Admin Insider: These 6 steps can help you address security threats in G Suite
Sam Lugani
Group Product Manager, Google
Recognize and help stop threats in their tracks using G Suite security tools.
Try Google Workspace at No Cost
Get a business email, all the storage you need, video conferencing, and more.
SIGN UPBusinesses are increasingly at risk of phishing and malware attacks, with email continuing to be one of the leading attack vectors. Because phishers are constantly changing their tactics, these threats can be hard to detect, and many times, admins don’t have the required controls in place to protect their organizations.
We believe that security solutions need to be three things in order to be effective: 1.) proactive, and have some default protections in place, 2.) intelligent, and adaptable to the ever-changing threat landscape, and 3.) simple to use, for both end users and admins. G Suite was designed with these principles in mind; we’ve built protections to help admins and users detect and remediate attacks. Here’s an example of how you can recognize and help stop threats in their tracks using G Suite security tools.
1. Recognize the problem.
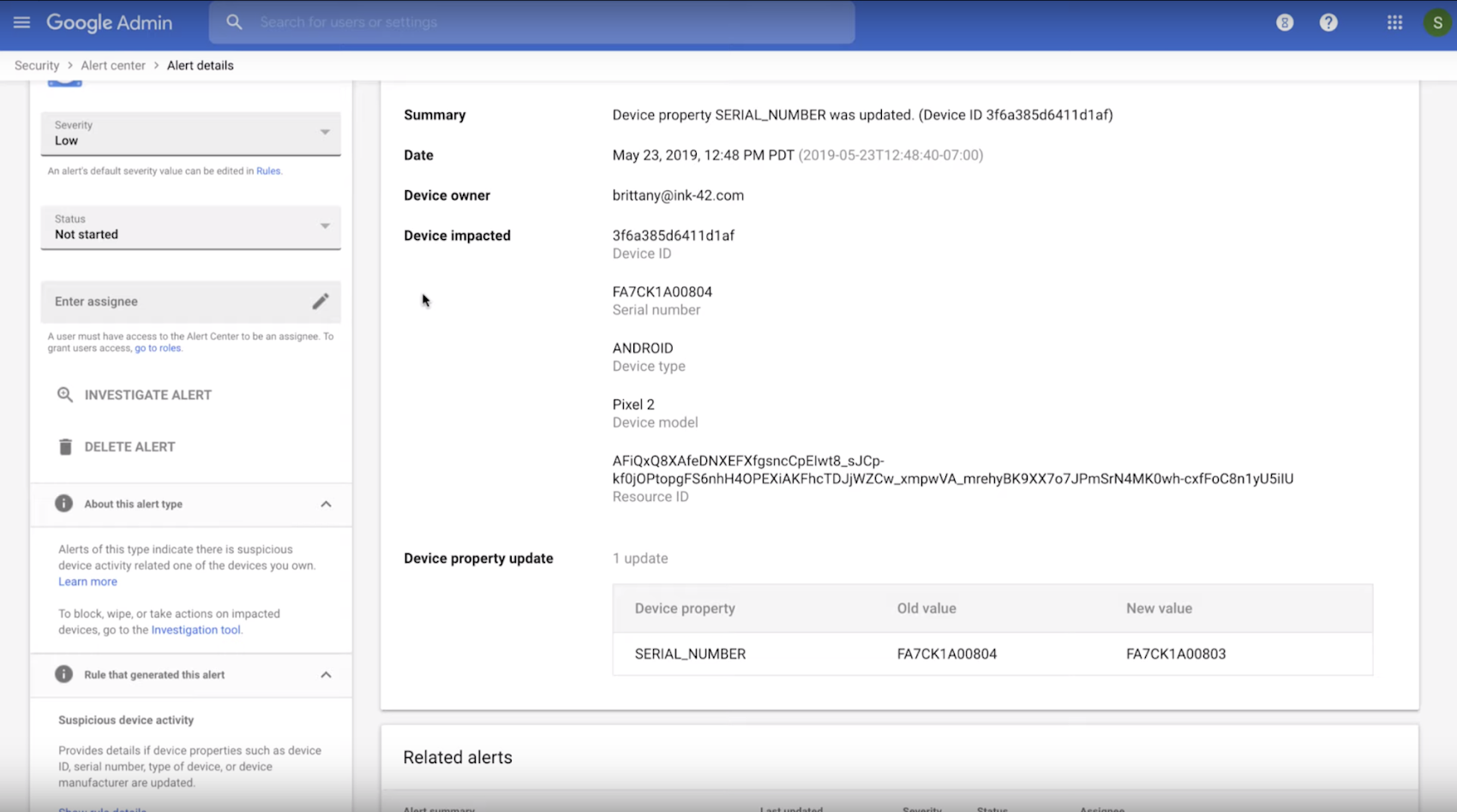
Managing a large organization isn’t easy. It’s not uncommon for IT admins to receive thousands of alerts each day! With this volume, it’s no surprise that almost half of these alerts are not investigated. It can be hard to separate the signal from the noise, which is where G Suite can help. The G Suite Alert Center provides admins with a single, comprehensive view of the most important security updates.
