Introducing the Cloud KMS plugin for HashiCorp Vault
Seth Vargo
Distinguished Software Engineer
HashiCorp Vault is a powerful open source tool for secrets management, popular with many Google Cloud customers. Vault provides "secret management as a service," and we strive to make Google Cloud an excellent platform on which to operationalize it.
Today, we are pleased to announce the Cloud Key Management Service (KMS) secrets engine for HashiCorp Vault. Building on the security and scalability of Cloud KMS, Vault users can manage Cloud KMS keys, encrypt/decrypt data, and sign/verify data using the familiar Vault API.
The Vault GCP KMS secrets engine brings a number of features and benefits:
Familiar APIs, authentication, and authorization - With this new secrets engine, you'll interact with Cloud KMS using the HashiCorp Vault APIs and syntax with which you're already familiar. After users authenticate to Vault using any pre-configured authentication method, they can create new KMS keys, rotate primary KMS key versions, and encrypt/decrypt data–all using the Vault API.
Unprivileged ciphertext upgrades - Users can upgrade ciphertext to the latest version of a crypto key without revealing the plaintext data, allowing unprivileged processes to re-encrypt data over time.
FIPS 140-2 Level 3 certification - Cloud KMS keys can optionally be backed by Google Cloud HSM. Once configured, cryptographic operations such as encryption and decryption are performed on a FIPS 140-2 Level 3 HSM. This is ideal for customers subject to complex regulatory compliance or for customers who require the highest levels of trust and security.
Getting started
To get started, download and install the latest version of HashiCorp Vault. The Vault GCP KMS secrets engine was added in Vault 1.0.0 (beta released on October 23, 2018), so make sure you're running that version or later before you continue.
Next, start a Vault server. This example uses Vault's built-in development mode, which does not represent best practices or a production-hardened installation, but it's one of the fastest ways to try the new Vault GCP KMS secrets engine.
Next, enable the GCP KMS secrets engine.
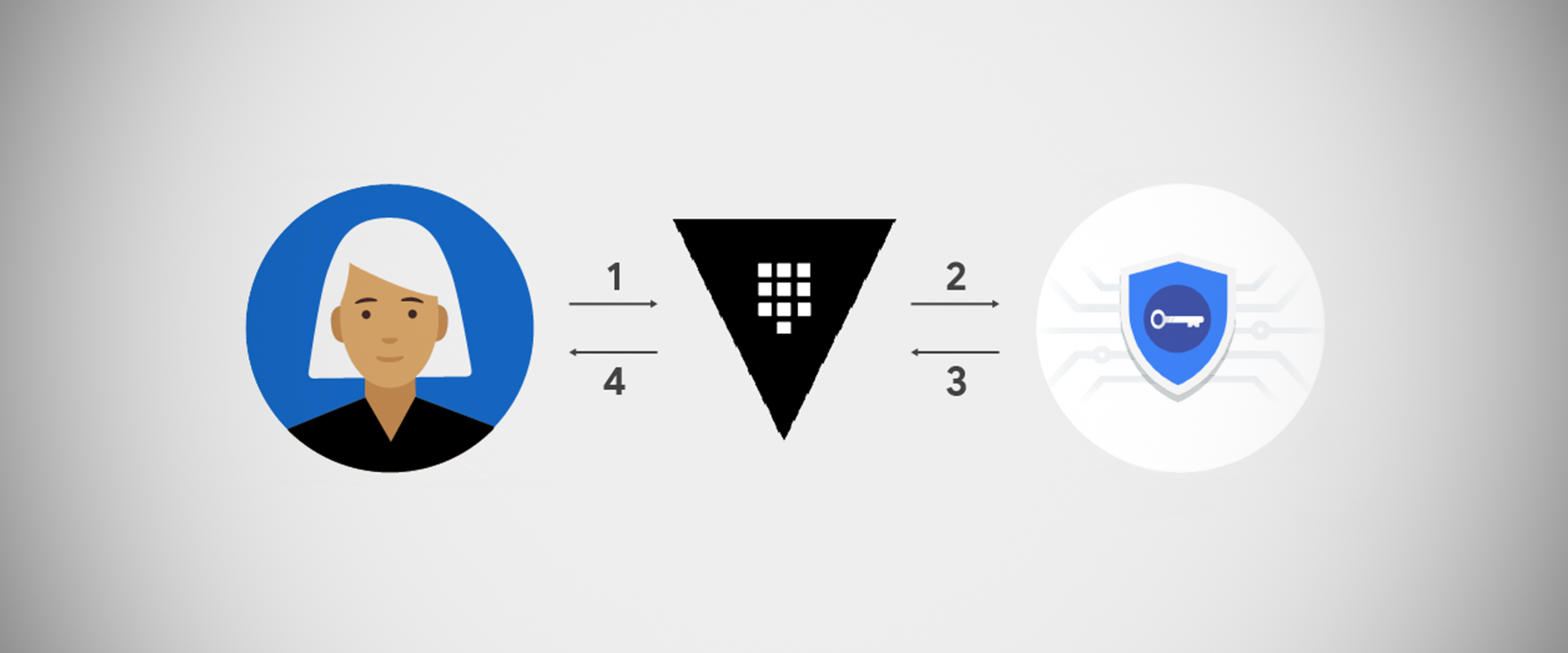
Then, create a Cloud KMS key using Vault. During this process, Vault makes the necessary API calls to Cloud KMS to create a key ring, crypto key, and crypto key version. The metadata is stored in Vault, but the actual encryption keys are stored and managed by Google Cloud.
Next, encrypt plaintext data using this KMS key with Vault. You will receive back ciphertext. Neither HashiCorp Vault nor Cloud KMS store the ciphertext. You are responsible for persisting the ciphertext.
When you want to retrieve the plaintext, give Vault the stored ciphertext. Vault makes the necessary API calls to Cloud KMS to decrypt the ciphertext.
It is also possible to rotate crypto keys, upgrade ciphertext data, restrict key versions, and perform asymmetric signing and verification. To learn more about the Vault GCP KMS secrets engine, read the HashiCorp Vault Cloud KMS secrets engine documentation. To learn more about Cloud KMS, check out the Cloud KMS documentation.
A look toward deeper Vault integrations on Google Cloud
The KMS Vault secrets engine enables organizations to leverage the familiarity and flexibility of Vault with the security and piece of mind of globally available keys and optional HSM FIPS 140-2 Level 3 encryption of Cloud KMS. In addition to providing this great new integration for our customers, we are also delighted to continue our relationship with HashiCorp as part of our long-standing partnership. We are excited to see how this new secrets engine enables organizations to be more successful with Vault on GCP. Be sure to follow us on Twitter and open a GitHub issue if you have any questions.

