Protect your users’ accounts with reCAPTCHA Enterprise’s account defender
Badr Salmi
Product Manager Lead, Web Risk, User Protection Services
Aaron Malenfant
Technical Lead reCAPTCHA
reCAPTCHA Enterprise is Google’s online fraud detection service that leverages over a decade of experience defending the internet. reCAPTCHA Enterprise can be used to prevent fraud and attacks perpetrated by scripts, bot software, or humans. When installed on a web page at the point of action, such as login, purchase, or account creation, reCAPTCHA Enterprise provides a frictionless user experience that allows legitimate users to proceed while fake users and bots are blocked.
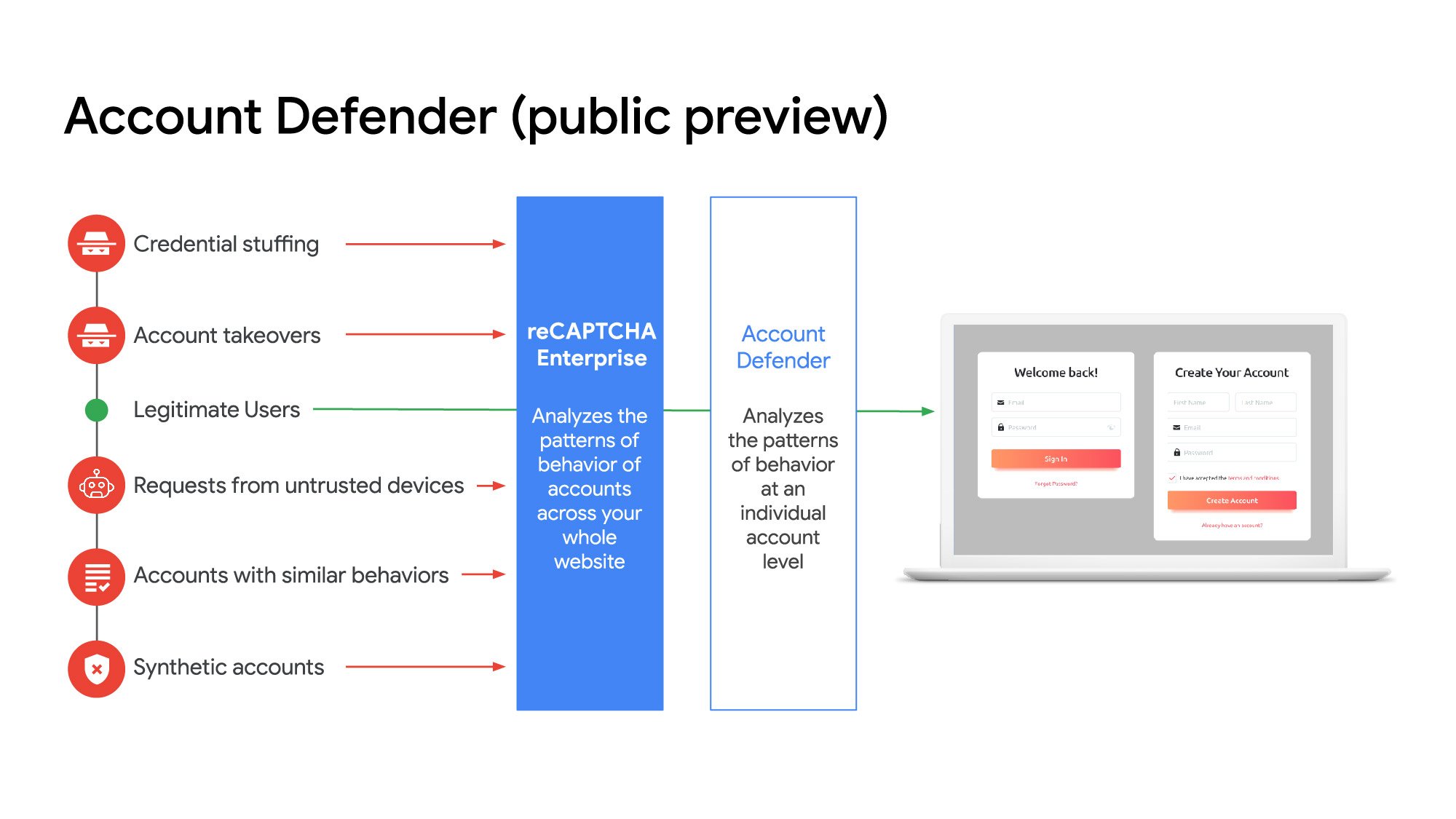
As part of our continued investment to offer more tools to fight online fraud targeting your accounts and payments, we are pleased to announce account defender in public preview. It’s a new feature built into reCAPTCHA Enterprise that helps you determine if an action aligns or deviates from the account owner’s typical behavior.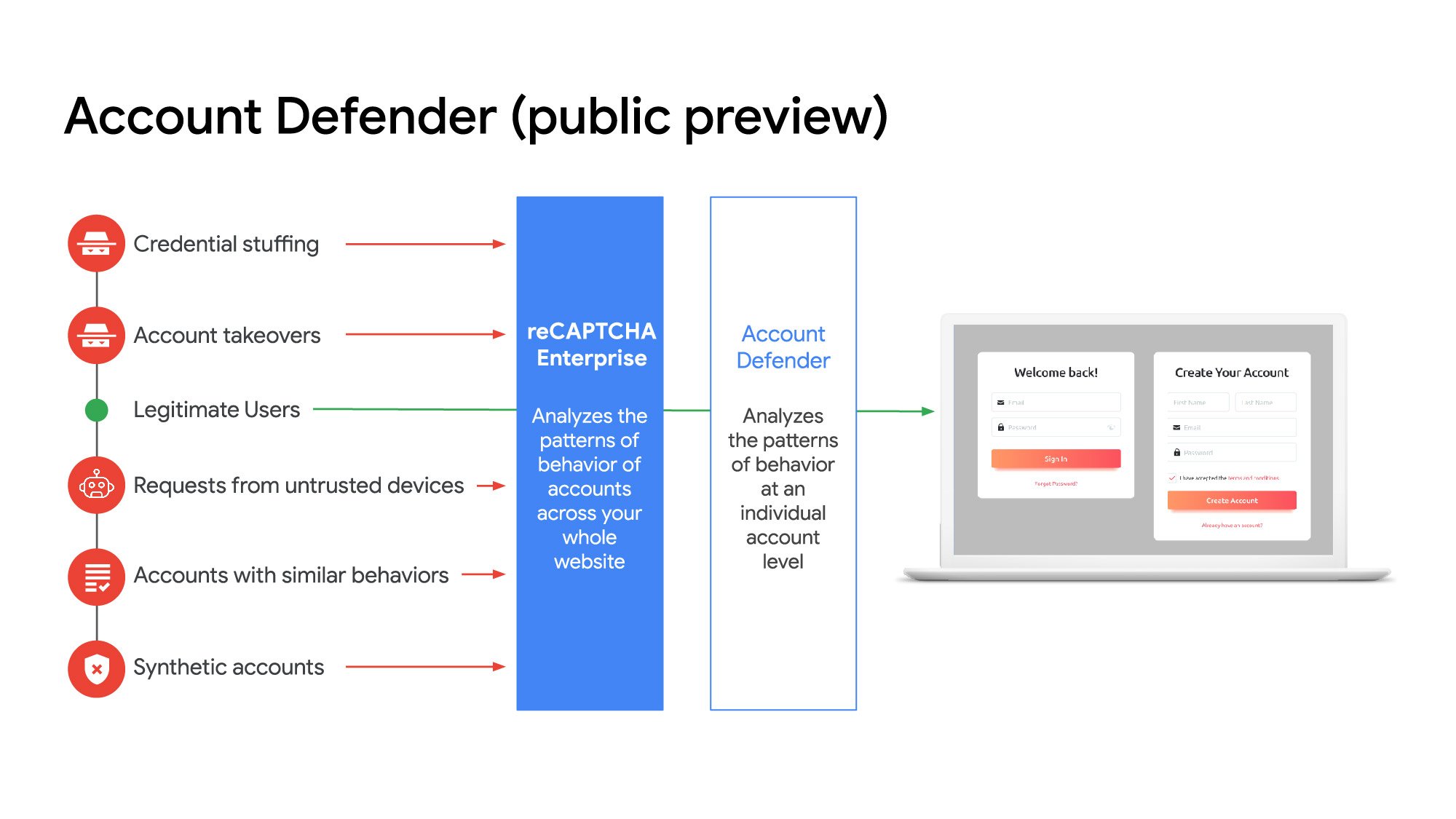
What is account defender?