Within the alert center, admins can receive alerts and actionable insights about the latest security threats including phishing, malware, suspicious account, and suspicious device activity. For example, a suspicious device activity alert may include specifics like device ID and serial number. This lets the admin figure out that, say, a Pixel 2 owned by an employee has displayed some suspicious behavior.
2. Evaluate and take action right away.
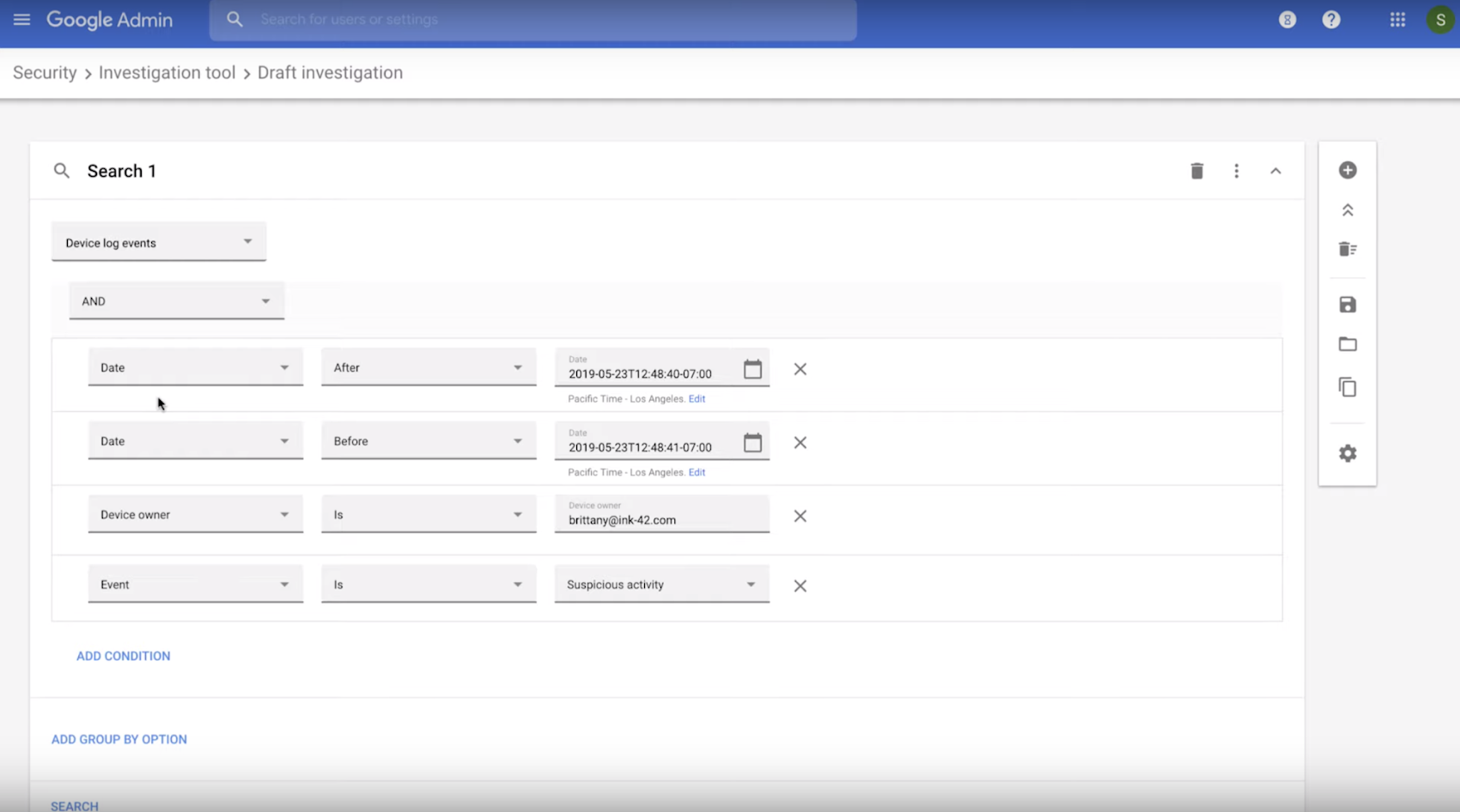
Security remediation workflows can be quite cumbersome. At the end of the day, security tools are only useful if you can easily deploy them—if they are difficult or complicated, they’re of limited use. In G Suite, the alert center and the security center workflows operate together seamlessly.
