How you can build a FedRAMP High-compliant network with Assured Workloads
Haider Witwit
Customer Engineer - Networking Specialist, Google Cloud
Neha Chhabra
Product Manager
Get original CISO insights in your inbox
The latest on security from Google Cloud's Office of the CISO, twice a month.
SubscribeGoogle Cloud recently achieved a major U.S. government compliance milestone with more than 130 services, including 12 additional Cloud Networking services, approved for FedRAMP High authorization — the strictest standard for protecting the most sensitive unclassified data. To help our customers securely deploy a network architecture that aligns with FedRAMP High, we have outlined several of our recommended best practices.
Google Cloud's Assured Workloads enables public sector customers to run regulated FedRAMP High workloads on Google's public cloud infrastructure. By enforcing U.S. data location and personnel access controls, Assured Workloads simplifies the process of maintaining security and compliance while allowing customers to take advantage of the flexibility and innovation of Google Cloud.
The new Cloud Networking additions to Google Cloud’s FedRAMP High authorization include:
- Cloud Router
- Cloud NAT
- Cloud VPN
- Cloud Interconnect
- Cloud Load Balancing
- Cloud Armor
- Cloud IDS
- Cloud CDN
- Traffic Director
- Network Intelligence Center
- Network Connectivity Center
- Network Service Tiers
The full list of Google Cloud services in scope for FedRAMP High is available here.
Configuring Assured Workloads network foundations for FedRAMP High
Customers should start by creating an Assured Workloads folder within their org, and setting the control package to FedRAMP High. This folder provides a boundary within the org to identify regulated data types. By default, any project under this folder will inherit the security and compliance guardrails set at the folder level by Assured Workloads.
The Assured Workload folder will enforce security controls on supported Google Cloud products to adhere to the FedRAMP High control package. These controls include setting an organization policy that restricts resource usage to only supported products, and allows creating or using resources only in allowed locations. It is important to review services in scope for FedRAMP High to assure support for services before using them in your design.
Next, you can create new or migrate existing projects inside the Assured Workload folder to host your resources. You can also create sub-folders if needed.
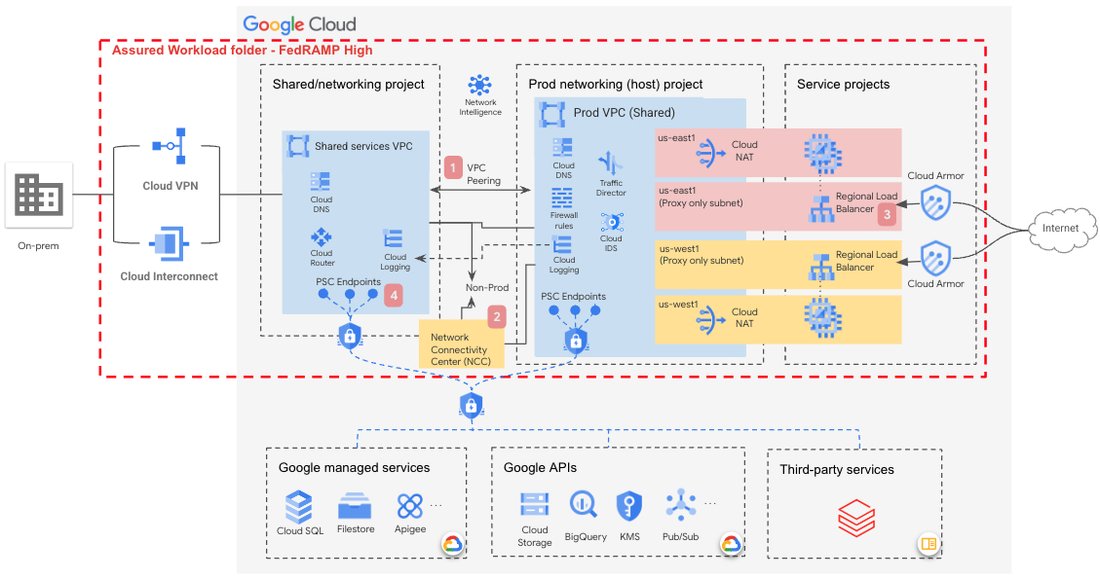
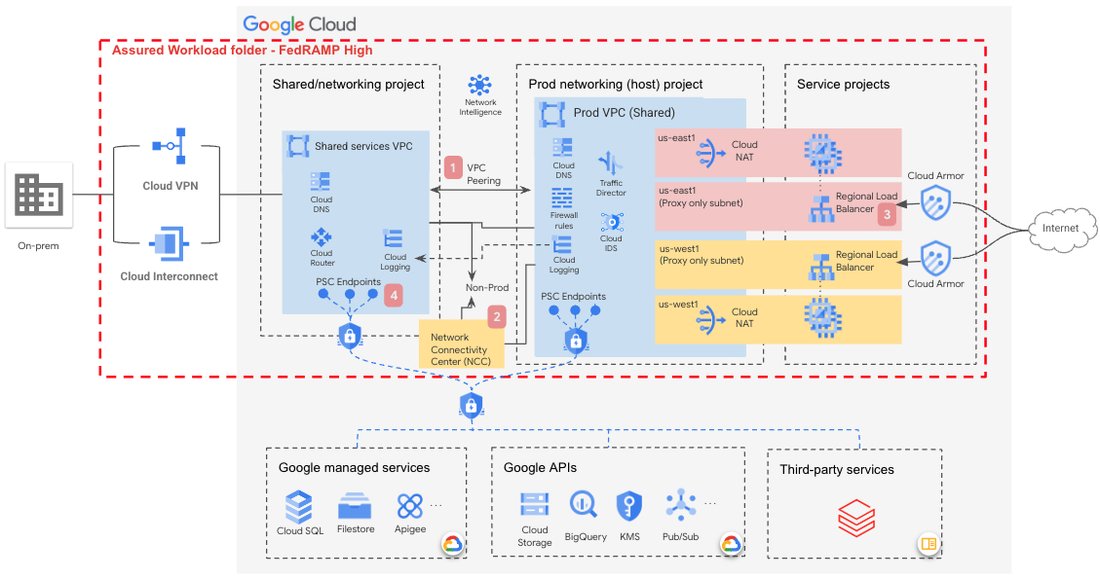
Example network landing zone solution that leverages services in scope within a FedRAMP High boundary.
This diagram shows an example of a landing zone solution for FedRAMP High network boundaries. Please note some of its important features:
- Multiple VPCs are used to separate Prod from non-Prod environments in a hub and spoke design using VPC Peering. VPCs by design are global, but Assured Workload restrictions will prevent creation of subnets outside supported Assured Workloads locations.
- If spoke to spoke connectivity is needed we recommend a NCC hub with VPC spoke types to address the lack of transitivity over VPC Peering.
- Regional Load Balancers protected by Cloud Armor are used to provide external access to web and TCP/UDP workloads hosted in Shared VPC service projects.
- Private Service Connect endpoints are used to provide private access to GCP managed and third party services.
For more detailed guidance on how to configure the proposed design, check out how to configure networks for FedRAMP and the U.S. Department of Defense in Google Cloud.

