Protecting Cloud Storage with WORM, key management and more updates
Subhasish Chakraborty
Group Product Manager
Make it reliable, access it fast, keep it safe: That’s what we’re working on in Google Cloud Storage. The availability, performance and security of your storage infrastructure are key to building reliable applications that help keep your users happy and your data safe. We just announced new capabilities for improving the reliability and performance of your data, and we’re now happy to bring some updates for storage security as well. We’ve recently rolled out key features in Cloud Storage for the security and privacy of your data and compliance with financial services regulations. Here are a few reminders of what’s new, and a new announcement, related to keeping data safe and compliant in Cloud Storage:
Cloud Storage Bucket Lock is now generally available
Recent UI changes improve privacy management
Cloud KMS integration with Cloud Storage
Access Transparency for Cloud Storage and Persistent Disk
Retain data and prevent modification with Cloud Storage Bucket Lock
We’re excited to announce the general availability of Cloud Storage Bucket Lock, which enables you to prevent the deletion or modification of content for a period of time that you specify. This will be especially useful to those of you who need WORM (Write Once Read Many)-compliant or immutable storage.
Many organizations have compliance, legal and regulatory requirements for retaining data for specific lengths of time. These requirements may be based on your industry, or might be triggered by audits or investigations. To help you meet these requirements, Bucket Lock provides retention lock capabilities as well as temporary and event holds for content.
Cloud Storage Bucket Lock works with the following constructs:
A retention policy defines the retention period for current and future objects in the bucket. It means objects cannot be deleted or overwritten until they reach the age you define in the retention policy.
The retention period defines how long an object is retained; the object is unmodifiable until the retention period is up.
Retention expiration time metadata tells you when a particular object’s retention period is up.
A lock on a bucket prevents reducing the retention period for objects in that bucket.
A hold on an object retains the object indefinitely.
So, for example, an administrator can specify a retention policy for their bucket with a set retention period and can lock the policy for compliance purposes. Once the retention policy is locked, the retention period cannot be reduced. A temporary hold can be placed on objects when a company is audited or investigated. An event hold allows you to set retention policies to get triggered after the completion of an event. For example, a financial services company can place a six-year retention policy on loan documents to go into effect after a loan is paid off.
Bucket Lock is integrated into the Cloud Storage console, our APIs and gsutil, and it takes just a few steps to set up a retention policy for a bucket and store some data, as you can see here:
Once expired or unneeded, it’s simple to remove a policy, as shown here:


Bucket Lock works with all tiers of Cloud Storage. You can use the same storage setup for both primary and archive data. You can also use object lifecycle management to automatically move locked data into colder storage tiers and delete data once the retention period expires.
Here are a few of the most common uses we’ve seen for Bucket Lock:
Financial records compliance. Common regulations for those in banking and finance include SEC Rule 17a-4 (f), CFTC Rule 1.31 (b)-(c), FINRA Rule 4511(c), and CFR 1.31 section 3. All of these regulations require that you retain certain information for a designated time period.
Healthcare records retention. These records are subject to industry regulations and timelines for retention and deletion.
Media content archives. Content creators such as publishing houses, media studios, film and photography producers want to protect original content in its original form. You can store content in Cloud Storage and use Bucket Lock to prevent any modifications.
General archives. Use Bucket Lock for any data that you need to ensure is retained and unmodified.
Bucket Lock is free for all Cloud Storage users. Bucket Lock has been assessed by records and governance expert Cohasset Associates, which validated it for the SEC, CFTC and FINRA regulations listed above. Learn more about Bucket Lock from the documentation here.
Get better control over public storage buckets and objects
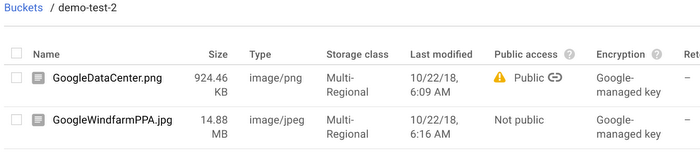
New UI features in the Cloud Storage console provide you with secure mechanisms for sharing your data, and better oversight over which data is public. You can see which buckets and objects are public across your Cloud Storage environment, shown here:
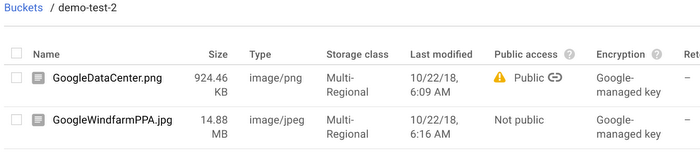
If you’re already a Cloud Storage user, you might notice the public sharing option in the UI has been replaced with an Identity and Access Management (IAM) panel. This helps prevent a mouse click-slip that publicly shares your objects. It’s still simple to make an object public using the new panel, as you can see here.
These UI elements make it clear for administrators which content is publicly available, and introduces a deliberate process for users to share their content.
Go straight to your Cloud Storage console here.
Use Cloud KMS keys with Cloud Storage data
You now have sophisticated encryption key management capabilities with Cloud Key Management System (KMS) keys protecting your Cloud Storage data through a new integration. The Cloud Storage–KMS integration allows you to manage and control encryption keys for your Cloud Storage datasets. This means managing active keys, authorizing users or applications to use certain keys, monitoring key use, and rotating and revoking keys as needed.
This KMS integration provides several features to Cloud Storage users: key rotation, revocation and deletion. Rotating your key is when a new key version is generated and selected as the primary key in operation. Revoking a key means temporarily removing a key or access to a key. These can be reinstated, and data or metadata access will be restored, but often you’ll revoke a key prior to deleting a key.
Learn more about Cloud KMS integration.
Use Access Transparency for Cloud Storage and Persistent Disk
Access Transparency (AXT) shows you who, when, where and why Google support or engineering has accessed your Cloud Storage and Persistent Disk environment. Example actions logged by AXT could include Google support actions you’ve requested, engineering actions investigating your support requests, or a Google Site Reliability Engineer (SRE) helping your team recover from an issue. You can also monitor logs related to Cloud Storage actions programmatically through Stackdriver APIs and use Cloud Storage to archive your logs if required for future auditing. This comprehensive logging gives complete visibility into administrative actions for monitoring and compliance purposes, not to mention the peace of mind it brings.
These Cloud Storage improvements can help you add more security and control of your cloud resources. Learn more about Cloud Storage here.