A better, safer normal: Helping you modernize security in the cloud or in place
Sunil Potti
VP/GM, Google Cloud Security
During the first few months of the COVID-19 pandemic, many organizations expected a slowdown in their digital transformation efforts. Instead, we saw many enterprises accelerate their use of cloud-based services to help them manage and address emerging priorities in the new normal, which includes a distributed workforce and new digital strategies.
Today, to kick off our Google Cloud Next ‘20: OnAir Security Week, we’re sharing the latest on some unique and powerful capabilities to help you simplify security operations in your organization and make the new normal a better, safer normal.
Advanced security tools to support compliance and data confidentiality
More and more companies, especially those in regulated industries, want to adopt the latest cloud technologies, but they often face barriers due to strict data privacy or compliance requirements. Last month, we introduced two new capabilities that help you securely take advantage of all the cloud has to offer while also simplifying security operations.
Assured Workloads for Government, now in private beta, lets those in regulated industries like the public sector configure and deploy sensitive workloads according to their security and compliance requirements—in just a few clicks. Unlike traditional “government clouds,” Assured Workloads removes the tradeoff between meeting compliance requirements and having the latest capabilities in your cloud.
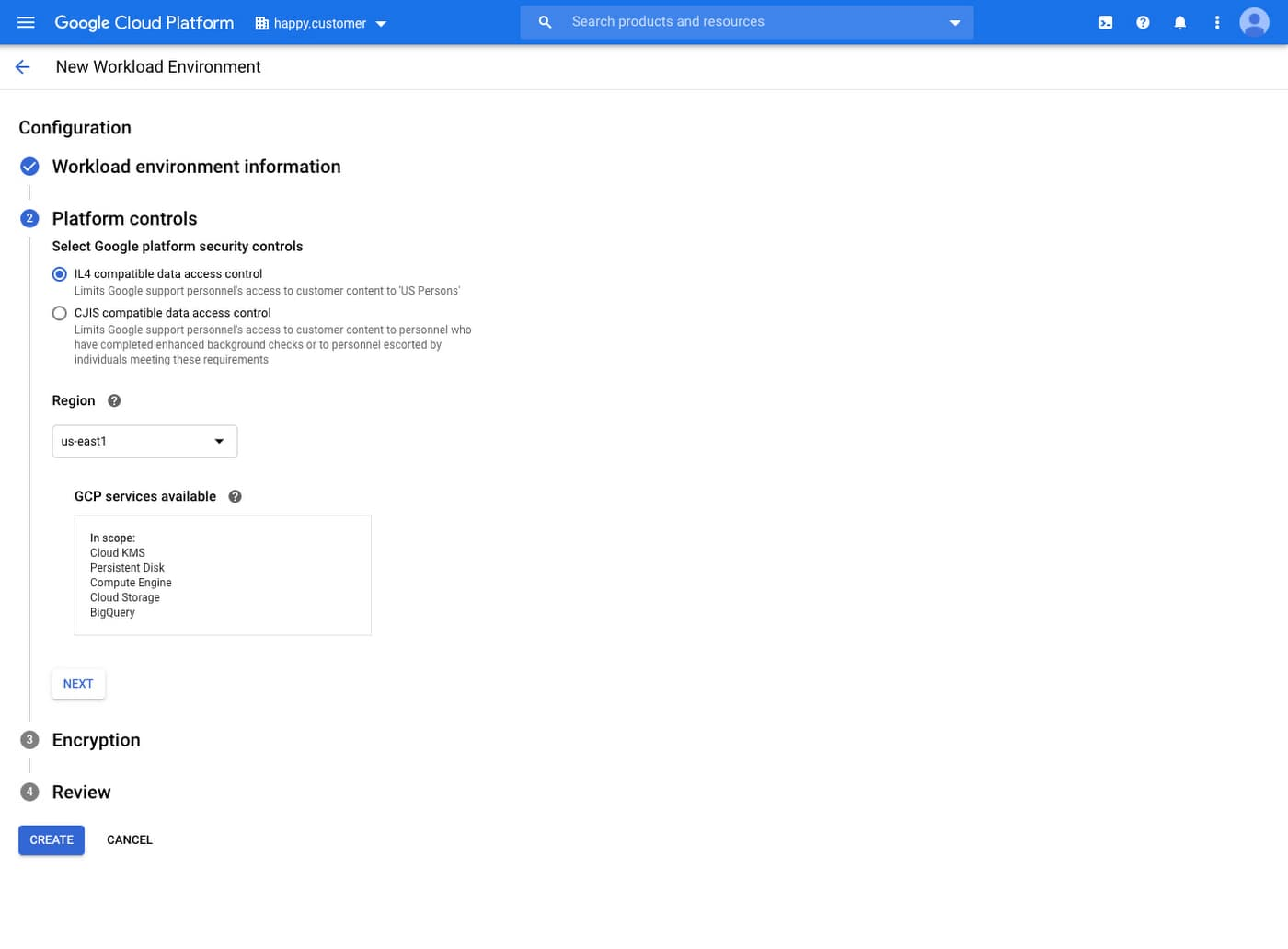
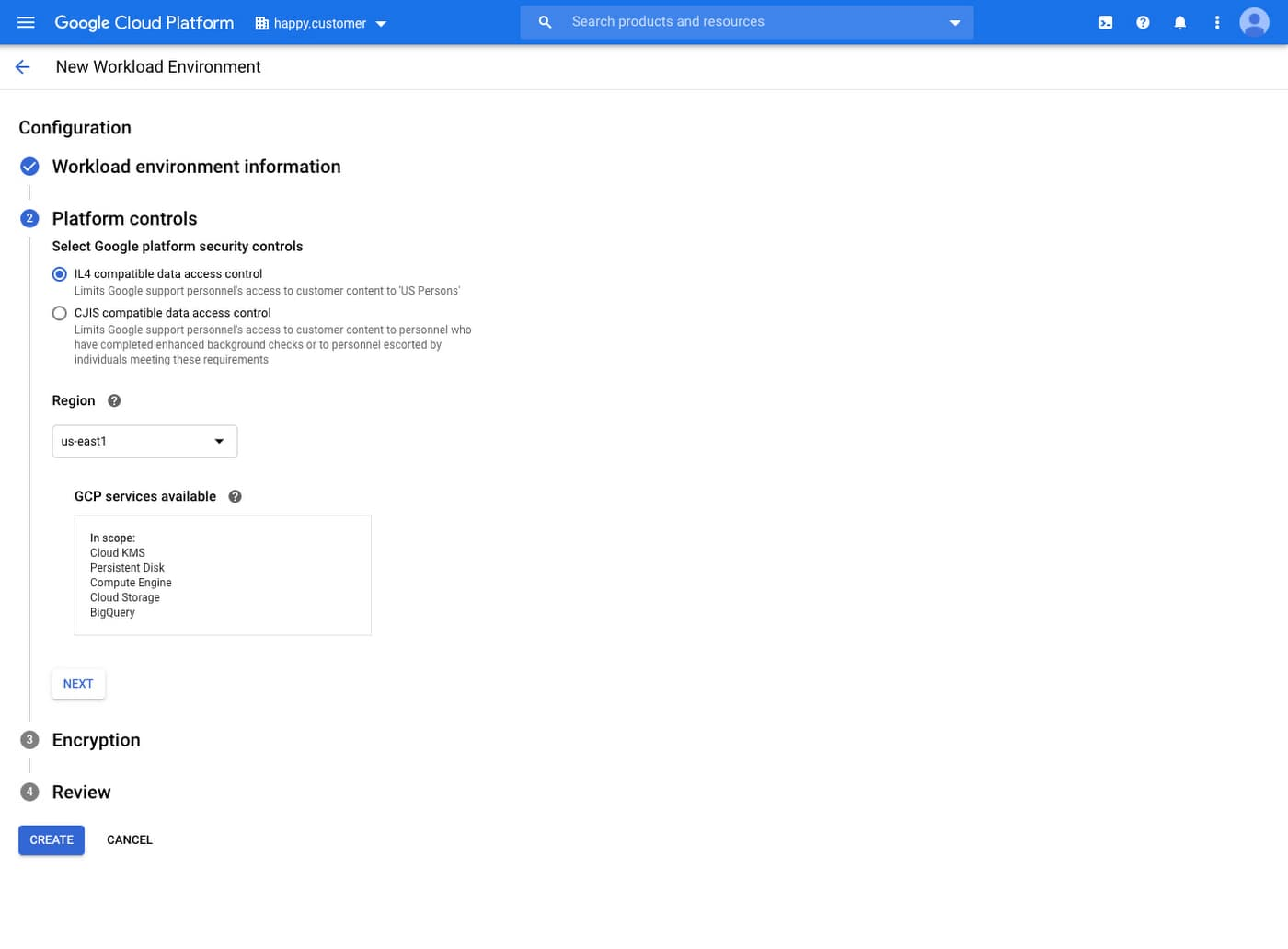
Configuring a new workload in Assured Workloads for Government
Confidential VMs, the first product in our Confidential Computing portfolio, helps you protect your sensitive data in the cloud. We already encrypt data at-rest and in-transit, but customer data must traditionally be decrypted for processing. Confidential Computing is a breakthrough technology which encrypts data in-use—while it’s being processed. Confidential VMs takes this technology to the next level by offering memory encryption so that you can further isolate your workloads in the cloud. With the beta launch of Confidential VMs, we’re the first major cloud provider to offer this level of security and isolation while giving you a simple, easy-to-use option for your newly built and “lift and shift” applications.
