Coletar dados do Microsoft Windows Sysmon
Este documento:
- descreve a arquitetura de implantação e as etapas de instalação, além de qualquer configuração necessária que produza registros aceitos pelo analisador do Chronicle para eventos Sysmon do Microsoft Windows. Para ter uma visão geral da ingestão de dados do Chronicle, consulte Ingestão de dados no Chronicle.
- inclui informações sobre como o analisador mapeia campos do registro original para os campos do Chronicle Unified Data Model.
As informações neste documento se aplicam ao analisador com o rótulo de ingestão WINDOWS_SYSMON. O rótulo de ingestão identifica qual analisador normaliza os dados de registro brutos para o formato UDM estruturado.
Antes de começar
Revise a arquitetura de implantação recomendada
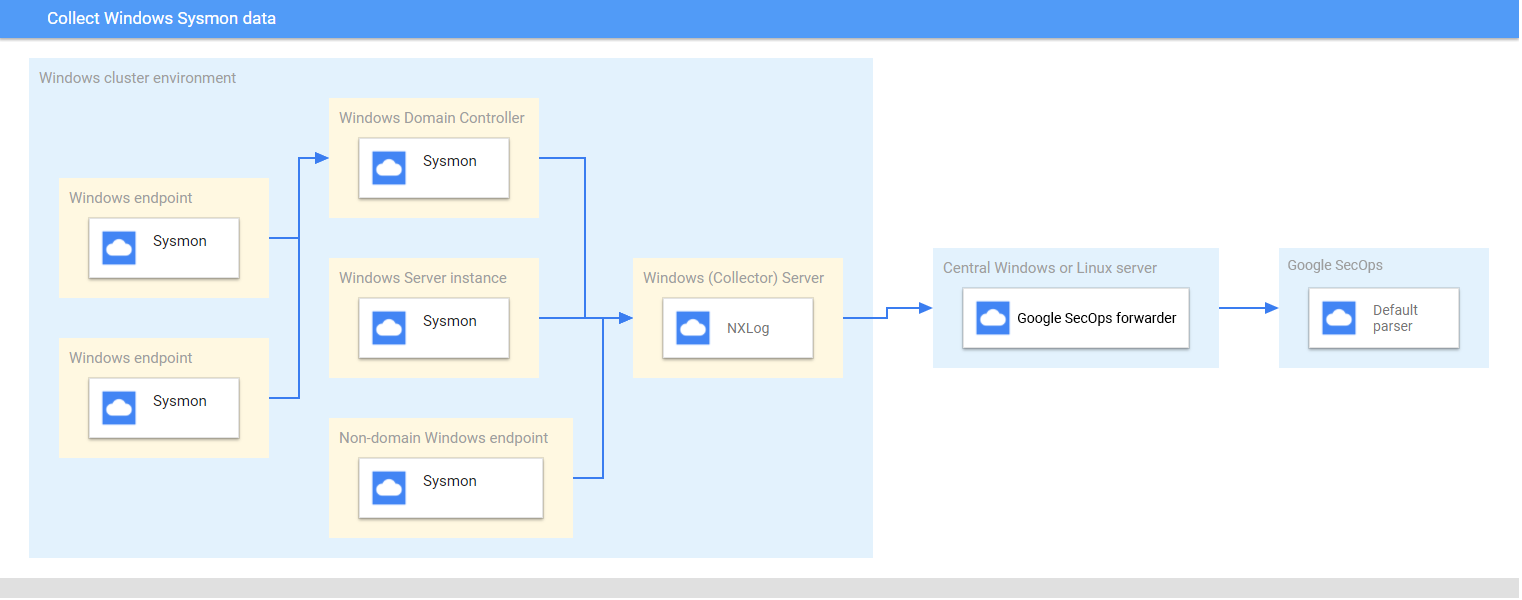
Este diagrama representa os principais componentes recomendados em uma arquitetura de implantação para coletar e enviar dados do Microsoft Windows Sysmon para o Chronicle. Compare essas informações com seu ambiente para ter certeza de que esses componentes estão instalados. Cada implantação de cliente será diferente dessa representação e pode ser mais complexa. Os seguintes itens são obrigatórios:
- Os sistemas na arquitetura de implantação são configurados com o fuso horário UTC.
- O Sysmon é instalado em servidores, endpoints e controladores de domínio.
- O Microsoft Windows Server do coletor recebe registros de servidores, endpoints e controladores de domínio.
