How to strengthen supply chain security with GKE Security Posture
Amit Bapat
Product Manager, Google Cloud Security
Poonam Lamba
Product Manager, Google
The security of the software supply chain is a complex undertaking for modern enterprises. Securing the software supply chain, particularly build artifacts like container images, is a crucial step in enhancing overall security. To provide built-in, centralized visibility into your applications, we are introducing software supply chain security insights for your Google Kubernetes Engine workloads in the GKE Security Posture dashboard.
Our built-in GKE Security Posture dashboard can provide opinionated guidance to help improve the security posture of your GKE clusters and containerized workloads. It includes insights into vulnerabilities and workload configuration checks. The dashboard also clearly points out which workloads are affected by a security concern and provides actionable guidance to address it.
More transparency with GKE security posture dashboard
To boost transparency and control over your software supply chain, we are introducing a new “Supply Chain” card within the GKE Security posture dashboard. Now available in public preview, this powerful feature allows you to visualize potential supply chain risks associated with your GKE workloads.
In this initial launch we provide two key insights:
-
Outdated images: Identify all images that have not updated in the last 30 days, potentially exposing you to recent vulnerabilities.
-
“Latest” tag usage: Gain clarity on images still using generic “latest” tag, hindering precise version control and traceability.
Our Binary Authorization service scans your images running in GKE clusters. You can view a summary of concerns on the “Supply Chain” card and drill down for further details in the “Concerns” tab within the GKE Security Posture dashboard.
Follow these steps to view the supply chain concerns:
1. Navigate to the GKE Security Posture page in the Google Cloud console. Note: You need to enable Security Posture if you haven’t already done so.
2. On the “Supply Chain” card, click “Enable Binary Authorization API” and then click on “Enable”.
3. On the next pop-up titled “Supply Chain” and click “Enable”.
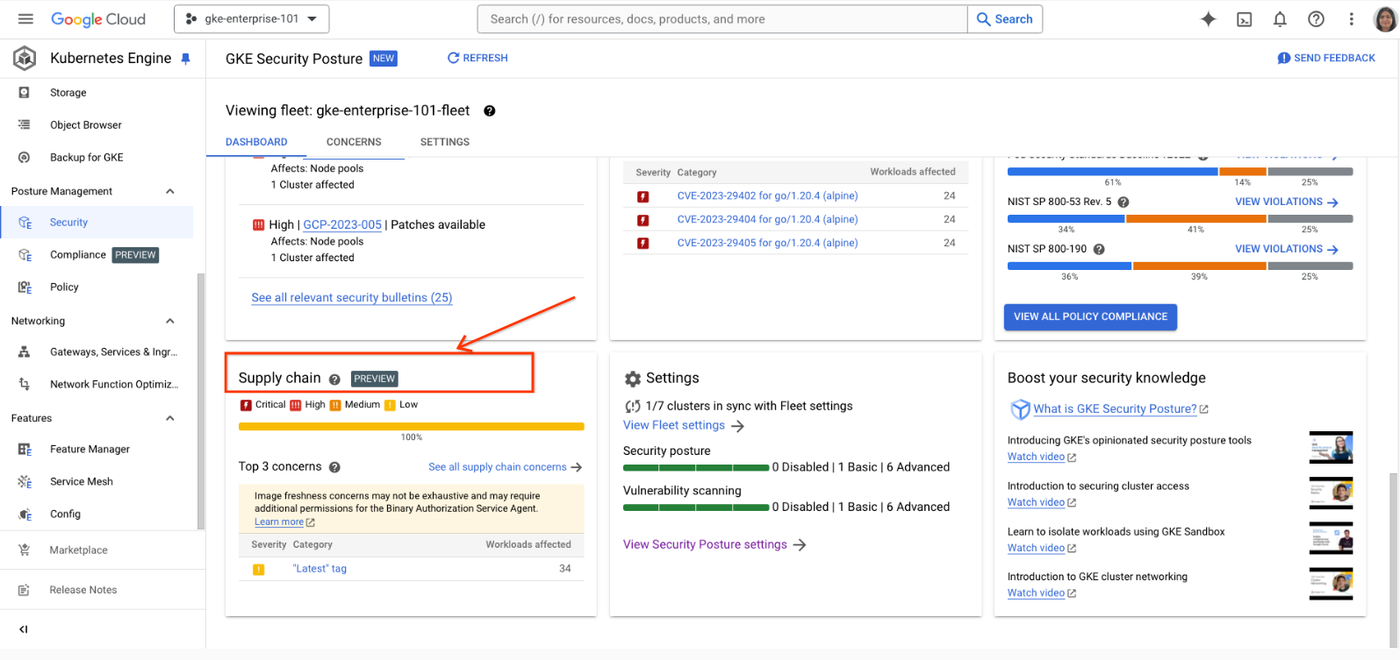
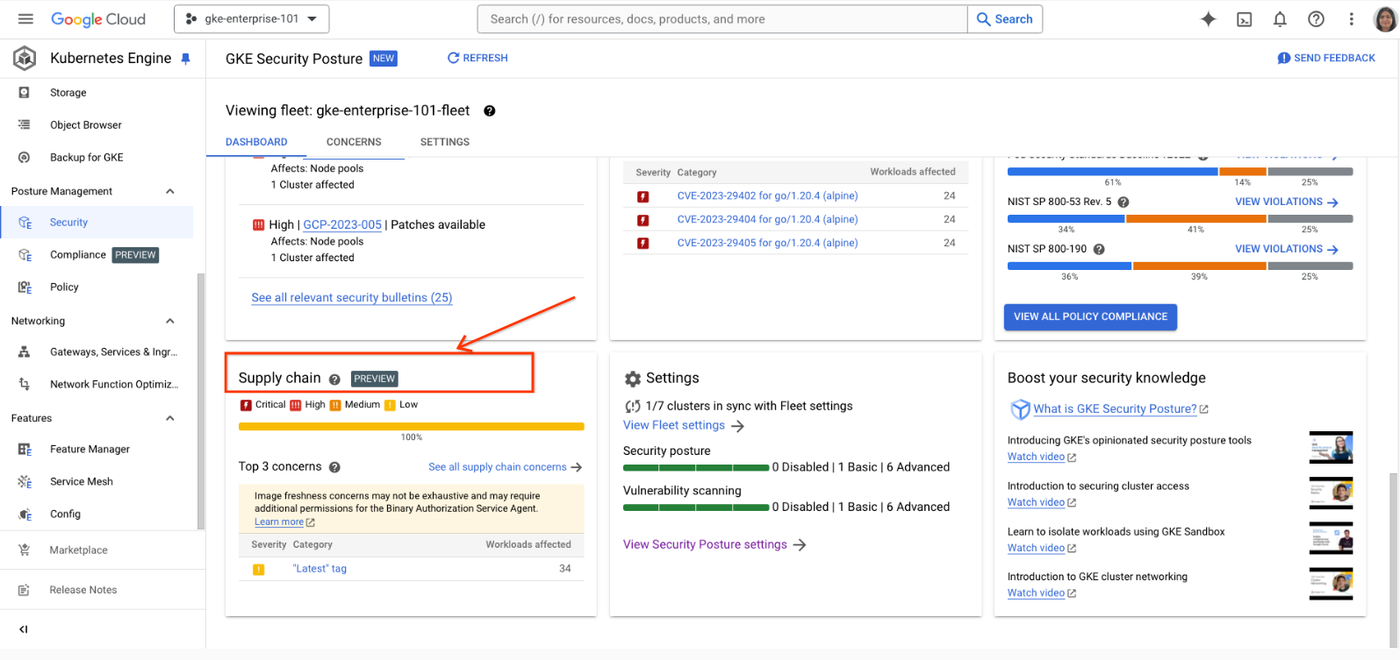
GKE Security dashboard.
4. Concerns related to “image freshness” or “latest tag” will appear in the “Supply Chain” card within 15 mins.
5. Click on a concern to view the details, “Affected Workloads” tab will show a list of workloads affected by the selected concern.
