A year in the cybersecurity trenches with Mandiant Managed Defense
Ng Choon Kiat
Senior Manager of Mandiant SOC
Yash Gupta
Senior Manager of Mandiant SOC
From the front lines of cyber investigations, the Mandiant Managed Defense team observes how cybercriminals find ways to avoid defenses, exploit weaknesses, and stay under the radar. We work around the clock to develop new techniques to identify attacks and stop breaches for our clients.
Our aim is to help organizations better protect themselves against the security challenges of today, as well as the future. To minimize the impact of an incident, organizations must prioritize a robust detection posture and a well-structured response plan. This blog highlights our key observations from the many engagements we were involved with in 2023.
Infostealers: 2023’s most prevalent malware
Infostealer, information stealing malware, was the most prevalent type of malware observed by Managed Defense in 2023. The trend coincides with the observed demand and supply of stolen data within underground forums and markets. Infostealers are lucrative for cybercriminals, as stolen data can be used for extortion or to facilitate advancing multiple stages of an intrusion.
For example, infostealers can obtain credentials for initial access or lateral movement, and they also gather information about an environment. This reconnaissance data can be used to tailor future attacks, significantly escalating a breach's severity and impact.
Infostealers are often distributed through cracked or pirated software as a lure. Cybercriminals used social engineering and search engine optimization (SEO) tactics to more effectively distribute their malware. In July, Managed Defense uncovered a campaign that used fake Zotero and Notion installers (free, open-source reference management tools) to gain unauthorized access to targeted machines. These thematically-relevant lures demonstrate how easily cybercriminals can tailor their attacks to specific industries and organizations.
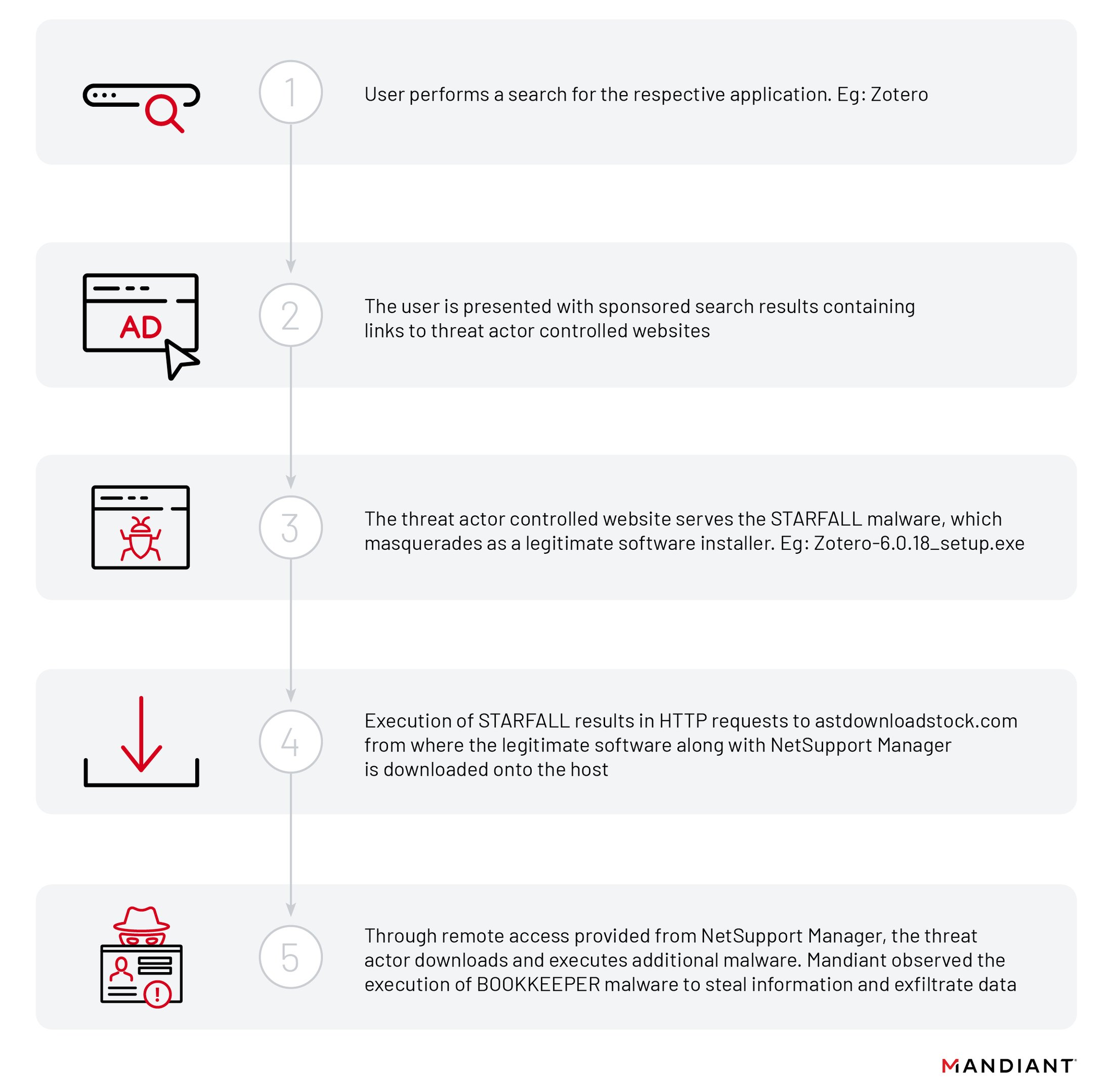
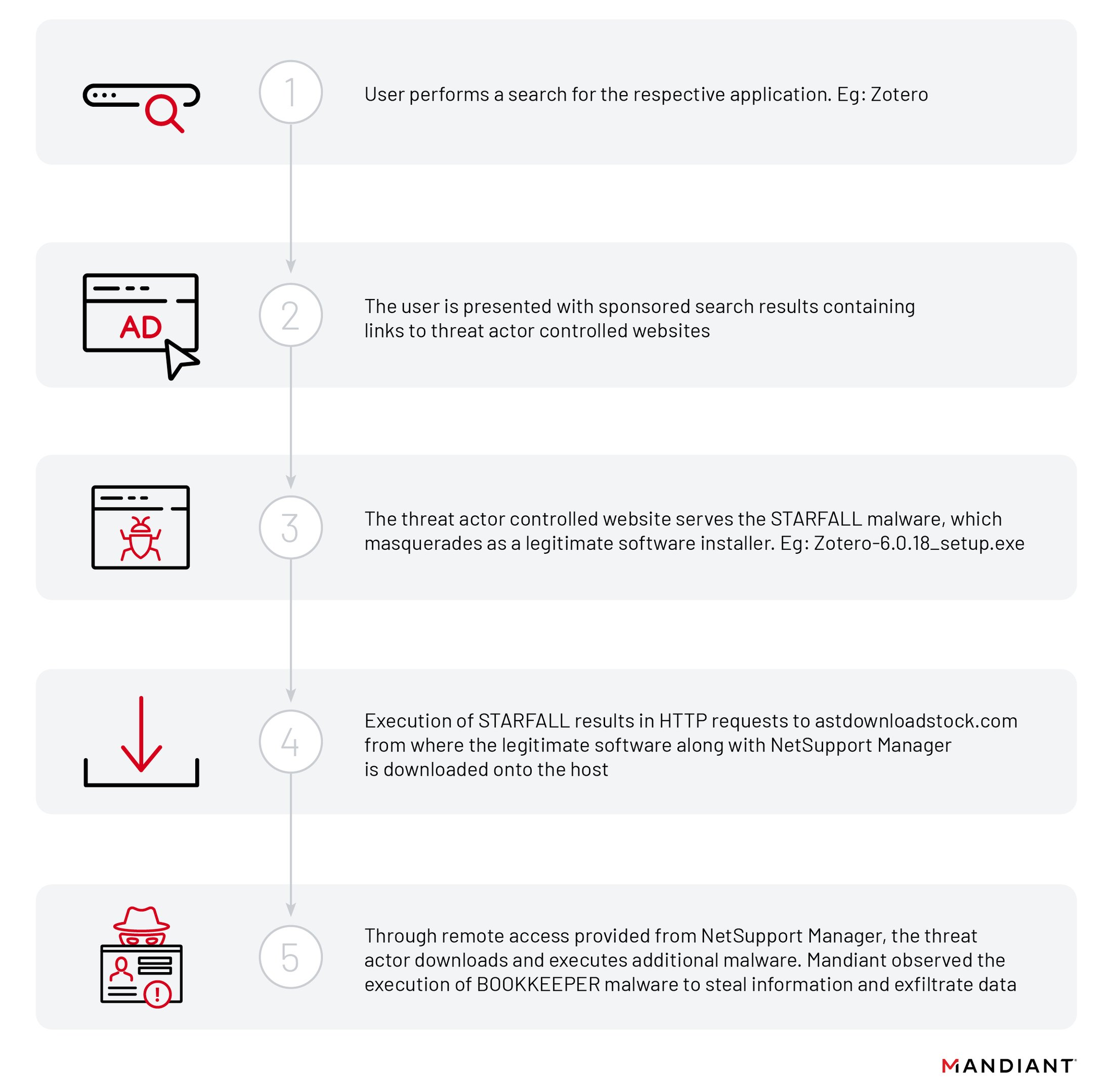
Figure 1: UNC4864 Infection Lifecycle: Leveraging Fake Installers - You can find this research piece from Managed Defense.