Confidential VMs demo
A cloud-based, managed CA for the DevOps and IoT world
Recently, we’ve seen a surge in interest in using Public Key Infrastructure (PKI) in DevOps and IoT device management. But a fundamental problem with PKI remains: it’s hard to set up Certificate Authorities (CA), and even harder to do it reliably at scale. These issues are front and center for these growing use cases.
To help, we’re announcing the beta availability of Google Cloud’s new Certificate Authority Service (CAS)—a highly scalable and available service that simplifies and automates the management and deployment of private CAs while meeting the needs of modern developers and applications. With CAS, you can offload to the cloud time-consuming tasks associated with operating a private CA, like hardware provisioning, infrastructure security, software deployment, high-availability configuration, disaster recovery, backups, and more, allowing you to stand up a private CA in minutes, rather than the months it might normally take to deploy.
A single pane of glass into your security posture
Protecting your users, data, and applications while staying compliant can be challenging. Add in the demands of managing a remote workforce and the complexity increases. With Cloud Security Command Center (SCC), our native posture management platform, you can prevent and detect abuse of your cloud resources, centralize security findings from Google Cloud services and partner products, and detect common misconfigurations, all in one easy-to-use platform.
We recently announced a Premium tier for Security Command Center to provide even more tools to protect your cloud resources. It adds new capabilities that let you:
Spot threats using Google intelligence for events in Google Cloud Platform (GCP) logs and containers
Surface large sets of misconfigurations
Perform automated compliance scanning and reporting
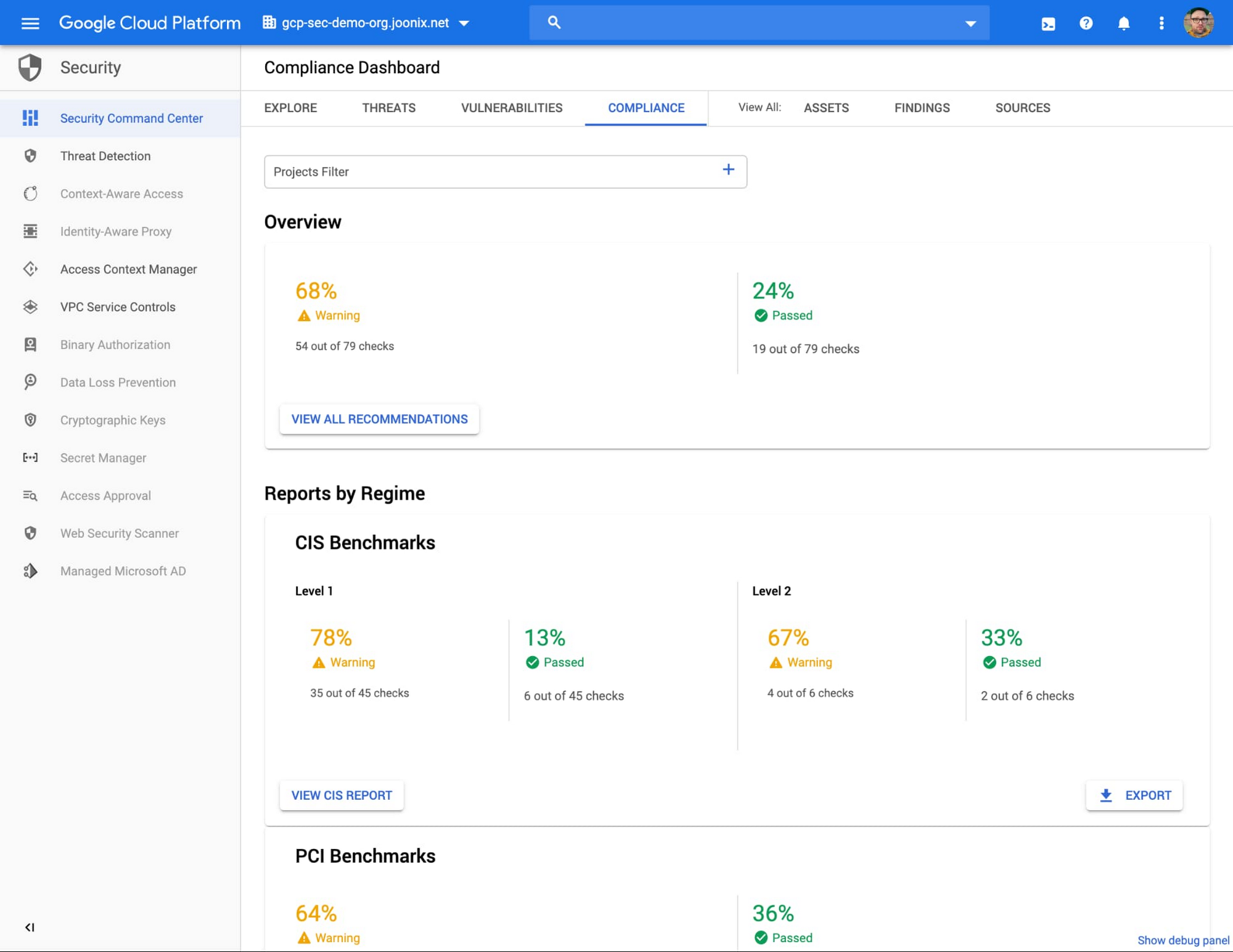
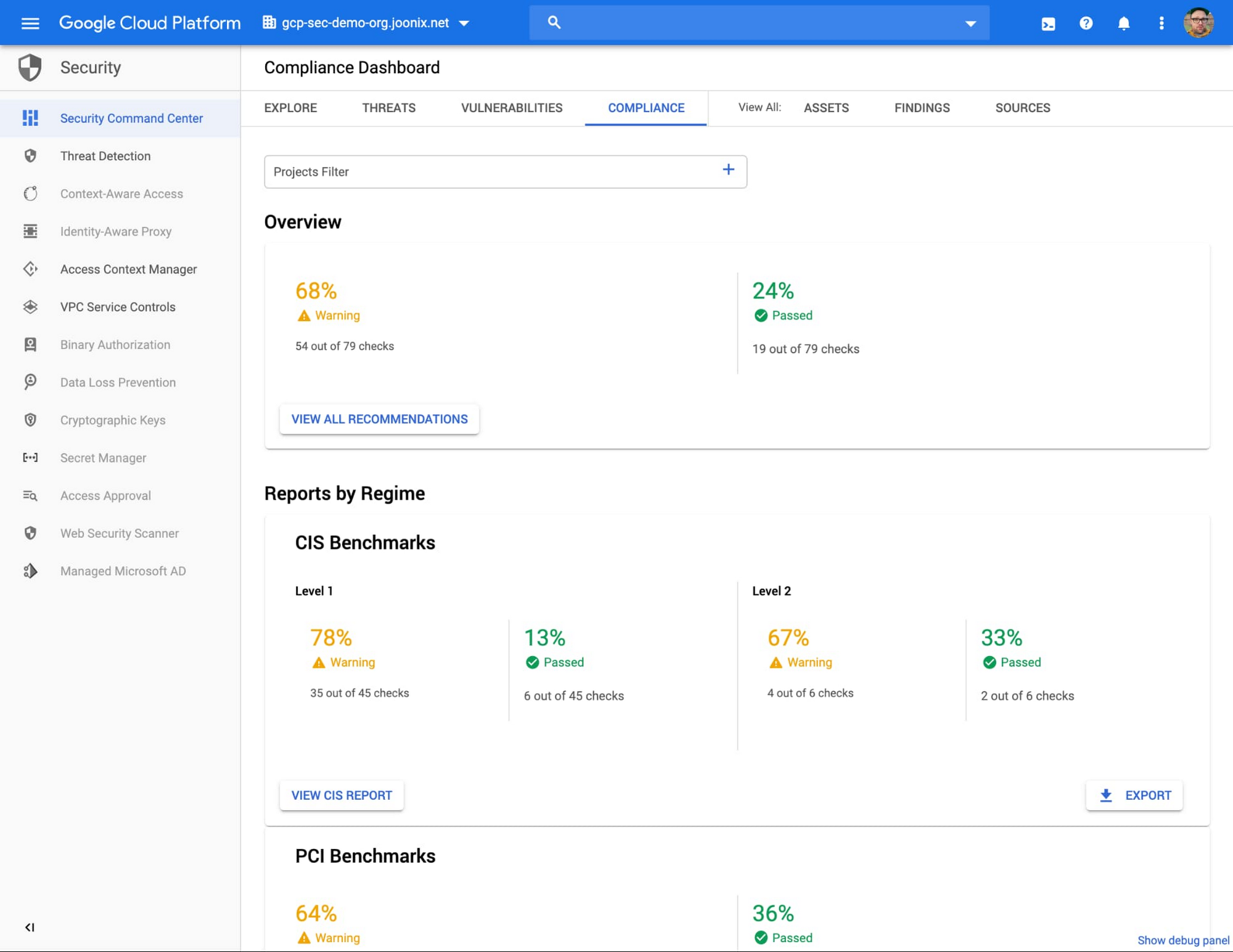
Reporting on CIS Benchmarks in the SCC Compliance Dashboard
These features help you understand your risks on Google Cloud, verify that you’ve configured your resources properly and safely, and document it for anyone who asks.
Collaborating with partners on orchestration and endpoints
As part of our mission to enable operational security and simplicity, we’re committed to working with our security partners to help you on this journey. This week we’re announcing new integrations and go-to-market activities with Palo Alto Networks on their xSOAR Marketplace.
Additionally, we’re announcing an expanded partnership with Tanium, which is integrating and offering Chronicle with their endpoint security and management solution. This integrated solution, sold by Tanium, links endpoint data from Tanium with other telemetry, such as DNS and proxy data in Chronicle, to provide a broader, clearer picture of threats in the enterprise. Chronicle retains Tanium telemetry for a year by default, improving your ability to investigate incidents over long periods of time.
Simplifying protection against DDoS and web attacks
We’re simplifying how you can use Google Cloud Armor to help protect your websites and applications from exploit attempts, as well as Distributed Denial of Service (DDoS) attacks. With Cloud Armor Managed Protection Plus (in Beta), you will get access to DDoS and WAF services, curated rule sets, and other services for a predictable monthly price. You can learn more about our Cloud Armor announcements here.
Automating more secure deployments with blueprints
While these new products provide real benefits, you also need to configure cloud deployments to meet your own unique security and compliance requirements. To help, we’re publishing a comprehensive new Google Cloud security foundations blueprint that provides curated, opinionated guidance and accompanying automation to help build a secure starting point for Google Cloud deployments. It’s launching as the cornerstone of our Google Cloud security best practices resource center, a new web destination that delivers world-class security expertise from Google and our partners in the form of security blueprints, guides, whitepapers, and more.
A better, safer normal together
Defending your enterprise requires continuous evolution, and the events so far in 2020 have made that even more clear. With compliance automation, simpler security operations, and better protection for employees and customers we’re committed to helping you adjust and evolve to make today’s new normal a safer normal.
Be sure to check out our security sessions throughout this week where we’ll be digging into the new capabilities we’re introducing, and some we’ve already launched in 2020. You can also find more information at our privacy and security home page.