Os sistemas Microsoft Windows na arquitetura de implantação usam:
- Assinaturas iniciadas pela origem para coletar eventos em vários dispositivos.
- Serviço WinRM para gerenciamento remoto do sistema.
O NXLog é instalado no servidor da janela do coletor para encaminhar registros ao encaminhador do Chronicle.
O encaminhador Chronicle é instalado em um servidor Microsoft Windows central ou em um servidor Linux.
Confira os dispositivos e versões compatíveis
O analisador do Chronicle oferece suporte aos registros gerados pelas seguintes versões do servidor do Microsoft Windows. O Microsoft Windows Server é lançado com as seguintes edições: Foundation, Essentials, Standard e Datacenter. O esquema de eventos dos registros gerados por cada edição não é diferente.
- Microsoft Windows Server 2019
- Microsoft Windows Server 2016
- Microsoft Windows Server 2012
O analisador Chronicle oferece suporte aos registros gerados por:
- Microsoft Windows 7 e sistemas de clientes superiores
- Sysmon versão 13.24.
O analisador do Chronicle oferece suporte aos registros coletados pela NXLog Community ou Enterprise Edition.
Revisar os tipos de registro compatíveis
O analisador do Chronicle oferece suporte aos tipos de registro abaixo gerados pelo Microsoft Windows Sysmon. Para mais informações sobre esses tipos de registro, consulte a documentação do Microsoft Windows Sysmon. Ele oferece suporte a registros gerados com texto em inglês, mas não é compatível com registros gerados em idiomas diferentes do inglês.
| Tipo de registro | Descrição |
|---|---|
| Registros Sysmon | O canal Sysmon contém 27 IDs de eventos. (ID do evento: 1 a 26 e 255). Para ver uma descrição desse tipo de registro, consulte a documentação de eventos Sysmon do Microsoft Windows (em inglês). |
Configurar servidores, endpoints e controladores de domínio do Microsoft Windows
- Instalar e configurar os servidores, os endpoints e os controladores de domínio. Para mais informações, consulte a documentação de Configuração do Sysmon do Microsoft Windows.
- Configure um coletor do Microsoft Windows Server para analisar os registros coletados de vários sistemas.
- Configurar o servidor Microsoft Windows ou Linux central
- Configurar todos os sistemas com o fuso horário UTC.
- Configure os dispositivos para encaminhar registros para o coletor do Microsoft Windows Server.
- Configure assinaturas iniciadas por origem nos sistemas Microsoft Windows. Para mais informações, consulte Como configurar uma assinatura iniciada por origem.
- Ative o WinRM em servidores e clientes Microsoft Windows. Para mais informações, consulte Instalação e configuração do Gerenciamento Remoto do Microsoft Windows.
Configurar o NXLog e o encaminhador do Chronicle
- Instale o NXLog no Microsoft Windows Server do coletor. Siga a documentação do NXLog, incluindo informações sobre como configurar o NXLog para coletar registros do Sysmon.
Crie um arquivo de configuração para o NXLog. Use o módulo de entrada im_msvistalog. Confira um exemplo de configuração do NXLog. Substitua os valores
<hostname>e<port>pelas informações sobre o servidor Microsoft Windows ou Linux central de destino. Para mais informações, consulte a documentação do NXLog sobre o módulo om_tcp (link em inglês).define ROOT C:\Program Files (x86)\nxlog define SYSMON_OUTPUT_DESTINATION_ADDRESS <hostname> define SYSMON_OUTPUT_DESTINATION_PORT <port> define CERTDIR %ROOT%\cert define CONFDIR %ROOT%\conf define LOGDIR %ROOT%\data define LOGFILE %LOGDIR%\nxlog.log LogFile %LOGFILE% Moduledir %ROOT%\modules CacheDir %ROOT%\data Pidfile %ROOT%\data\nxlog.pid SpoolDir %ROOT%\data <Extension _json> Module xm_json </Extension> <Input windows_sysmon_eventlog> Module im_msvistalog <QueryXML> <QueryList> <Query Id="0"> <Select Path="Microsoft-Windows-Sysmon/Operational">*</Select> </Query> </QueryList> </QueryXML> ReadFromLast False SavePos False </Input> <Output out_chronicle_sysmon> Module om_tcp Host %SYSMON_OUTPUT_DESTINATION_ADDRESS% Port %SYSMON_OUTPUT_DESTINATION_PORT% Exec $EventTime = integer($EventTime) / 1000; Exec $EventReceivedTime = integer($EventReceivedTime) / 1000; Exec to_json(); </Output> <Route r2> Path windows_sysmon_eventlog => out_chronicle_sysmon </Route>Instale o encaminhador Chronicle no servidor Microsoft Windows ou Linux central. Para mais informações sobre como instalar e configurar o encaminhador no Linux, consulte Como instalar e configurar o encaminhador no Linux ou Como instalar e configurar o encaminhador no Microsoft Windows.
