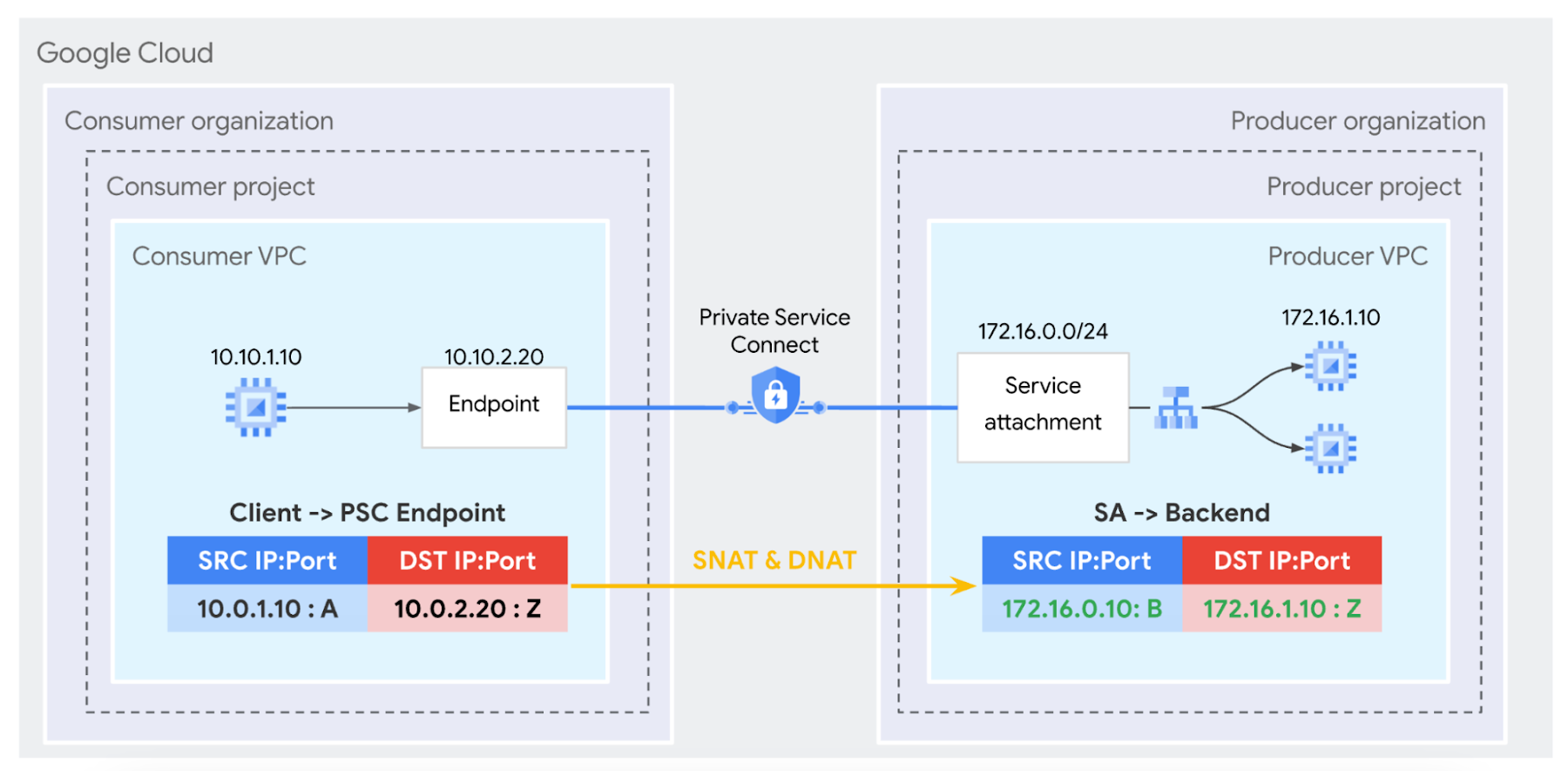
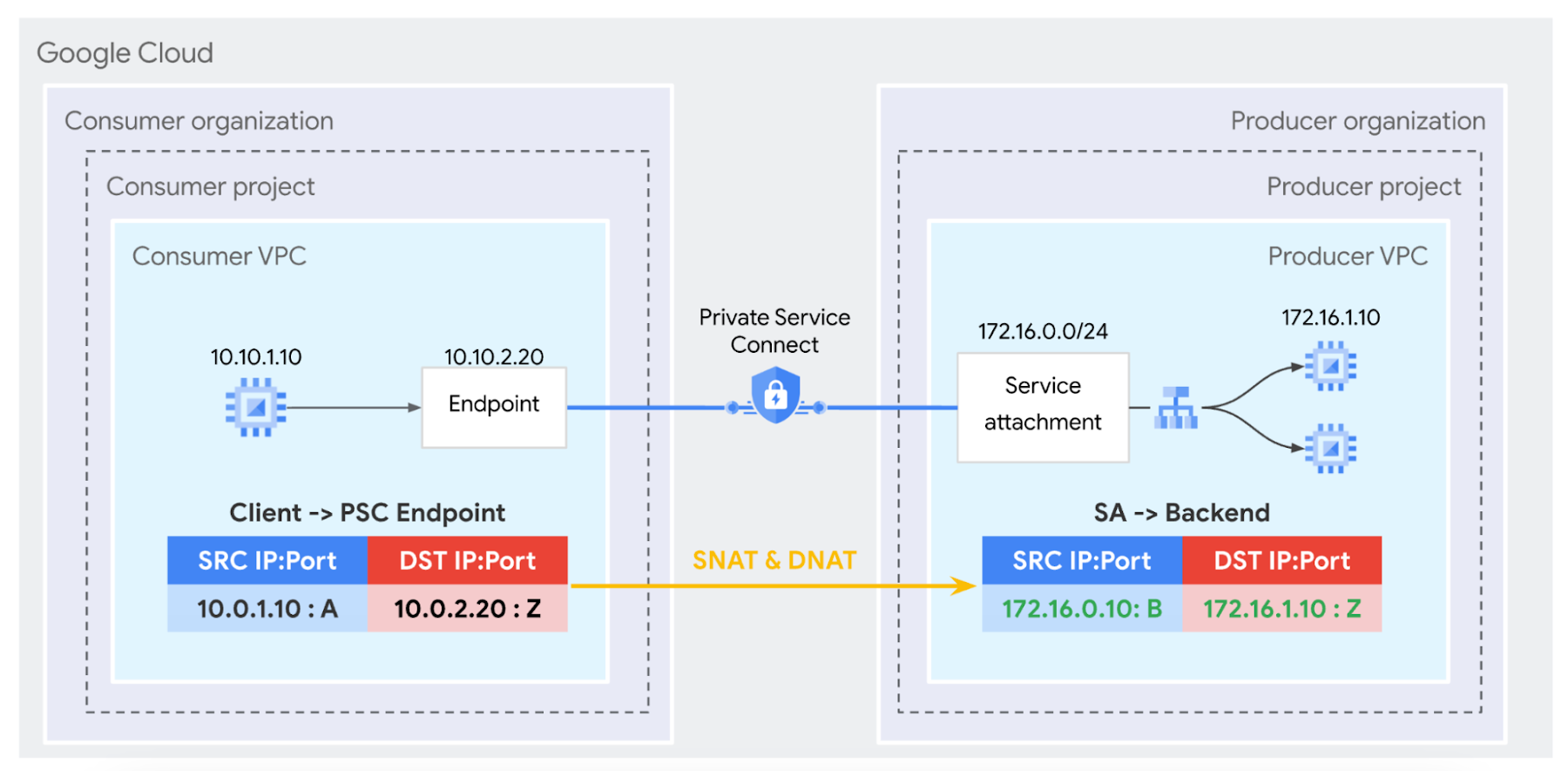
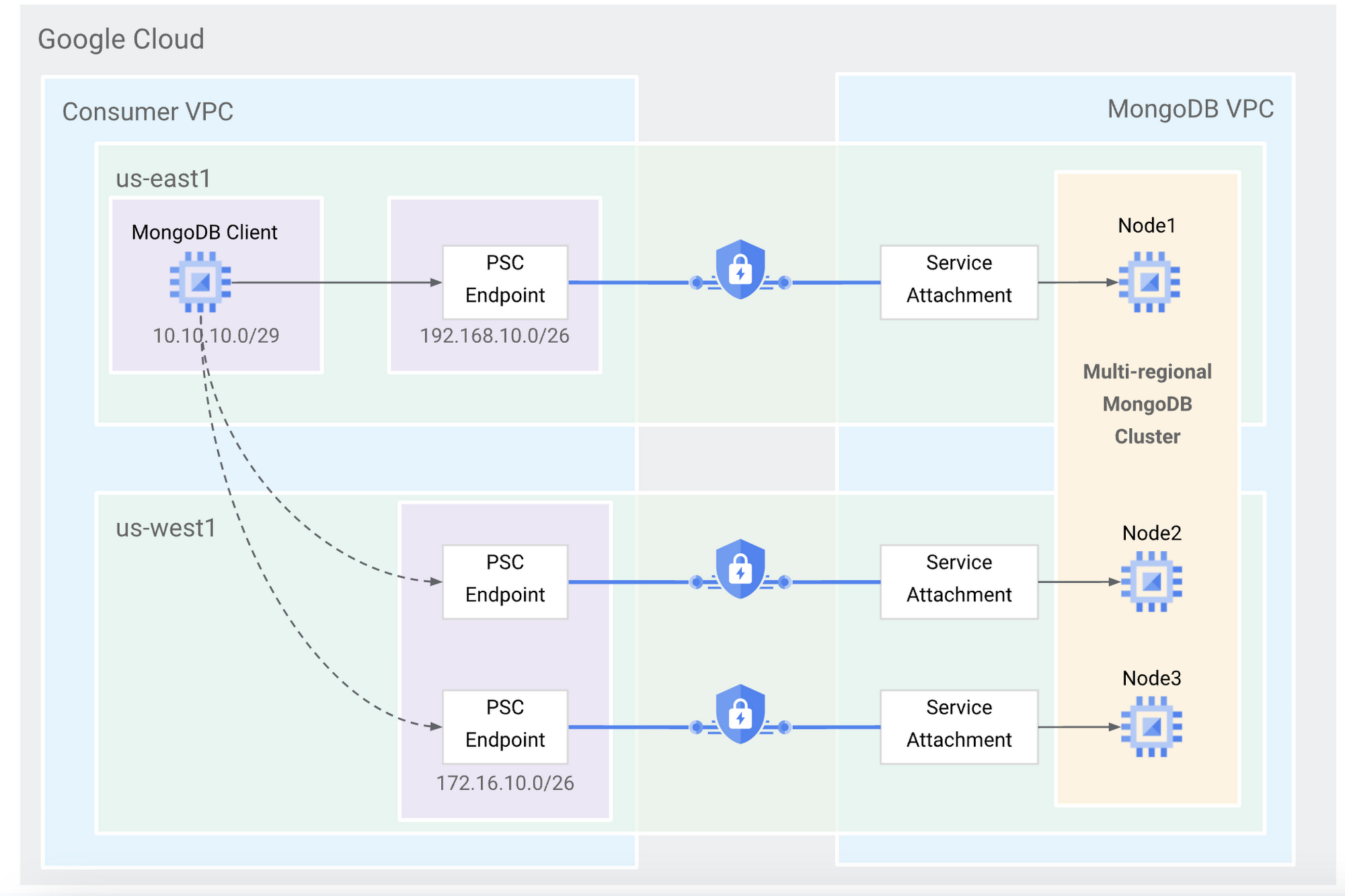
Private Service Connect eliminates complex dependencies between consumers and producers by using Network Address Translation (NAT) on the traffic between them (“NATing the traffic,” as it were). This means that all traffic between consumer and producer is NAT’d to the private address ranges specified by the respective consumer and producer. This allows each side to use the address ranges of their choosing without being aware or caring about how the other side is configured.
