iFrame sandbox permissions tutorial
Jim Rottinger
Software Engineer at Looker
Understanding iFrame sandboxes and iFrame security
Embedding third-party JavaScript in web applications is a tale as old as time. Whether it’s dropping a widget onto your web page or including custom content from a client in your cloud application, it’s something that many developers have encountered in their career. We all know about the iframe element in HTML, but how much do we really know about how it works? What are the security concerns associated with running code inside of an iframe and, furthermore, how can the HTML5 sandbox attribute on the frame alleviate these concerns?
The goal of this tutorial is to walk through the various security risks associated with running third-party JavaScript on your page and explain how sandboxed iframes can alleviate those issues by restricting the permissions it is allowed to run with.
In this post, we’ll demonstrate setting up a demo application from the ground up that will simulate running JavaScript coming from a different origin. What we should end up with is a sandboxed environment in which we can execute any arbitrary JavaScript and still sleep well at night, knowing our host application will be safe from harm.
With all of that in mind, the guided walkthrough will consist of the following parts:
- Setting up two node servers to simulate two different origins
- Embedding the content of our client page in an iframe on the host page and investigating what the client iframe is and is not allowed to do
- Applying the sandbox attribute to the iframe and exploring the various options for the sandbox.
Let’s get started!
Step 1: Setting up the servers for our demo application
To simulate executing code from a different origin, we are going to set up two node servers — one which we’ll call the host and second which we will call the client. We can do this using node’s http library to listen to and serve from two different ports.
Save this JS file to whatever name you’d like - I called it server.js. Then, to start our server, we can simply run:
This should start two different http servers, one on port 8000 and the second on port 8001. To test that it is working, you can individually visit your localhost on port 8000 and 80001, which should look like this:
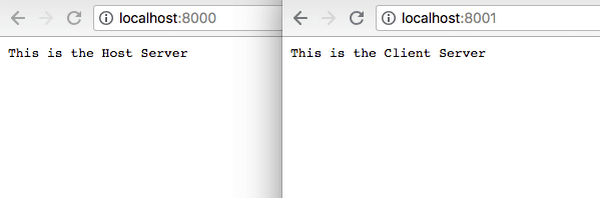
Even though they are both running on localhost, the same-origin policy that browsers implement operate on a protocol-host-port tuple that will only be true if the protocol, the hostname, and port number all match up. In this case, the protocol and host are the same, but since the ports are different, these will be considered to be different origins.
Of course, just having a hard-coded response won’t get us very far. We’ll need to be able to serve both HTML and JS for this demo. To do this, I whipped up a function to serve assets from a given folder.
This function will take in a root folder path, a url, and the response object. If the file is not found, it will return 404. If it is found, it will set the header to be text/javascript or text/html, depending on the file suffix. To get this to work, we need to include two more dependencies at the top of the file:
Fun fact - Since we’re just using built-in node libraries, we do not have to install anything via npm! Once you instantiate fileSystem, path, and our asset function, go ahead and update your servers as well to call serveAsset.
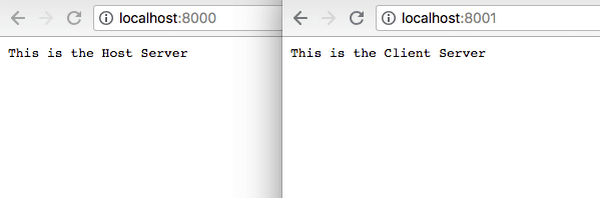
These now look very similar. The only difference is that the host_server will look for its assets in the host folder and the client_server will look in the client folder. If we were to restart our server now, we would see the following error message:
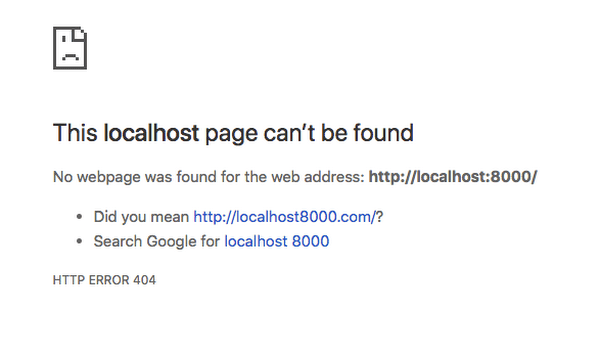
This is because our serveAsset function is looking in either the host or client folder for an asset to serve, and we haven’t created them yet! Let’s create both of them, each with an index.html and a JS file.