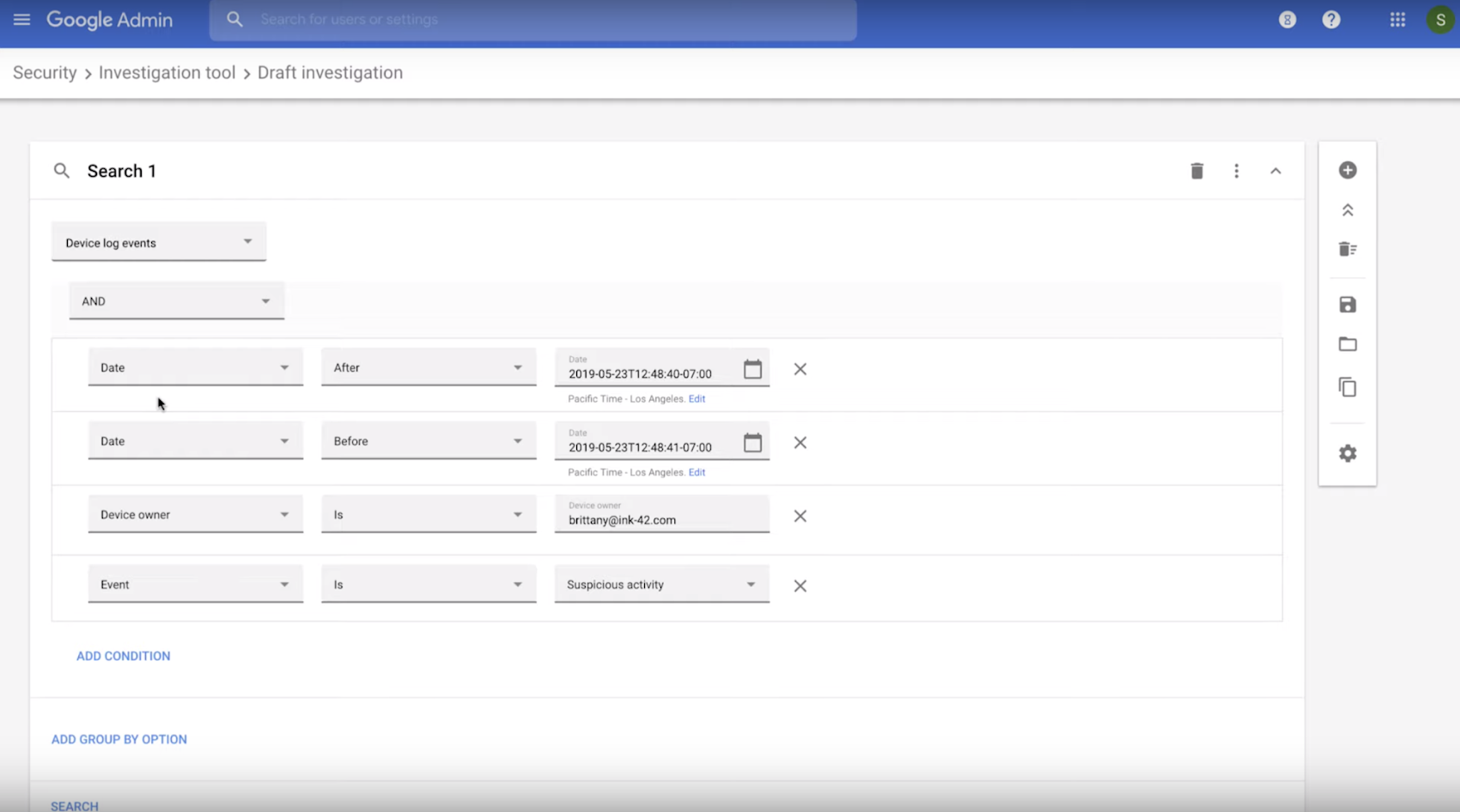
In this example, we can click on investigate alert which directly loads the investigation tool within the security center. The investigation tool allows admins to identify, triage, and take action on security issues in their domain. As a next step, admins can perform bulk actions (organization-wide) to delete malicious email and examine file sharing to spot and stop potential data exfiltration. Lets walk through what that might look for an organization.
3. Investigate potential causes.
It’s important to try to understand the root of the problem, so that you can avoid future breaches. Remember what we said about