Google Cloud Armor: Introducing 3 key features to protect your websites and applications
Emil Kiner
Senior Product Manager
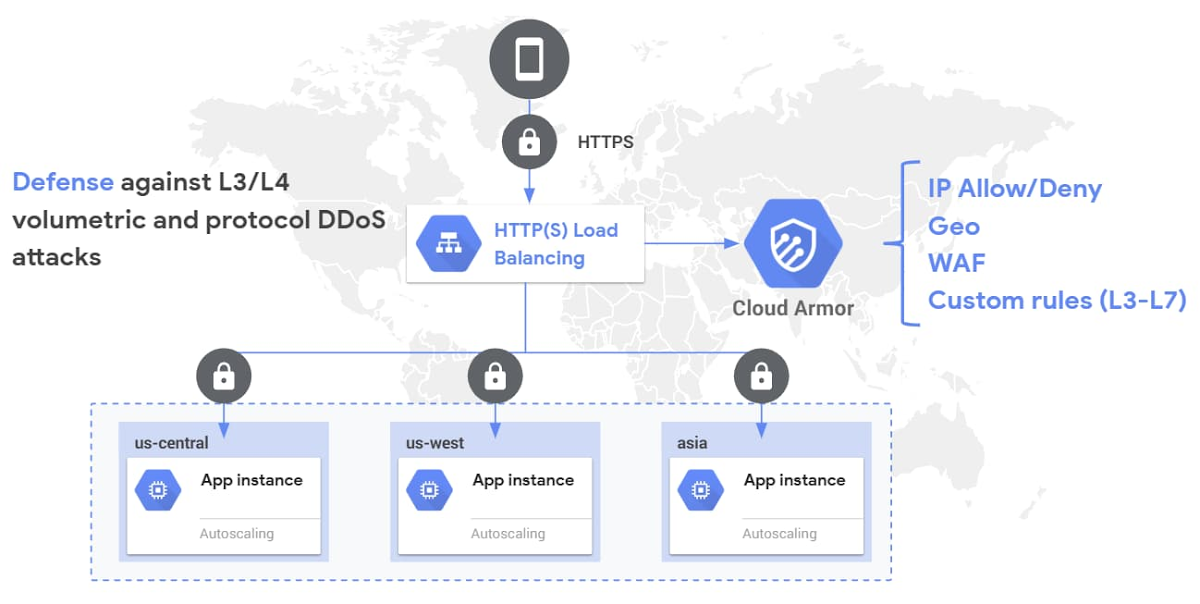
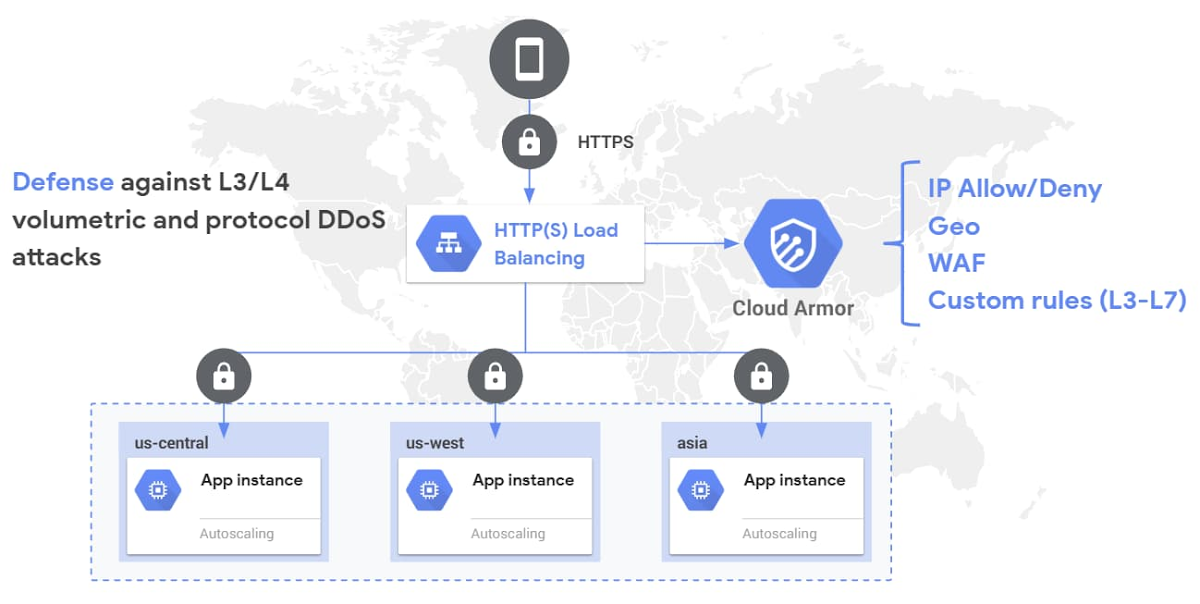
With the seemingly never-ending list of threats, keeping your websites and applications secure is a constant challenge. At Google, we strive to help you operate your mission critical workloads securely and efficiently, while reducing toil along the way. Over the first half of this year we’ve made several critical features and capabilities generally available for Google Cloud Armor, including WAF rules, geo-based access controls, a custom rules language, support for CDN Origins servers, and support for hybrid deployment scenarios.
