Extending our Trusted Cloud: Introducing Cloud IDS for Network-based Threat Detection
Shailesh Shukla
Vice President and General Manager, Networking, Google Cloud
Megan Yahya
Product Manager Cloud IDS
Try Google Cloud
Start building on Google Cloud with $300 in free credits and 20+ always free products.
Free trialEvery day, Google Cloud helps customers around the world stay ahead of evolving threats and keep their workloads safe. Today, we’re advancing these efforts with Cloud IDS, our new network security offering, which is now available in preview. With Cloud IDS, we’re extending our trusted cloud with native network-based threat detection capabilities to help you solve your most critical network security challenges.
Cloud IDS delivers easy-to-use, cloud-native, managed, network-based threat detection. With Cloud IDS, customers can enjoy a Google Cloud-integrated experience, built with Palo Alto Networks’ industry-leading threat detection technologies to provide high levels of security efficacy.
Cloud IDS is simple to set up and deploy. In just a few clicks, you can deploy Cloud IDS and benefit from in-depth network threat detection. Customers can also leverage Cloud IDS to gain deep insight into network-based threats and support industry-specific compliance goals that call for the use of an intrusion detection system.
Cloud-native, managed network threat detection
We’ve heard time and time again that customers want an easier path to network threat detection, built into our cloud, that is easy to deploy and manage. They’ve also made it clear that they need broad visibility into traffic coming into their cloud environment as well as traffic between workloads. Finally, they cannot compromise on security efficacy - the ability for the system to detect malicious activity with low false positives. Cloud IDS addresses all of these needs.
“Cloud IDS was simple and straightforward to deploy, and easy to manage. That's important to us; we want to spend our time on mitigation, not setup and management. It enables us to focus on the most critical alerts so we can respond to them quickly.” - Paras Chitrakar, Co-Founder/Chief Technology Officer, Dave.com