email being the leading attack vector? Often attacks can come via email, and sometimes users can click on links despite warning banners.
By doing a quick pivot and search within the investigation tool, one can see that the suspicious email came in with the subject line “Time sensitive - update your 401k contact details” which the employee clicked on. That could be a potential reason for the device being compromised.


4. Determine the reach of your security incident.
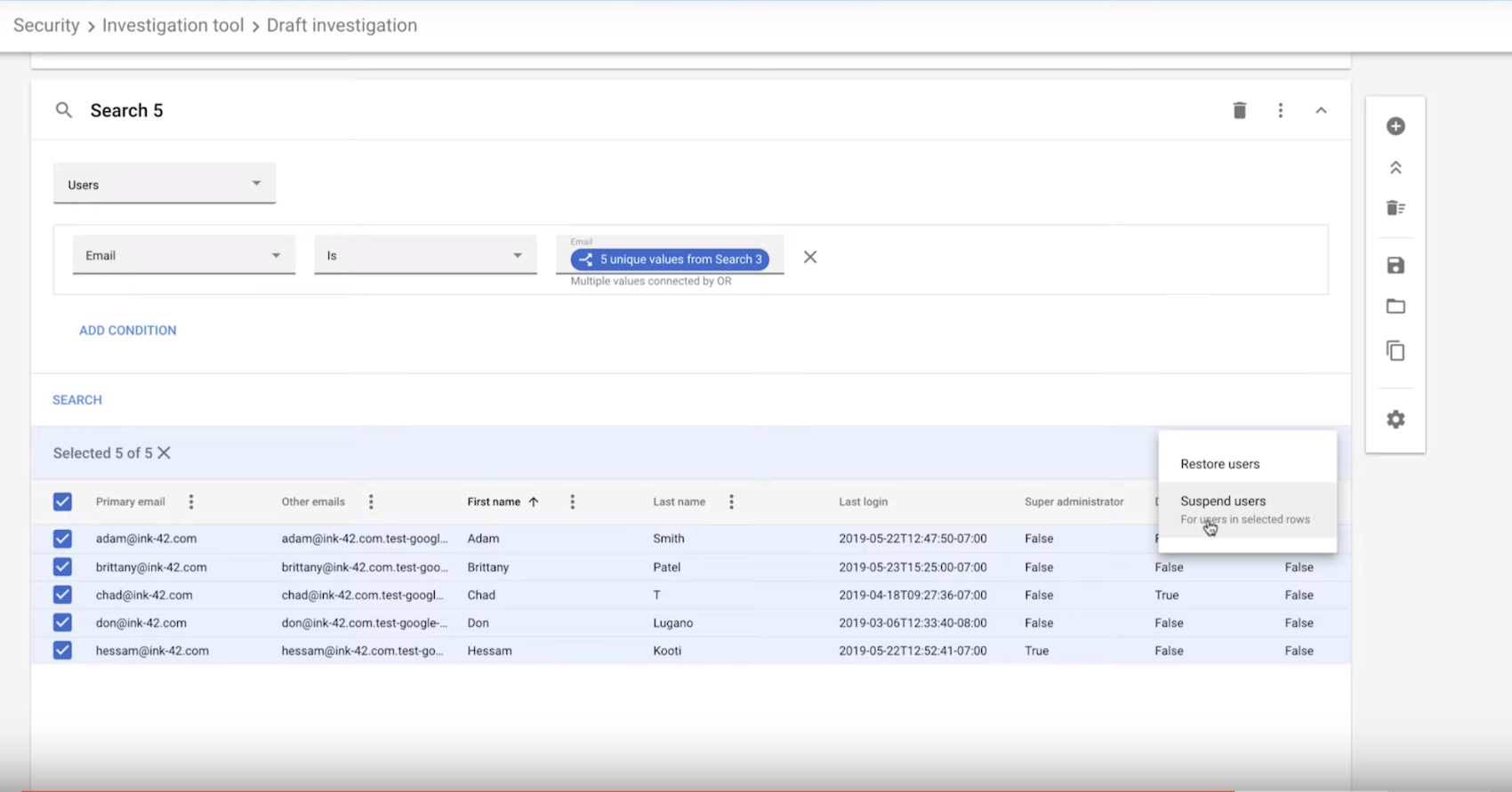
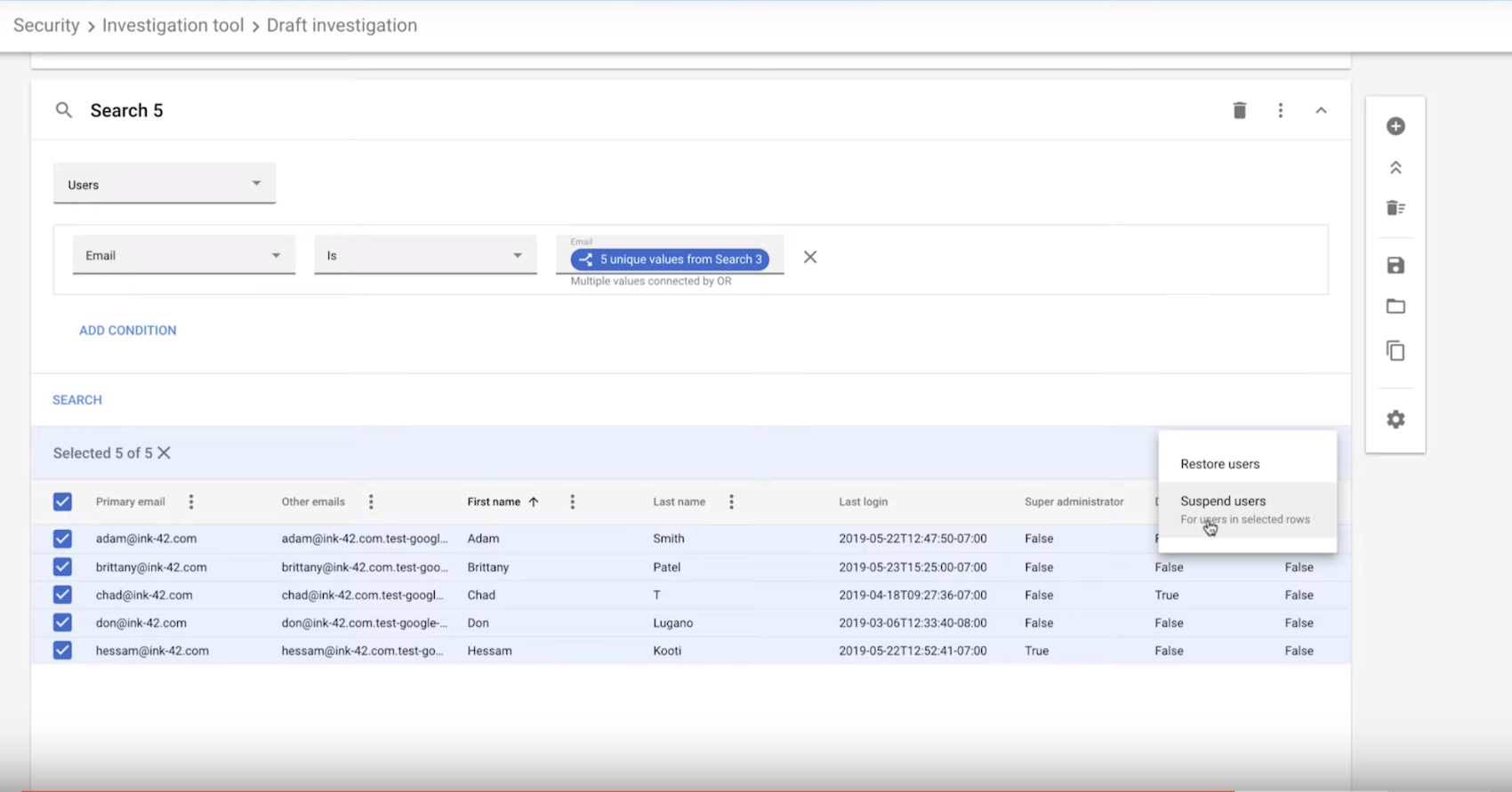
Now that you’ve figured out how this user got compromised, your next worry should be whether more users have been affected. The investigation tool is the place to figure this out. Within the same window, you can pivot and find out other people within the organization that have received the same suspicious email. In this instance, it looks like we have a bigger problem at hand.


5. Limit attack proliferation.
Now that we know that 18 other employees received the same suspicious email, we need to do some firefighting. Since we caught this attack early (thanks to the visibility that G Suite controls provide), it's likely that most employees wouldn’t haven’t opened the email. Within the investigation tool, super admins can proactively delete suspicious emails from user inboxes. This action is logged and can be audited by the organization if needed. Another option might be suspend those user accounts just to be safe, until the admin has more time to investigate.
