Introducing Cloud HSM beta for hardware crypto key security
Il-Sung Lee
Senior Product Manager, Google Cloud
Data protection is a top consideration when running enterprise workloads in the cloud. At Google Cloud Platform (GCP), we offer numerous options to encrypt your data, including our default data-at-rest encryption (we’re proud to be the only cloud provider that encrypts all customer data at rest) as well as our Cloud Key Management Service (KMS) which allows explicit encryption of blocks of data with a key under your control. But we’ve heard from many of you that you’d like even more options that help you protect your most sensitive information assets and meet compliance mandates.
That’s why we’re excited to announce the availability of the beta release of Cloud HSM, a managed cloud-hosted hardware security module (HSM) service. Cloud HSM allows you to host encryption keys and perform cryptographic operations in FIPS 140-2 Level 3 certified HSMs (shown below). With this fully managed service, you can protect your most sensitive workloads without needing to worry about the operational overhead of managing an HSM cluster.


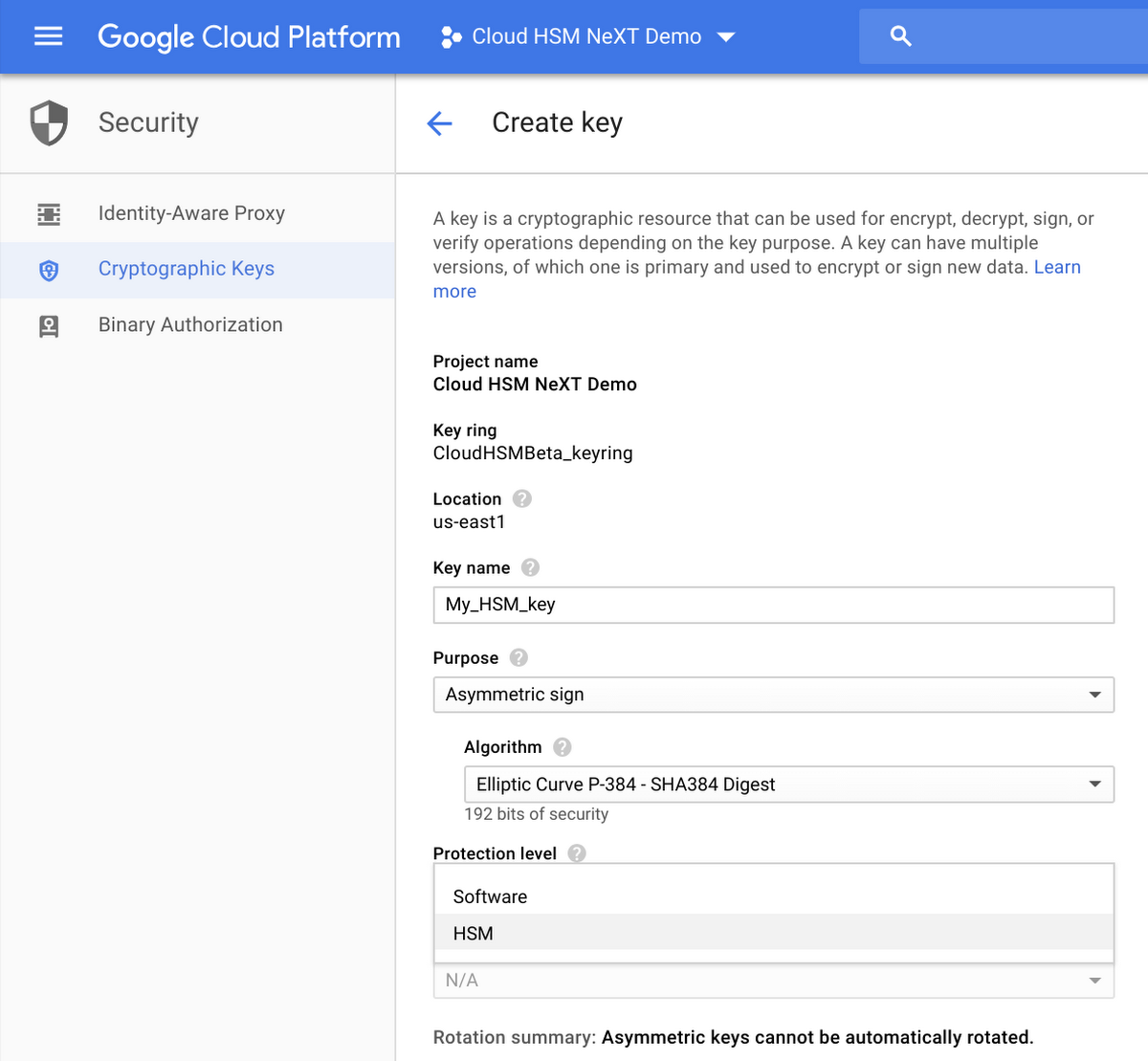
By operational overhead, we mean tasks like cluster management, scaling, and upgrades. You control your use of the Cloud HSM service through the regular Cloud KMS APIs, and the Cloud HSM service will take care of the patching, scaling, and clustering automatically with no downtime. You can see the interface here:
And because the Cloud HSM service is tightly integrated with Cloud KMS, you can now protect your data in customer-managed encryption key-enabled services, such as BigQuery, Google Compute Engine, Google Cloud Storage and DataProc, with a hardware-protected key.