Our file structure should look like this:
Now, if we start our server and visit our localhost location, we no longer get the 404, which means our server found the file! — but it has no content yet. To get some content in, let’s start with something very simple. For the host, we simply have the HTML as:
And the JavaScript as:
The client content is exactly the same, just with the word host changed to client. If we restart our server now, we should be able to go to both http://localhost:8000/ and http://localhost:8001/ and see our content in action! Each page should send an alert from the JS file and then render our html content to the page.
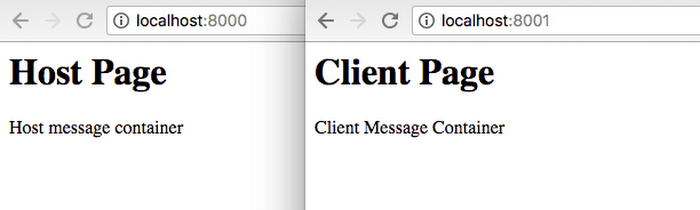
Each node server is serving an index.html file which includes a JavaScript file
Step 2: Embedding the client in the host without sandboxing and investigating its permissions
With our two servers running, we are now ready to begin testing some iframe scenarios. Before we do that, let’s add a second file to our host so that we can compare the permissions of an iframe from the same origin and an iframe from a different origin.
Fill in the content of these files with the same content as we used for our other html/JS pairs. We’ll call this one the “Hosted Client,” meaning an iframe client coming from the same origin as our host.
Once we do that, back in our host/index.html we can iframe both our same-origin client and our different-origin client.
Please note that we use localhost for the hosted-client and 127.0.0.1 for the other. This will become important in the cookies section below. Refreshing the host page, you should now see two iframes, each with the content of our individual HTML files.
If you have alerts in your JS files like I do, you should have seen that each individual file triggers an alert at the top level of the browser. Should it be able to do this? That question brings us to our first area of concern — pop-ups and dialog boxes.
Pop-ups and dialog boxes
JavaScript has three different functions that trigger a popup — alert, prompt, and confirm. Each of these open up a dialog box at the top of the browsing context, regardless of whether it comes from the top-level window or not. The scary thing about these dialogs, as can be found in the alert documentation, is:
“Dialog boxes are modal windows — they prevent the user from accessing the rest of the program’s interface until the dialog box is closed. For this reason, you should not overuse any function that creates a dialog box (or modal window).”
I am sure that most of us have, at some point in our lives, been forcefully redirected to a spammy site against your will that then bombarded you with these types of dialogs. Even when you try to close out of it, it just pops open another one. This annoying behavior completely blocks you out of using a site and sadly, it’s incredibly simple to reproduce. Try adding this to your client.js file:
Now, when you visit your host site, you get this:
These prompts make it impossible to ever interact with the page and you have to close the entire tab or kill the JavaScript execution to get rid of it. The worst part is that regardless of whether your embedded content is coming from a different host or the same origin, this behavior is exploitable.
You might think that you could just do something like this to get rid of it:
The problem with this is that each iframe operates within its own nested browsing context, so overriding the functions at the host level will not affect the functions at the frame level.
Fortunately, sandboxing can come to our rescue here, which we will see later in this post. For now, let’s move on to whether or not the iframe can navigate the page away from the current one.
Step 3: Top-level window navigation and opening new tabs
Let's now examine how and if the iframes are able to change the url of the top-level window and if they’re able to open a new window.
There are two different methods that we want to test here.
- window.open for opening new windows and tabs, and
- window.location for navigating the page away from the current url.
Helpful note: iframes can reference its top-level window using window.top. Similarly, it can reference its parent’s window with window.parent. In our case, they do the same thing.
Let’s remove all the code in client.js and replace it with:
This will attempt to redirect the top-level window to the client host. If we run this, we get the following error:
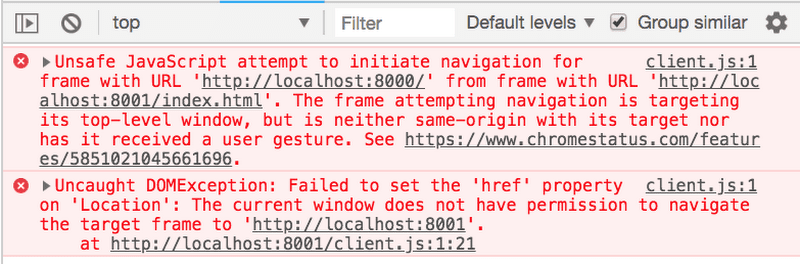
That’s great! It blocks the automatic redirect. But wait — what’s that last part? “… nor has it received a user gesture.”
What does that mean? Does it mean that a user-initiated gesture can navigate the window? Let’s try it.
If we add this code to our JS and HTML respectively, it will add a link to the client page. When we click it, the page navigates!
As it turns out, a user-initiated action can navigate the top-level window, which is the basic idea behind clickjacking. A typical clickjacking attack will put transparent click boxes over a page and then “hijack” the click to redirect the page to a different url. window.open works the same way.
If we have this, the browser will block the pop-up request of the outer function call, however, when we have it in a click handler, it will open the window regardless of whether we blocked pop-ups or not.
The other part of the above error message saying the iframe “does not have the same origin as the window it is targeting” means our iframe is the same origin as the host and it has full access to redirect the page, click-action or not.
If you run this, the browser will allow the redirect to happen since it is the same origin. This is not the case for window.open. Even if it is from the same origin, the browser will block the window.open unless you explicitly tell the browser to allow the pop-up.
Cookies and browser requests
The final thing we are going to look at is browser cookies. Before getting started, make sure your hosted-client iframe is pointed at localhost and your client.js iframe is pointed at 127.0.0.1.
We need to do this because cookies care about domain and ignore the port. Once you have checked this, let’s set a cookie on the host.
This is representing a session ID, something that is often included in requests. Let’s see if our iframes can access the cookies.
As you can see, the client cannot access the cookies since it is a different origin, but the hosted-client can. Let’s try to make a request using the fetch API.
When we do this, we get a 200 response.
That means the server accepted the request and gave us a response, but did it send through the cookies? We can check this on the server side. Let’s add a console log to our host server request handler.
This will output the headers when we make a request to our host server. Make sure you restart the server after you add this line, and then reload your page and look for the request coming from the hosted-client. It looks like this:
As you can see, it sends the cookies through. If the server were to use just the session ID to authenticate the request, then it would think this is a legitimate request.
Step 4: Applying the sandbox attribute to the iFrame
So far, we’ve identified four areas of concern when working with iframes.
- They can exploit pop-up dialog boxes to prevent interaction with the website
- Navigating the top-level window through clickjacking even on different-origin iframes
- Navigating the top-level window when the origin is the same even without user interaction
- Same-origin iframes can make requests with cookies.
Now we’re going to begin making use of the sandbox attribute for iframes, introduced in HTML5. When added to an iframe, the sandboxed iframe restricts pretty much all scripts and browser behavior of any kind. It is not until we add the permissions in a space-separated list that we enable the exact permissions we want to set. To see its initial state, add the attribute as an empty string to both of our iframes.
When we sandbox the iframe, it blocks all scripts from executing
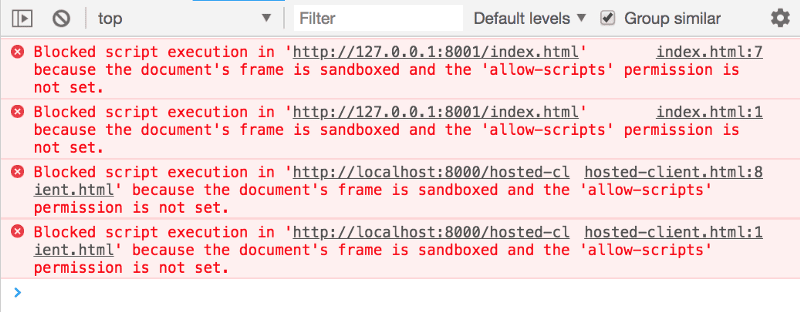
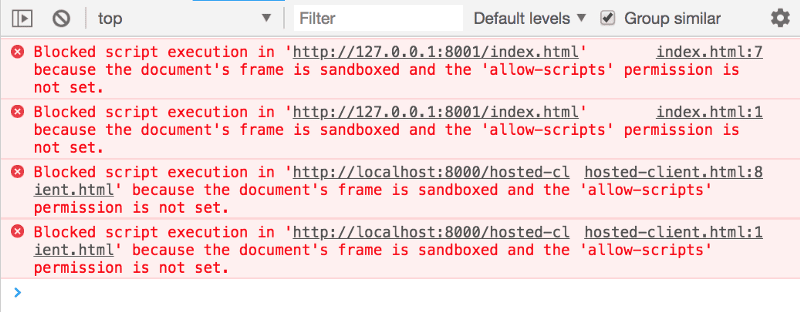
Sandboxed iframes with no permissions block all scripts from running
Getting this to work starts by allowing various permissions one at a time . The full list of string values can be found in the iframe documentation under the sandbox section. We will be starting with allow-scripts.
Allowing scripts
To begin here, let’s clear out our client.js and hosted-client.js and start with a simple console log.
Without defining any permissions, our sandbox won’t allow a console log to run. We can get our script running by adding the allow-scripts permission to our iframe attribute.
Once you do this, and refresh the page, you should see a console log from each of our pages.
Pop-ups and modals
One of the concerns we learned about is that an iframe can pop up dialog boxes at the top of the browsing context and prevent the user from interacting with the page. To see if this is exploitable in a sandbox, let’s add an alert to our client script.
When we run that we get the following error:
Even though we are allowing scripts to run, the sandbox still limits a lot of the browser behaviors. In order for the alert to work from the iframe, we would have to add the allow-modals property to the iframe.
Keep in mind that this is an all-or-nothing thing. We cannot allow some popups and block others. This is an okay restriction, in my opinion, and it crosses off our first iframe security concern.
Top-level window navigation and opening new tabs
Our second and third security concerns are related to navigating the page away from the original URL. We saw that a same-origin iframe could navigate the page without a user interaction, and that a different-origin iframe could do so with user interaction. Let’s try this in our sandbox.
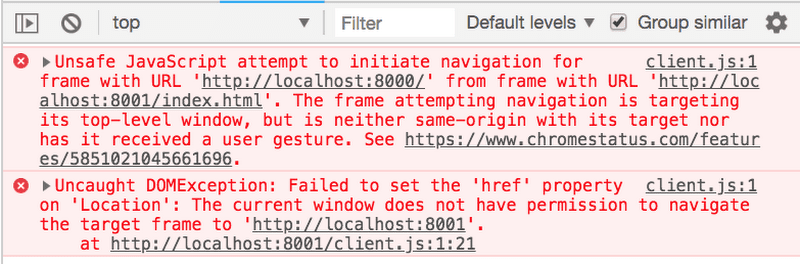
This results in the following errors:
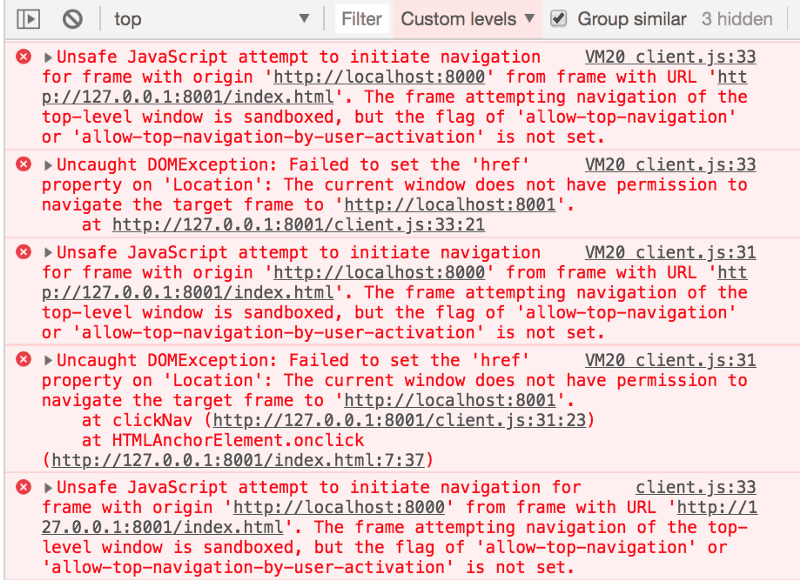
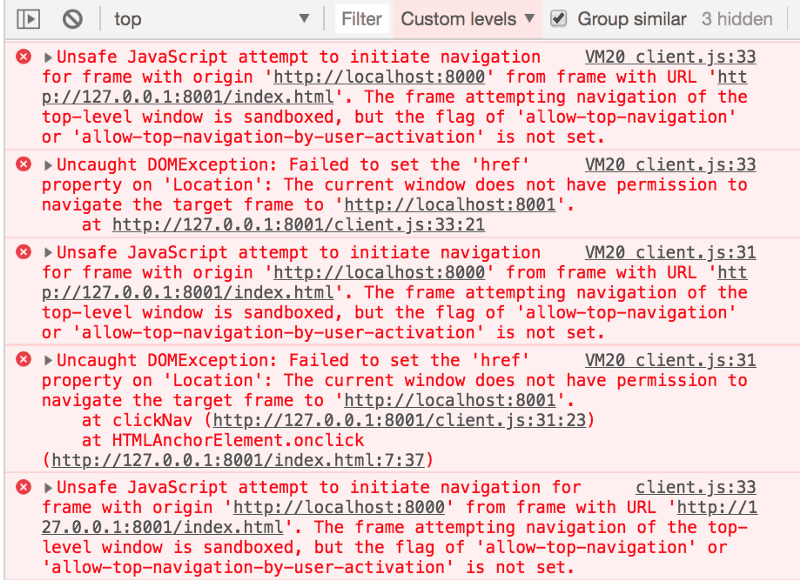
With this, we covered two cases at once. The initial command to change the location failed, as did the one on-click. By applying separate permissions to our iframe for each of these cases, we can allow any navigation with allow-top-navigation and user-activated navigation with allow-top-navigation-by-user-activation.