An effective way for organizations to reduce the risks of infostealers is to implement application allowlisting that restricts employees to installing only authorized software from approved sources.
Removable storage devices, a useful vector for threat actors
Threat actors linked to the People’s Republic of China (PRC-nexus) are relying on removable storage devices extensively to achieve their initial intrusion of targeted systems. Managed Defense has responded to numerous intrusions stemming from this initial access method. Investigations into these incidents revealed a wide range of distinct malware families being used.
PRC-nexus cyber espionage actor TEMP.HEX used removable drives to spread SOGU, also known as PlugX to steal sensitive information. You can read more about how this specific threat group targeted the public and private sectors globally, and what mitigation strategies we recommend to defend against them.
Russian groups also included removable drive propagation in their malware. QUICKGAME is the latest in an arsenal of USB-driven malware that TEMP.Armageddon has relied upon to gain and further its access in victim environments.
The proven effectiveness of removable drives as malware distribution tools for strategic espionage outweighs the potential inconvenience for users. Managed Defense recommends that organizations restrict removable storage device access for workstations where such access is not essential.
Cybercriminals leveraging new vulnerabilities
Zero-day exploits are a major security risk due to their ability to facilitate undetected attacks. These zero-day vulnerabilities were usually uncovered through either threat hunting or incident response activities.
As risky as zero-day attacks are, the real surge in threat activity occurs when vulnerabilities are publicly disclosed and exploit proof-of-concepts are made available. These “open doors” provide low-effort, high-reward opportunities for threat actors engaged in both financial crime and cyber espionage. This highlights the critical importance of rapid patching to mitigate the impact of known vulnerabilities.
This table lists some of the exploits responded to by Managed Defense in 2023, highlighting the continuous trend of cybercriminals and espionage actors leveraging vulnerabilities for initial access.
There's no "golden window" to patch, so prioritizing software updates immediately is crucial to stay ahead of attackers.
Wiper defense: Have a robust data protection strategy
New ransomware malware families continue to emerge with the ultimate goal of financial gain. Businesses and services are disrupted until a payment is made.
Though ransomware remains a common threat to organizations, recent developments in wiper malware exhibit a disturbing trend of sophistication and widespread use.
In 2023, Managed Defense tracked the continuous deployment of new wiper malware families, particularly during wartime or conflict. Wiper malware became a weapon of choice for crippling critical infrastructure from power grids to communication networks. The malware sophistication demonstrates that threat actors are investing significant time and effort into developing them.
We also saw a pattern shift in how it was used. Initially deployed as a targeted destructive tool, wiper malware has evolved into a weapon wielded by vigilante groups motivated by disagreement or conflict.
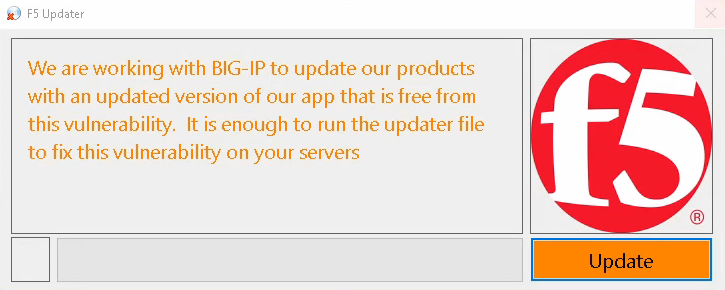
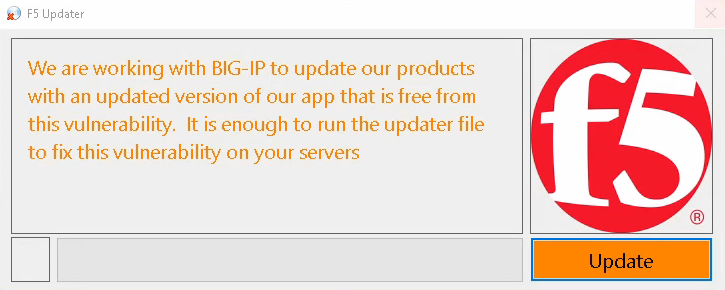
Figure 2: A wiper malware masquerading as a fake update seen in December 2023 underscores the steady emergence of wiper malware in the evolving threat landscape targeting businesses and governments.