At Google Cloud Next ’20: OnAir we’re simplifying the way you can use Cloud Armor to help protect your websites and applications from exploit attempts as well as distributed denial-of-service (DDoS) attacks.
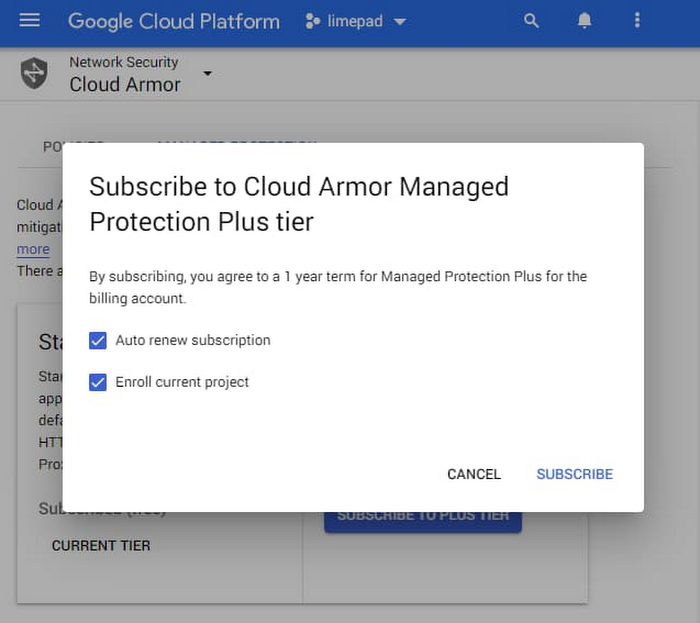
We’re announcing the beta release of Cloud Armor Managed Protection Plus, a bundle of products and services that helps protect your internet-facing applications for a predictable monthly subscription fee.
We’re making Google-curated Named IP Lists available as a beta.
We’re continuing to expand our set of pre-configured WAF rules by launching beta rules for Remote File Inclusion (RFI), Local File Inclusion (LFI), and Remote Code Execution (RCE).
Introducing Cloud Armor Managed Protection Plus
Cloud Armor Managed Protection Plus leverages the edge of Google’s network, as well as a set of products and services from across Google Cloud, to help protect your applications from DDoS attacks and targeted exploit attempts. With Managed Protection, you can now benefit from the same scale and expertise Google employs to protect your applications and mission critical services from malicious activity on the internet.
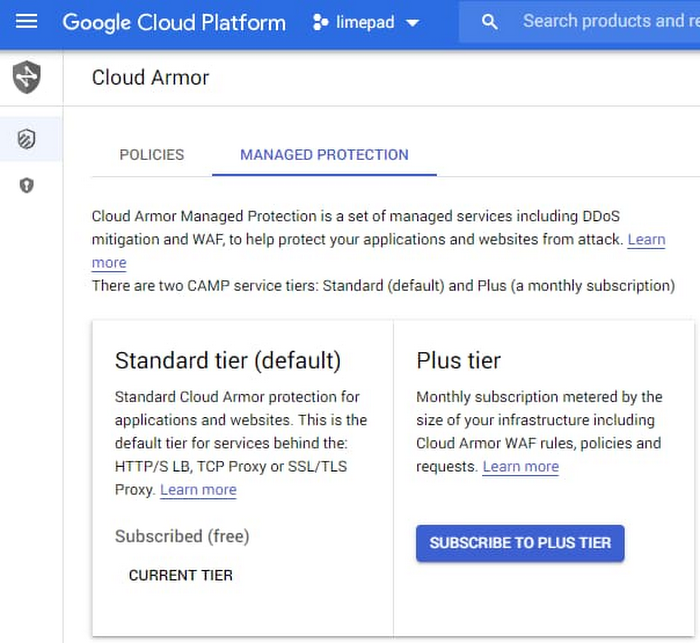
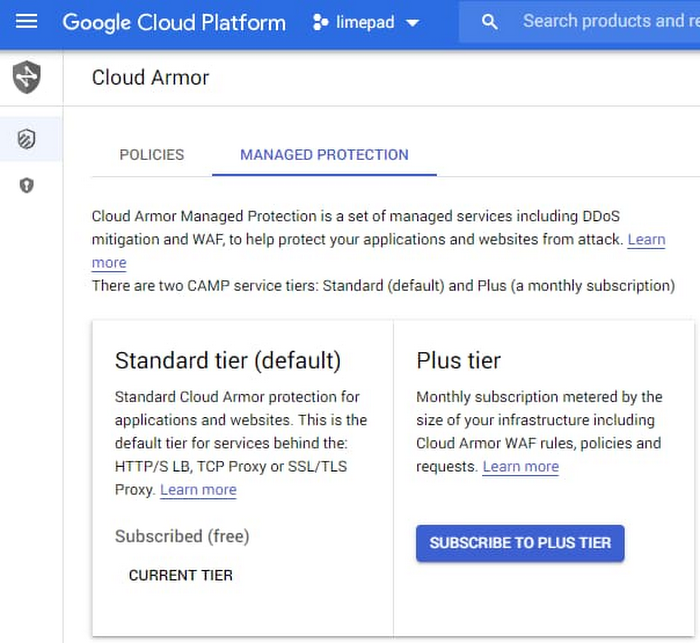
Managed Protection is available in two service tiers: Standard and Plus. All existing Cloud Armor users, as well as workloads behind any of our global load balancers, are automatically enrolled in Managed Protection Standard. At this level, you get Google-scale volumetric and protocol-based DDoS protection for any of your globally load balanced applications and services, as well as access to Cloud Armor WAF and layer 7 (L7) filtering capabilities, including the pre-configured WAF rules subject to usage based pricing based on rules, policies, and requests.
