Chrome Insider: Protecting enterprise credentials with Password Alert
Fletcher Oliver
Chrome Enterprise Customer Engineer
Learn more about Chrome Enterprise Core
Powerful and flexible management capabilities both in the cloud and on premises, at no additional cost.
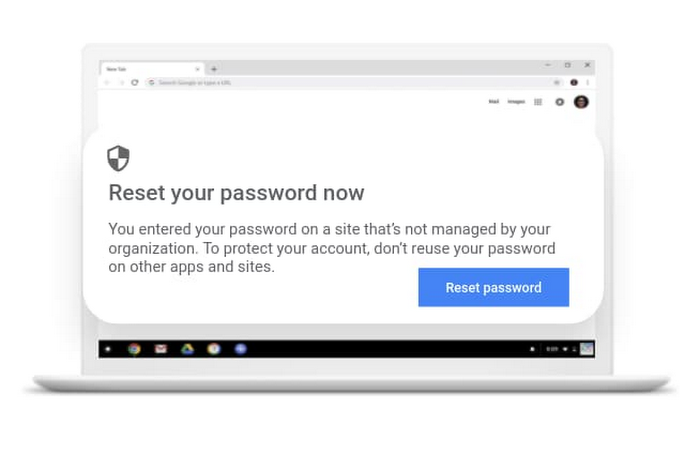
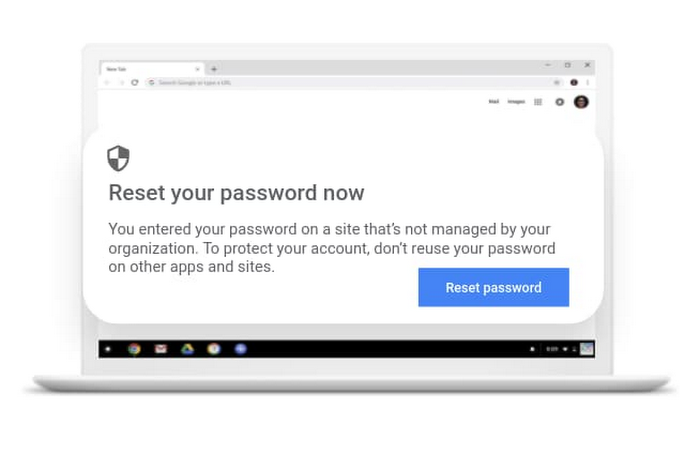
Learn moreProtecting users and data is a big job for organizations, especially as attackers continue to attempt to access enterprise credentials and gain control of corporate machines. Google has been working hard to help protect corporate passwords with features like Password Checkup and a variety of other Chrome functionalities. There’s another free feature in Chrome Browser that can help enterprises: Password Alert.
Password Alert helps enterprises:
Avoid phishing attacks by detecting when an employee enters their corporate credentials into a known phishing or suspicious site
Prevent reuse of corporate passwords on non-corporate sites
If suspicious activity is detected, Password Alert warns the user and asks them to reset their corporate password. This functionality is not specific to Google credentials; it can protect non-Google credentials, too.
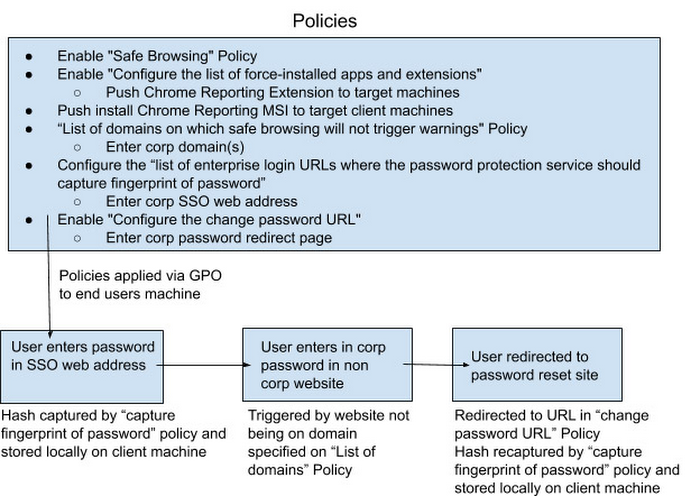
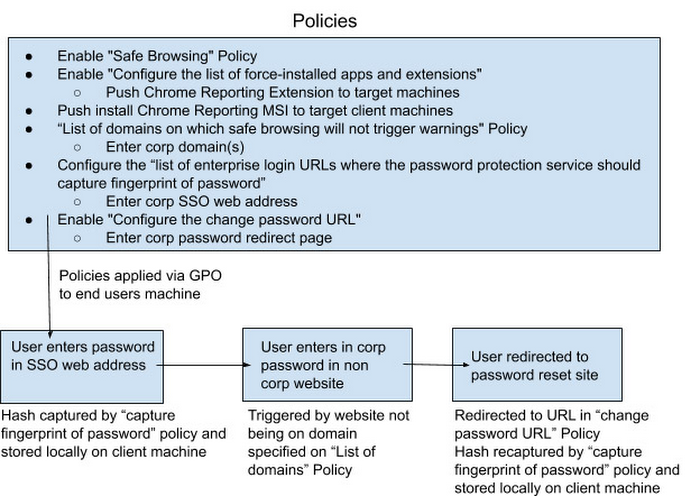
An encrypted hash of the password is captured and stored on the local machine. When the user enters their corporate password on a non-corporate site, it prompts the user to reset their password.
What information is stored
Data is stored locally on the client’s machine in a secure manner, so no data is sent to Google's servers.
Only the following information is stored, locally:
A salted, 37-bit partial hash of the password (the password fingerprint)
The length of the password
The date and time that the password was last successfully used
The corporate account email address
When Password Alert is triggered, the following data is optionally logged to local disk, if the Chrome Browser Enterprise Reporting extension is installed:
The corporate account user name
The URL of the offending page
The date and time of the alert
A flag indicating if the site was classified as a phishing site by Google Safe Browsing
Password Alert can be configured in two modes:
Passive Monitoring Mode: Admins can turn on Password Alert in passive monitoring or dry-run mode to log password reuse events onto the local filesystem or Windows Event Logger without showing warnings to the end user. This is useful for understanding the existing password reuse behavior inside your enterprise.
Active Detection Mode: When turned on in the Active Detection Mode, Password Alert will show warnings to the user when they reuse their corp credentials on non-whitelisted or phishing websites. The events will also be logged in the local filesystem or Windows Event Logger.
Here is how you can set this up in GPO today:
Check out this video that walks you through enabling Password Alert:
For some additional resources to help you get started, you can check out step-by-step instructions in this Help Center article on Controlling Password Reuse, and read this FAQ about Password Alert.