Configurar o encaminhador do Chronicle para enviar registros ao Chronicle. Confira um exemplo de configuração de encaminhador.
- syslog: common: enabled: true data_type: WINDOWS_SYSMON Data_hint: batch_n_seconds: 10 batch_n_bytes: 1048576 tcp_address: 0.0.0.0:10518 connection_timeout_sec: 60Inicie o serviço NXLog.
Referência de mapeamento de campo: campos de evento do dispositivo para campos de UDM
Esta seção descreve como o analisador mapeia campos de registro originais do dispositivo para campos do Unified Data Model (UDM). O mapeamento de campo pode variar de acordo com o ID do evento.
Campos comuns
| Campo NXLog | Campo UDM |
|---|---|
| UtcTime | metadata.event_timestamp |
| Categoria | security_result.summary e metadata.product_event_type |
| AccountName | principal.user.userid |
| Domínio | principal.administrative_domain |
| RecordNumber | metadata.product_log_id |
| HostName | principal.hostname |
| UserID | principal.user.windows_sid |
| SeverityValue | security_result.severity |
| ProcessID | observer.process.pid |
| ProviderGuid | observer.asset_id |
| LogonId | principal.network.session_id |
| ThreadID | additional.fields.key definido como thread_id e
valor armazenado em additional.fields.value.string_value |
| Canal | additional.fields.key definido como channel e
valor armazenado em additional.fields.value.string_value |
| EventID | security_result.rule_name definido como EventID: <EventID>metadata.product_event_type definido como <Category> [<EventID>] |
ID do evento: 1
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to PROCESS_LAUNCH |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | target.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | target.process.pid |
| IntegrityLevel | The value for the field target.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | target.process.file.full_path |
| Description | metadata.description |
| CommandLine | target.process.command_line |
| CurrentDirectory | additional.fields.key set to current_directory and
value stored in additional.fields.value.string_value |
| User | Domain stored in principal.administrative_domainUsername stored in principal.user.userid |
| Hashes | Based on Hash algorithm.
|
| ParentProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ParentProcessGuid> |
| ParentProcessId | principal.process.pid |
| ParentImage | principal.process.file.full_path |
| ParentCommandLine | principal.process.command_line |
ID do evento: 2
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to FILE_MODIFICATION |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | principal.process.file.full_path |
| TargetFilename | target.file.full_path |
| CreationUtcTime | target.resource.attribute.labels.key set to CreationUtcTime and value
stored in target.resource.attribute.labels.value |
| PreviousCreationUtcTime | target.resource.attribute.labels.key set to PreviousCreationUtcTime and
value stored in target.resource.attribute.labels.value |
ID do evento: 3
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to NETWORK_CONNECTIONsecurity_result.action set to ALLOWnetwork.direction set to OUTBOUND |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | principal.process.file.full_path |
| User | Domain stored in principal.administrative_domainUsername stored in principal.user.userid |
| Protocol | network.ip_protocol |
| SourceIp | principal.ip |
| SourcePort | principal.port |
| DestinationIp | target.ip |
| DestinationHostname | target.hostname |
| DestinationPort | target.port |
ID do evento: 4
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to SETTING_MODIFICATIONtarget.resource.resource_type set to SETTINGtarget.resource.resource_subtype set to State |
|
| UtcTime | metadata.event_timestamp |
| State | target.resource.name |
| Version | metadata.product_version |
ID do evento: 5
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to PROCESS_TERMINATION |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | target.process.pid |
| IntegrityLevel | The value for the field target.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | target.process.file.full_path |
ID do evento: 6
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to PROCESS_MODULE_LOAD |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ImageLoaded | principal.process.file.full_path |
| Hashes | The field populated is determined by the Hash algorithm.