Cloud Armor Managed Protection Plus, which is now in beta, is a subscription service with a predictable, enterprise-friendly monthly pricing model that mitigates cost risk from defending against a large L7 DDoS attack. Managed Protection Plus streamlines and bundles in DDoS protection, Cloud Armor WAF, and other future value added services. Customers that subscribe to Managed Protection Plus will get access to DDoS and WAF services, and curated rule sets for a predictable monthly price based on the size of a deployment. Since Cloud Armor WAF usage is included in Managed Protection Plus, subscribers no longer need to worry about the number of queries processed or the size of an L7 attack. Managed Protection Plus subscribers will also have access to a growing list of advanced capabilities, including Named IP Lists and future Google-curated rule sets and services. Sign up your projects for access to the beta.
Introducing Named IP Lists
Named IP Lists, now in beta, are Google-curated rule sets containing a pre-configured list of IP addresses that can be referenced and reused across policies and projects. We’re starting with providing Named IP Lists that have source IP ranges for common upstream service providers that many of our users would want to allow through their Cloud Armor security policies.
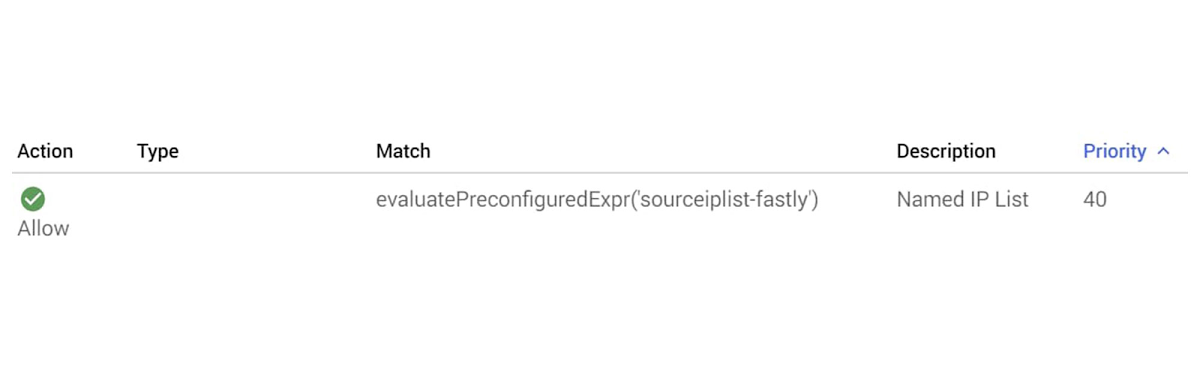
Customers often have to configure Cloud Armor security policies with a large set of IP ranges to allow traffic from an upstream provider. With Named IP Lists, customers no longer have to self-manage the list of their upstream providers’ IP addresses and instead can rely on Google to curate and keep up to date the list of IPs. We’re now working with a growing list of service providers to ensure that customers can seamlessly permit traffic from third-party services through a Cloud Armor security policy without having to keep track of the service providers’ changing lists of source IPs.