Cloud IDS not only has visibility into traffic to and from the Internet, but it can also monitor east-west traffic, which includes both intra- and inter-VPC communication for suspicious lateral movement. What’s more, because Cloud IDS is an end-to-end cloud-native solution, customers can leverage an extensive, continually updated, built-in catalog of attack signatures from Palo Alto Networks’ threat analysis engine to detect the latest threats, as well as anomaly detection for unknown threats.
“Our team was looking for cloud-native network threat detection and got enrolled in a private preview of Cloud IDS. All in all my feedback so far from using Cloud IDS is very positive. The ease of set up is what I had hoped for and it was simple and quick to deploy. I really look forward to experimenting more with this new offering.” - Josh Harshman, Senior Software Engineer - Platform, Bitly
Network threat detection built with industry-best security efficacy
We’re delivering a strong combination of Google Cloud’s trusted cloud infrastructure and Palo Alto Networks’ best-in-class threat detection technologies in Cloud IDS. Palo Alto Networks’ threat detection capabilities are backed by their threat analysis engine and extensive security research teams that continually add to the catalog of known threat signatures and leverage other threat detection mechanisms to stay on top of unknown threats.
“We continue to expand our partnership with Google Cloud to help customers achieve their business goals as they move to the cloud. By combining the simplicity of native cloud controls in Google Cloud and our best-in-class security to help keep our customers’ networks safe with Cloud IDS, customers will no longer need to strike a compromise between security and simplicity on their most important digital initiatives.” - Muninder Singh Sambi, Senior Vice President of Product Management, Palo Alto Networks
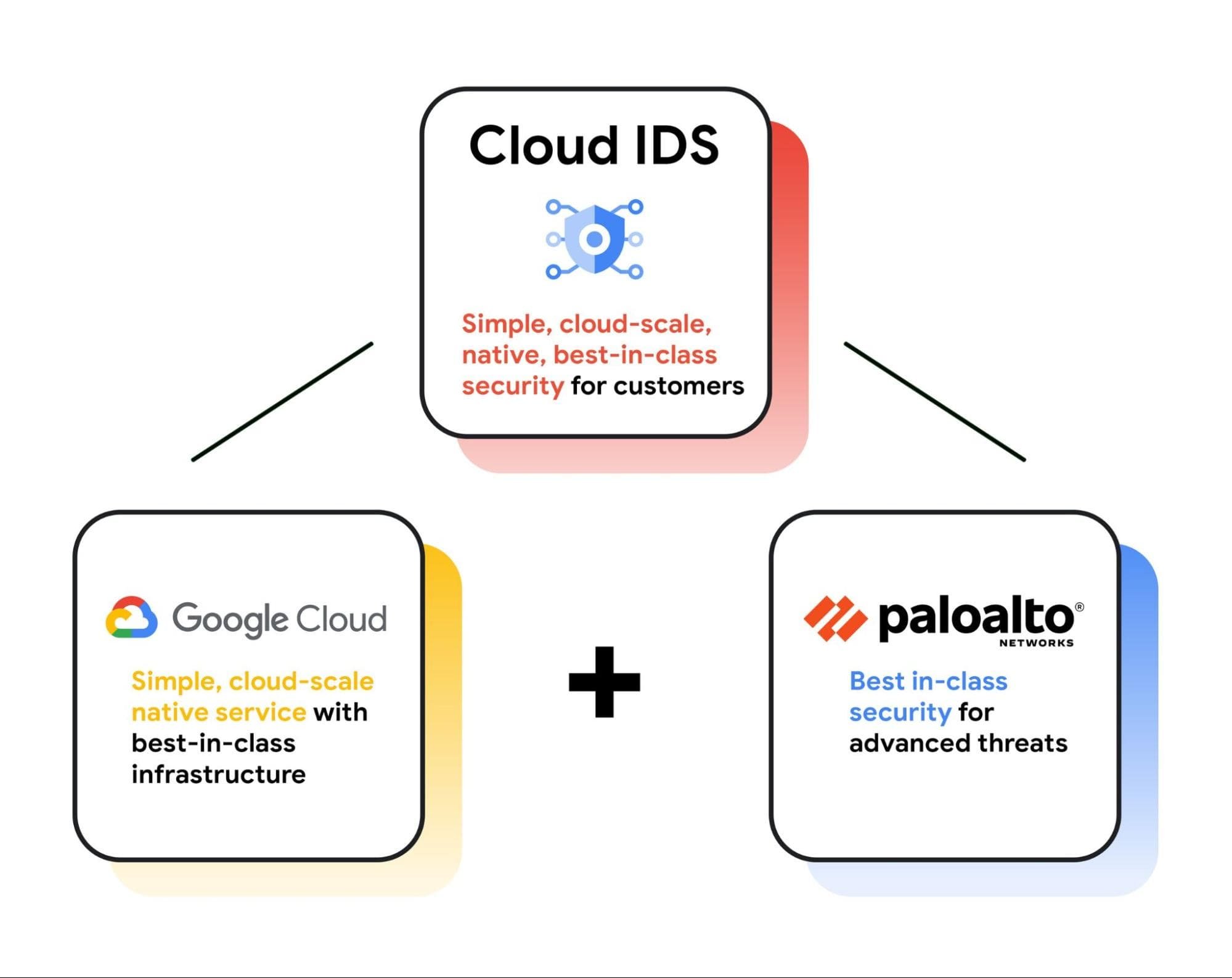
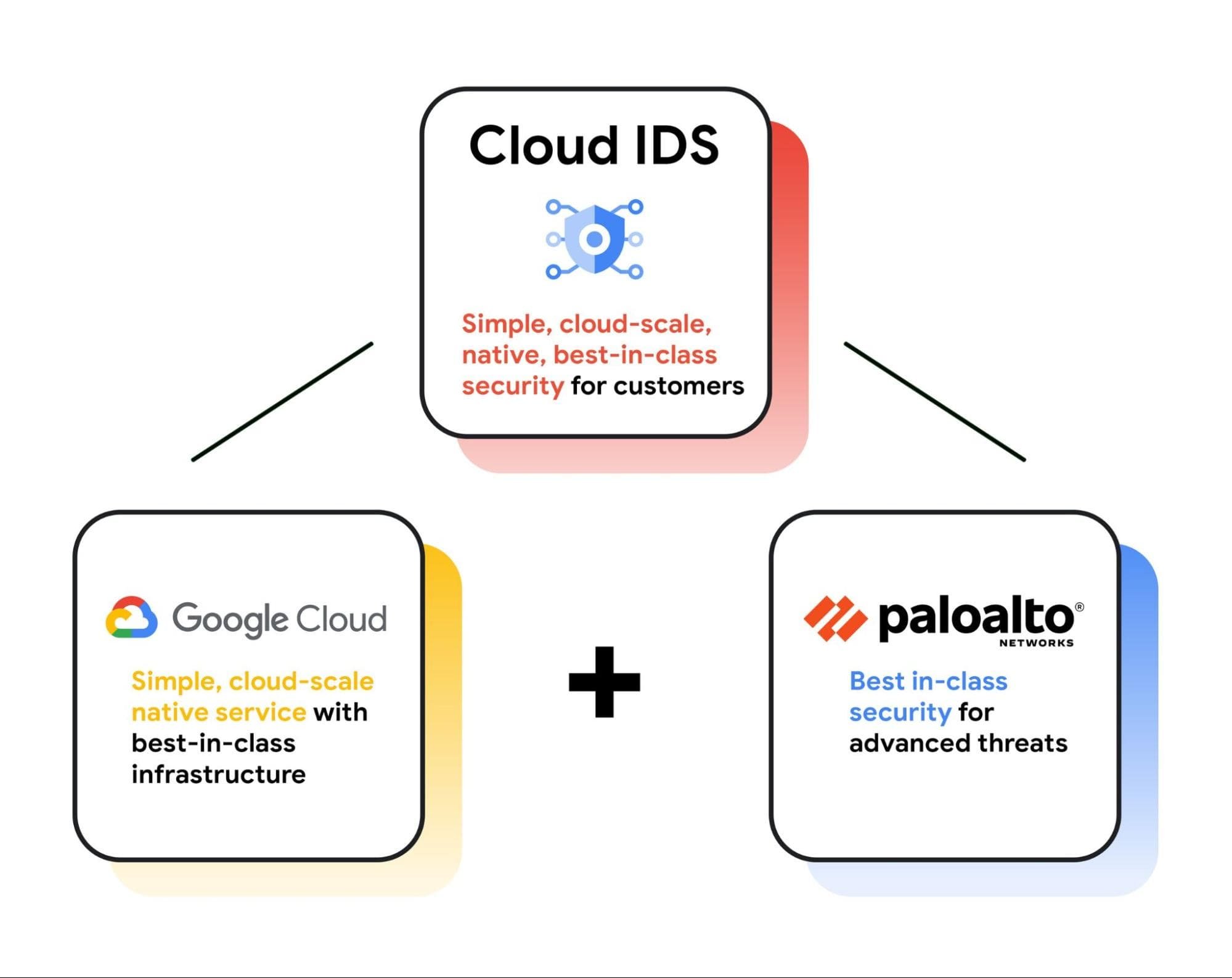
Better together: delivering best-in-class security
Detect and prioritize the most critical network threats
Cloud IDS provides broad visibility into traffic coming into your cloud environment, between GCE workloads, between GKE workloads, or between GCE and GKE workloads. This helps you satisfy your security posture and compliance goals while detecting malware, spyware, command-and-control (C2) attacks, and other network-based threats. It also detects exploits and evasion attempts at both the network and application layers.