Account defender takes reCAPTCHA Enterprise's traditional detection a step further. It analyzes if the request is in alignment with the normal patterns of behavior demonstrated from the account, not just your website. This analysis is achieved by using a site-specific model that observes typical behavior patterns across your website to detect suspicious behavior or a change in activity. By using the site-specific model, reCAPTCHA Enterprise account defender helps you detect these main scenarios:
Suspicious activities linked to a potential account takeover or fake account
Accounts on your website with similar behaviors
Requests coming from devices that were marked as trusted for specific users
Synthetic accounts
By using account defender, you can:
Restrict or disable fraudulent accounts
Prevent account takeover attempts
Mitigate the successful account takeovers
Grant access only to the requests coming from legitimate user accounts
Reduce friction for users logging in from one of their trusted devices
How account defender works
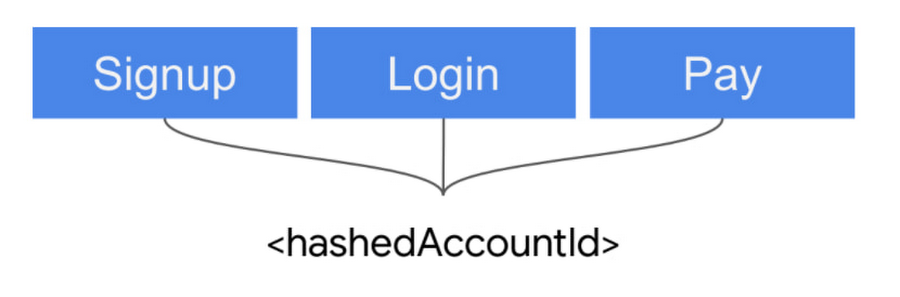
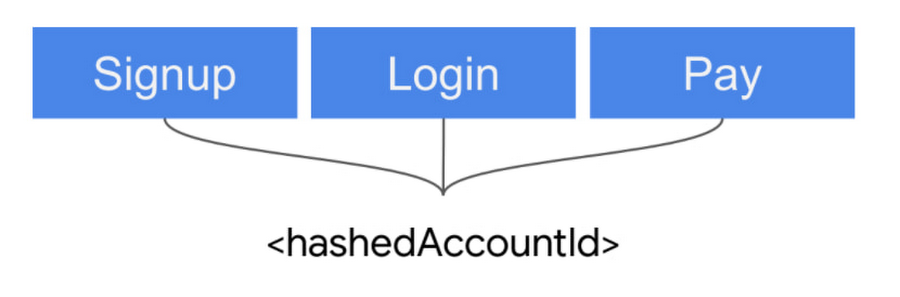
reCAPTCHA Enterprise account defender ties activity to a pseudonymous account identifier (labeled as hashedAccountId in the product) to the site owner. This is to protect the user’s privacy– the identity of the user can only be tied back to a plaintext username by the site owner. The user account identifier is then used by the site owner to annotate data related to the account. For example, the site owner generates a unique hashId such as 36228b7496a6ab9bb5fecf12b5799105 for their user. All requests from that user should include this hash for sensitive actions such as ‘login’, ‘signup’, ‘payment’ or ‘search’. This will allow reCAPTCHA Enterprise to build site specific models to determine if this account is hijacked or fake.
When combined with the already available Annotations API, site owners can send us account-related metadata such as incorrect password entry or passed two-factor authentication, which will help reCAPTCHA Enterprise determine suspicious patterns of activity.
To understand why account defender made its decision, we return additional details to indicate that this is an expected behavior for the user. On the other hand, if we have seen abusive requests that look like the current request, account defender will label this request as either a suspicious login or account creation.
If fraud is detected on your website from a user, a site owner can use the related accounts’ API to search for similar users. This will give site owners all hashed account identifiers showing similar behavior, allowing them to also investigate these accounts for fraud. To find new malicious accounts, you can look at account groups and analyze their usage patterns to determine if they are malicious. This allows you to protect all sensitive actions on your website including signups, logins, and payments.