The below diagram shows how PSC works. The consumer PSC endpoint appears as a load balancer address in the consumer VPC. All traffic sent to the PSC endpoint is NAT’d and is sourced from the service attachment NAT subnet in the producer VPC which goes directly to the published service. This allows a producer to be very explicit with what they publish and share to consumers. This improves the security posture when establishing connectivity between independent parties — only the desired service must be published and nothing more. This is fundamental to service networking.
Private Service Connect’s unique architecture also provides:
Line-rate VM-to-VM latency and bandwidth
No bandwidth limits or latency hits. PSC traffic is routed directly from consumer host to producer host.
No middle proxy. All load balancing and NAT’ing is performed directly on the consumer and producer hosts.
Hybrid access
Several months ago Private Service Connect introduced the ability for Interconnect traffic to reach published services through Private Service Connect endpoints, allowing on-premises and multi-cloud clients to access managed services in Google Cloud privately. See Accessing Endpoints from Hybrid Networks to learn more.
Global access
Today, we’re introducing Private Service Connect global access to Preview, so that PSC endpoints can be accessed by clients from any region in Google Cloud. When global access is enabled, Traffic from Compute Engine VMs, Cloud VPN tunnels, and Cloud Interconnect can reach Private Service Connect endpoints in different regions. While PSC endpoints must still be in the same region as the service attachment, the flow of traffic between the client and the PSC endpoint can be across regional boundaries.
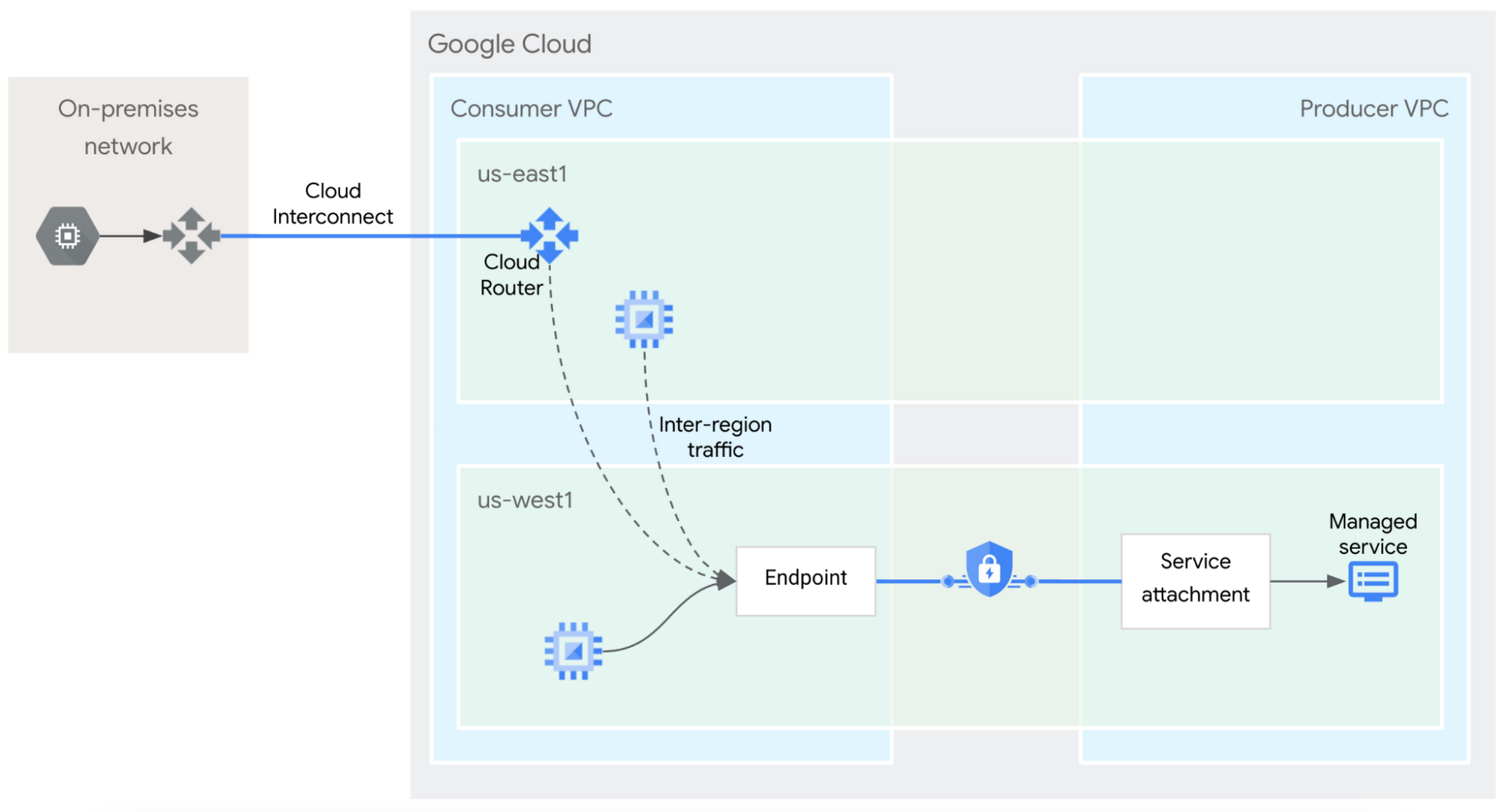
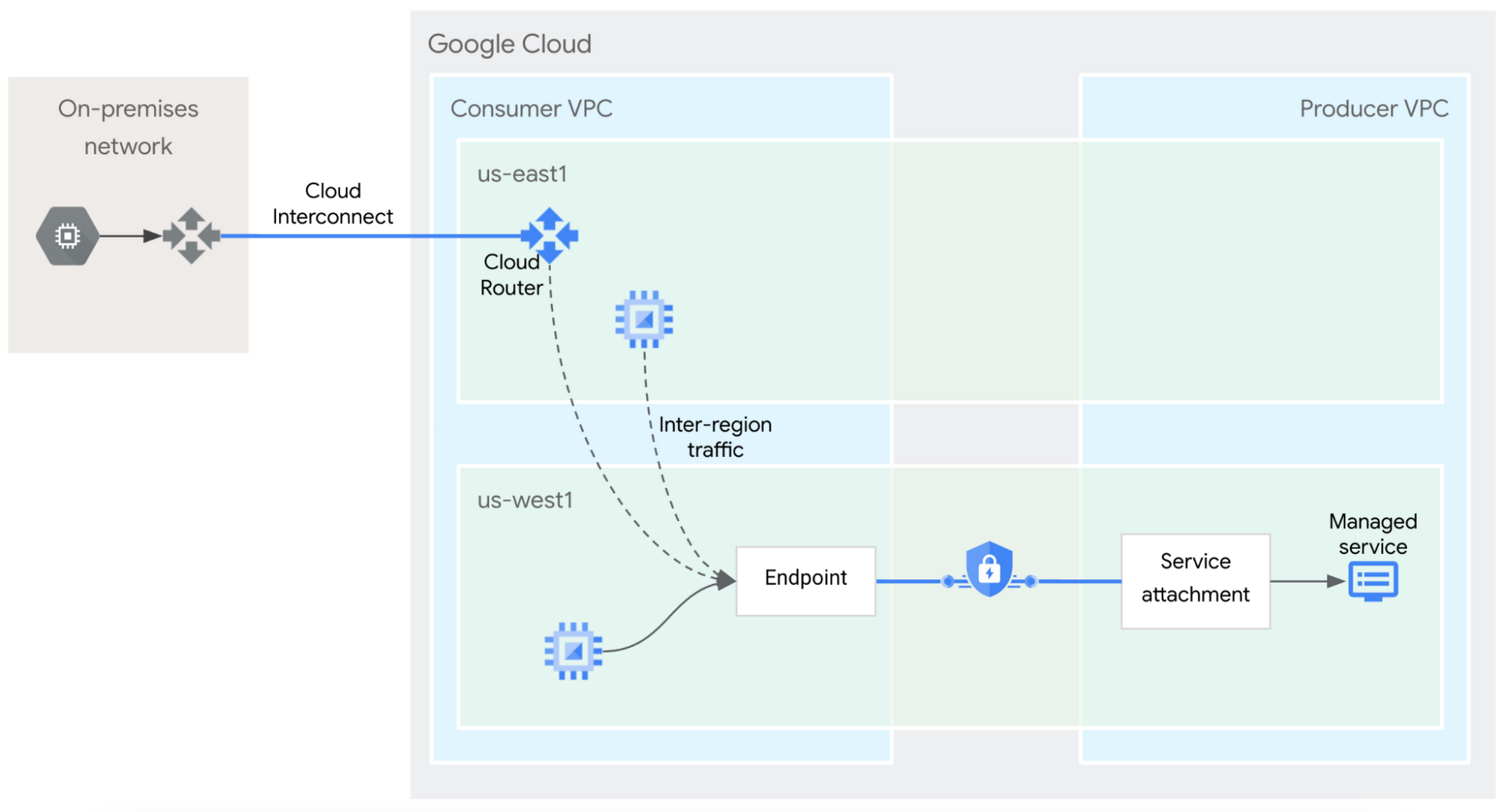
Because Google Cloud supports global VPCs, it’s easy to enable global access on new or existing PSC endpoints. Simply apply the following command on an existing or new PSC forwarding-rule and global access is enabled without any traffic disruption. Enabling global access is a consumer-side configuration that does not require any changes for the producer. This allows consumers to easily and seamlessly enable access to their managed services from any region.
Multi-regional services
Customers have already started to deploy different managed services with global access to enable new high-availability architectures.
