Protecting your cloud VMs with Cloud IAP context-aware access controls
Christiaan Brand
Group Product Manager, Security & Identity
Organizations have increasing numbers of Internet-facing apps and infrastructure that they need to protect. Since 2011, Google has been leveraging the BeyondCorp security model to protect our internet-facing resources, and over the past few years we have made it easier for you to adopt the same model for your apps, APIs, and infrastructure through context-aware access capabilities in our cloud products. At Next ‘18 in London, we added context-aware access capabilities to Cloud Identity-Aware Proxy (IAP) to help protect web apps. Today, we are extending these capabilities to TCP services such as SSH and RDP, to help protect access to your cloud-based virtual machines (VMs).
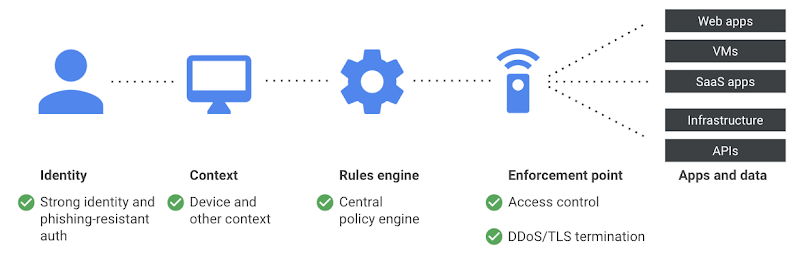
A zero trust security model for your apps and infrastructure
Context-aware access allows you to define and enforce granular access to cloud resources based on a user’s identity and the context of their request. This can help increase your organization’s security posture while decreasing complexity for users, giving them the ability to access apps or infrastructure resources securely from virtually anywhere and any trusted device.
Granular access controls
Unlike the all-or-nothing approach often used in the traditional network-based access model, context-aware access helps you ensure that access is restricted to the right people and only to the right resources. You can now determine who can access a VM based on unique security considerations such as location, device security status, and user’s identity. In addition, VMs protected by IAP require no changes—simply turn on IAP, and access to your VM instance is protected.
Here’s how it works
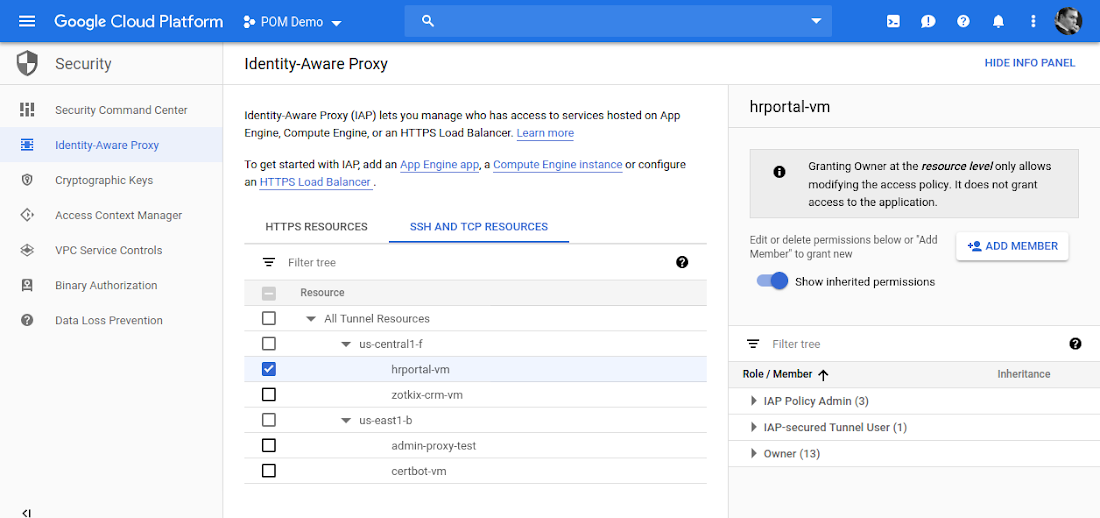
Let’s say you’re an administrator who wants to allow SSH access to VMs for a group of DevOps users in GCP. You can now use Cloud IAP to enable access without exposing any services directly to the Internet. DevOps admin simply configures Cloud IAP’s TCP forwarding feature. Subsequently when a user performs SSH from the gCloud command tool, the SSH traffic is tunneled over a websocket connection to Cloud IAP which applies any relevant context-aware access policies. If access is allowed the tunneled SSH traffic is forwarded to the VM instance transparently. Remote Desktop Protocol (RDP) works similarly. As an administrator, all you have to do is configure access to the VM instances from the Cloud IAP IP subnet; your VM instances don’t even need public IP addresses or dedicated bastion hosts.
Getting started
Context-aware access for TCP services in Cloud IAP is now available in beta. To get started, navigate to the admin console and check out the documentation for step-by-step instructions.