|
| Signed | target.resource.attribute.labels.key set to Signed and value set to
target.resource.attribute.labels.value |
| Signature | target.resource.attribute.labels.key set to Signature and value stored in
target.resource.attribute.labels.value |
| SignatureStatus | target.resource.attribute.labels.key set to SignatureStatus and value
stored in target.resource.attribute.labels.value |
ID do evento: 7
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to PROCESS_MODULE_LOAD |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | principal.process.file.full_path |
| ImageLoaded | target.process.file.full_path |
| Description | metadata.description |
| Hashes | The field populated is determined by the Hash algorithm.
|
| Signed | target.resource.attribute.labels.key set to Signed and value stored in
target.resource.attribute.labels.value |
| Signature | target.resource.attribute.labels.key set to Signature Signature value in target.resource.attribute.labels.value |
| SignatureStatus | target.resource.attribute.labels.key set to SignatureStatus and value
stored in target.resource.attribute.labels.value |
ID do evento: 8
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to PROCESS_MODULE_LOAD |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| SourceProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<SourceProcessGuid> |
| SourceProcessId | principal.process.pid |
| SourceImage | principal.process.file.full_path |
| TargetProcessGuid | target.process.product_specific_process_id set to
SYSMON:<TargetProcessGuid> |
| TargetProcessId | target.process.pid |
| TargetImage | target.process.file.full_path |
ID do evento: 9
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to FILE_READ
If the |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | principal.process.file.full_path |
| Device | target.file.full_path |
ID do evento: 10
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to PROCESS_OPENtarget.resource.resource_subtype set to GrantedAccess |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| SourceProcessGUID | principal.process.product_specific_process_id set to
SYSMON:<SourceProcessGUID> |
| SourceProcessId | principal.process.pid |
| SourceImage | principal.process.file.full_path |
| TargetProcessGUID | target.process.product_specific_process_id set to
SYSMON:<TargetProcessGUID> |
| TargetProcessId | target.process.pid |
| TargetImage | target.process.file.full_path |
| GrantedAccess | target.resource.name |
ID do evento: 11
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to FILE_CREATIONtarget.resource.resource_subtype set to CreationUtcTime |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | principal.process.file.full_path |
| TargetFilename | target.file.full_path |
| CreationUtcTime | target.resource.name |
ID do evento: 12
| Campo NXLog | Campo UDM |
|---|---|
If the Message the field contains CreateKey|CreateValue, then
metadata.event_type set to REGISTRY_CREATIONIf the Message field contains DeleteKey|DeleteValue, thenmetadata.event_type set to REGISTRY_DELETIONOtherwise, metadata.event_type set to REGISTRY_MODIFICATION |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | principal.process.file.full_path |
| TargetObject | target.registry.registry_key |
ID do evento: 13
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to REGISTRY_MODIFICATION |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | principal.process.file.full_path |
| TargetObject | target.registry.registry_key |
| Details | target.registry.registry_value_data |
ID do evento: 14
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to REGISTRY_MODIFICATION |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | principal.process.file.full_path |
| TargetObject | src.registry.registry_key |
| NewName | target.registry.registry_key |
ID do evento: 15
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to FILE_CREATION |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | principal.process.file.full_path |
| TargetFilename | target.file.full_path |
| CreationUtcTime | target.resource.attribute.labels.key set to CreationUtcTime and value
stored in target.resource.attribute.labels.value |
| Hash | The field populated is determined by the Hash algorithm.
|
ID do evento: 16
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to SETTING_MODIFICATION |
|
| UtcTime | metadata.event_timestamp |
| ProcessID | target.process.pid |
| Configuration | The value is stored in target.process.command_line when this field value
contains any command line or processThe value is stored in target.process.file.full_path when this field value
contains the configuration file path. |
| ConfigurationFileHash | The field populated is determined by the Hash algorithm.