Further secure your account with multi-factor authentication and recommended actions
If you integrate with reCAPTCHA Enterprise’s multi-factor authentication, account defender will return a recommended action to indicate whether or not you should challenge a user. This capability helps reduce user friction for real users as well as costs associated with SMS authentication. If you use a non-Google MFA provider, this same capability can be achieved through the Annotations API.
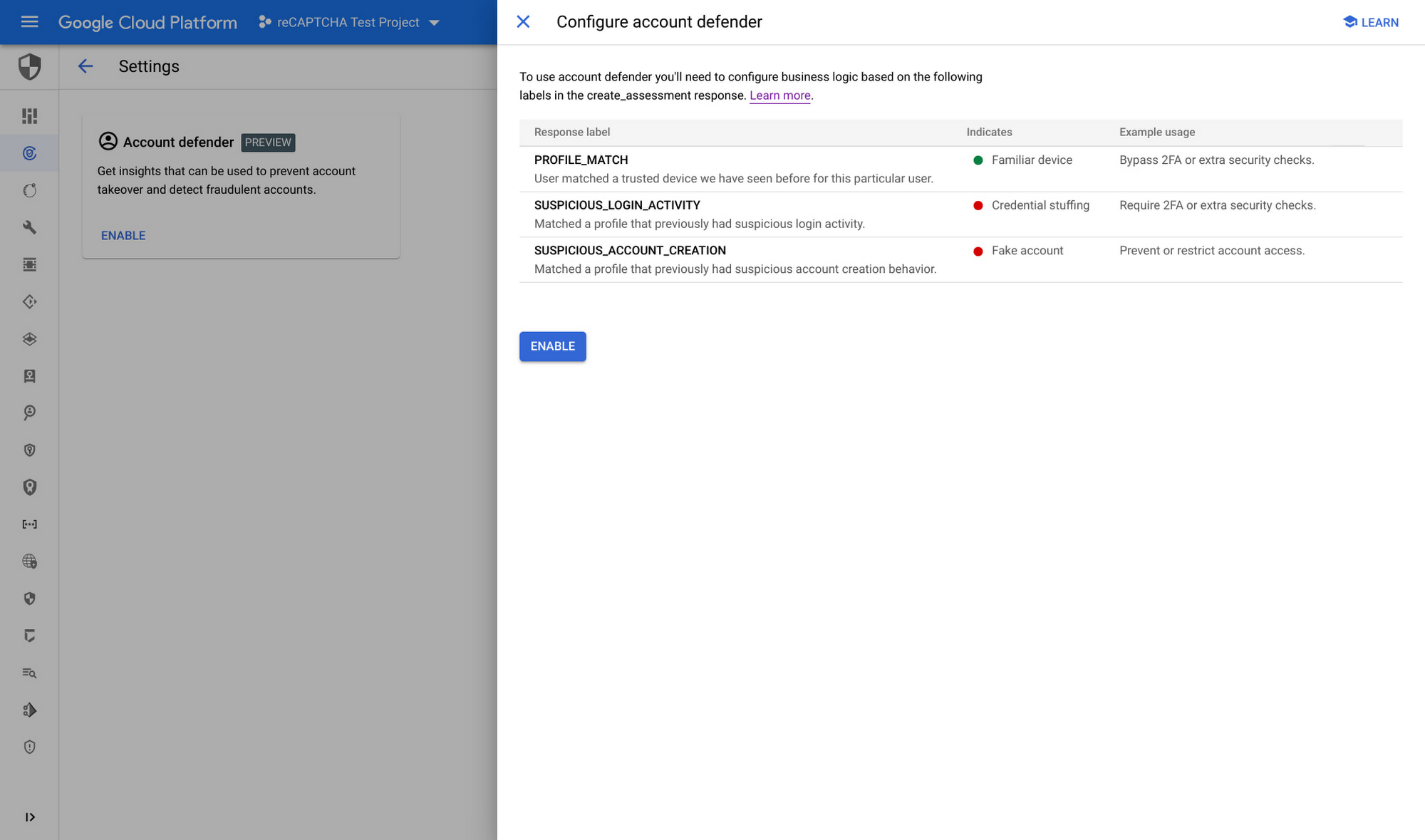
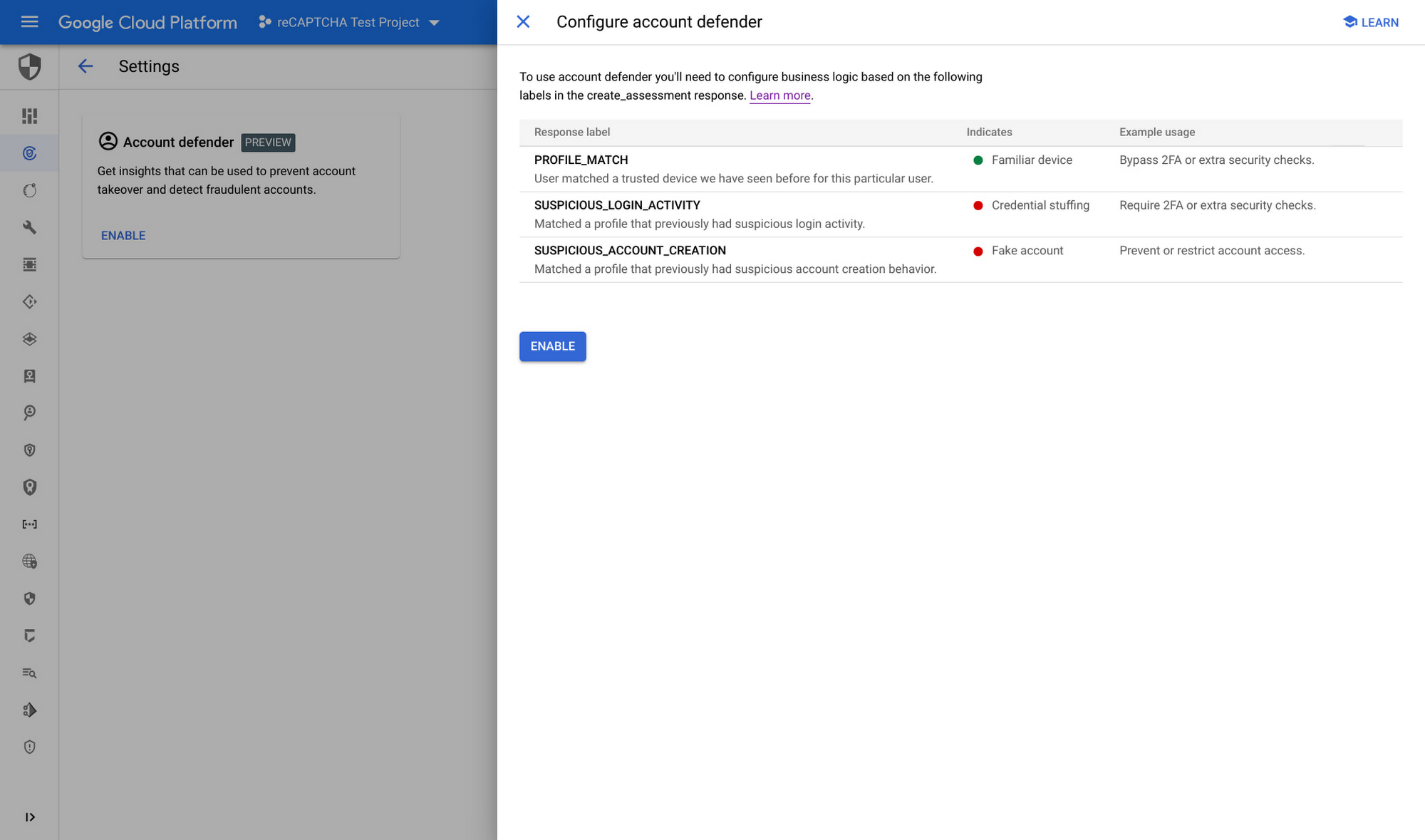
Get started with account defender
New and current reCAPTCHA Enterprise customers can easily activate account defender in the Google Cloud console in a few clicks. For more detailed guidance, you can check out our documentation.
To learn more about how to use account defender to protect against account and payment fraud, sign up for our webinar on Tuesday, March 29 at 9am PST.