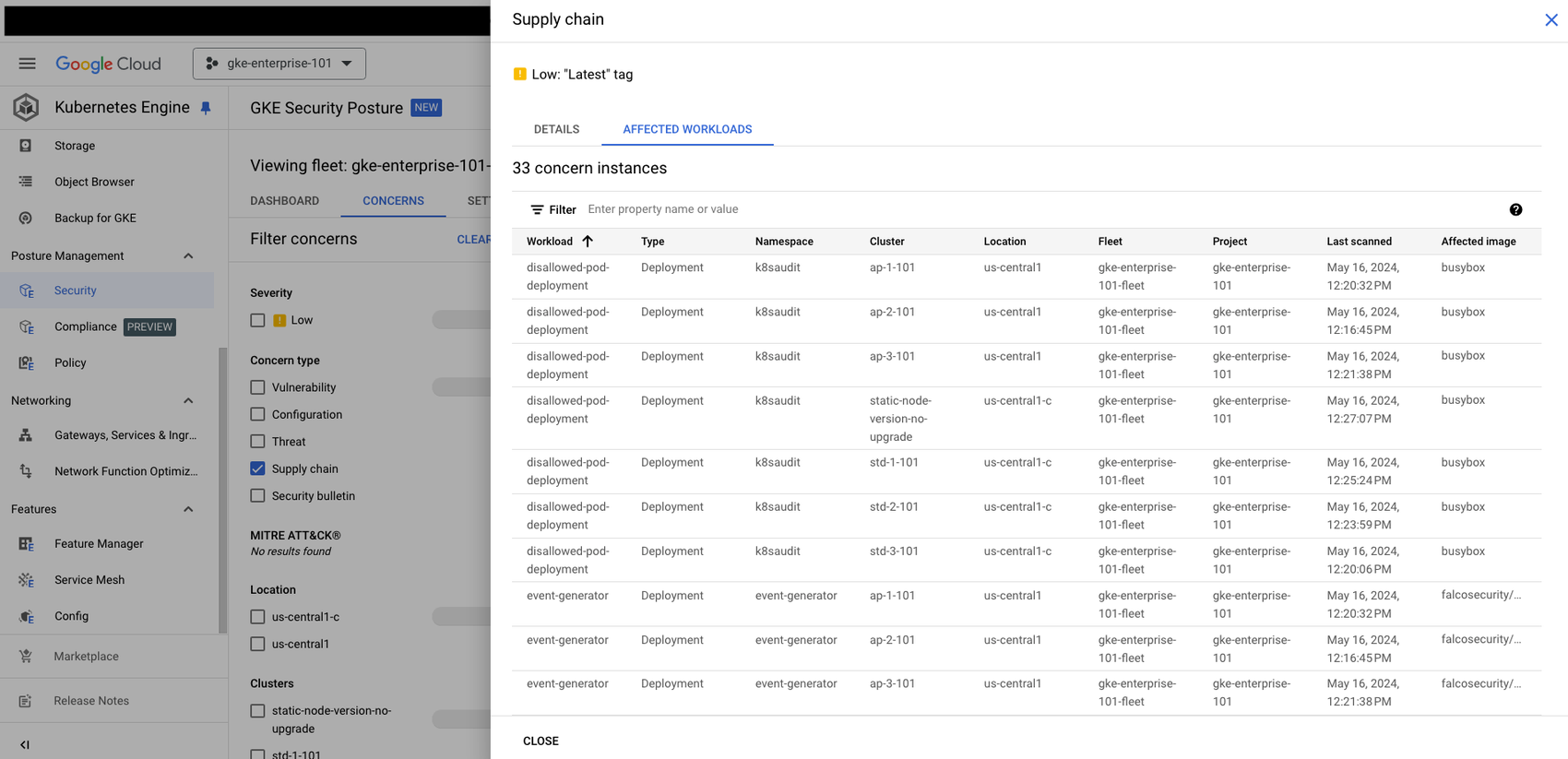
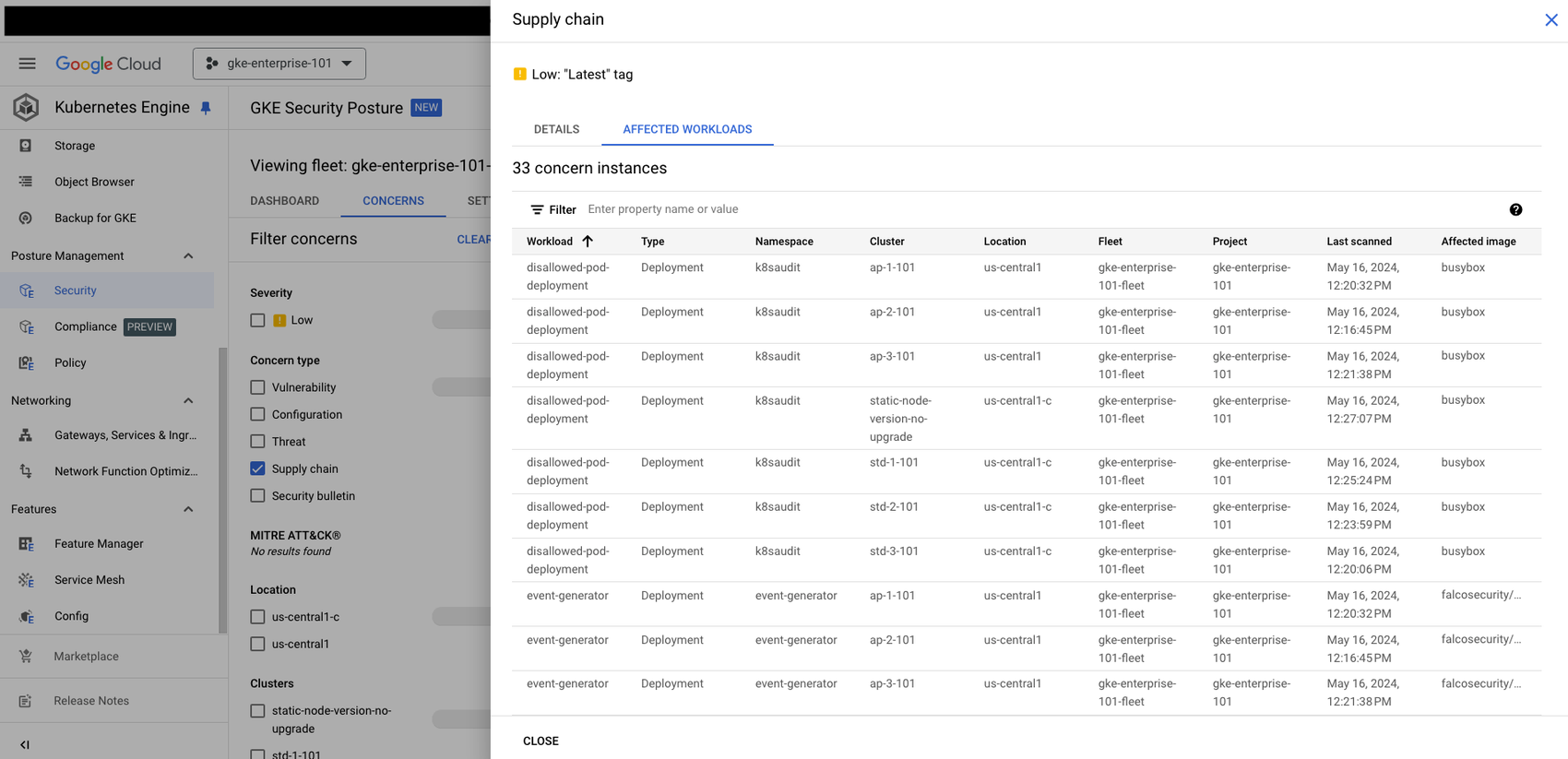
GKE Security dashboard.
Get started today
This initial release to address supply chain concerns in GKE Security Posture is part of our ongoing commitment to enhancing workload security. In the coming months, we plan to introduce more sophisticated supply chain concerns that can be scanned by Binary Authorization and displayed in GKE Security Posture, further bolstering the protection and adding transparency for your application and workloads.
Ready to take advantage of the improved security experience? Learn more about Binary Authorization and GKE Security Posture dashboard.