Even with all of these advanced intrusion detection capabilities built into Cloud IDS, you can avoid detection notification noise drowning out the most important alerts because Cloud IDS provides a prioritized list of threats based on severity that help you to address the most important network threats first.
Investigate, correlate, and respond to threats
To respond to the network threats that Cloud IDS detects, you can create custom workflows within Google Cloud to take remediation action based on alerts. You can also leverage the data that Cloud IDS generates to investigate and correlate threats in your SIEM (Security Information and Event Management) and respond to them with your SOAR (Security Orchestration and Automated Response). Cloud IDS can be used with our security partners’ SIEM and SOAR solutions so that you can get additional visibility into network threats, security analytics on Cloud IDS’s alerts, and can set up automated threat responses based on Cloud IDS’s alerts. At public preview, Cloud IDS integrates with Splunk Cloud Platform, Splunk Enterprise Platform, Exabeam Advanced Analytics, The Devo Platform, and Palo Alto Networks Cortex XSOAR. And soon, Cloud IDS will integrate with Google Cloud’s Chronicle and Security Command Center as well.
"As enterprises move applications and workloads in the cloud, security teams want to replicate their on-premises network security stack in the cloud. Google Cloud IDS provides network threat detection as a service, helping enterprises mature their security programs and align on-premises security with a cloud-native implementation. This is why Google created Cloud IDS, built with Palo Alto Networks, to provide customers with a simple and powerful network security offering that can span a hybrid IT infrastructure." - Jon Oltsik, Senior Principal Analyst and Fellow, Enterprise Strategy Group (ESG)
You can learn more about Cloud IDS and sign up for access on the Cloud IDS webpage, and you can learn more about the other security innovations we’re unveiling at the Security Summit.