MongoDB Atlas is one such service that supports global MongoDB clusters. By enabling global access on PSC endpoints, MongoDB clients can access MongoDB nodes in any region, improving the reliability and fault tolerance of the overall system.
Follow this step-by-step tutorial Accessing multi-regional MongoDB Atlas with Private Service Connect to configure PSC global access for MongoDB Atlas clusters.
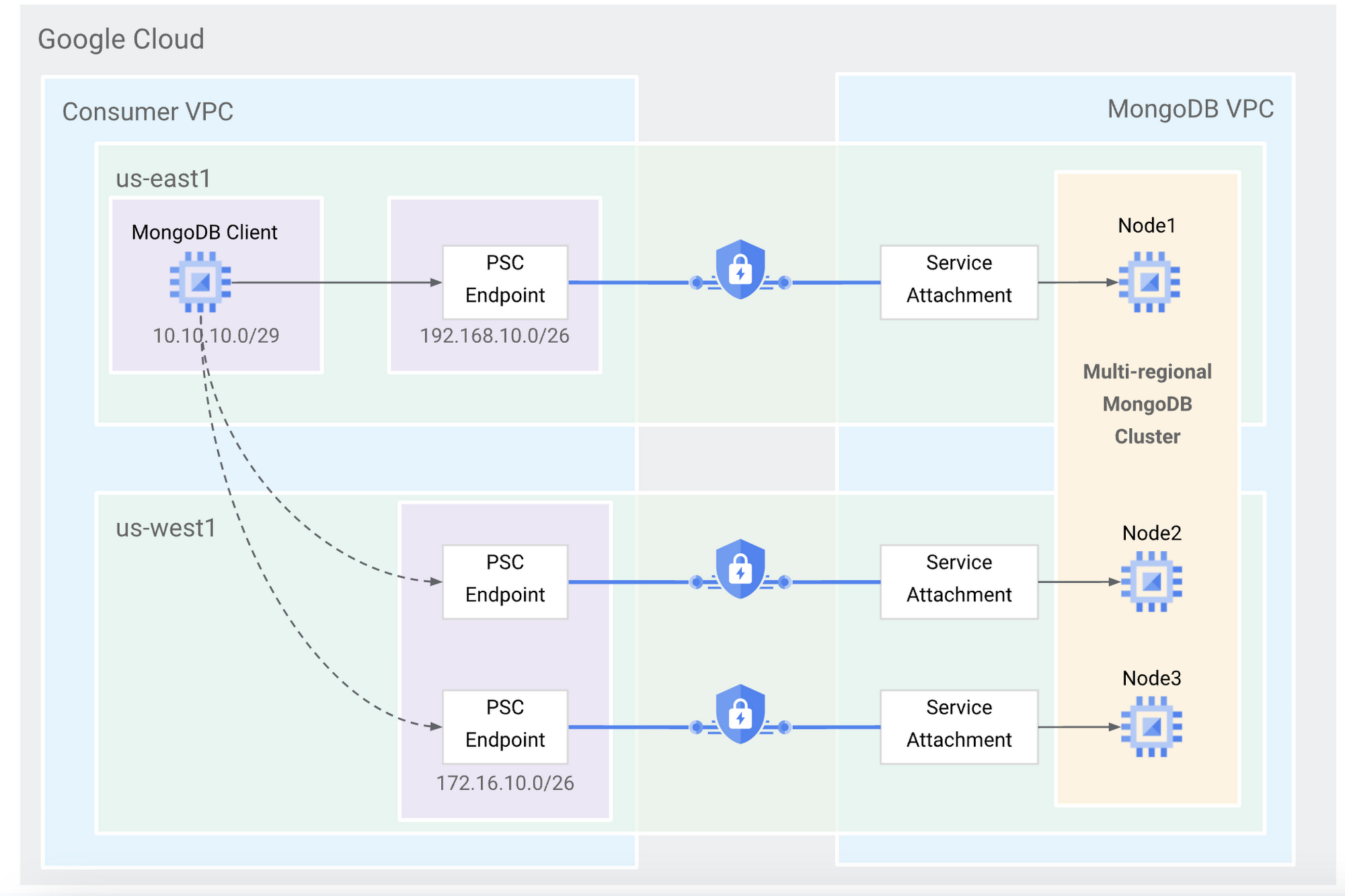
“Global access for Private Service Connect is a game changer. Along with the many other improvements that PSC has received since launch, global access enables customers to connect to their globally distributed MongoDB clusters from anywhere, whether that’s a different region or an on-premises data center — this allows customers to reach the highest levels of scale and availability while preserving a simple user experience.” - Chris Shum, Product Lead, MongoDB
Built on Apache Kafka, Confluent is another cloud-native, managed service that supports deployment across all environments and multi-regional connectivity patterns. Using PSC global access, Confluent Cloud can now be accessed completely privately and across regional boundaries for the highest level of security and high availability. See how to Configure Private Service Connect with Confluent.
“Global access has been a big differentiator for Confluent Cloud, enabling resilient multi-regional architectures with ease. The simplicity with which Google enables global managed services is very unique and it’s one more thing that makes it great to run Confluent on Google Cloud.” - Dan Rosanova, Sr. Director of Product Management, Confluent Cloud
Improving the managed services experiences
With global access and hybrid access Private Service Connect now offers the same communication flows that are possible within a single VPC. This makes it even easier to use managed services in the same way that consumers used self-hosted services. Private Service Connect further helps users to:
Secure their communications with fully private networking
Reduce complex coordination between consumer and producer
Eliminate resource and scale dependencies between consumer and producer
In short, Private Service Connect provides better security to your applications without sacrificing the user experience or scalability. And now thanks to global access, you don’t have to sacrifice on global connectivity either.