You can now refer to these Named IP Lists while crafting custom rules. The underlying list of IPs is kept up to date by regular syncs with the third-party service providers’ APIs.
New WAF rules: RFI, LFI, RCE
As part of our effort to expand the scope of the pre-configured WAF rules to all Cloud Armor customers, we are making RFI, LFI, and RCE rules available as a beta. Collectively, these rules contain industry standard signatures from the ModSecurity core Rule Set to help mitigate the Command Injection class vulnerabilities while enhancing the out-of-the-box coverage for OWASP Top 10 vulnerabilities as well.
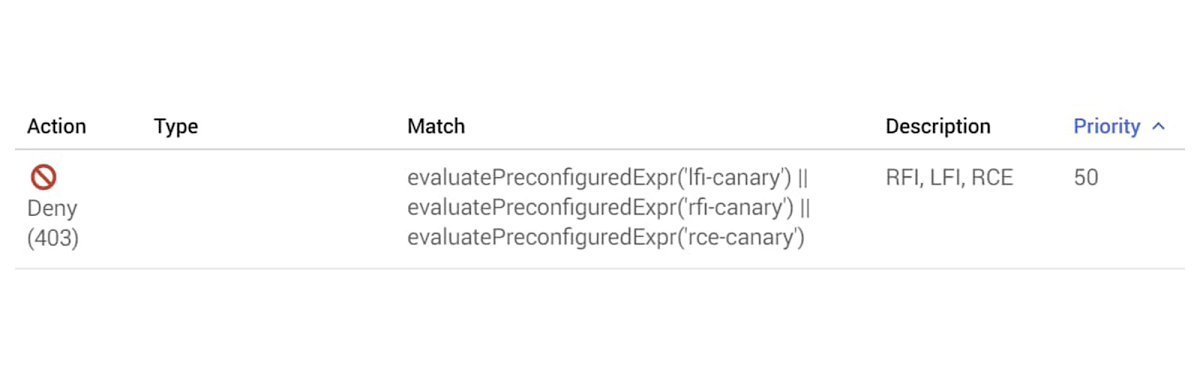
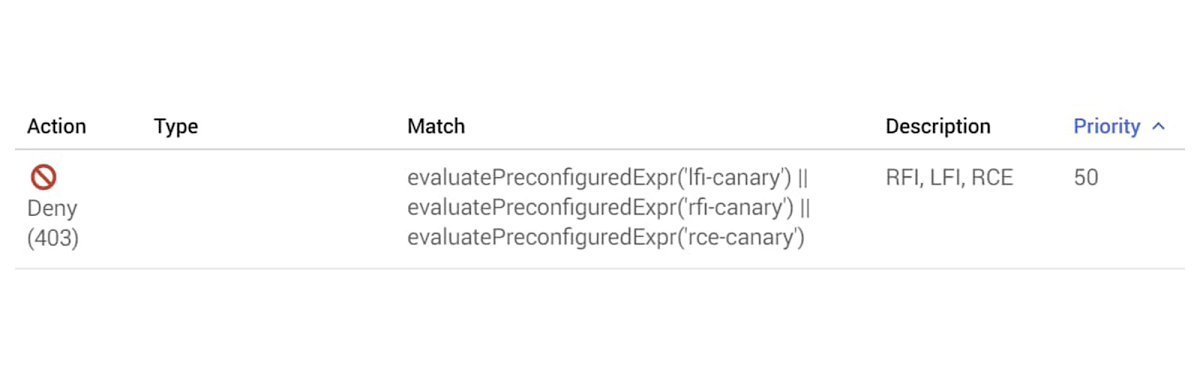
Like the other pre-configured WAF rules, the new rules contain dozens of sub-signatures and are tunable on a per-application basis by end users. As usual, a rich set of telemetry including per-request logging, near real-time request volume metrics, and correlated security findings are sent to Cloud Logging, Cloud Monitoring, and Cloud Security Command Center respectively.
Conclusion
Google Cloud Armor is helping protect a rapidly growing set of customers’ mission critical workloads while helping support their compliance requirements, like PCI DSS, for their Google Cloud deployments. With the capabilities and services we announced this week, you can simplify your deployments and reduce operational overhead when integrating with upstream partners and service providers.
More resources:

