Prepare for RSA with this cybersecurity snapshot, by the numbers

Seth Rosenblatt
Security Editor, Google Cloud
Anton Chuvakin
Security Advisor, Office of the CISO
The RSA Conference returns to San Francisco next week. Recent Google Cloud and Mandiant research can help business leaders fine-tune security strategies
The evolution of the printing press was remarkable. The oldest known printed book, the Diamond Sutra in China, dates to 868 A.D. Printing presses still weren’t widespread by the 1450s — until Johannes Gutenberg helped popularize the technology with sturdy, alloy metal letter blocks, oil-based ink, and other innovations. Less than a century later, there would be an estimated 2,500 printing presses in Europe, one in nearly every city on the map.
Cloud technology’s Gutenberg moment has arrived, and it is dominating the IT landscape — but instead of taking centuries, it’s taken less than two decades to reach this point. To take advantage of the best benefits of the cloud, organizations engaging in digital transformations will also need to transform their approach to security. Cyber threats continue to rise, and they cost businesses more money and time every year. Global cyber attacks worldwide increased by 38% in 2022, and the annual cost of cybercrime could reach $10.5 trillion by 2025.
To help the C-suite, IT, and business decision-makers stay sharp with industry-shaping security trends and prepare for April’s RSA Conference next week, we’ve pulled together the following statistics from recent Google Cloud and Mandiant research that help paint a picture of what’s happening in the market and how business leaders can fine-tune their strategies as a result.
1. Cybersecurity is the No. 1 investment priority for organizations in 2023.
How important is cybersecurity as an investment priority? Of 4,332 global enterprise cloud decision makers who responded to a recent Google Cloud survey, 31% ranked “cybersecurity” as a top investment priority for their organization in 2023, outpacing data management and/or data analytics (25%), AI&ML (20%), app and/or infrastructure modernization (12%), and productivity & collaboration (11%). Download slide. Source: Google Cloud Brand Pulse Survey, Wave 5, 2022.
2. It’s a matter of trust — and how to build it.
How do you know that you can trust a cloud provider? Cloud providers can gain trust with enterprise decision makers when they offer “strong capabilities for protecting and controlling my data in the cloud” (40%) and “working well with existing security solutions and other security vendors” (38%). Download slide Source: Google Cloud Brand Pulse Survey, Wave 5, 2022.
Along similar lines, 71% of the respondents to our State of Cloud Detection and Response report, published in March, said that “entire classes of threats” are eliminated by migrating to the cloud. And weak or no identity credential requirements are behind 48% of compromised cloud systems, according to research from our January Threat Horizons report.
3. Good news: Attacker dwell time is decreasing.
The global median dwell time, which is the time between when an organization is compromised and when the attack is discovered, was 16 days in 2022. That’s an improvement from the previous year, which had a global median dwell time of 21 days, and a giant leap from 2011, when the median dwell time was 416 days. Source: M-Trends 2023, Mandiant.
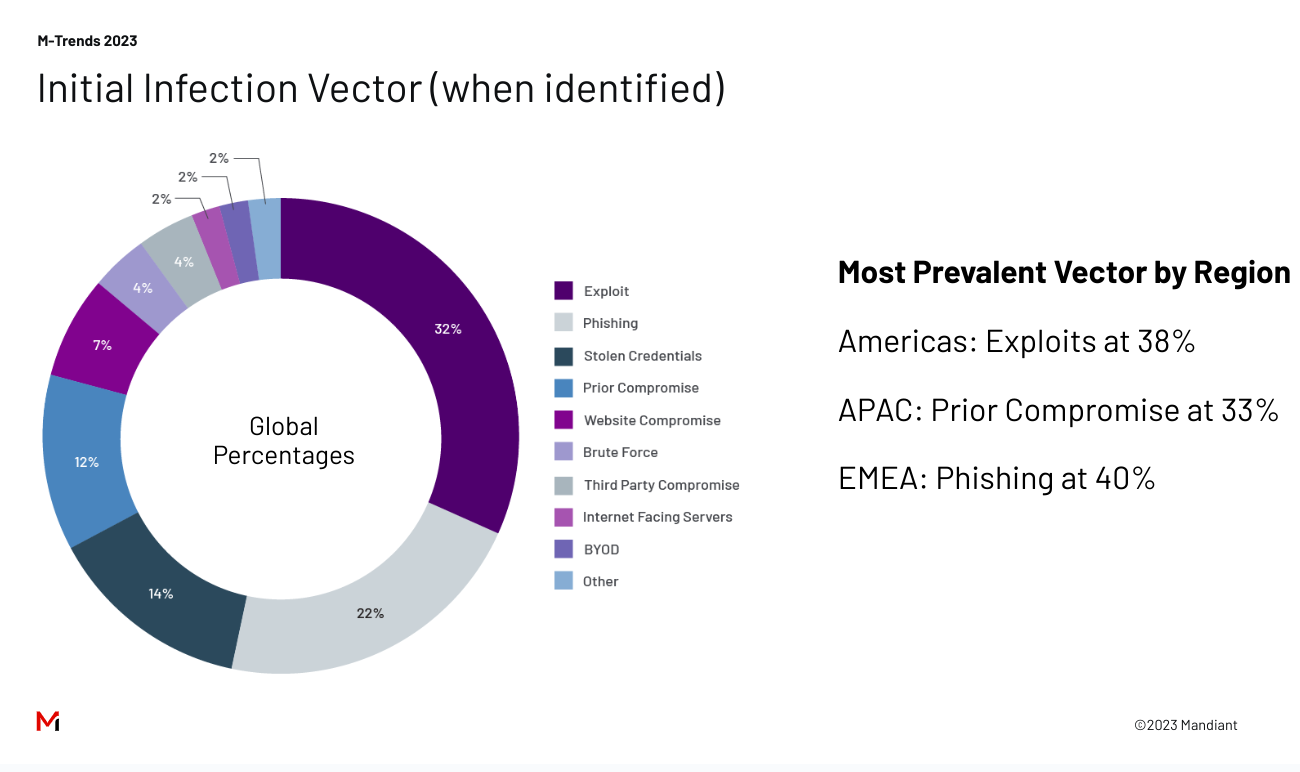
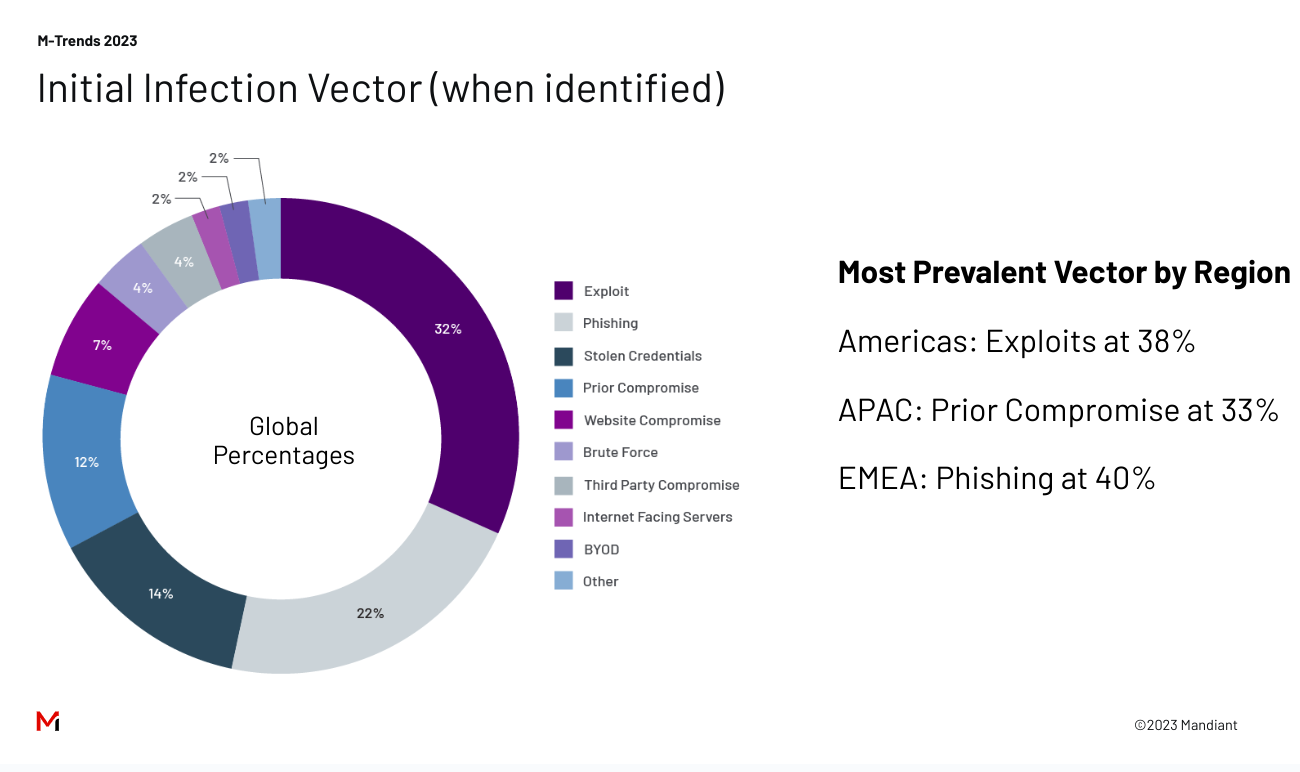
4. The most successful methods of initiating a cyberattack change depending on the location of your organization.
The world is not homogenous, and neither are the ways that threat actors start their cyberattacks. To gain access to organizations, attackers are leveraging what works best in different regions. Exploits are the most successful method for launching an initial cyberattack in the Americas, where 38% of cyberattacks start that way. In EMEA (Europe, the Middle East, and Africa), 40% of successful attacks start with phishing, and 33% of successful attacks begin with prior compromises in the APAC (Asia-Pacific) region. Source: M-Trends 2023, Mandiant.
5. Automation can help achieve better security outcomes for APIs.
API security concerns have delayed the rollout of new services and applications, said more than half (53%) of organizations we surveyed. That jumps to 77% for organizations that have experienced a security incident in the past 12 months.
To stay ahead of security threats, many organizations look for solutions that allow them to be proactive while minimizing the burden on their security teams. Capabilities that identify security threats (60%) and improve security automation (57%) are at the top of most IT leaders’ wish lists. Download slide. Source: API Security: Latest Insights & Key Trends.
6. The biggest predictor of the quality of an organization's software security practices is cultural, not technical.
High-trust, low-blame cultures focused on performance were 1.6 times more likely to have above-average adoption of emerging security practices than low-trust, high-blame cultures focused on power or rules. Download slide. Source: 2022 State of DevOps Report, commissioned by the Google Cloud DORA Team.
Actions you can guide your security teams towards include endpoint hardening, proper management of credentials, and recovery planning. If possible, make it a requirement to regularly test your abilities with a ransomware defense assessment.
Phil Venables, VP and CISO, Google Cloud
7. Europe may surpass the United States as the most targeted region for ransomware.
Ransomware continues to have a significant impact on businesses across the globe, but especially in the U.S. and Europe. While reports show that the U.S. is the country most targeted by ransomware attacks worldwide, some indicators show that ransomware activity is decreasing in the United States and growing in Europe.
As Google’s Threat Analysis Group noted in its Fog of War report on the cybersecurity impacts of Russia’s invasion of Ukraine, “The invasion has triggered a notable shift in the Eastern European cybercriminal ecosystem that will likely have long term implications for both coordination between criminal groups and the scale of cybercrime worldwide.”
“Executive leaders can help prioritize and identify an organization’s most valuable assets,” said Google Cloud CISO Phil Venables in a blog post about the report. “Actions you can guide your security teams towards include endpoint hardening (such as firewall protections), proper management of credentials (such as identity and access tools), and recovery planning. If possible, make it a requirement to regularly test your ability to prevent, detect, and respond to threats with a ransomware defense assessment.”
With the number of European victims on the rise, Europe could become the region most targeted by ransomware in 2023. Download slide. Source: Cybersecurity Forecast 2023, Mandiant.
Organizations need security partners with proven expertise, solutions, and extended support capable of addressing this new reality. This includes gaining the latest, unique threat intelligence, comprehensive visibility across their attack surface and infrastructure, and the ability to rapidly detect, investigate, respond to, and remediate security incidents.
For more cloud computing statistics and trends, please read our digital forecast for 2023. And visit Google Cloud and Mandiant at the RSA Conference April 24-27 to see how our portfolio of security solutions can help support your security transformation.