When we turn this on, the different-origin iframe can redirect the page upon user action. The case is the same for same-origin iframes, where you can explicitly set the navigation permissions, regardless of the origin.
Cookies and browser requests
The final concern to address is the ability to access cookies and make requests with same-origin iframes. Let’s try accessing the cookies with a sandboxed iframe.
Unlike last time, this results in the following error:
Similarly, when we try to make a request with the same request code as the previous section, we get a different error.
The above error is the browser blocking our request because we no longer have the same origin. This is because the sandbox property sets the origin of the frame to null, meaning it will now be a cross-origin request, even though the iframe is hosted on the same domain.
Adding the allow-same-origin sandbox attribute will prevent both of these errors from occurring. However, you should be careful and make sure you have complete control over the content of the frame before using it. As noted in the Mozilla iframe documentation:
“When the embedded document has the same origin as the main page, it is strongly discouraged to use both allow-scripts and allow-same-origin at the same time, as that allows the embedded document to programmatically remove the sandbox attribute. Although it is accepted, this case is no more secure than not using the sandbox attribute.”
Generally speaking, if you find yourself needing both allow-scripts and allow-same-origin for your sandbox, you should ask yourself why you are iframing in the first place, and whether or not having the sandbox property is appropriate.
Putting it all together: how we use iFrames at Looker
As an example of a practical use of this, here at Looker, we use iframes to allow customers to create and run their own custom visualizations within our application.
Without any one way to vet every single line of code our customers could write for their custom visualizations, we needed to create a secure execution environment to run the code in. A diagram of this environment can be seen below.