|
ID do evento: 17
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to PROCESS_UNCATEGORIZEDtarget.resource.resource_type set to PIPE |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | target.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | target.process.pid |
| IntegrityLevel | The value for the field target.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| PipeName | target.resource.name |
| Image | target.process.file.full_path |
ID do evento: 18
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to PROCESS_UNCATEGORIZEDtarget.resource.resource_type set to PIPE |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | target.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | target.process.pid |
| IntegrityLevel | The value for the field target.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| PipeName | target.resource.name |
| Image | target.process.file.full_path |
ID do evento: 19
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to USER_RESOURCE_ACCESS |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| Operation | |
| User | The Domain is stored in principal.administrative_domainThe Username is stored in principal.user.userid |
| EventNamespace | target.file.full_path |
| Name | target.application |
| Query | target.resource.name |
ID do evento: 20
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to USER_RESOURCE_ACCESS |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| Operation | target.resource.attribute.labels.key set to Operation and the value is
stored in target.resource.attribute.labels.value |
| User | The domain is stored in principal.administrative_domainThe Username is stored in principal.user.userid |
| Name | target.resource.attribute.labels.key set to Name Name value in target.resource.attribute.labels.value |
| Type | target.resource.attribute.labels.key set to Type and the value is stored
in target.resource.attribute.labels.value |
| Destination | target.resource.name |
ID do evento: 21
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to USER_RESOURCE_ACCESS |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| Operation | target.resource.attribute.labels.key set to Operation and the value is
stored in target.resource.attribute.labels.value |
| User | The domain is stored in principal.administrative_domainThe username is stored in principal.user.userid |
| Consumer | target.resource.attribute.labels.key set to Consumer and the value is
stored in target.resource.attribute.labels.value |
| Filter | target.resource.name |
ID do evento: 22
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to NETWORK_DNSnetwork.application_protocol set to DNS |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| QueryName | network.dns.questions |
| QueryStatus | Stored in security_result.summary as Query Status: <QueryStatus> |
| QueryResults | Type is saved to network.dns.answers.type with values separated by a
semicolon (;)Data is saved to network.dns.answers.data Values that do not have type are mapped to network.dns.answers.data. |
| Image | principal.process.file.full_path |
ID do evento: 23
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to FILE_DELETION |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| User | Domain stored into principal.administrative_domainUsername stored in principal.user.userid |
| Image | principal.process.file.full_path |
| TargetFilename | target.file.full_path |
| Hashes | The field populated is determined by the Hash algorithm.
|
| IsExecutable | Field target.resource.attribute.labels.key set to IsExecutable and the
value is stored in target.resource.attribute.labels.value |
| Archived | target.resource.attribute.labels.key set to Archived and the value is
stored in target.resource.attribute.labels.value |
ID do evento: 24
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to RESOURCE_READ |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | target.process.product_specific_process_id set to
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | target.process.file.full_path target.resource.name |
| ClientInfo | ip stored in target.iphostname stored in target.hostnameuser stored in principal.user.userid |
| Hashes | The field populated is determined by the Hash algorithm.
|
| Archived | target.resource.attribute.labels.key set to Archived and value stored in
target.resource.attribute.labels.value |
ID do evento: 25
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to PROCESS_LAUNCH |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | target.process.product_specific_process_id stored as
SYSMON:<ProcessGuid> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| Image | target.process.file.full_path |
ID do evento: 26
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to FILE_DELETION |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id set to
SYSMON:<%{ProcessGuid}> |
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| User | Domain set to principal.administrative_domainUsername set to principal.user.userid |
| Image | principal.process.file.full_path |
| TargetFilename | target.file.full_path |
| Hashes | Based on Hash algorithm. MD5 set to target.process.file.md5SHA256 set to target.process.file.sha256SHA1 set to target.process.file.sha1 |
| IsExecutable | target.resource.attribute.labels.key set to IsExecutable & value in
target.resource.attribute.labels.value |
ID do evento: 29
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to FILE_CREATION |
|
| RuleName | security_result.rule_name |
| UtcTime | metadata.event_timestamp |
| ProcessGuid | principal.process.product_specific_process_id is set to
SYSMON:<PROCESS_GUID>
PROCESS_GUID is the ProcessGuid. The ProcessGuid field is a unique value for this process across a domain to make event correlation easier.
|
| ProcessId | principal.process.pid |
| IntegrityLevel | The value for the field principal.process.integrity_level_rid
is determined based on the value of the field IntegrityLevel as follows:
|
| User | Domain is set to principal.administrative_domainUsername is set to principal.user.userid |
| Image | principal.process.file.full_path |
| TargetFilename | target.file.full_path |
| Hashes | Based on the hash algorithm, the following values are set:
|
ID do evento: 255
| Campo NXLog | Campo UDM |
|---|---|
metadata.event_type set to SERVICE_UNSPECIFIEDmetadata.product_event_type set to Error - [255]target.application set to Microsoft Sysmon |
|
| UtcTime | metadata.event_timestamp |
| ID | security_result.summary |
| Description | security_result.description |
