Democratizing Zero Trust with an expanded BeyondCorp Alliance
Sampath Srinivas
Director, Product Management
The need to quickly provide secure access for a newly remote workforce during the early days of COVID-19 drove many organizations to explore new technologies and start down a path towards a Zero Trust model. As time has passed, it’s become clear that remote work will be a defining characteristic of the new normal, and modernizing security by fully embracing zero trust models is an imperative, not an option. We need to work to further democratize this technology, accelerate and ease its adoption to help organizations stay secure, agile, and productive.
We’ve been working on Zero Trust for more than a decade at Google, and earlier this year, we introduced BeyondCorp Remote Access, our cloud-based solution that helps make access to internal applications easier and more secure. We offer similar context-aware access controls for apps in Google Workspace and Cloud Identity.
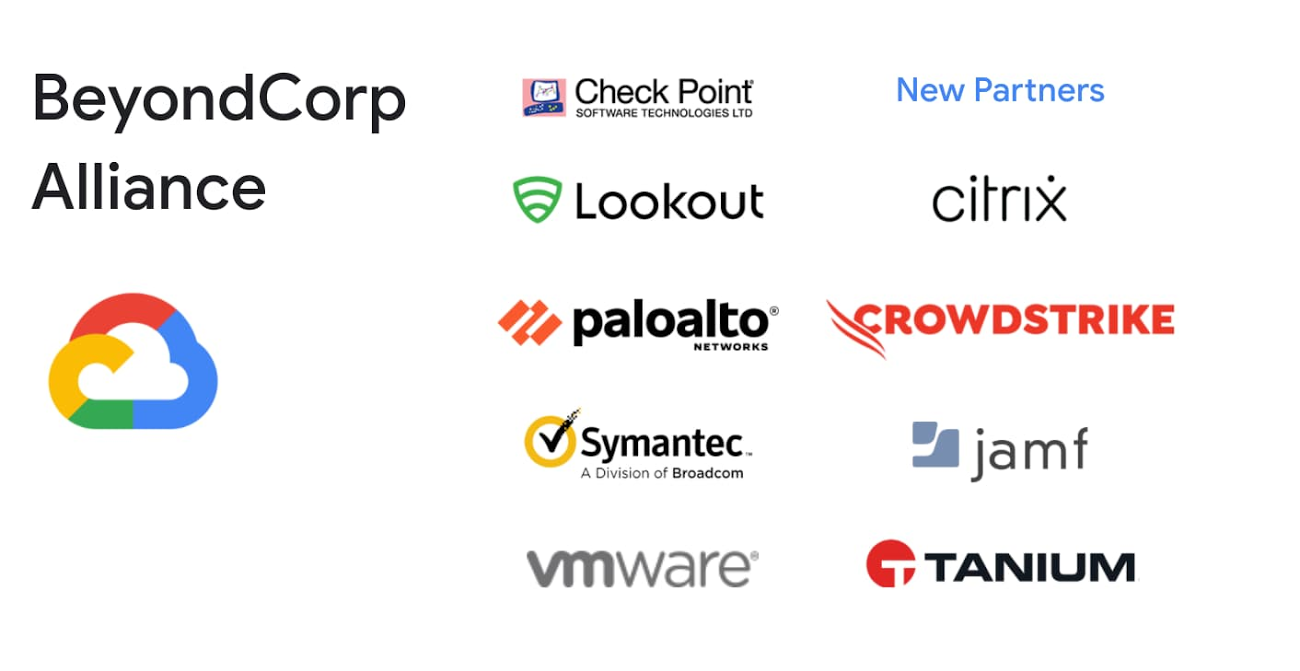
Last year, we assembled a group of partners that share our Zero Trust vision and who are committed to help our joint customers make it a reality: the BeyondCorp Alliance. These partners are key to our effort to further promote and democratize this technology. They allow customers to leverage existing controls to make adoption easier while adding key functionality and intelligence that enable customers to make better access decisions. We’re now pleased to announce that Citrix, CrowdStrike, Jamf, and Tanium are joining Check Point, Lookout, Palo Alto Networks, Symantec (a division of Broadcom), and VMware as BeyondCorp Alliance members.
As Sunil Potti, VP and GM Google Cloud Security, puts it, BeyondCorp delivers world-class security for the reimagined workplace. Partners who share our vision are an essential part of how we help our customers modernize their security approaches in-place to deliver a better, safer normal.
Our BeyondCorp Alliance Partners add capabilities in the following areas:
Device Management: Enterprise Mobility Management (EMM) vendors can provide device context and telemetry such as whether a device is managed or corporate-owned to aid in policy evaluation.