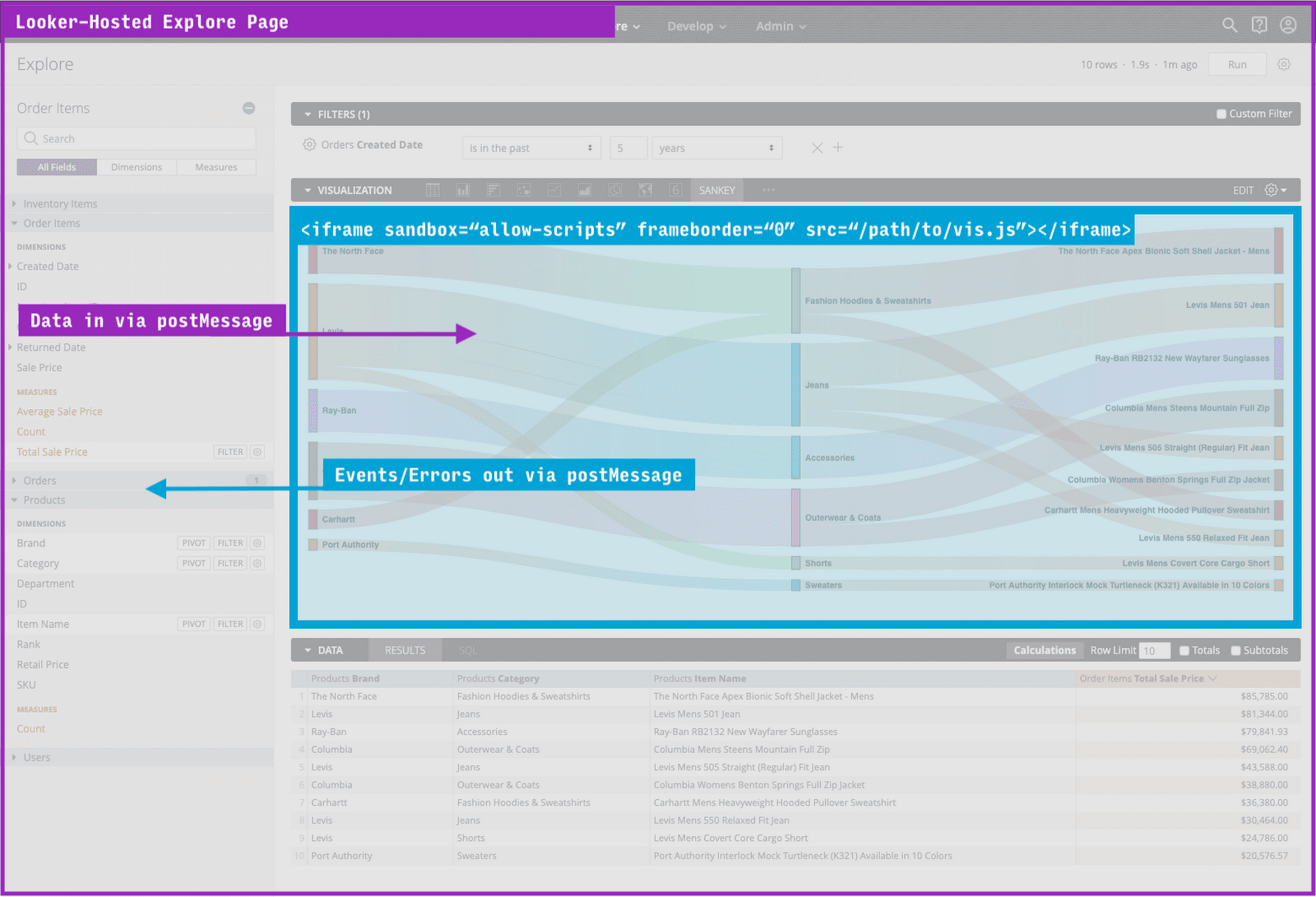
Looker explore page using an iframe to render custom data visualization
We leverage the postMessage API to pass the data in and to receive back any events or errors that the visualization produces. Given the restrictions of the sandboxed iframe, it is not able to make calls outside of its own frame, nor is it able to read or modify anything about the parent page. This let’s us rest assured that both our application and our customers’ data is safe and secure.
Wrapping up
I hope you found this post helpful as you address security concerns related to sandboxed iframes. By walking through this tutorial, you should now have a better understanding of:
- How sandboxed iframes without allow-modals permission prevent user interaction on the page
- How sandboxed iframes without the allow-top-navigation or the allow-top-navigation-by-user-activation properties can alleviate same-origin iframes that can redirect the top-level page, as well as different-origin iframes with some user interaction.
- Why sandboxed iframes without the allow-same-origin property prevent same-origin iframes from having access to the domain’s cookies and making requests as if they were the host.
If you have any questions about this tutorial, feel free to reach out on the Looker Community. And if you’re curious to learn more about our Looker team, check out our open positions.
Important notes
- Although sandboxing is very powerful for security, don’t put all of your security eggs in the sandbox basket, as it is not supported by IE9 and below.
- If you struggled with any part of this tutorial, all of the code can be found in the sandbox-sandbox repository.