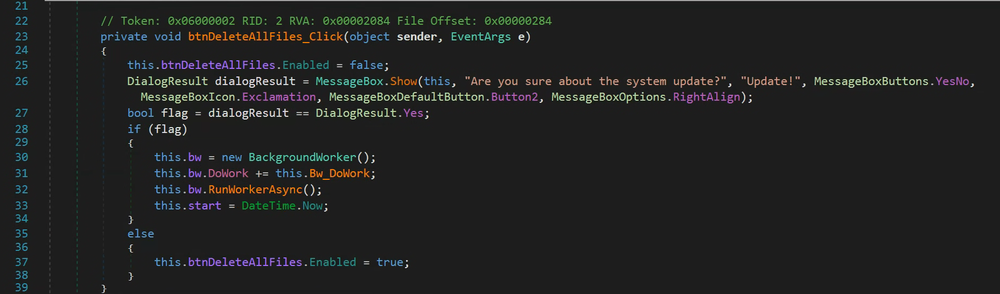
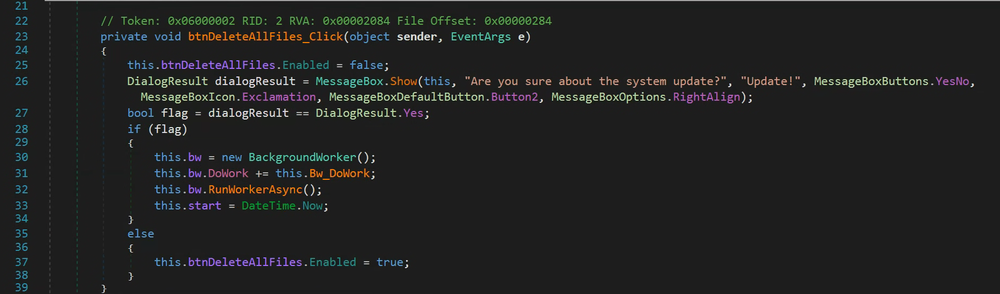
Figure 3: Analysis of the code reveals the “wiper”, file deletion, functionality.
The increasing use of Wiper malware alongside today's ransomware threat, organizations are at greater risk of losing their data. We recommend organizations implement a robust data protection strategy.
Generative AI and the adversary
The prevalence of malware distribution through social media, scam calls, and email phishing schemes continues unabated. These methods are designed to lure users into downloading malware or unknowingly surrendering their credentials on phishing pages, and they remain a persistent and concerning reality that can result in monetary loss for both businesses and individuals.
Threat actors like UNC3944 (also known as Scattered Spider) have mastered these tactics, using phone-based social engineering and smishing to infiltrate victim organizations, exfiltrate sensitive data, and extort victims with ransomware. We have published a guide to how to mitigate threats from this specific threat group.
Other threat groups also use social engineering to further their goals, including:
- FIN6 and UNC4962 have employed lures such as resume-themed files and fake job postings on fabricated personal websites to lead users into downloading malicious software.
- The BazarCall campaign initiated by UNC3753 stands out because it used phone calls to fake businesses as part of its phishing scheme, ultimately tricking victims into downloading remote access tools that grant the attackers an initial foothold.
- UNC4214 has been using social media and messaging platforms, and malicious social media advertisements, to distribute credential-stealing malware. Their ultimate goal is to infiltrate organizations, gain control of social media business accounts, and then use those accounts for financial gain.
As threat actors regularly evolve their tactics to use new and emerging technologies, we anticipate that cybercriminals will integrate AI more deeply into their toolkits. Realistic, AI-generated content can enhance the persuasiveness of these social media lures, making them more difficult to identify and avoid. However, while there is threat actor interest in this technology, adoption has been limited so far.
Organizations should explore the implementation of security frameworks like the Principle of Least Privilege (PoLP) and Zero Trust security. PoLP centers on granting user access to only what is strictly necessary, while Zero Trust adds a focus on continuous verification and access control. Organizations also may benefit from investing in a strong detection and response program, underpinned by modern Security Operations tools such as Chronicle. An organization's ability to demonstrate resilience through rapid and effective incident response will foster community confidence and build trust in its products and services.
Looking ahead and next steps
The Managed Defense team is committed to continuous innovation that empowers our customers. This commitment drives our ongoing development of robust, helpful solutions, such as the recently-launched Mandiant Hunt for Chronicle, which can provide direct proactive threat hunting directly on Chronicle data. Our commitment also motivates our partnerships with industry leaders including Microsoft Defender for Endpoint, CrowdStrike, and SentinelOne, so we can offer flexibility and choice within your security stack.
We are excited about the future, reimagining security operations to find new ways to relentlessly protect our customers from impactful cyberattacks.