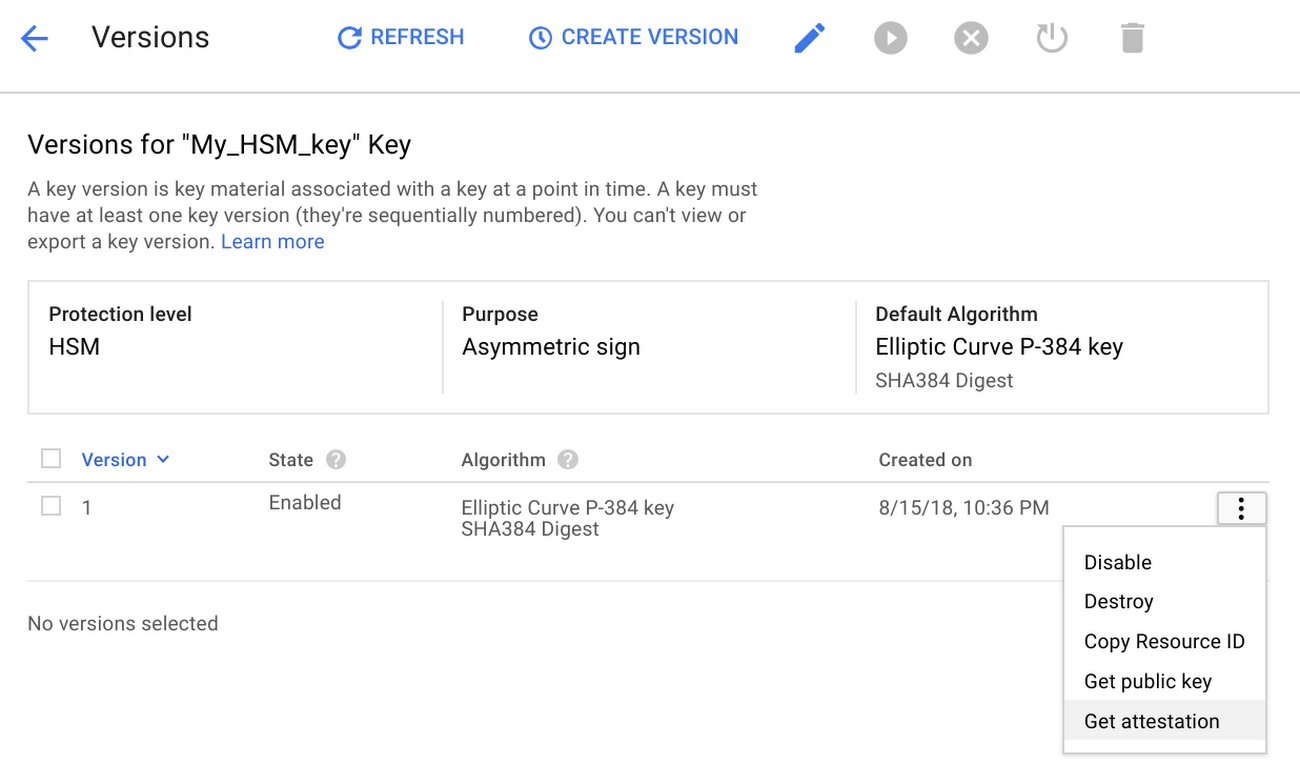
For those of you managing compliance requirements, Cloud HSM can help you meet regulatory mandates that require keys and crypto operations be performed within a hardware environment. In addition to using FIPS 140-2 certified devices, Cloud HSM will allow you to verifiably attest that your cryptographic keys were created within the hardware boundary, as shown here:
It’s easy to get started with Cloud HSM directly from the Google Cloud Platform console. To learn more, visit the Cloud HSM homepage or check out the documentation.
Introducing asymmetric key support
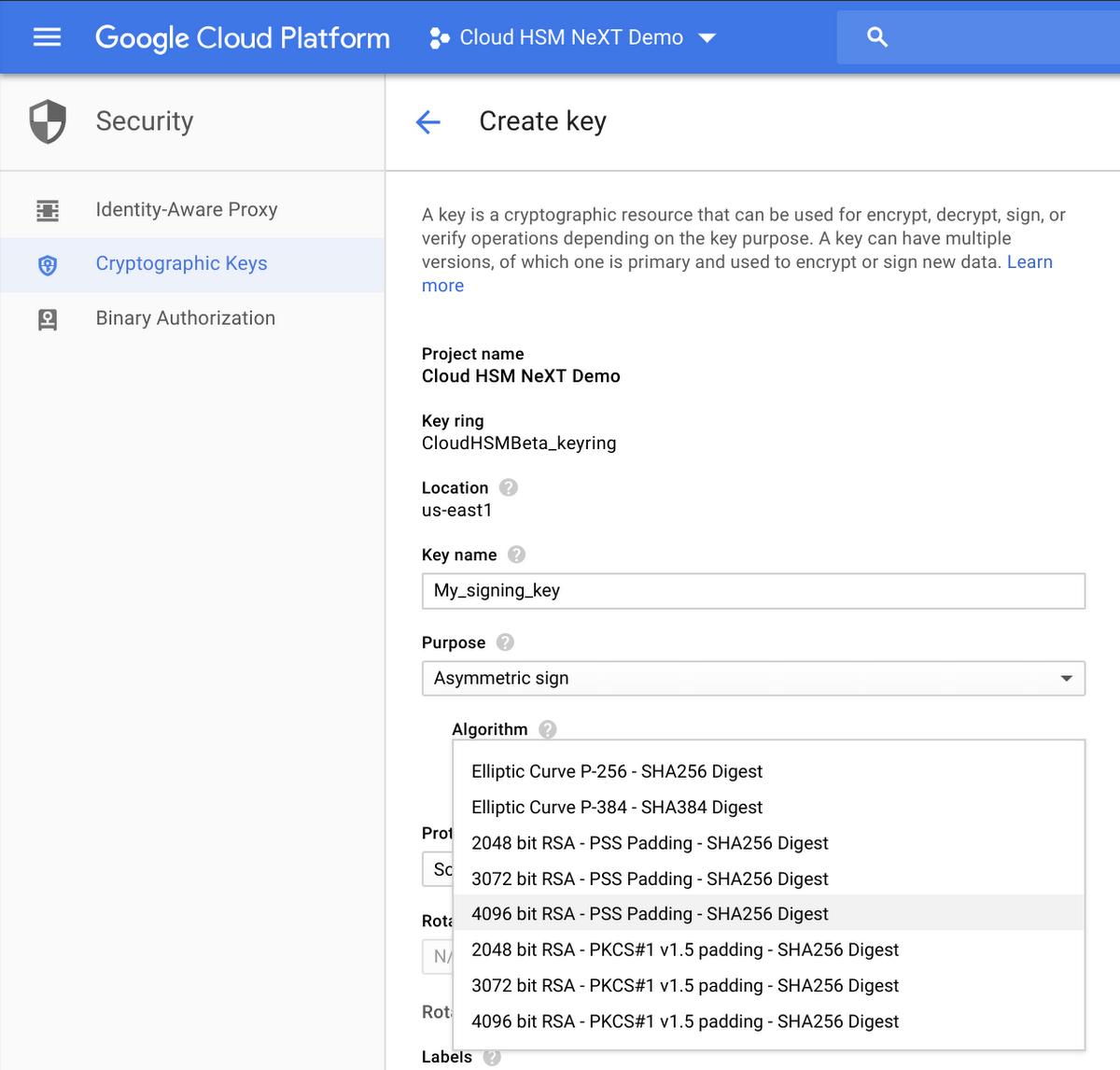
In addition to Cloud HSM, we’re excited to announce the beta release of asymmetric key support for both Cloud KMS and Cloud HSM. In addition to symmetric key encryption using AES-256 keys, you can now create various types of asymmetric keys for decryption or signing operations, which means that you can now store your keys used for PKI or code signing in a Google Cloud managed keystore. Specifically, RSA 2048, RSA 3072, RSA 4096, EC P256, and EC P384 keys will be available for signing operations, while RSA 2048, RSA 3072, and RSA 4096 keys will also have the ability to decrypt blocks of data. Check out the documentation for more information, and take a look at the interface here: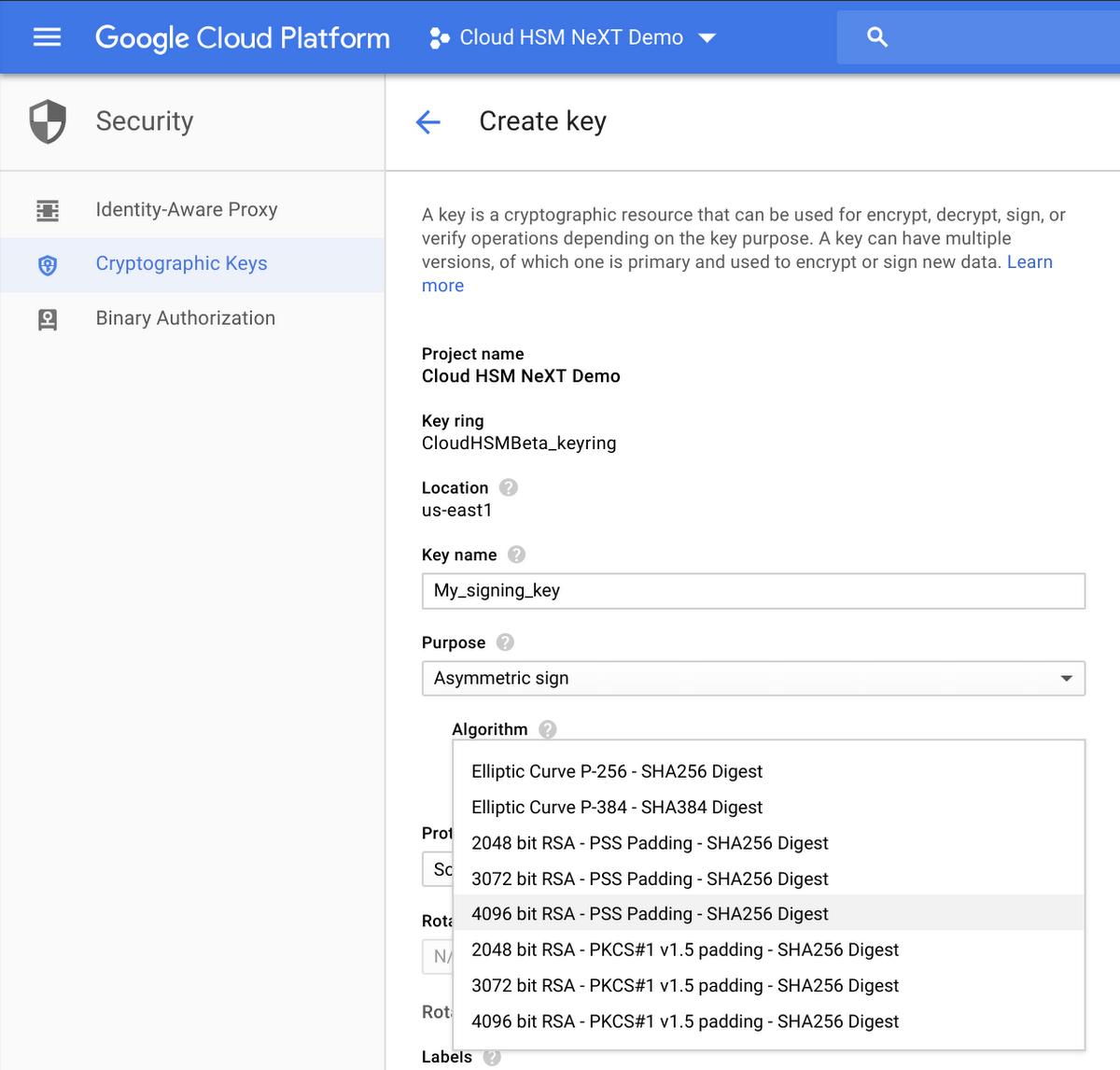
Further HashiCorp Vault integration with Cloud KMS
Finally, we’re glad to share great news around HashiCorp Vault’s support for Cloud KMS. You can now use Google Cloud KMS or Cloud HSM to encrypt HashiCorp Vault tokens at rest with the GCP Cloud KMS Vault Token Helper. Vault's default token helper stores tokens as plaintext on disk. With this new feature, the GCP token helper encrypts those tokens using Cloud KMS or Cloud HSM keys and stores the encrypted values on disk. The Vault token helper automatically makes all the necessary API calls for encrypting/decrypting the data, so the user experience is unchanged.
You can get started with Cloud HSM today. To learn more, visit the Cloud HSM homepage or check out the documentation.