Endpoint Security: Endpoint Detection and Response Vendors (EDR) or Mobile Threat Defense (MTD) vendors can provide device posture information, such as whether a device is compromised to aid in policy evaluation.
Gateways: Infrastructure vendors can provide more secure access to hosted infrastructure (e.g., virtual desktops, etc.) via BeyondCorp.
Keep reading to learn more about updates to our existing BeyondCorp Alliance partnerships and new solutions with leading security partners that we are excited to announce today:
Check Point SandBlast Mobile is a mobile threat defense solution that detects and stops attacks on iOS and Android devices before they start. Integration with the Google Admin console can be used to selectively prevent compromised devices from accessing applications and resources, helping to keep sensitive data secure. The integration is now available to customers in preview in the Google Admin console.
Citrix and Google Cloud are extending our deep collaboration to include BeyondCorp. Google Cloud has always been one of the best places to run Citrix Workspace, and the first step, bringing together Citrix Workspace and BeyondCorp, is coming soon. It will allow customer applications, whether they are deployed on-premises, on GCP, or delivered as a service (SaaS), to be exposed through Citrix Workspace with BeyondCorp’s access controls and policy enforcement. Users get a single pane of glass for all of their applications, which can now be accessed from BYOD and non-corporate devices without the need for a VPN. We’re also exploring the sharing of endpoint signals and further extending policy enforcement to virtual desktops. For more information, check out the Citrix blog on our joint zero trust security solutions.
CrowdStrike will deliver real-time endpoint posture assessments from endpoints regardless of location, network, or user so that BeyondCorp adopters can prohibit access from untrusted or compromised hosts as part of conditional access policies, reducing risk for users and the organization. This integration is coming soon. To learn more about how CrowdStrike and Google Cloud are collaborating on Zero Trust, register for CrowdStrike’s Cybersecurity Conference Fal.Con 2020, taking place on October 15, 2020.
Jamf is working to extend its device compliance capabilities for organizations leveraging Google Cloud and BeyondCorp. In the past, organizations have expressed concerns about unprotected Mac devices accessing cloud and on-premises resources. Now, through a unique Jamf preview, customers can ensure that only trusted users, from managed devices, using approved apps, are accessing company data. Read Jamf’s blog on our collaboration and contact the Jamf team to learn more about this preview.
Lookout continuously assesses a smartphone, tablet or Chromebook’s risk level and provides it to Cloud Identity and BeyondCorp from the Lookout Security Graph. Device risk levels of “high, moderate or low” are set based on the organization’s security policies. When Lookout detects a threat on a mobile device, the risk level is changed accordingly and delivered in real-time to Cloud Identity via API. This integration enables Google Workspace to block risky or non-compliant devices from accessing applications and data. This functionality is now available in preview via the Google Admin console. Learn more by reading Lookout’s blog.
Symantec Endpoint Protection (SEP) and Symantec Endpoint Protection Mobile (SEP Mobile) report on the security posture of an organization’s traditional and mobile endpoints, including both managed and unmanaged devices. With the upcoming integration, customers can leverage Symantec’s endpoint signals such as indications of compromise, operating system configuration risks, app risks, anomalous network behavior, and more, to create more granular and customized access policies for Google Workspace, web apps, and Google Cloud infrastructure.
Tanium and Google Cloud recently announced a strategic partnership with the goal of delivering security transformation for the distributed IT era. As part of the BeyondCorp Alliance, Tanium will be providing device identity information through Tanium Endpoint Identity, which is available today. Tanium monitors and evaluates the health of endpoints in real-time, providing comprehensive visibility and control from a single platform no matter where the device is located. Through the combined solution, coming soon, organizations will be able to ensure that devices connecting to network resources and applications are authorized, secured, and up-to-date. To learn more about Tanium’s partnership with Google Cloud and BeyondCorp integration, register to attend their upcoming virtual user conference, Converge.
VMware is working to bring Workspace ONE and Google Cloud's BeyondCorp solution together to keep devices under control and compliant with policies that protect corporate data. Workspace ONE will continually feed device compliance status information to Google Cloud’s context-aware access engine, allowing access to be revoked at any time if a device becomes non-compliant. This integration is coming soon.
To learn more about how you can take advantage of our joint capabilities to advance your own Zero Trust strategy, visit the BeyondCorp Alliance partner links above or reach out to our team.
Also be sure to check out our BeyondCorp product home, browse BeyondCorp educational resources in our Security Best Practices Center, and view BeyondCorp use case videos in our Cloud Security Showcase.