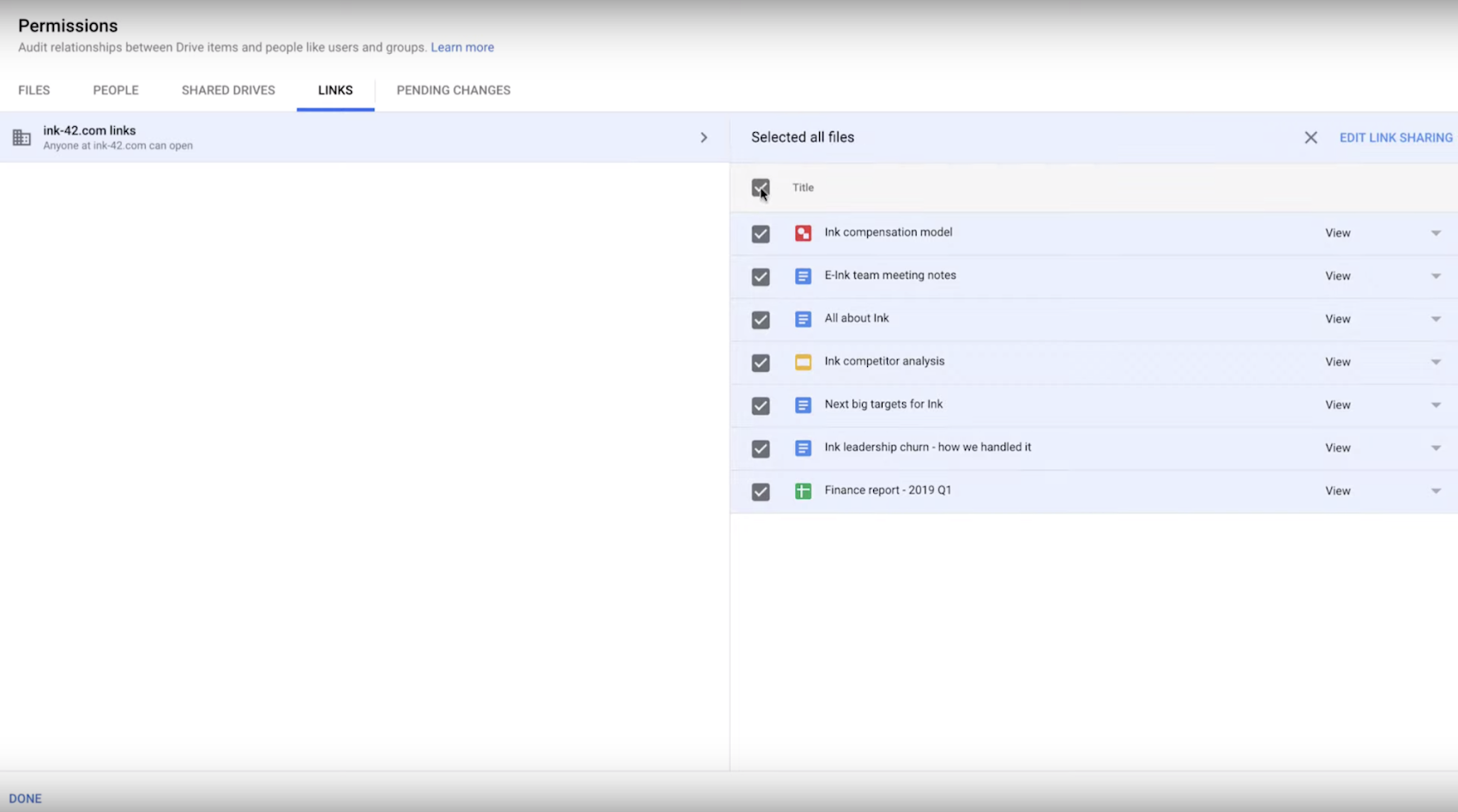
6. Finally, explore other apps or data that have been affected.
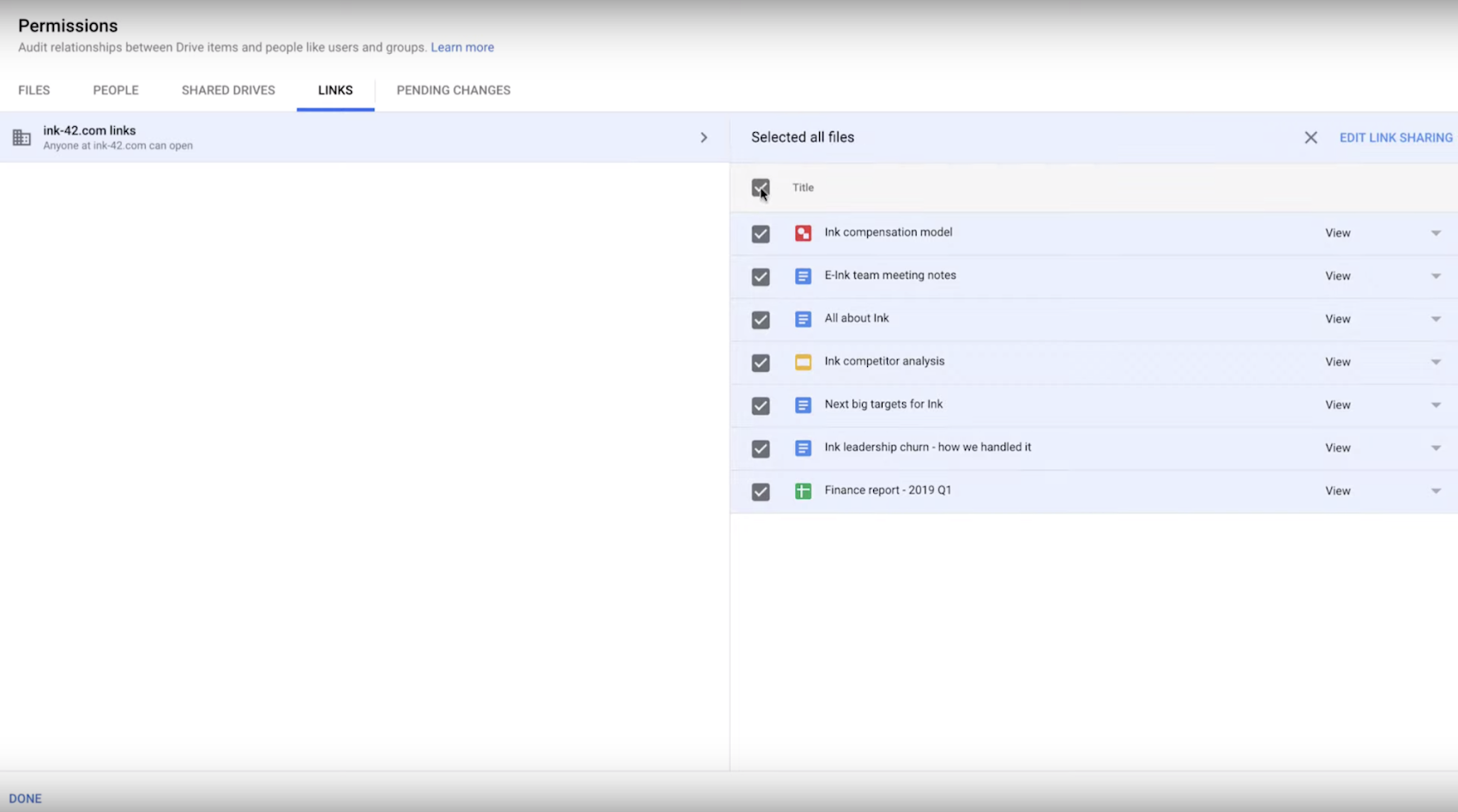
Having access to accurate information quickly is critical in these situations. For example, an admin may want to find out right away if any data has been exfiltrated because of these attacks. The investigation tool allows the admin to look at all files that have changed visibility from “internal only” to “externally visible” in just a few clicks. Once this is known, the admin can limit file sharing of these files within the organization or remove access for a certain set of users.
Next steps
This is one of the many ways you can help solve security issues using G Suite’s proactive, intelligent tools. Learn more security tips from Google experts by watching these G Suite security videos or register to attend our free Digital Conference on December 10, 2019 where Google experts will provide strategies to help you better secure business data in G Suite.

